Phishing Analysis
Detailed analysis of captured phishing page
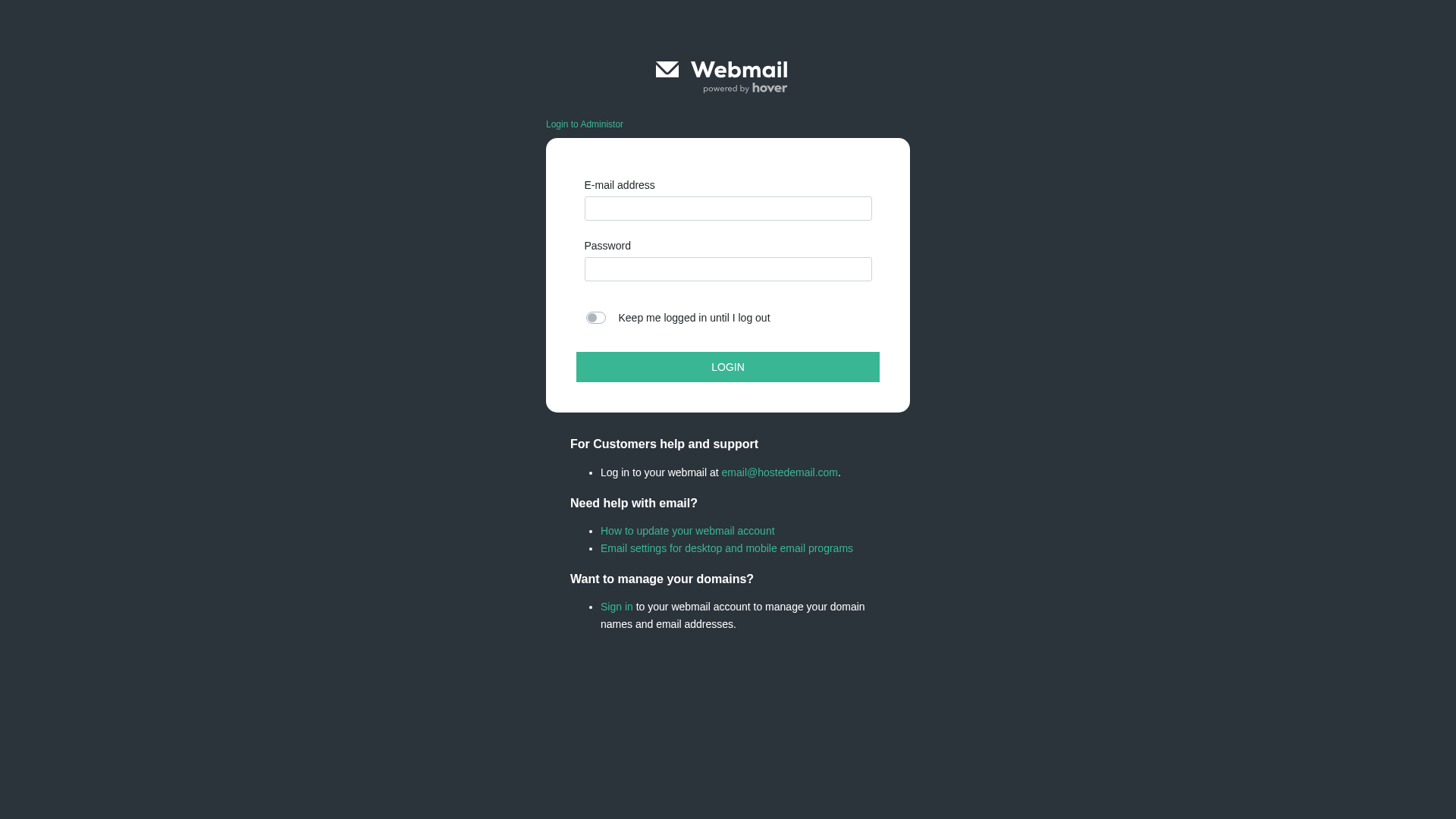
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12152B8E112246BAD84D795DEAF72D694638F80B6FAA2C5C45AFECB5858C3C80F717810 |
|
CONTENT
ssdeep
|
384:yw/O+rMimrrRMAciBMABrczvtVqpM6KK3:fkrriPdI+vtV0X3 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc9933666699cc36 |
|
VISUAL
aHash
|
0018181818000000 |
|
VISUAL
dHash
|
14b2b2b232343008 |
|
VISUAL
wHash
|
383c3c3c18181800 |
|
VISUAL
colorHash
|
07008000c00 |
|
VISUAL
cropResistant
|
e060e8608c9c3111,14b2b2b232343008 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Hover Webmail users
• Method: Impersonation of login page.
• Exfil: Telegram Bot token (likely credentials)
• Indicators: Domain mismatch, Javascript Obfuscation, Form present
• Risk: HIGH
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://mail.hover.com/plugins/skins/login.css?s=1728655216
🔑 Telegram Bot Tokens (1)
- 8159384639:AAFn...NMHM_LSQ
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- 1 Telegram bot token(s)
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 68 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The website is designed to steal the user's email and password by presenting a fake login form. The collected credentials can then be used to access the user's Hover webmail account.
Secondary Method: JavaScript Obfuscation
The presence of obfuscated Javascript code suggests the attacker is trying to hide malicious intent, further suggesting the website is not legitimate.
📡 Telegram Command & Control Infrastructure
💬 Message Templates (3)
| ID | Portuguese | English | Trigger |
|---|---|---|---|
🌐 Infrastructure Indicators of Compromise
Domain Information
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Moderate
- : Light
- : Light
- : None
- : Light
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for ipfs.io
Found 10 other scans for this domain
-
https://bafybeifucnntp2tzvo2smmgd2nrz2anlih4bapzou...
https://bafybeidainj73npe2kepzldqmuwzes5stwbgtu2pb...
https://bafybeidzv5orafwm4qq7m5wdptagbyyaksssolxhe...
https://bafybeiby3jwvxj44lno5pu2qjn5ezh5mlm4fkoy4q...
https://bafybeiaz6xbudbilnb4a52kkl2ffapf7oim253s7i...
https://bafybeieqilhn5yjrdt2cs46bglcamzimrcgbfuvq3...
https://bafkreidpy5pr2m6yvnk6v7ry7tu5lydi2rkd5reft...
https://bafybeih4lunv4ykv3qnx3n4c2c3d3gl5vlonz34ui...
http://ipfs.io/ipfs/bafybeibo7ht7ythkoucqnhcd4lzr5...
https://bafybeicfvmv4fni2inofzgesr4hc754scsn2zsohf...