Phishing Analysis
Detailed analysis of captured phishing page
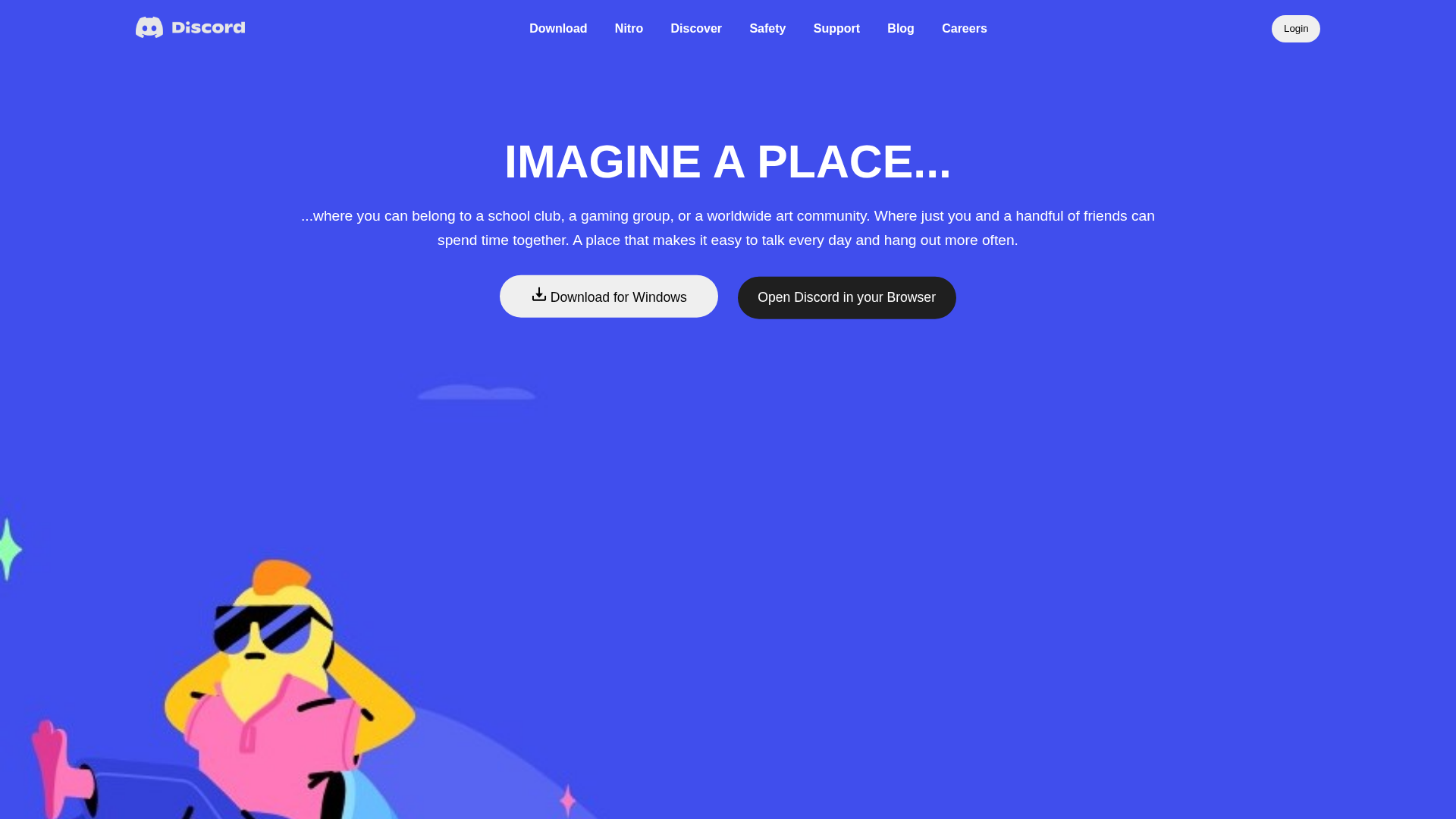
Visual Capture
No screenshot available
Detection Info
http://botkesaksham.github.io/Discord_landingpage
Detected Brand
Discord
Country
International
Confidence
100%
HTTP Status
200
Report ID
ef993fe1-e2d…
Analyzed
2025-12-21 06:25
Final URL (after redirects)
https://botkesaksham.github.io/Discord_landingpage/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T185910071A484873B42C393D0AB61372E37E241C6ED574E0811F9C74E9F69F4ACD2A987 |
|
CONTENT
ssdeep
|
48:n+fxCQNqjB9abWriFT9c4umlxioifKf9DuPD88vdqALI1/Fc:nxDiIAzbifaDu6e |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c01ef13b37e40ef0 |
|
VISUAL
aHash
|
013c30300000e0e0 |
|
VISUAL
dHash
|
a370642458809080 |
|
VISUAL
wHash
|
ffff763000c0e0f0 |
|
VISUAL
colorHash
|
000000001c0 |
|
VISUAL
cropResistant
|
84a2a2221baab280,29d0e4469ad0e676,a370642458809080 |
Code Analysis
Risk Score
50/100
Threat Level
ALTO
🎣 Credential Harvester
🔬 Threat Analysis Report
• Threat: Brand impersonation phishing attack.
• Target: Discord users.
• Method: Using Discord's brand and logo on a free hosting domain.
• Exfil: Not applicable, as there's no form. Likely aimed at redirecting users to malicious sites or other forms of attack.
• Indicators: Free hosting (botkesaksham.github.io), Discord branding.
• Risk: HIGH - Could lead to credential theft or malware installation if the user is redirected to a malicious site.
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for botkesaksham.github.io
Found 2 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.