
Phishing Analysis
Detailed analysis of captured phishing page
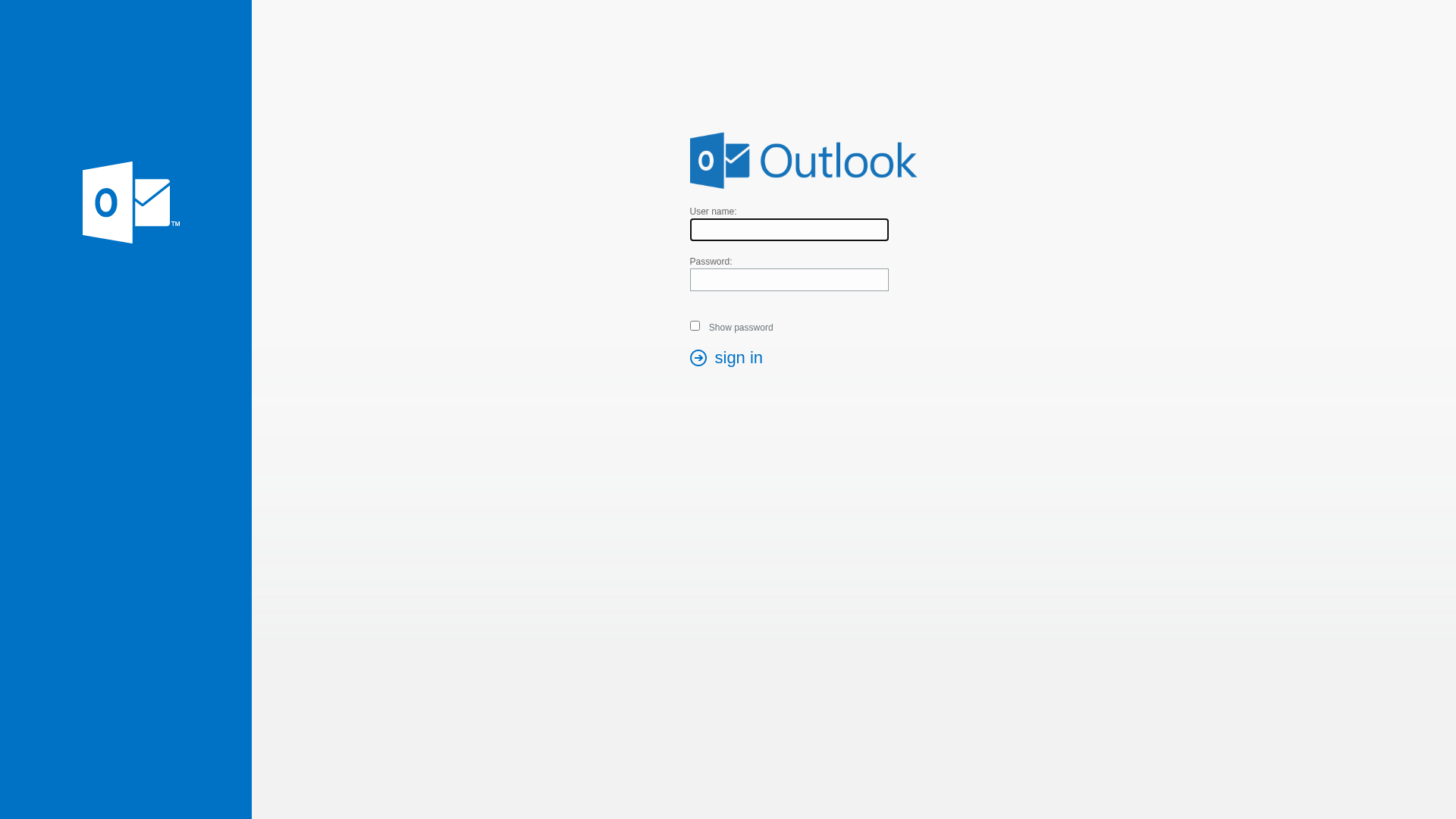
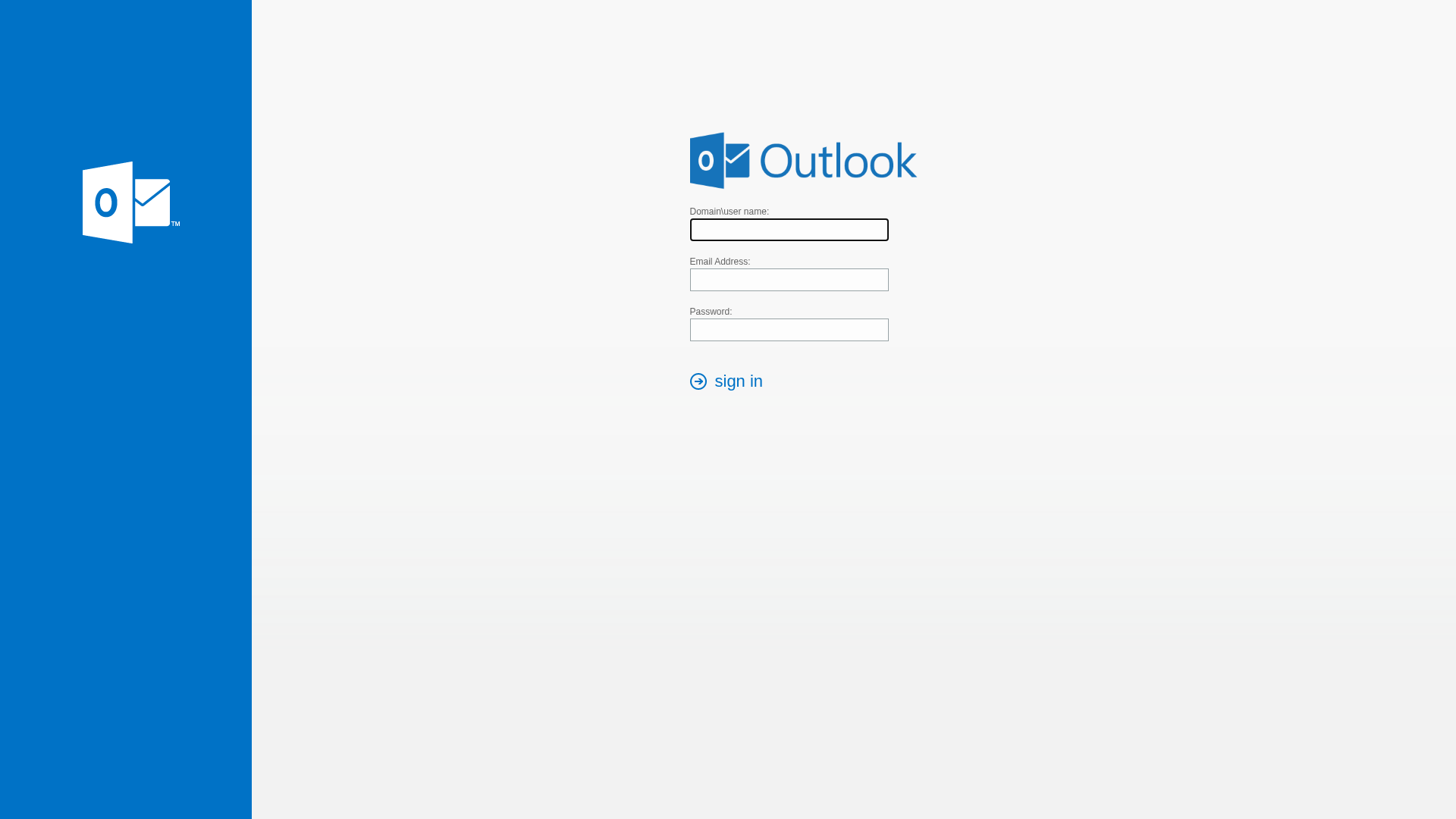
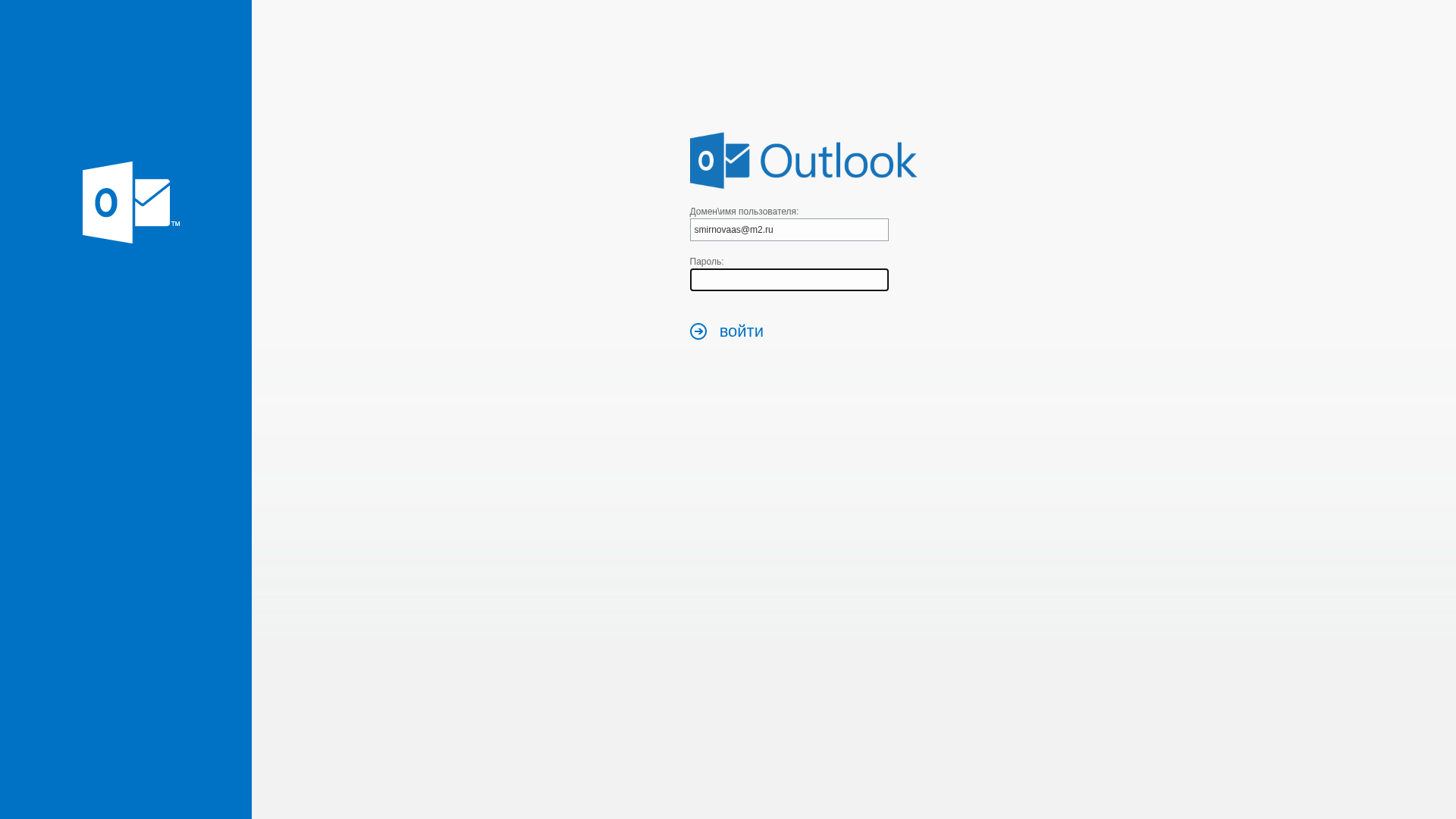
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T11E51E060901AAC339113E1E86AE46B4B3297C705C787294867F4C37C2EF3C5DDF66669 |
|
CONTENT
ssdeep
|
48:+k1UJhhzkkz9d9zTOiyXhxnja26YXAPy9u5X/a3LM7ay6BLPHwur16:jOZz9P+hxnebBy9u5vabMeBFPwE6 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
83f67e09890999fc |
|
VISUAL
aHash
|
3f3f3f3f3f3f3f3f |
|
VISUAL
dHash
|
d0ccccdad0d0d0d0 |
|
VISUAL
wHash
|
3f27373f3f000000 |
|
VISUAL
colorHash
|
060000001c0 |
|
VISUAL
cropResistant
|
a09c989080808080,f184acb6b6ac84f3,0e71710e20000000 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Microsoft Outlook users
• Method: Credential harvesting
• Exfil: Unknown. Obfuscation suggests exfiltration may be present
• Indicators: Domain mismatch, use of obfuscation.
• Risk: HIGH
🔒 Obfuscation Detected
- atob
- document.write
📡 API Calls Detected
- login.php
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer
- 7 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The site is designed to steal the victim's login credentials for Microsoft Outlook. It imitates the official login page, tricking users into entering their email and password.
Secondary Method: Javascript Obfuscation
The use of JavaScript obfuscation makes analysis more difficult. Malicious code could be present to further compromise the victim's data.
🌐 Infrastructure Indicators of Compromise
Domain Information
🔬 JavaScript Deep Analysis
🔐 Obfuscation Detected
- : Light
🤖 AI-Extracted Threat Intelligence
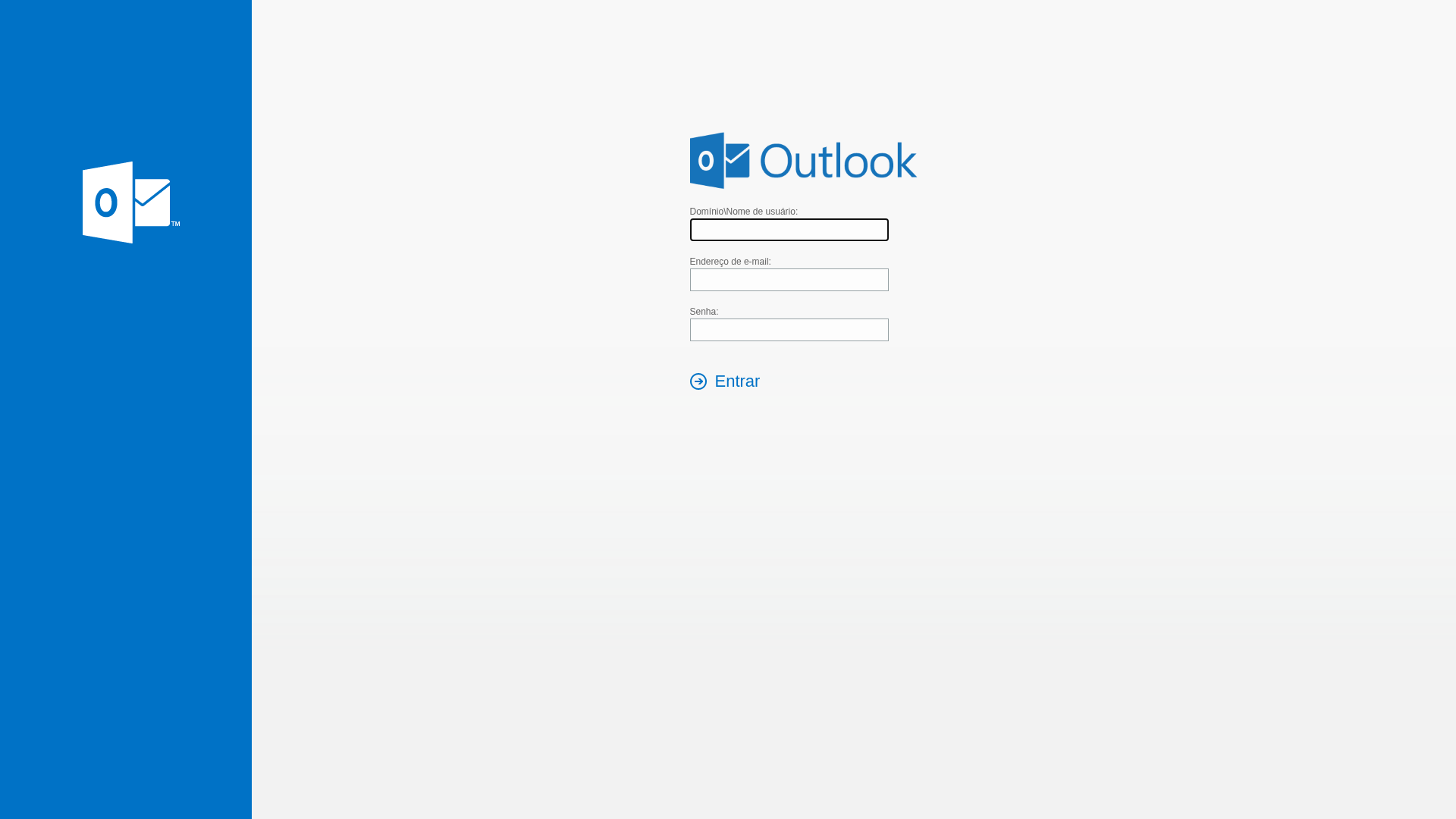
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for autodiscover.sociospanama.com
Found 2 other scans for this domain
