
Phishing Analysis
Detailed analysis of captured phishing page
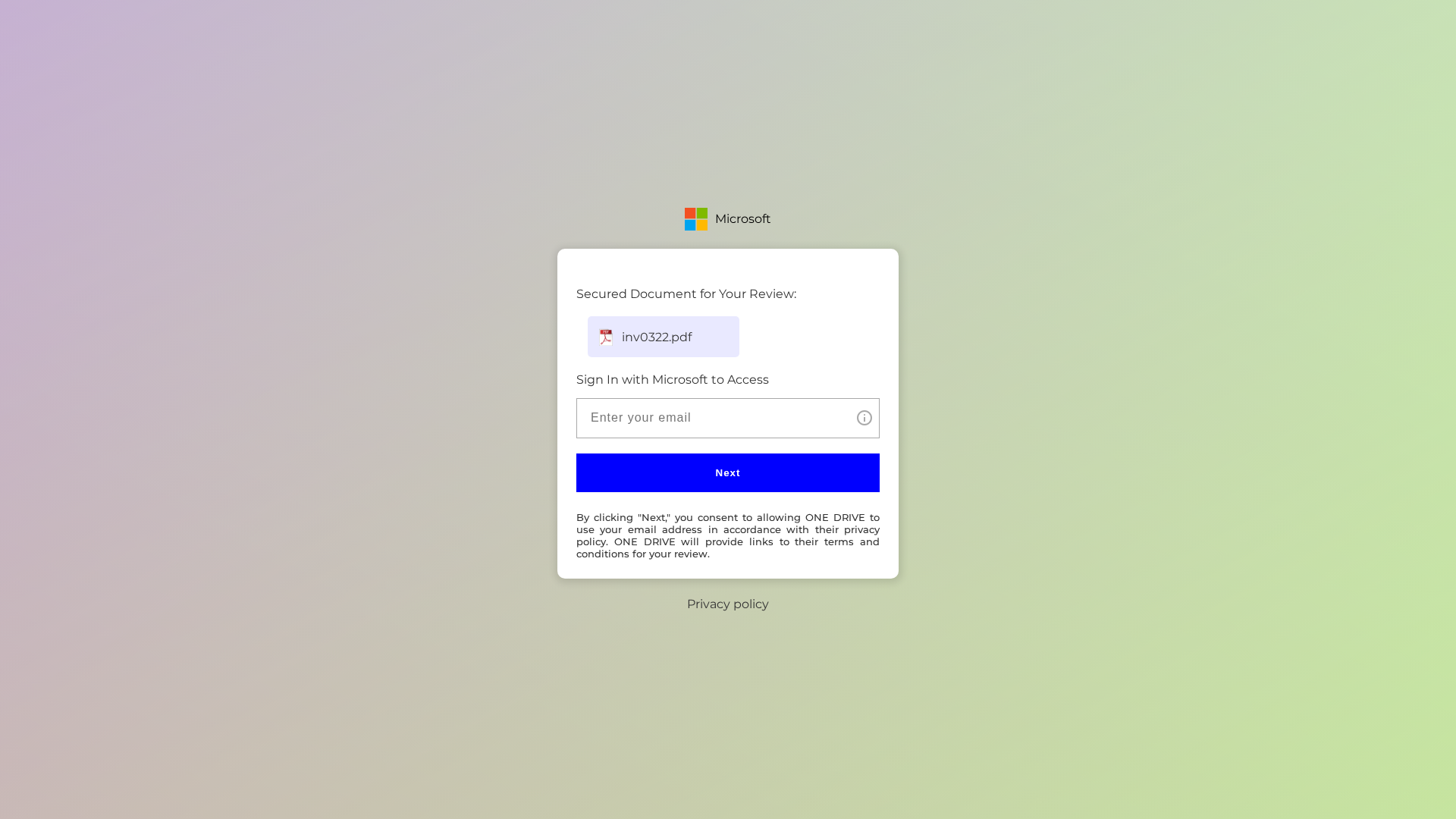
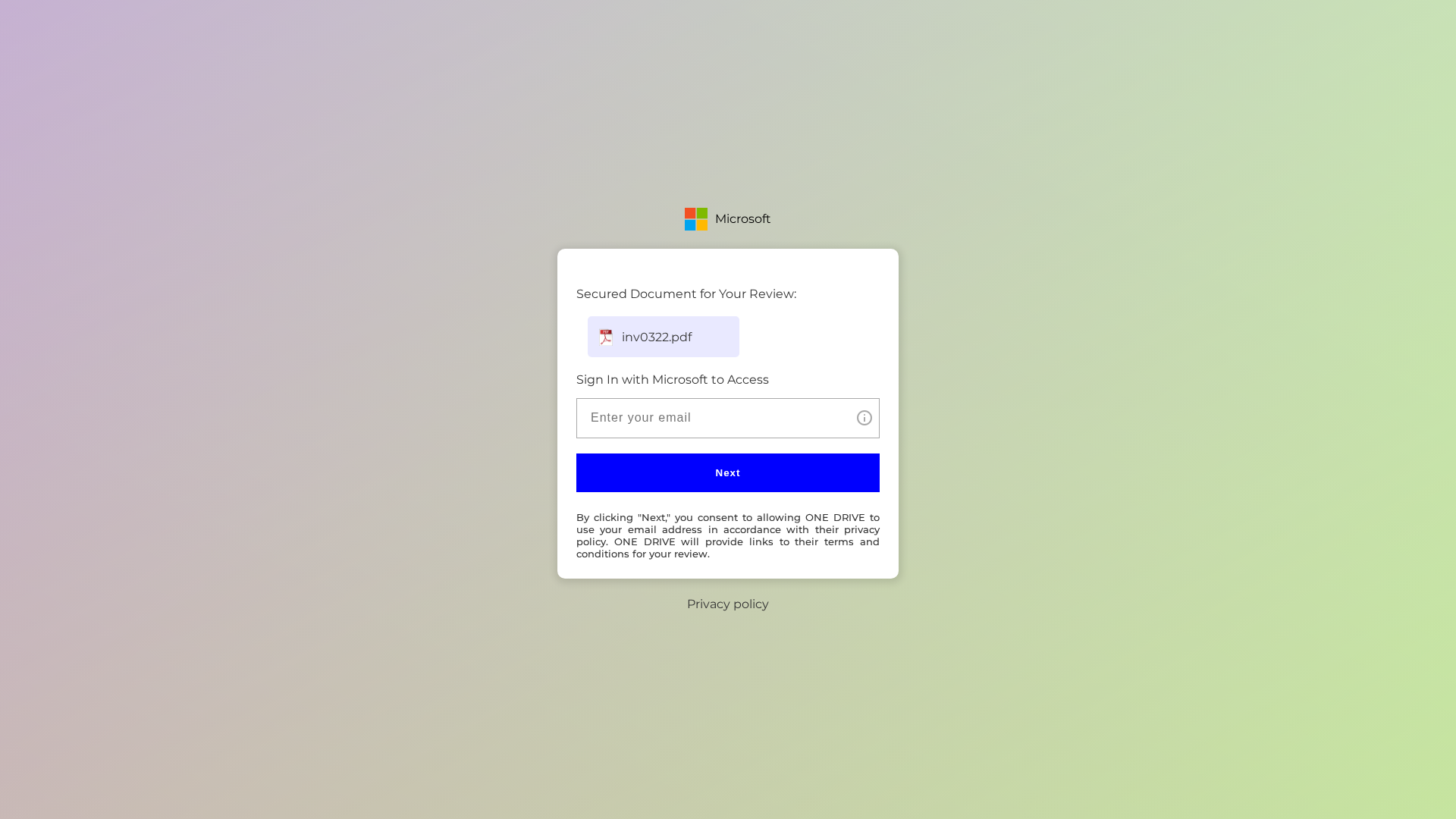
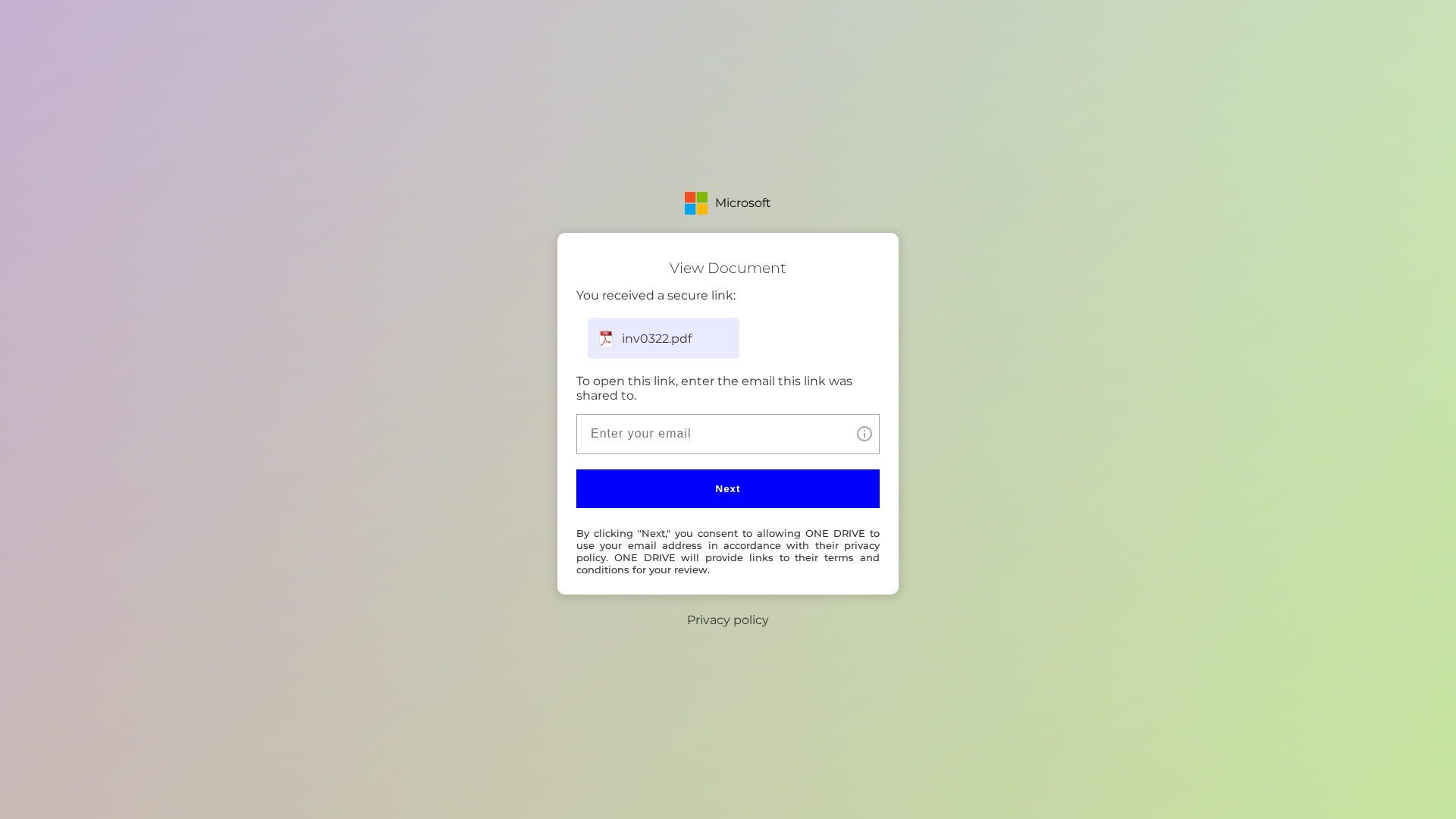
Visual Capture
Detection Info
https://starelectronicaccess.com/acmarca
Detected Brand
Microsoft
Country
International
Confidence
95%
HTTP Status
200
Report ID
f4e939af-5aa…
Analyzed
2026-02-25 04:13
Final URL (after redirects)
https://starelectronicaccess.com/acmarca/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12C219528C0059A670142D1C07FD7EA0679C443CBEB196F1098EDC3AD16E6F6ECC6E684 |
|
CONTENT
ssdeep
|
24:n/CMqc+1KuCL2vHVg345gKeU3+TcaV2tGS1/N/oJAT/tWyP9xAUMMj:nSKvL2ve36ReUOvV2tGOl/8AztxmI |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
888936667799d966 |
|
VISUAL
aHash
|
0f071f1f071f0707 |
|
VISUAL
dHash
|
ffeff3b3cdf3ffff |
|
VISUAL
wHash
|
070f1f1f071f0f07 |
|
VISUAL
colorHash
|
07000019040 |
|
VISUAL
cropResistant
|
ffeff3b3cdf3ffff |
Code Analysis
Threat Level
ALTO
⚠️ Phishing Confirmed
🔬 Threat Analysis Report
• Threat: Credential Phishing
• Target: Microsoft users
• Method: Impersonation via login form
• Exfil: Email address
• Indicators: Domain mismatch, young domain, form present
• Risk: HIGH
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Recent Domain
The domain is very young, which is a strong indicator of phishing.
Domain Mismatch
The domain does not match the brand being impersonated.
Form Present
The page includes a form requesting sensitive information, a common phishing tactic.
🔬 Comprehensive Threat Analysis
Threat Type
Microsoft Credential Harvester
Target
Microsoft users (International)
Attack Method
Brand impersonation + credential harvesting forms
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
LOW - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
🏢 Brand Impersonation Analysis
Impersonated Brand
Microsoft
Official Website
https://www.microsoft.com/
Fake Service
Microsoft account login
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker is attempting to steal user's credentials by presenting a fake login form that mimics the appearance of a Microsoft login page. The form will capture the email and possibly the password entered by the victim.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
starelectronicaccess.com
Registered
2024-02-13T00:00:00Z
Registrar
Namecheap
Status
clientTransferProhibited
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Microsoft
https://alabamanoticiastoday.com/metalworkservice/index.php
Apr 08, 2026
Microsoft
https://unisgrouplcd.com/publicittaspa
Mar 20, 2026
Microsoft
http://www.unisgrouplcd.com/contactsrl/
Mar 20, 2026
Microsoft
http://www.liagauthorizationaccess.com/admdecor/
Mar 05, 2026
Microsoft OneDrive
https://vuthisegweka.co.za/metalworkservice/index.php
Feb 13, 2026

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.