Phishing Analysis
Detailed analysis of captured phishing page
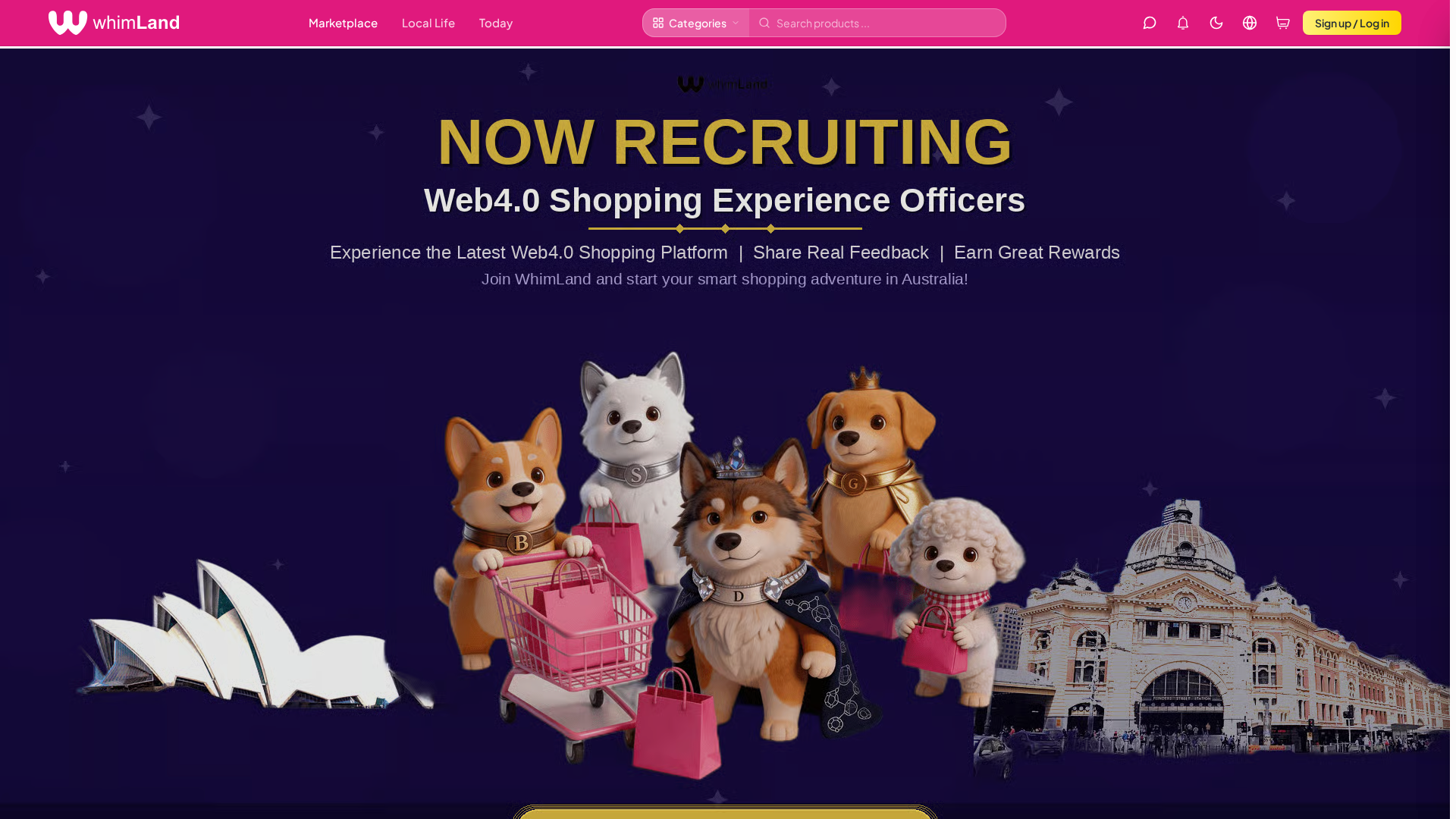
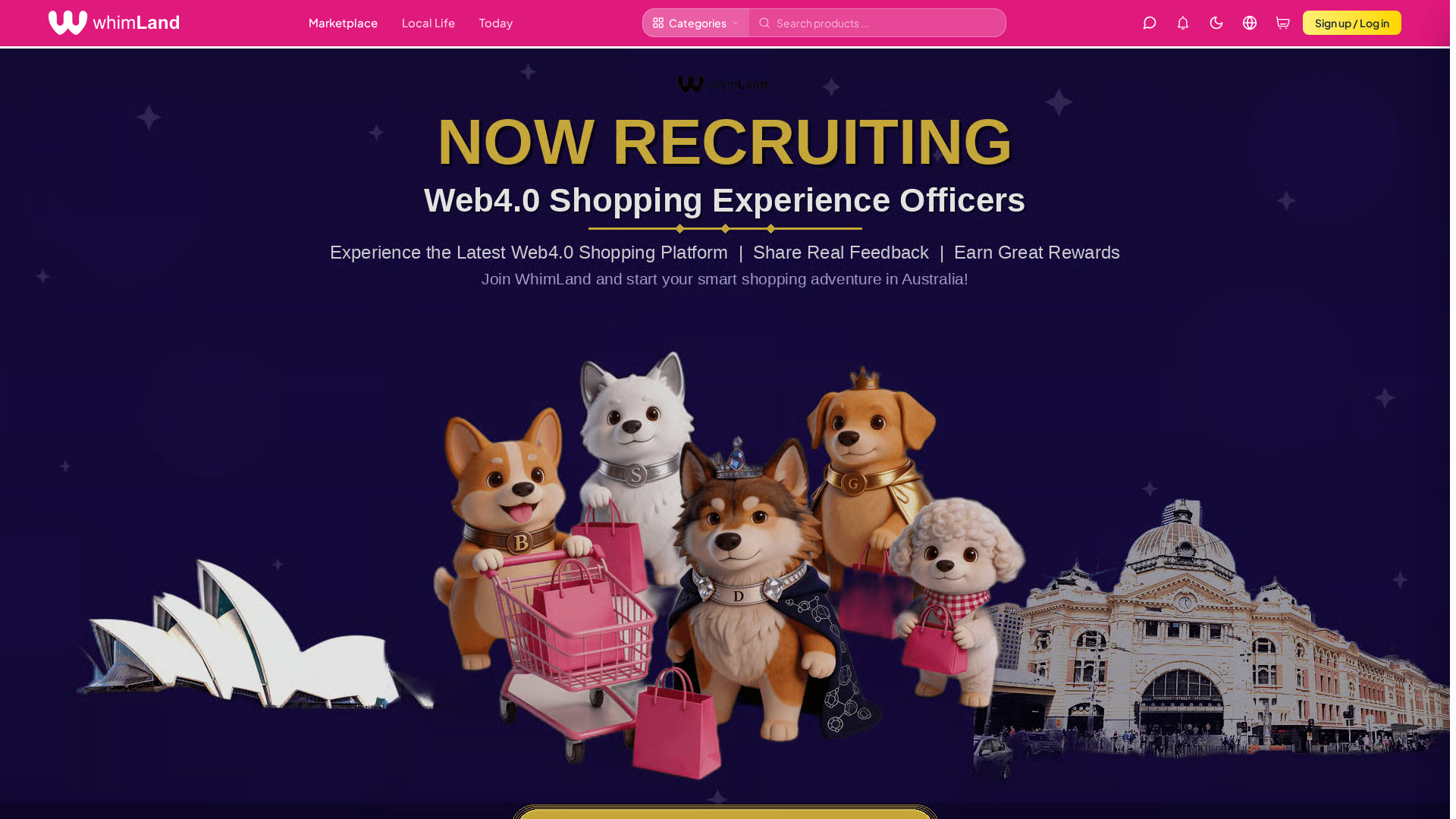
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T143044CF87341661B0227D3FB3096B826E21EA117ED179874B38EE0D7D35DD9588272E8 |
|
CONTENT
ssdeep
|
1536:mPjLZp1dmRVFXzDz3OG+m2W614XQ8PjLZp1dSdthpXHjbIeh197r3P0/VJx/PLDO:crX2wd9W/guGO+ |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
8c7ba1942be01fab |
|
VISUAL
aHash
|
ff180000383eff10 |
|
VISUAL
dHash
|
336971a361a0a6f3 |
|
VISUAL
wHash
|
ff3c0010387eff18 |
|
VISUAL
colorHash
|
39200008003 |
|
VISUAL
cropResistant
|
fcb61abcbefe7c36,148bd8dc3e97c8fc,6ce0f8e8e1b8b8b0,64f4d262a2cefc3b,336971a261a0a6f3 |
Code Analysis
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773392813052-t0xo9h-__20260313170631_23_2.png?w=3840&q=75
- https://polygon.technology
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773563283737-pmpmru-__20260315162044_17305_1588_1_.png?w=3840&q=60
- https://img.whim.land/storage/v1/object/public/admin-uploads/ads/1772779383815-crcfzo-__20260306144240_28_212.png?w=3840&q=70
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773563283737-pmpmru-__20260315162044_17305_1588_1_.png?w=3840&q=75
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773392813052-t0xo9h-__20260313170631_23_2.png?w=3840&q=70
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773563189802-7aqqr9-__20260315162031_17304_1588_1_.png?w=3840&q=70
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773566880157-0icduo-__20260315172238_1032_2362_1_.png?w=3840&q=70
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773566922525-lw8rtx-__20260315172253_1034_2362_1_.png?w=3840&q=60
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773563136583-2eko0b-__20260315162029_17303_1588.png?w=3840&q=75
- https://img.whim.land/storage/v1/object/public/admin-uploads/ads/1772779627440-3cphh4-__20260306144541_29_212.jpg?w=3840&q=70
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773392813052-t0xo9h-__20260313170631_23_2.png?w=3840&q=60
- /admin/login
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773566880157-0icduo-__20260315172238_1032_2362_1_.png?w=3840&q=75
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773566880157-0icduo-__20260315172238_1032_2362_1_.png?w=3840&q=60
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773563283737-pmpmru-__20260315162044_17305_1588_1_.png?w=3840&q=70
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773566922525-lw8rtx-__20260315172253_1034_2362_1_.png?w=3840&q=70
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773566922525-lw8rtx-__20260315172253_1034_2362_1_.png?w=3840&q=75
- https://img.whim.land/storage/v1/object/public/admin-uploads/banners/1773563136583-2eko0b-__20260315162029_17303_1588.png?w=3840&q=60
📡 API Calls Detected
- /api/product-attributes?
- /api/stripe/create-checkout-session
- /api/merchant/apply?wallet=
- /api/hot-searches?
- /api/coupons/redeem-code
- /api/shipping-address?walletAddress=
- /api/favorites?wallet_address=
- /api/member/level?wallet=
- 0x3b3b57de
- /api/search-suggestions?
- /api/chat/unread-count
- /api/coupons/available?wallet=
- /api/coupons/member?wallet=
- /api/favorites
- /api/coupons/use
- /api/sync-chain-holdings
- /api/coupons/claim
- /api/categories?locale=
- /api/shipping-address
- /api/exchange-rate?currency=
- /api/user/upload-avatar
- /api/mint-print-edition-on-purchase
- /api/checkin?wallet=
- /api/flash-sales
- /api/log-search
- /api/admin/announcements
- /api/home-nfts?
- /api/favorites/batch?
- /api/coupons/member/claim
- /api/campaigns/interact
- /api/checkin
- GET
- /api/search-insights?
- /api/complete-purchase
- /api/daily-picks
- /api/mystery-boxes
- /api/daily-picks/personalized?wallet=
- POST
- /api/platform-treasury-address?chainId=
☁️ Cloud Backend
- Supabase: xdngabnyxyyyuimogekq.supabase.co
- Supabase: app.supabase.co
- Supabase: dzfsogxbygymmufbfhxq.supabase.co
- Supabase: placeholder.supabase.co
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- Kit signatures: angler
- 979 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 979 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)