Phishing Analysis
Detailed analysis of captured phishing page
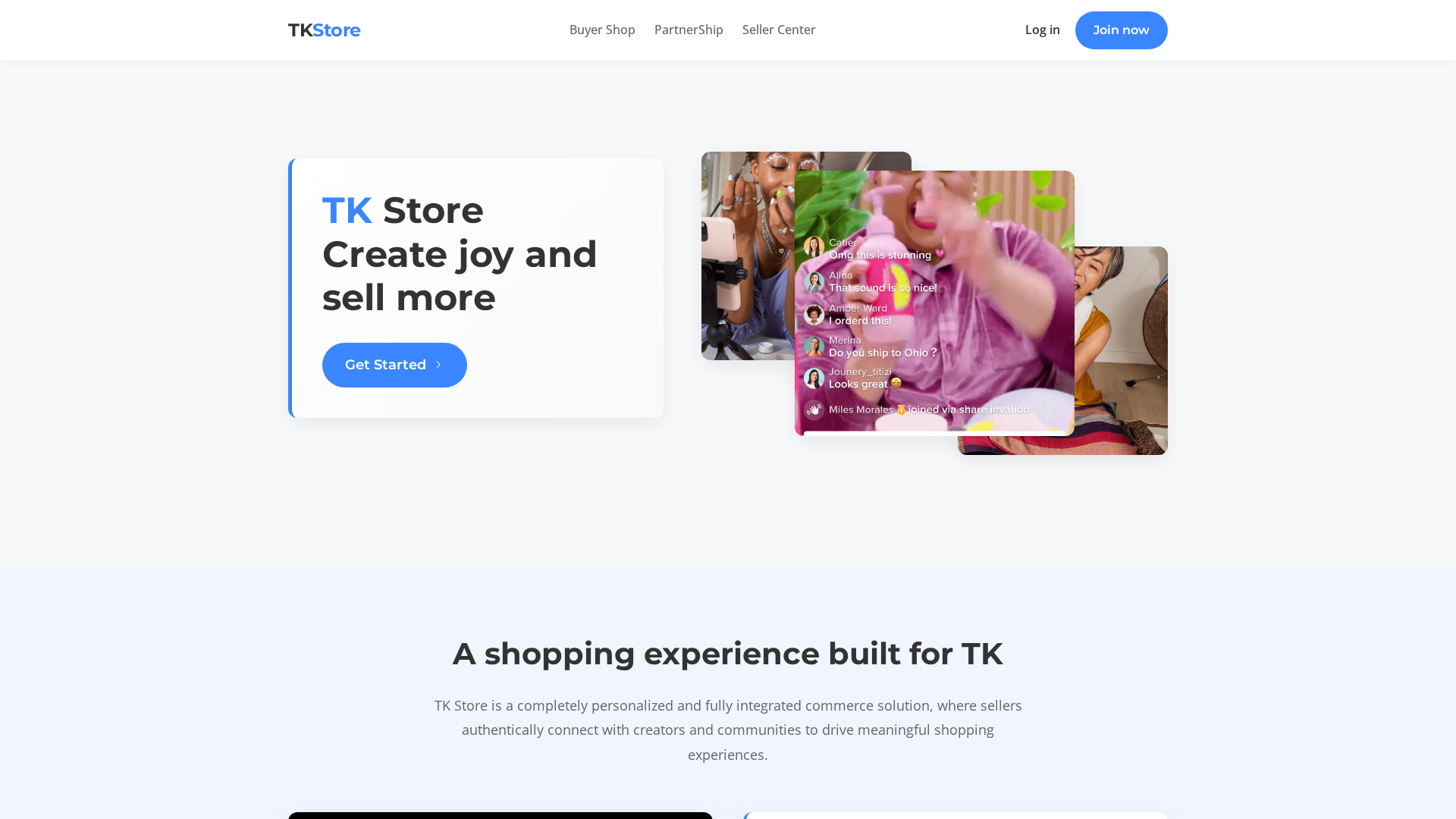
Captura Visual
Información de Detección
http://not8syq7.ridistrict.com/
Detected Brand
TK Store
Country
International
Confidence
100%
HTTP Status
200
Report ID
088fb64b-773…
Analyzed
2026-01-12 13:07
Final URL (after redirects)
https://not8syq7.ridistrict.com/
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1CE526032A051B53740C383F2AB302BAABBE0C2A7D693464595F8C35C5BD1D52DD2F62B |
|
CONTENT
ssdeep
|
192:CSZeRQxgRj5sMiDM6Mc+TfyKTpfT4I40STp4MnloFnxpq/+1qp31qPaWI:CJREaP6McWa6trZyhnixpaUk0XI |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ec6e9393c9693264 |
|
VISUAL
aHash
|
fff3c191f9ffe7cf |
|
VISUAL
dHash
|
5b262723230c861e |
|
VISUAL
wHash
|
fde38181f1ff0103 |
|
VISUAL
colorHash
|
07400080000 |
|
VISUAL
cropResistant
|
5b262723230c861e,646e261fb7b5b757,ee77770404cc7131 |
Análisis de Código
Risk Score
85/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Kit de phishing para robo de credenciales
• Objetivo: Usuarios de TK Store internacionalmente
• Método: Formulario falso que roba credenciales de usuario
• Exfil: Datos enviados a través de JavaScript ofuscado
• Indicadores: Dominio no relacionado, JS ofuscado, detección de envío de formulario
• Riesgo: ALTO - Robo inmediato de credenciales
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- unicode_escape
- base64_strings
📡 API Calls Detected
- GET
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.