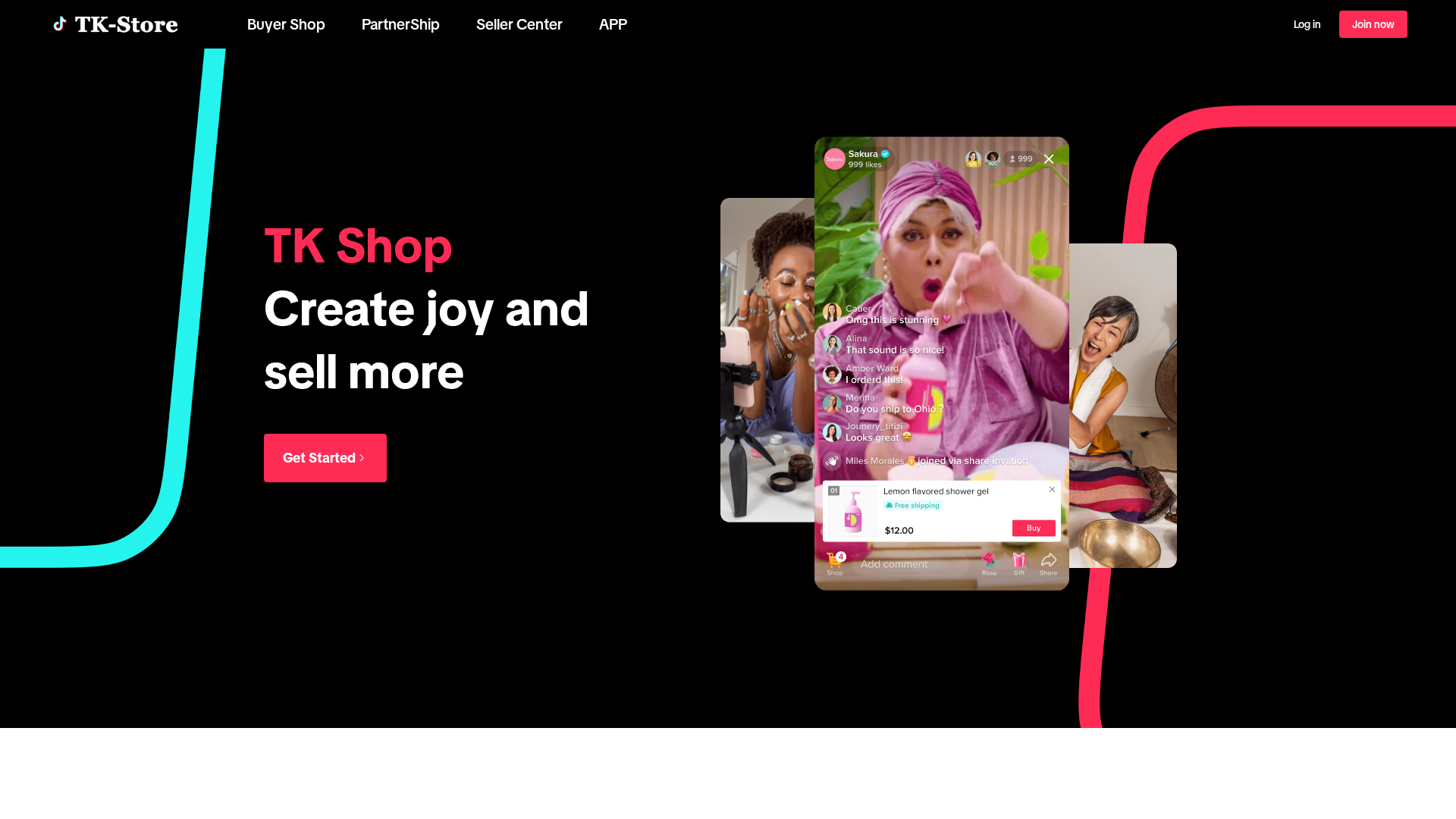
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A50395729161EA7381C3C7F0933A676AB3C1C15ADB634B4982FC634D6BD2C52DC3661A |
|
CONTENT
ssdeep
|
768:Lili35IwuSI4I1q/bmuENs10YuT1wBGtu9/7ImC47:ui35IoI4I1q/b4Ns10h1wBGu/7IZ47 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9210ed7ee1659758 |
|
VISUAL
aHash
|
00040e0e0c0c00ff |
|
VISUAL
dHash
|
839998dc9818c60c |
|
VISUAL
wHash
|
004f6e6ece8e00ff |
|
VISUAL
colorHash
|
39400040002 |
|
VISUAL
cropResistant
|
e9696f65d232f8f0,0400000000000000,838998dc98980c84 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing kit
• Target: TikTok users internationally
• Method: Fake login form stealing email and password
• Exfil: Data sent to unknown server (obfuscated JS)
• Indicators: Domain mismatch, obfuscated JavaScript, newer domain
• Risk: HIGH - Immediate credential theft
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAfsAAABHCAMAAAA3Kh5aAAACJVBMVEVHcEz///////////////////8AAAD///////////////////////////////8AAAD///////8AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAD///8l9O7+LFUJPTxA9fBfECD+e5UgBQq+IT8CDw/9LFXk/v3I/Pv+Rmp/Fir//v7+r78OW1kg1dAct7JvEyU/CxUQAgUvCBD+Ol8gBQsAAQHdJkoj5N/tKVAz9e/eJkr+YX//5eoSenf+iZ+fGzVPDRpB9fCE+PX/ytQTenf/8fPy/v7+iJ+t+/mS+fZPDhr+lapfESDuKVD+OV93+PTj/v1b9vL/ydT/5ekHLS3+sL8LTEr+booy9e+S+fcFHh7/ytUHLi0QAwW/O1VvLTswMDB06OXeqrQgICDH+/oiLy/e3t6t+/j+r74HLizx/v5b9/Ig1M9pnJvNPlqfkpWf+vgRBAb+VHUFHx/vk6UfxsH9YX/vkqU+5uFO9fH+YID/lar+YH+PGS8wCBDNJEQCEBBrn5+7+/pACxXfdoq+IUAHLi4OXFr/5Ogm9O7+orX/5OnBf47uhZrua4QQa2j+lqoXmZT//v/uk6WOGS/ua4XeXHVO9vH/8fTOI0Vp+PMj5d/+U3UZp6PuUXAap6MXmJT/vcneQWBp9/N2+PQNW1mGRFeTuj76AAAAKnRSTlMAEGCg8DBAgEDAcNAg4FD+sJAg7xDeMN++j7/uz5CAr19vAX9goHCwzp+lc9hQAAAKPklEQVR42u2dh5vcxBXAR80a1dv1VdvYxpQUaXU+m7PxOeCGGzYlEAiEHgiQBEjvHdILJb1Q0nuvf18k7WpPo5k3Zdcr7e3pfZ+/z7caaUf66b15896bWYQI2XFg//J8JJLl3Xt3oFZmSRauFWMfyvxbl9onNjPkd0WKsn9n+9RmQg7MR+pybfvcZkB2RSPJVa3qb3l7vzsaUZZb+FtcroqiFn5r8NXN/kL7ALeuXBeNJbvaJ7hlZefyeOyjNs6zZeV6Edv11b6sA8d3T/0t+ti1U3Gx3+Im1F6o16u9vjwlq/gWVhAtPQE82GcFnSYnoWHGQzE7en6mpnaN7ar2Kftbb8zktR++XUrxw1hFPIS64EEzg98FTpMRzTapUzs60rzsP3i7s1+WYH8wf2bvSE4CLch5nq3EPkbIgQ9meBzgNAlhkM8k8OKWPUI7Imn28S13Ai3eNJ3s+9rNv/h2ln0K7L/+MNDizY2wv6b4wmvYt2YRSm86jteyJ2S/Avv4hVNAQhdknz5xh2QXOBUIKSTdZvA1ndQx13LX0bW9yhEdq2m9kXuNmu4B7I3Sx2EbzmWwv+0DQJMFNnu7/wGBtP+Z5VWMt+aSQ7OpE93cZGN2Lbk7K71O5uYpLps93cNtIPMq7OPbPijh7A3Z6whkj7SgOnCT04MOqcNDirbsxEwHjHtpJNju7CMl9nH8IfEMv2BvIA57ZFXZazEMoNBhz5K+saBk8IkDuGU/IvvPfH5Vkr2pcdkPXxHEb4ZKM3xPPhpTVnsdsf2Rlr0a+zi+/xsn7pFhH4qgBrLsdab+8qXD8ee9lv2I7OP4e9/9/mkheweJoGJJ9ngE9MjkOO64ZT8y+/htyQ1C9ljIfjCKi5oVzpkSesJ5MIApQMt+MuxLai9QaEGzAr2rdFuYuJjFPjoCe5xnBLFSQtDH2OJdzm0qq6TA/p9PKLDXJdj3R3x+swK9jsZgb1pMxc/Z5xk9orlR5AorpkQ3gnJ8yaX455fSs2xxFtEKcnNj9U8yDaq173pEfnGq2K8/u/rseon9oWNPSrHXOumdIxn2btpQ5zYbTeur7OO4qzEOu1WnsCLlL/UNOi3kYCCWNPQntA4028BUc/nQxaTZr/7yQpaz/2+ZfbLxr0PPiNlTEstZVFb4b5Sxnr5YrngWNfu3EeImEza7qgFpZsfnsg+J9yUsqwczvYingf1TN2fgD/77P//beK7Efi1au/TI5fsefLom9qOjL4d2ho+2WwnthrLsrUDCNtAXMiqv31CvsQlcTW+c/frfU/Dvfd9jaWeS5DDBPooeuPNSktTDfgz0yGAn7gv8Wjooh0iSfVl9zW7qnwWsSYQjzFi6dNwp0ImyonrhM9C//+aM/Dv7KXuKfSpnHnhorQb246An4noV/KTXBRcNFUa67DsEPvVmFd2z3K7JZ9+h0WuV9FJsNco+Q3/w6KArx1jsVUt1R2M/TLqMxB4FnDIxnZxnAX7+AINv0mi0gO0SGlz2TjWZNJhlOuq1aBNi/48S+gbZ62x/W1pcHgXT5Xy3zY4AE68hYVZ8duN86kb8VW3iMS4WNsj+pjL65th7YxfY8Au2KhlBuIcAGFqfGSOI52Oqnc2YyMLJ63rZpxb/xrwTT/ziL8cu39IUe7pcV1Us/uhLFofAPQwoxaU9O0znCHOMGhlnyKyGZjLOUy9CnQj7VO0fzbtwR9KXaWCvkryVhg+GHm1Q7R3EhmywP07R+lWrwRwsGqoirFL8a693tEB/w6nT0ZloGtiz/b08gFgVXR6+TDyfGLC70DwCZF+2Dx41ErGSjjWmkqoU/9z7U9aBJ1P0a5V4fpPsmf6eLSre1vh+d6CJ2YsSy5W3iGK/+f7lSQWfPA3buQRTwf49vd79WQe+k2wuxGje1wNMoZA9K2zO7gvUQwyNEha/GGmzy75Tdi4l1ix1mmK/OjD55chdM3O8rtjfk2CfPvsuPNM3hex18P1j87IZzX13GESUWbvgNMX+pt6tcZ/9WsPsqRgp7e9Jsc90FMQfitjbcuwdHnvQfZg69r8fxHJfotg/XS97LRD5ezD7fJTVxfi7dbMXB/3LDmXd4/278w58K53bFfLzAfu/1cuedtNdafY2Q4FY+J1m2dsMcVFT7NeHa24311ufGLwPD9fMns7HYFn2mP3sdQ8a8Jthj5qVKsUT/fE+/vaLxSc/7vXuzj55JklO1cseCfw9F/TfMOQxV1Z+xc2O91PG/vZeP3kbf+X5/gc/ujBw/Q8lyXM1sxf5ey7DZlqlqRkWBvuukJ9vyLK3p2khMFW3ceGTg4598cvnzp175Z5er/eu7M9XLyV/jOpmr5mjTX4x7DK7SjYfx1DVFdsTEbHXGyzTEedybv9s0bMvffVEVrr10xx9/IMEHu4nxr4SQpGOemFOQtRU8fUk43qWLHtLHKlukP365x4runb07m/eddej/azeT/K0Tu3saX9PV2Fvanx3iznHM8AButT3kB0jErEnQ/dU97SOgxtkH336wwwP6g/HkmQjaoA9VQpjWgrsWVbfEcV2HOU8XleevcF9GEajuZwsvvMxCv3x3ybJ+dONsKc2zZGBjzlmtaR5AfO7PeX8vS/P3oo5im/XG9Bn7b3w8U9UHve9v0uSi4c5yziWJseeHvIl4GN4jMDCXE6sgYofMl09A8mzr0xdiImLUXPVFnOLtY9+5HhZ6R9PDf7FM7xlW9z9lH25cLUPuUGuOnwLdKjKZiRga3fl9RTW65WjDmL2lVfZGzYqEn715fHYey2d/cKn7u3j/9Xxxy+nbt55Lvp57ld05Zw1ErGJOUFwUzgmQotniIw+hmIuhp4tkhys5LEYdbrEuxJCwzm7l9VopGfny/g645QojSZ7AZwb579234M/+/XrbzySkj/ym9Pc1ZrgjroaxvQWWl6X2iXLwiFVZtFxi+Wpmsmosucvha1MDIu2YQC8hDonJRjSNtpgE/YrYcMuc4EtN5dn1rjlL7i34tm1l48cOZKk/y5uHBas1N0rRQAc9h1RK6DiQZp9yszIVseasP0JOF9QfjEC3fJDh7lwi10YHFADFG/LR7POtRkLnI22zp46uXHyIRF4jpt/pdgDqqLAXlCmC7xeQCCYfRksrgqE5q3j1aReeaOvIIto0uw1cyT2sII5vsArIad0UOFf+TIK7MmxR8GNqcvoy8vV0LVNudrLjrhVyK24AtjrzFXzcXXhPJDic8iVWx3RZSzgHphWXLNp+kb9u/uvTEztkWVD4pIPQtzKBTJ2gNjDErnQCIC1uDwejF01fJewT3SLkHkP4Gyd7JjnNrHvytLE1H5axA/tbr94v2uHXOXK5iUuvD0OwgO+4ZWJug9+z8N2G/sZh33joV9BrWxdGcvqL7Y/kLeVZefi6Oj3tD+HvV3ht+i3LfzFFv0MyK45dfJzK+1YPxOytKhKf8/V7VObFbluZU4e/9xb9rU/gjxTw/6BlT1zErJnZV/7I7gzKAtLOwSysx3lZ0L+D3bddzo/SQPXAAAAAElFTkSuQmCC
📡 API Calls Detected
- GET
- POST
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 1013 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The phishing kit captures TikTok login credentials in real-time via fake login forms. Submitted data is exfiltrated to attacker-controlled servers for account takeover and further exploitation.
Secondary Method: OTP and Payment Card Theft
The kit includes modules to intercept one-time passwords (OTPs) and steal payment card details, enabling unauthorized transactions and full account compromise.
🌐 Infrastructure Indicators of Compromise
Domain Information
🦠 Malicious Files
Large obfuscated JavaScript file likely containing credential harvesting and data exfiltration logic.
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Moderate
- : Heavy
- : Light
- : Moderate
- : Light
- : Heavy
- : Moderate
- : Light
- : Light
- : None
- : Light
- : Light
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
Similar Websites
Pages with identical visual appearance (based on perceptual hash)