
Phishing Analysis
Detailed analysis of captured phishing page
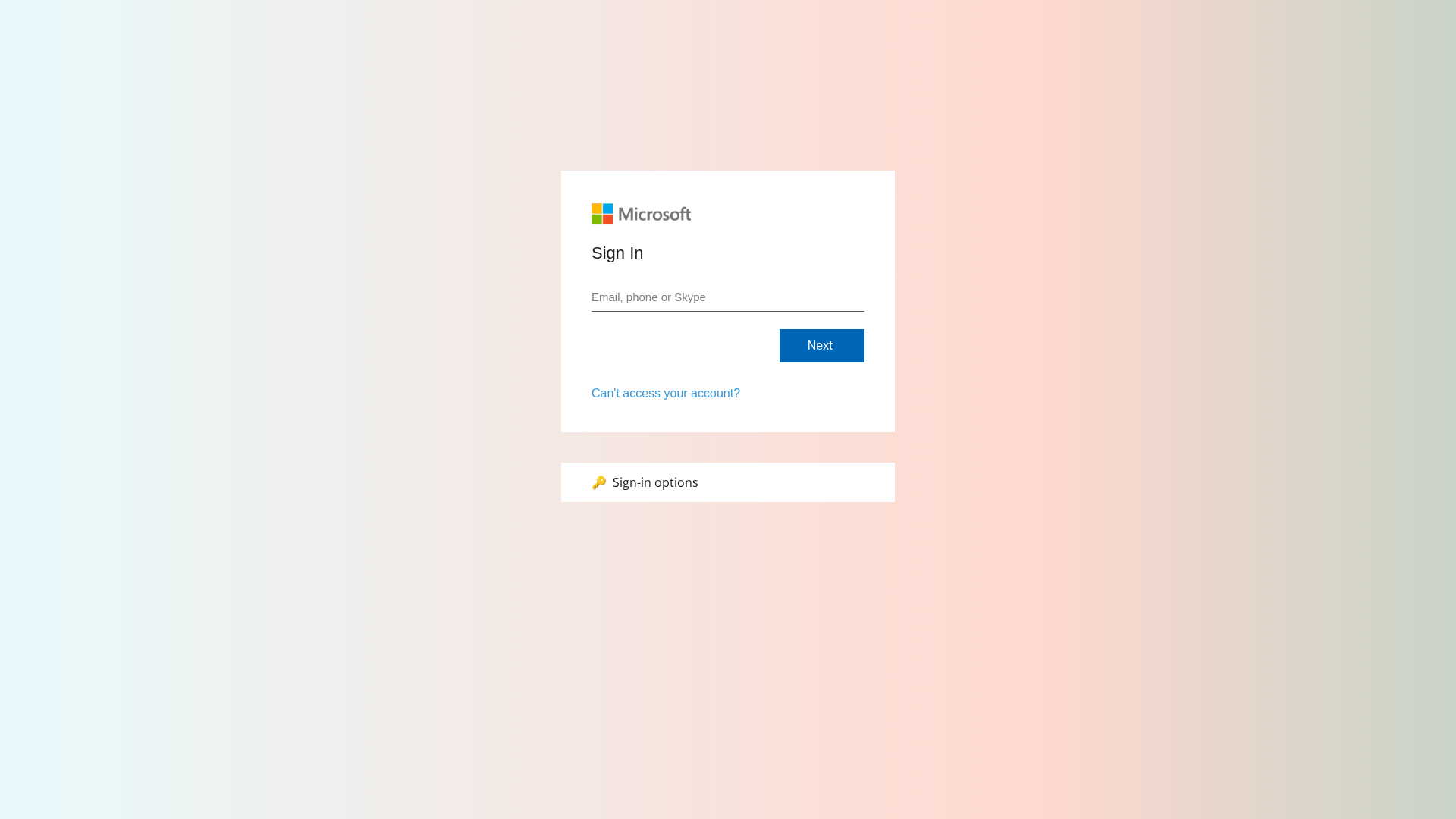
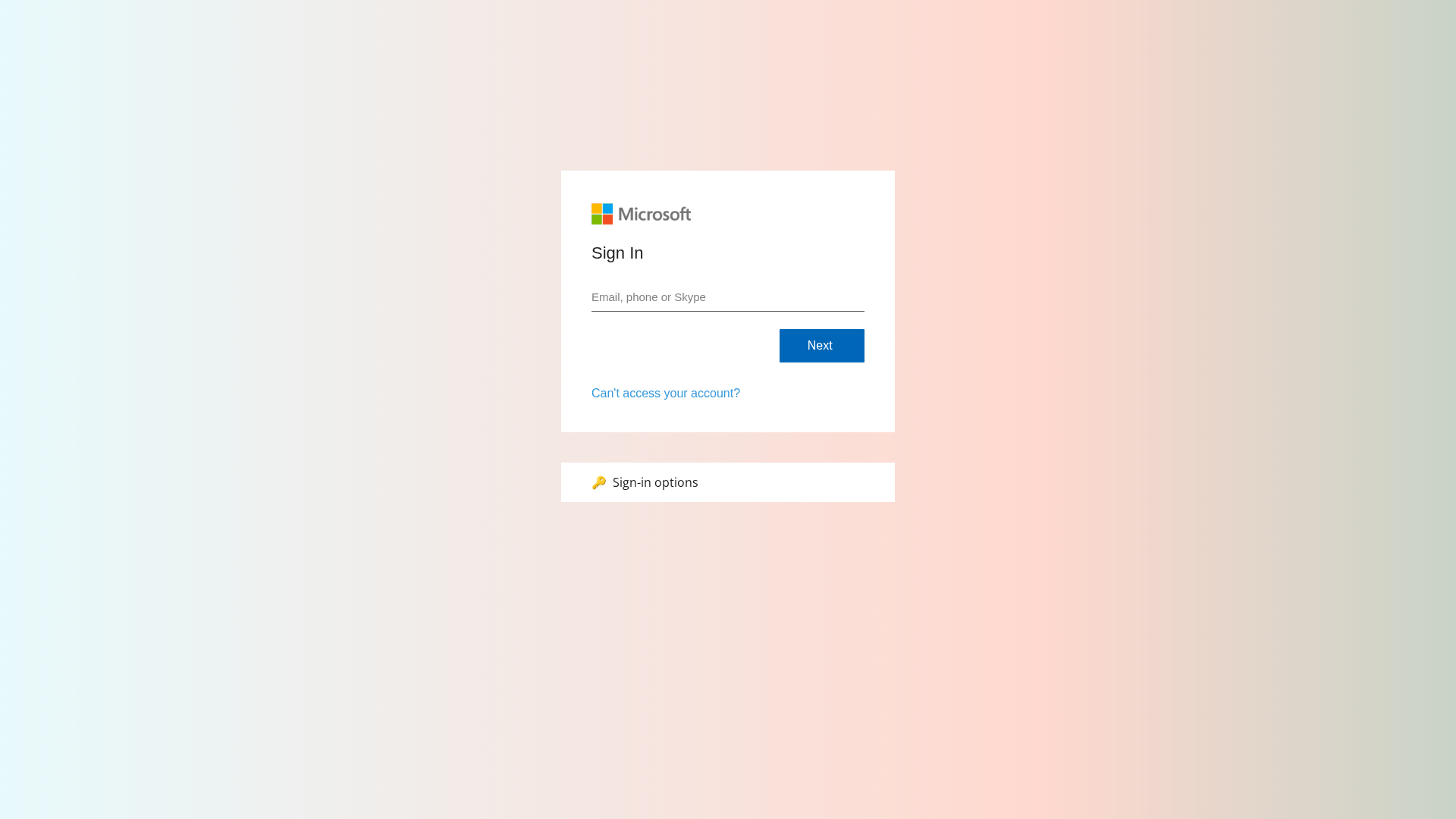
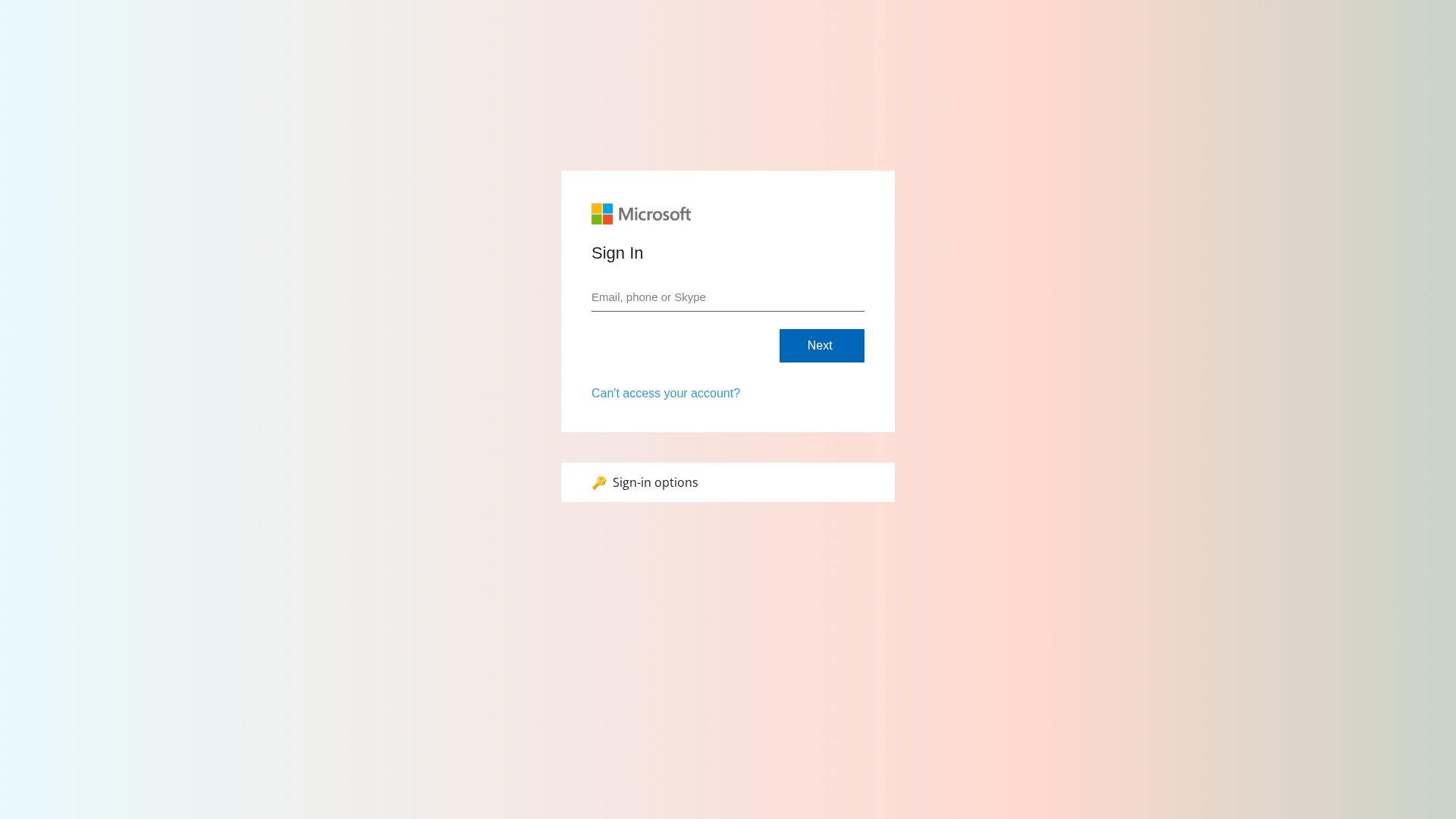
Captura Visual
Información de Detección
https://grouponedeals.com/?r=0d431905-e45d-4f55-89f1-b228db1bb97e&rg=eu
Detected Brand
Microsoft
Country
International
Confidence
100%
HTTP Status
200
Report ID
064889a3-5fe…
Analyzed
2026-02-12 23:42
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T113F1CE31E244C91B7251C9A4F6B1BB9A3B459385D70B0B70F6F0A23ABDC9CB04D942ED |
|
CONTENT
ssdeep
|
96:XNo9+uvTBSTST8FKF1fiPhevO9dShcFSTqM8V8+hucyBF+uuuup:XN6rQeQmfiPovO9dt0z8FvyM |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
dd88333366669999 |
|
VISUAL
aHash
|
f0f8f8f0f8f0f0f0 |
|
VISUAL
dHash
|
0010302430000000 |
|
VISUAL
wHash
|
e0f8f8f0f8e0f0e0 |
|
VISUAL
colorHash
|
07000000180 |
|
VISUAL
cropResistant
|
0010302430000000 |
Análisis de Código
Risk Score
74/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Banking
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Microsoft
• Método: Suplantación de identidad a través de una página de inicio de sesión falsa
• Exfil: Credenciales del usuario a través de la ofuscación de Javascript.
• Indicadores: Dominio no coincidente, presencia de un formulario de inicio de sesión.
• Riesgo: Alto
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://a#б
- https://тест
- https://a@b
- https://grouponedeals.com/js/usecure.bundle.js?v=c30c23a9-df52-49a9-a1d4-0790b6de4b9a
- https://a
- https://a/c%20d?a=1&c=3
- https://x
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain does not belong to Microsoft.
Impersonation
The site visually resembles the Microsoft login, making it appear legitimate.
JavaScript Obfuscation
Javascript obfuscation used to hide potentially malicious code.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Microsoft users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Banking
- 21 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Microsoft
Official Website
https://www.microsoft.com
Fake Service
Microsoft login
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attackers are using a phishing website to trick users into entering their Microsoft credentials (email/phone and password).
Secondary Method: Social Engineering
The site mimics the appearance of a legitimate Microsoft login page to build trust and deceive the user.
🌐 Indicadores de Compromiso de Infraestructura
🦠 Malicious Files
Main File
usecure.bundle.js?v=c30c23a9-df52-49a9-a1d4-0790b6de4b9a
File Size
🔬 JavaScript Deep Analysis
Operator Language
English (1%)
Sophistication Level
Basic
Total Code Size
371,8 KB
🔗 API Endpoints Detected
Other
6
🔐 Obfuscation Detected
- : Heavy
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
Main Drainer
usecure.bundle.js?v=c30c23a9-df52-49a9-a1d4-0790b6de4b9aFile Size
371KB
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Microsoft
https://hhelpdesk.ie/?r=87209375-dd2d-4b01-9f76-19271d3356fd
Abr 05, 2026
Microsoft
https://pessoleldept.com/?r=6b2cc31c-ddb6-400c-80d3-28671fce...
Mar 31, 2026
Microsoft
https://gdprlaw.co.uk/?r=6f900ecb-f8af-4c52-baff-66204623019...
Mar 30, 2026
Microsoft
http://humanres.in/?r=2ae1eb79-d77b-45e3-9cce-2c36bd88eca9&r...
Mar 26, 2026
Microsoft
https://sup0rt.ie/?r=abc696d6-acde-452c-9573-b7347bd36b3e&rg...
Mar 25, 2026
Scan History for grouponedeals.com
Found 2 other scans for this domain

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.