Phishing Analysis
Detailed analysis of captured phishing page
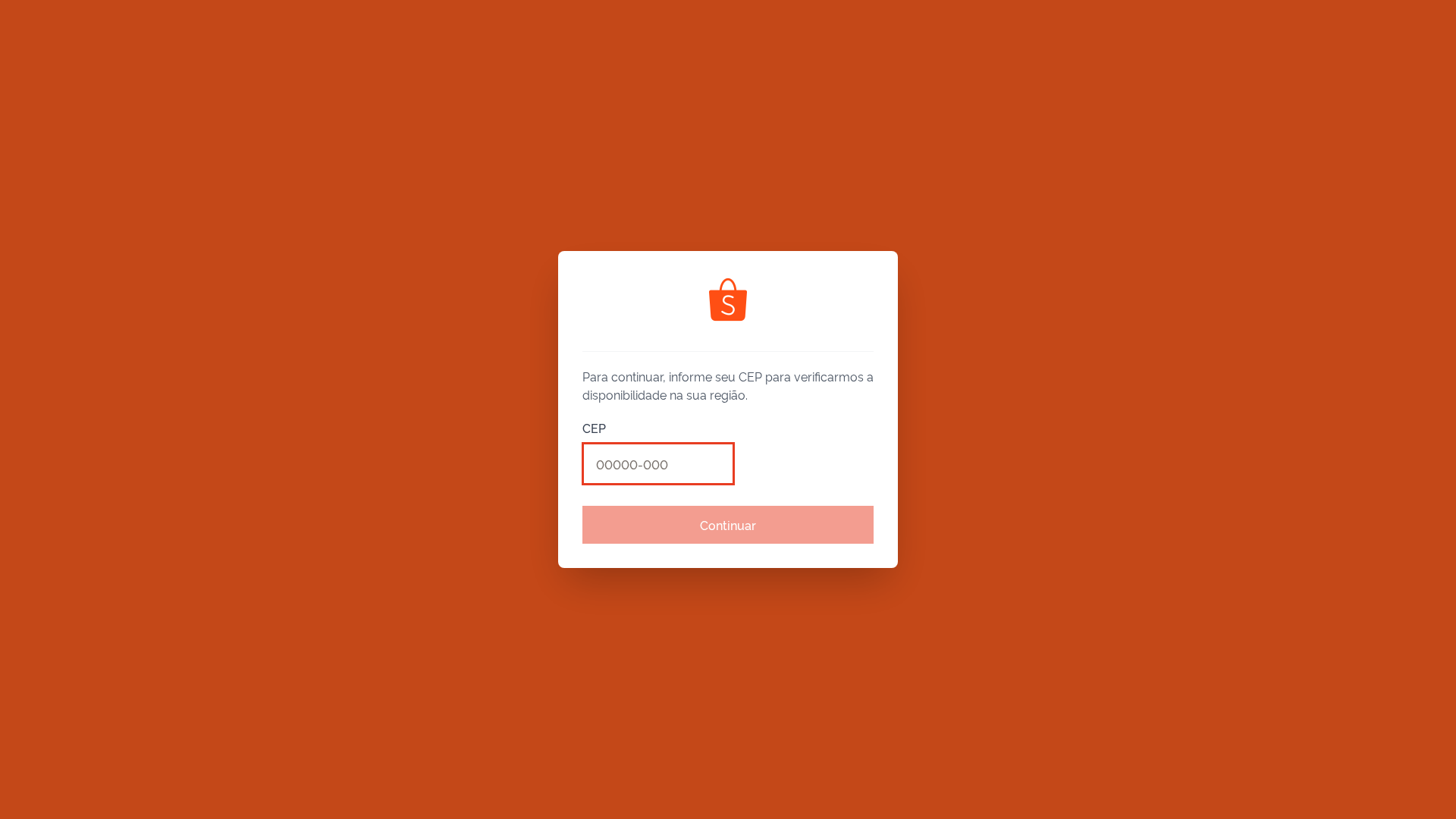
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T155D46CEA27A5942746D1818AA479461363397E0E5409C12CFF3EFDDB2A9CD84B07BF70 |
|
CONTENT
ssdeep
|
6144:E1D7ta3EIFJlNjFAW0rBotgnHYyuNFLzZOhfCCJHLTof3AS/MmlMfIAD2i04TnNP:eIFdXiotg4TsfCCJUA2Va5 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
99cc663399cccc99 |
|
VISUAL
aHash
|
0000181818180000 |
|
VISUAL
dHash
|
304cb2b2b2b24c30 |
|
VISUAL
wHash
|
00001818d8d8e4fc |
|
VISUAL
colorHash
|
00000038000 |
|
VISUAL
cropResistant
|
8a8ca2aaeaa833b2,304cb2b2b2b24c30 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Shopee en Brasil
• Método: Suplantación de identidad y envío de formularios
• Exfil: ppyxcanzwxsbsrokvpky.supabase.co
• Indicadores: Coincidencia de dominio, solicita CEP, JS ofuscado
• Riesgo: Alto
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- base64_strings
🎯 Kit Endpoints
- http://developers.facebook.com/policy/].
- https://scripts.converteai.net/652d55a2-1679-4d95-9c77-ce27d58a34ed/players/698a00856e05f1df8859a173/v4/player.js
- https://scontent.fbsb20-1.fna.fbcdn.net/v/t39.30808-6/329163340_1665584850557769_7952852576412662255_n.jpg?_nc_cat=109&ccb=1-7&_nc_sid=6ee11a&_nc_ohc=b-jDHW0yJegQ7kNvwF13tDF&_nc_oc=AdlSfTcWzldGer5kApqvcQnH-U80Slo2s5W2G3pgfzwpc5hkdqttwormwh9RCYlIiiXJqLTfjuvx109jZQN7nPms&_nc_zt=23&_nc_ht=scontent.fbsb20-1.fna&_nc_gid=aij5m0v7mEHZ7fNndPPt5g&oh=00_Afa2f5viMgJmqwb7vuqwH9EcbQBus9q3m7OJQbv0oF8iKw&oe=68D3ADF6
- https://i.ibb.co/QF8NYKFL/assets-task-01k4apnweffyd9n2vkabne2mn0-1757001052-img-0-removebg-preview-1.png
- https://vt-h-1.b-cdn.net
- https://scontent.fbsb20-1.fna.fbcdn.net/v/t39.30808-6/370157804_3458899707692320_7180734128752435178_n.jpg?_nc_cat=103&ccb=1-7&_nc_sid=6ee11a&_nc_ohc=aF8VtJwXZu4Q7kNvwGgVgUm&_nc_oc=AdmP6rJ8eHqOBfgJvt8-2lM0a_iNuHJvkQT_oRmRQ9VKTbz9JRUcMgb0x8WLPZ6TgQzgqQW5sI8bN8zfKjjJvP9T&_nc_zt=23&_nc_ht=scontent.fbsb20-1.fna&_nc_gid=bX3kQf2H7u9bM5eK8dHsqQ&oh=00_Afb2D3g5Jk8TwNRNKHuGJiNshD_Zk3yFvAg9qZl7LQiT7w&oe=68D3AF42
- https://vturb.com/en?via=player&utm_medium=powered_by_VTurb&utm_campaign=viral_player&utm_source=player&utm_content=want_to_optimize_your_vsl_en
- https://scontent.fbsb20-1.fna.fbcdn.net/v/t39.30808-6/482080356_1100022178479494_6625700935909497643_n.jpg?_nc_cat=104&ccb=1-7&_nc_sid=6ee11a&_nc_ohc=CEGBnChBYD8Q7kNvwGipFIU&_nc_oc=Adk8QaC2AccUq_QiH-_jxu__RXRkz18VjDFj6aB_4blNxEpEoK_cAxuMR_I9L8YaBkc1u7O6CLG74dHvPnHnL8JZ&_nc_zt=23&_nc_ht=scontent.fbsb20-1.fna&_nc_gid=RgOswtcaW9p59uGPnWhr3A&oh=00_AfamVaSfXdj2Mtg7J6-X-0E4MXGepKYmPNXMIcAL93h9cg&oe=68D3CD63
- https://i.ibb.co/prf2GtQT/Sem-nome-Story-1.webp
- https://player.vturb.com/v1/actions?companyId=${e}&playerId=`+t).then(t=
- https://connect.facebook.net/en_US/fbevents.js
- https://vturb.com/es?via=player&utm_medium=powered_by_VTurb&utm_campaign=viral_player&utm_source=player&utm_content=click_to_optimize_your_vsl_check_emoji_es
- https://www.clarity.ms/tag/
- https://${e}${this.token}/${t}/${r}/`+i}get
- https://scripts.converteai.net
- https://scripts.clarity.ms/0.8.54-beta/clarity.js
- https://i.ibb.co/Q7RXTRzN/a0e45d2fcc7fdab21ea74890cbd0d45e-2-1.png
- https://cdn.tailwindcss.com
- https://radix-ui.com/primitives/docs/components/${t.docsSlug}`;return
- https://opencep.com/v1/${y}.json`,{signal:AbortSignal.timeout(5e3)});if(x.ok){const
- https://freelogopng.com/images/all_img/1656181355shopee-icon-white.png
- https://www.facebook.com/tr/
- https://analytics.tiktok.com/i18n/pixel/events.js
- https://scontent.fbsb20-1.fna.fbcdn.net/v/t1.6435-9/44800709_193630054863696_2571333320239480832_n.jpg?_nc_cat=107&ccb=1-7&_nc_sid=6ee11a&_nc_ohc=uza0tkEIGroQ7kNvwF3cZDy&_nc_oc=Adk9_zktgMLioza307mY_Q8OAvt8FsdZpZ4kDT_C2rnGTmVWl7h5I_7lEu8KsDTk2oPj7eCWiEcpgsSjYzt8HHoz&_nc_zt=23&_nc_ht=scontent.fbsb20-1.fna&_nc_gid=Knkkcv09XN6RuBLdGRtYrg&oh=00_Afav5Jxl05tAnQZwr2lZwgYeQ6aZtTEOStsd1AXK7OS3BA&oe=68F5616E
- https://opencep.com/v1/${q}.json`,{signal:AbortSignal.timeout(5e3)});if(ve.ok){const
- https://images.converteai.net/{accountId}/players/{playerId}/thumbnail.jpg
- http://localhost
- https://play.google.com/store/apps/details?id=com.shopee.spx.driver.brazil&pcampaignid=web_share
- https://scontent.fbsb20-1.fna.fbcdn.net/v/t1.6435-9/186474682_10159246336497866_3964090686294664894_n.jpg?_nc_cat=108&ccb=1-7&_nc_sid=6ee11a&_nc_ohc=V38JwPIk5tAQ7kNvwHrYbRv&_nc_oc=AdkMuW3fNLq8GC4pKi3gN9cz9Q_NMfb7uQWXSYWnijs1eZgu_ml4Q8L_Cc41J7CJ3bieCMRV9UdbCr6xfcy0LSjH&_nc_zt=23&_nc_ht=scontent.fbsb20-1.fna&_nc_gid=9o5dBhAR2umxC6QHIUOYbw&oh=00_Afa1FYa_ZKaY6BNwt35B0F2eoGkKis0phGGmkFoiDiuuTQ&oe=68F56E22
- https://www.clarity.ms/tag/veuojjjutu
📡 API Calls Detected
- /api/send-notification
- GET
- https://www.google.com/ccm/geo
- /api/proxy/for4payments/pix
- https://play.google.com/store/apps/details?id=com.shopee.spx.driver.brazil&pcampaignid=web_share
- /api/push-subscriptions
- /api/app-users/save-cities
- /data/regions.json
- /api/app-users/save-profile
- /api/app-users/reached-delivery
- /api/app-users/login
- POST
☁️ Cloud Backend
- Supabase: ppyxcanzwxsbsrokvpky.supabase.co
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 245 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Impersonation
The site attempts to impersonate Shopee to collect user's postal code. This is likely the first step of a larger phishing attempt. The use of JavaScript obfuscation and Supabase endpoints suggests more complex behavior.
Secondary Method: Data Harvesting
The attacker likely intends to use the collected postal codes for fraud or identity theft.
🌐 Indicadores de Compromiso de Infraestructura
🦠 Malicious Files
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Light
- : None
- : Light
- : Moderate
- : Heavy
- : Light
- : Moderate
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
clarity.jsSimilar Websites
Pages with identical visual appearance (based on perceptual hash)