Phishing Analysis
Detailed analysis of captured phishing page
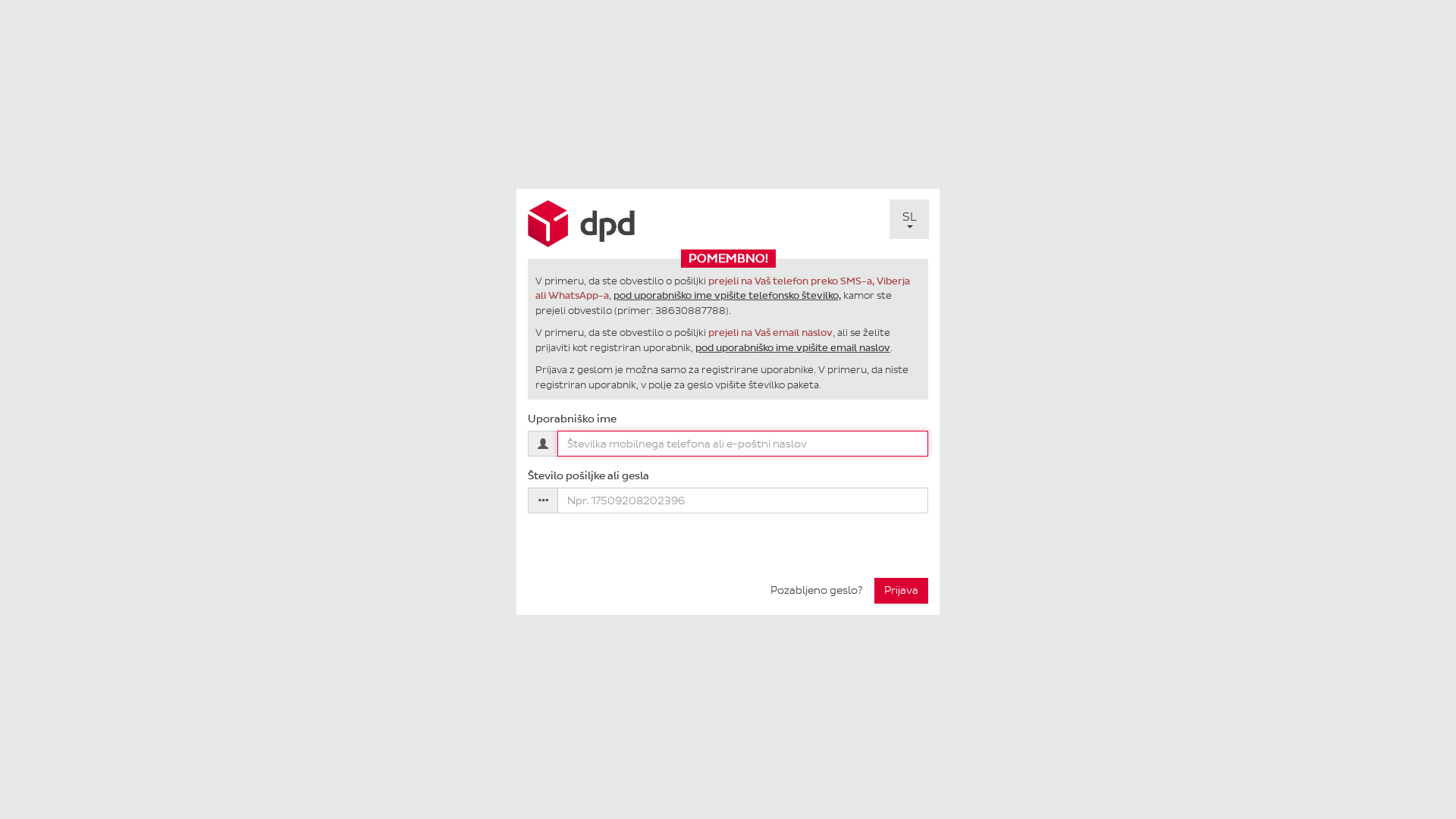
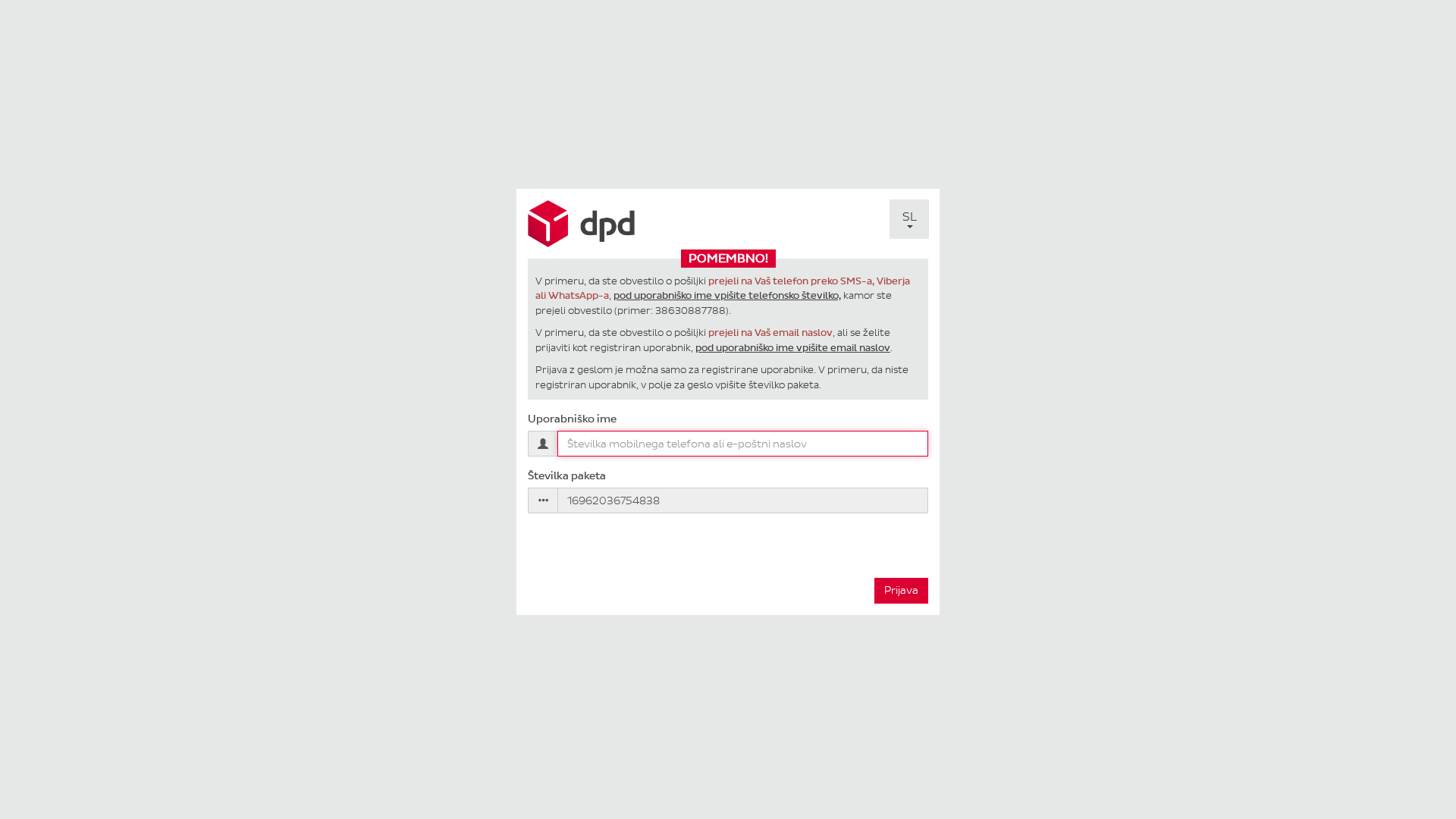
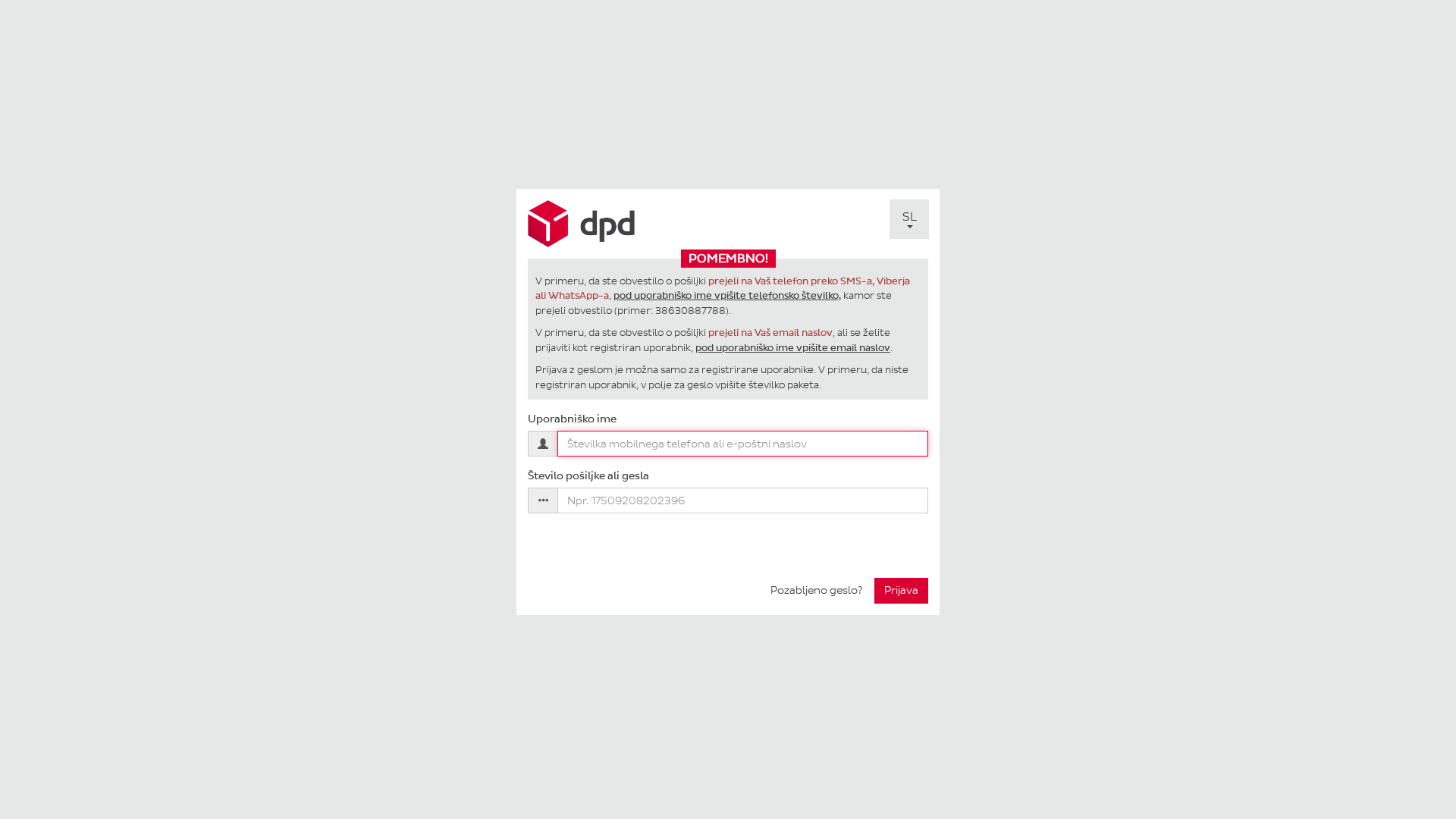
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D3A1956190048D3B1693D8EDBAB09B0A31C5C248CE4B9E42EBFC53EC4EE2C53EE25561 |
|
CONTENT
ssdeep
|
48:7d/cpZ8nYQg5ZIw0zZ0TMlllq8CGC9SrFy8P+jD3DVQcHsEZ0k+R3h6mbzSJmRER:5/8Z8YQAsZSUpCuF8bsaz+R3tSJmeh |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
993364cc3366ce99 |
|
VISUAL
aHash
|
201844243c381000 |
|
VISUAL
dHash
|
2c10184c32322408 |
|
VISUAL
wHash
|
1c3c04243f3b3f2f |
|
VISUAL
colorHash
|
07200000006 |
|
VISUAL
cropResistant
|
2c10184c32322408 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: DPD customers
• Method: Impersonation of login page.
• Exfil: Phone number/email and package number.
• Indicators: Forms, Obfuscation, JavaScript form submission
• Risk: HIGH
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
🎯 Kit Endpoints
- /SL/Login/PasswordForgotten
- /SL/Login/Login
- /EN/Login/Login
- /IT/Login/Login
- /HR/Login/Login
- /DE/Login/Login
📤 Form Action Targets
- /SL/Login/Login
- /SL/Login/PasswordForgotten
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 14 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The website presents a login form designed to steal DPD account credentials (phone/email and package number). The user is tricked into entering these details, which are then likely sent to the attacker.
Secondary Method: Impersonation
The site mirrors the visual appearance of the DPD login to increase the likelihood that a user will enter their details.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.pay.mojdpd.si
Found 3 other scans for this domain