
Phishing Analysis
Detailed analysis of captured phishing page
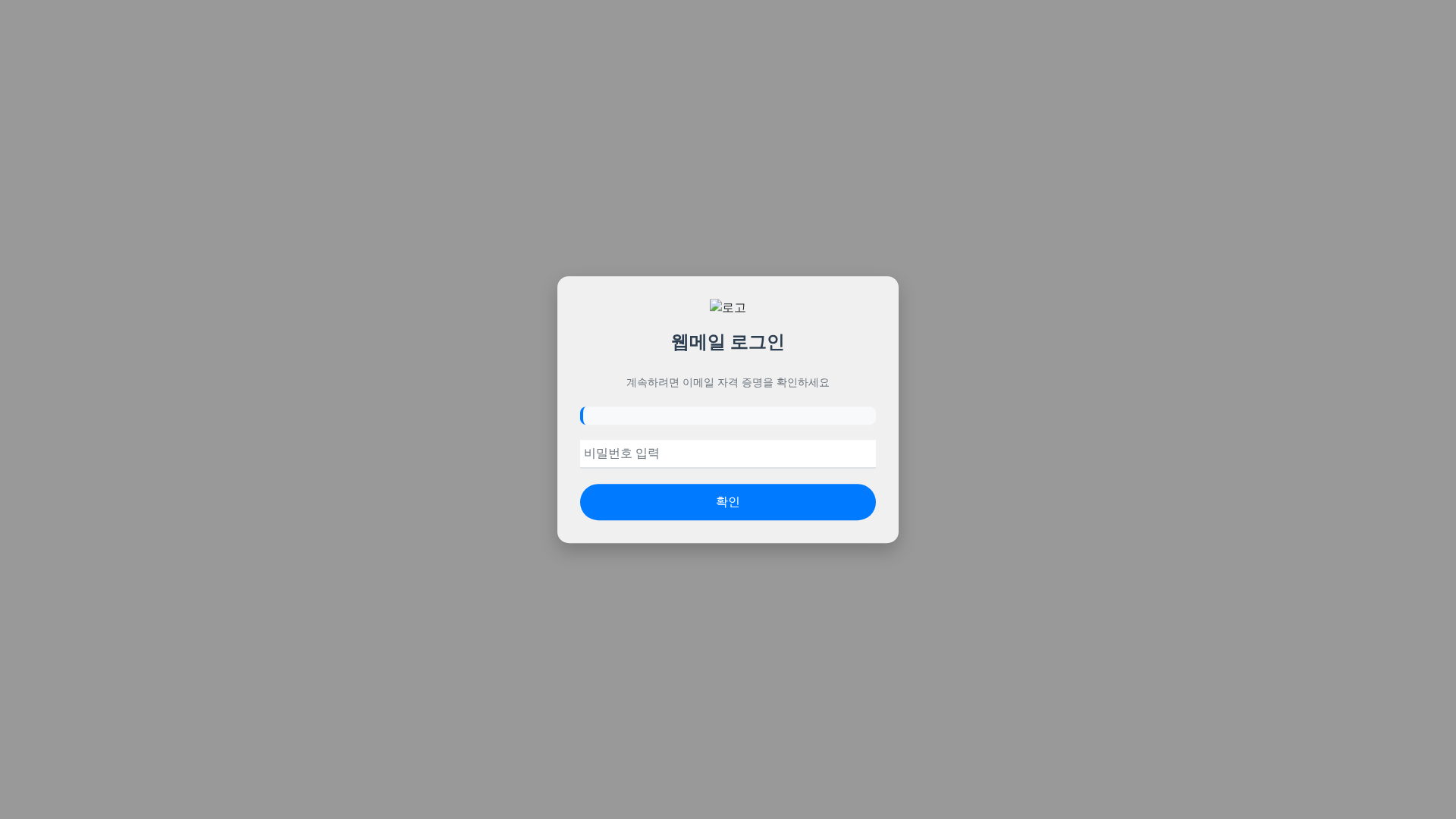
Visual Capture
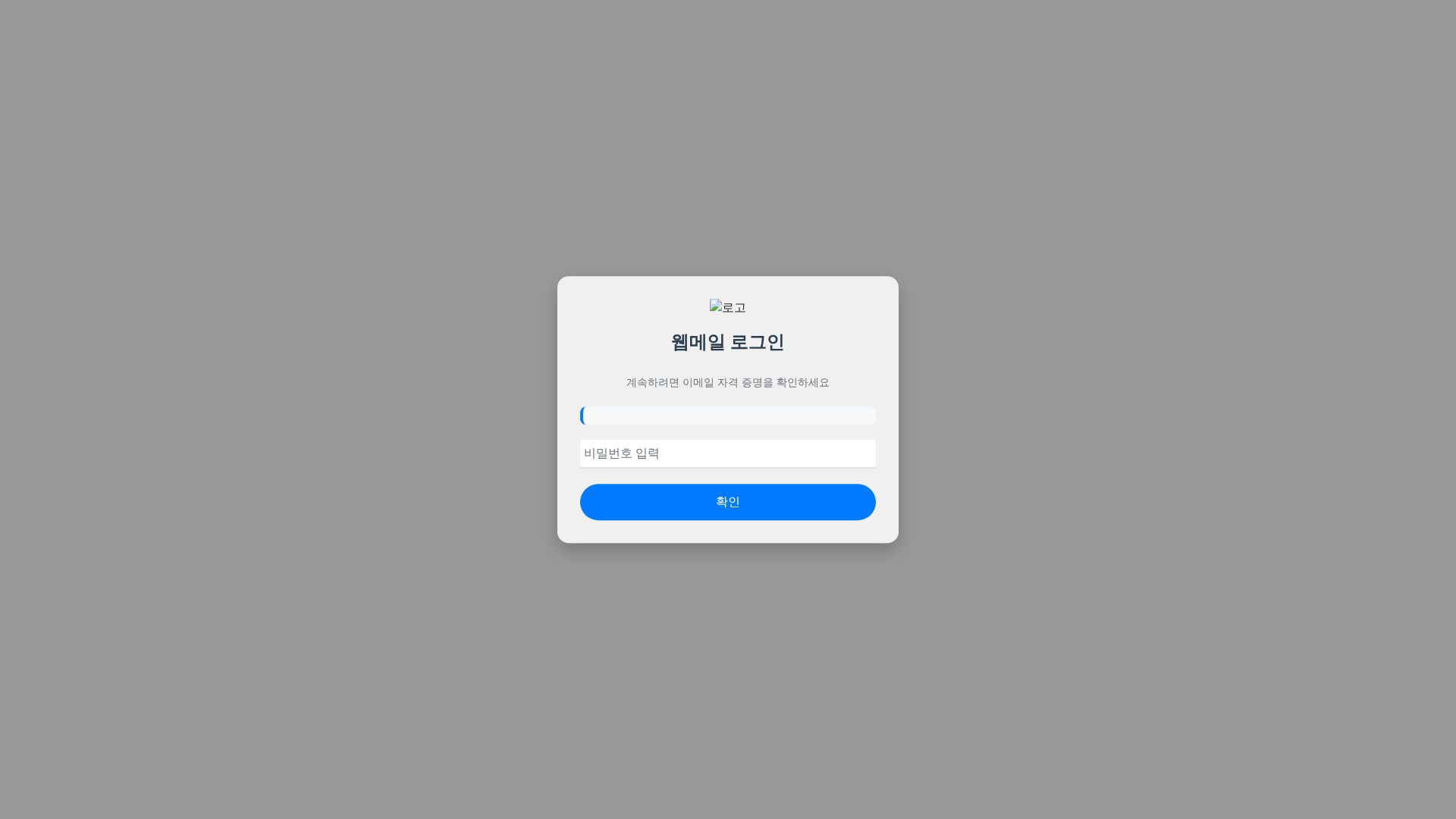
Detection Info
https://concentricaviation.com/Xx/Koreaweb/index.html
Detected Brand
Unknown
Country
International
Confidence
100%
HTTP Status
200
Report ID
f25b1cee-fa6…
Analyzed
2026-03-04 02:05
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1FD211220583E897779C286FC71D5B21D12DAC205CF530E1256FA83EC1AD2E9FCC61284 |
|
CONTENT
ssdeep
|
24:hcCOgecuDfjYHMC117rV/vt/iU8PDNbNxPFYT0zmaHWhLS:gcCbYp17dBiU0NbjPFYT0zmaQG |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
99cc663399cc6633 |
|
VISUAL
aHash
|
0000181818000000 |
|
VISUAL
dHash
|
200c32b2b2281400 |
|
VISUAL
wHash
|
0f0f1b1b1b1b0303 |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
200c32b2b2281400 |
Code Analysis
Risk Score
68/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Webmail users
• Method: Credential Harvesting
• Exfil: Unknown, likely to a server controlled by the attackers.
• Indicators: Domain mismatch, login form, korean language.
• Risk: High
🔒 Obfuscation Detected
- fromCharCode
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain does not match any known webmail service.
Forms Present - Credential Harvesting
The page has a form that is designed to capture login information.
Language Mismatch
The page is in Korean, indicating a possible targeted attack. The language doesn't align with the domain.
Obfuscation Detected
The presence of `fromCharCode` suggests the use of Javascript obfuscation.
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
General public
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Unknown
Fake Service
Webmail service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attackers are using a fake login page to collect the victim's email and password, which are then used to access the user's account.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
concentricaviation.com
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
https://cdn.gosafemode.com/screenshots/b475c5ea4219.png
Apr 07, 2026
No screenshot
Unknown
https://ln.run/RSSTc
Mar 02, 2026
Kakao
https://ln.run/iALGM
Jan 18, 2026
No screenshot
Unknown
https://cosmoslifters.com/kr/korea/index.html
Jan 18, 2026
No screenshot
Unknown
https://ln.run/iALGM
Jan 18, 2026

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.