
Phishing Analysis
Detailed analysis of captured phishing page
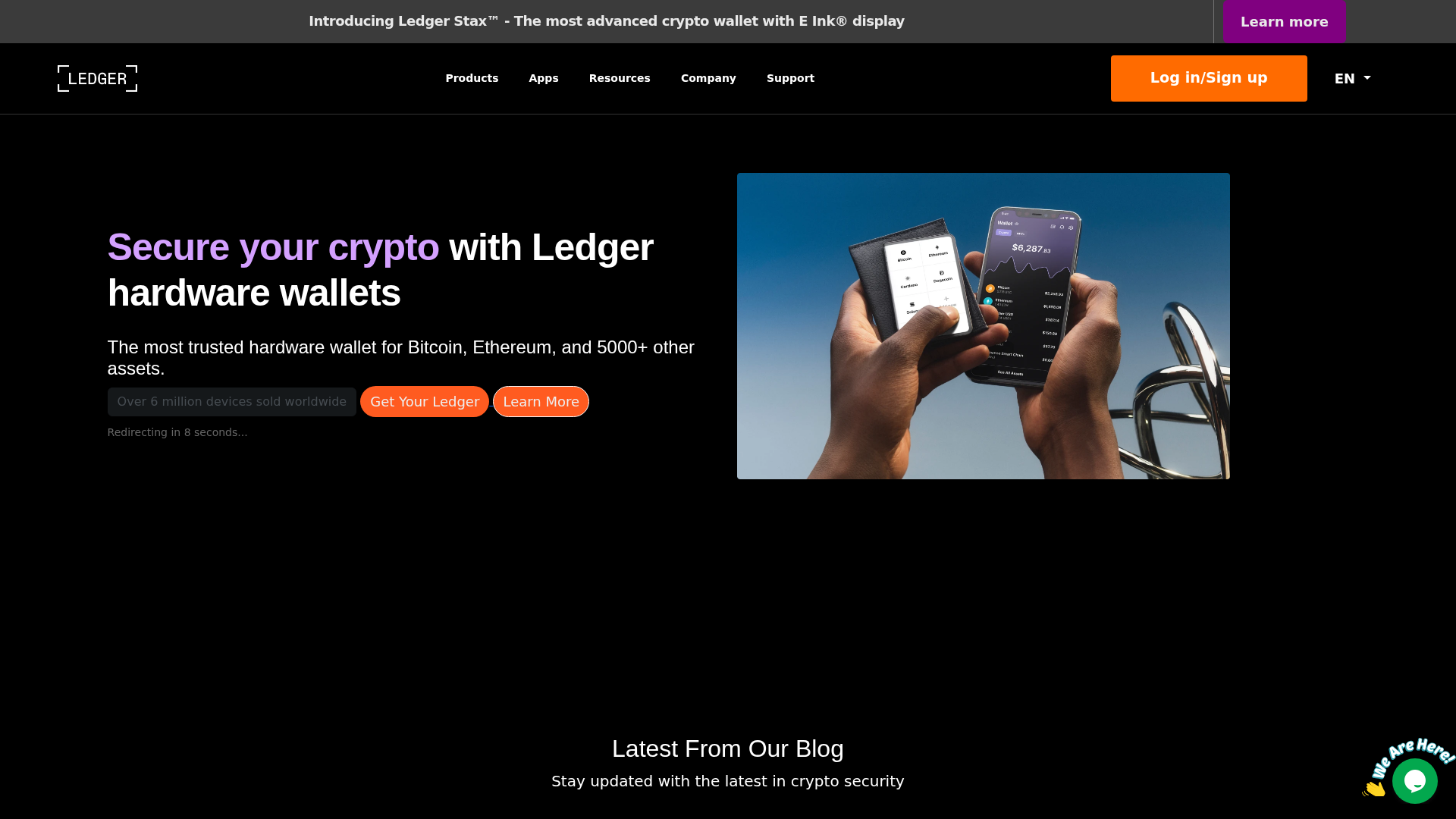
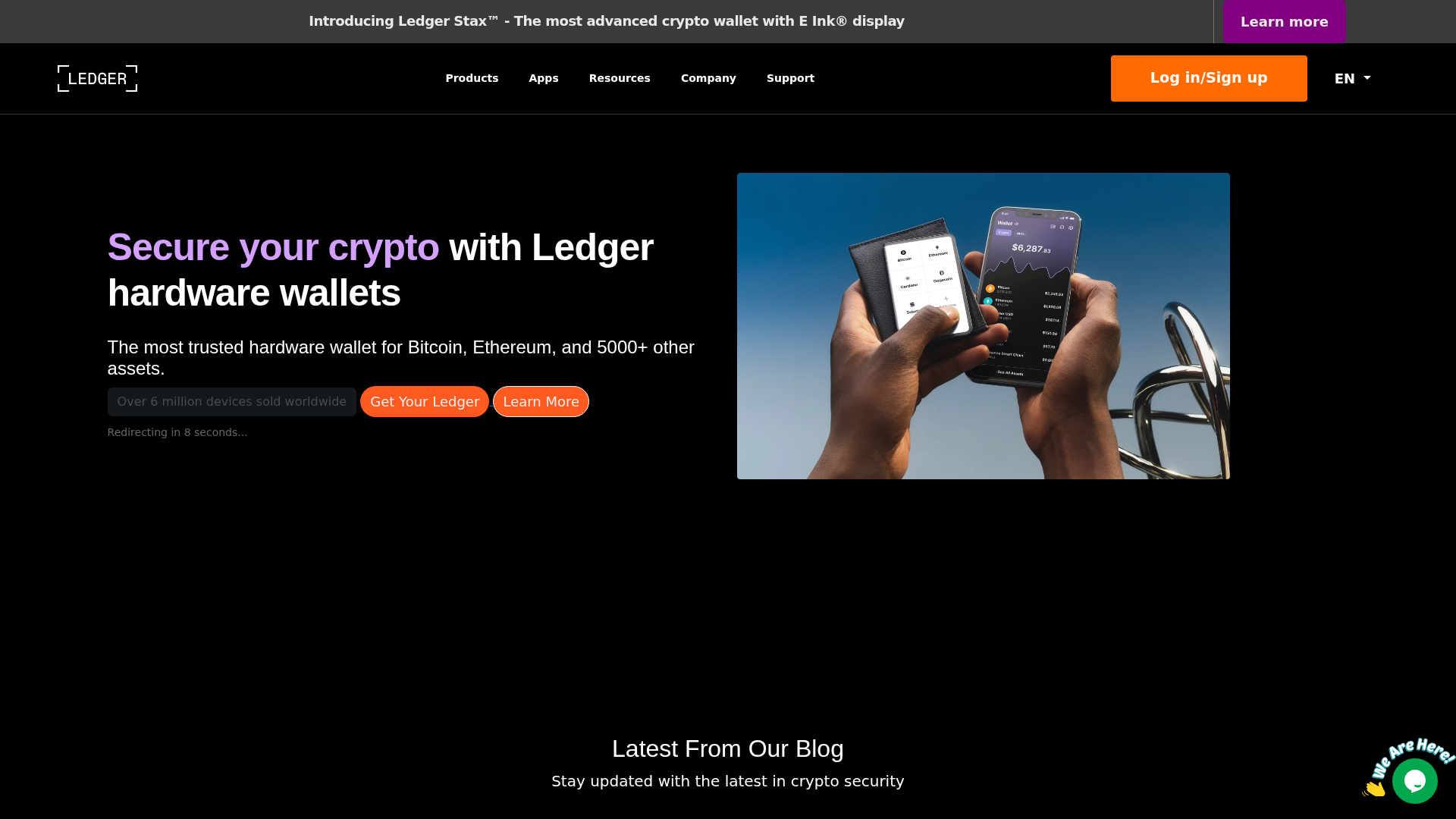
Captura Visual
Información de Detección
https://www.login-ledgger-load-io-frame.vercel.app/
Detected Brand
Ledger
Country
International
Confidence
100%
HTTP Status
200
Report ID
0d890a6c-5e6…
Analyzed
2026-03-19 05:16
Final URL (after redirects)
https://login-ledgger-load-io-frame.vercel.app/
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T11132C27064C6373F829602D5DBA06F5AB3D34242D52A060A96F1924FDEC7FC0DC5EA6D |
|
CONTENT
ssdeep
|
96:T3Ch6qh17Wiuv/GW/ww/GXfYGCCmG1IUndQGkt6/uaT6yd6yY+SdAubfeK2FVetY:TCPuNi0FR+SdAubWK2wtrr83Fxv |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
91956c6d99d1ea92 |
|
VISUAL
aHash
|
fb026e7e0e000001 |
|
VISUAL
dHash
|
661e98d858005031 |
|
VISUAL
wHash
|
ff0efefe2e000019 |
|
VISUAL
colorHash
|
30401008080 |
|
VISUAL
cropResistant
|
0000000000000204,64d4848082828180,661e98d858005031 |
Análisis de Código
Risk Score
85/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Ledger
• Método: Suplantación de identidad
• Exfil: Desconocido, probablemente robo de credenciales.
• Indicadores: Alojamiento gratuito, logotipo de la marca, ofuscación de JavaScript.
• Riesgo: Alto
🔒 Obfuscation Detected
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- base64_strings
📡 API Calls Detected
- GET
- POST
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Free Hosting
The domain is hosted on vercel.app which is a free hosting service commonly abused by phishers.
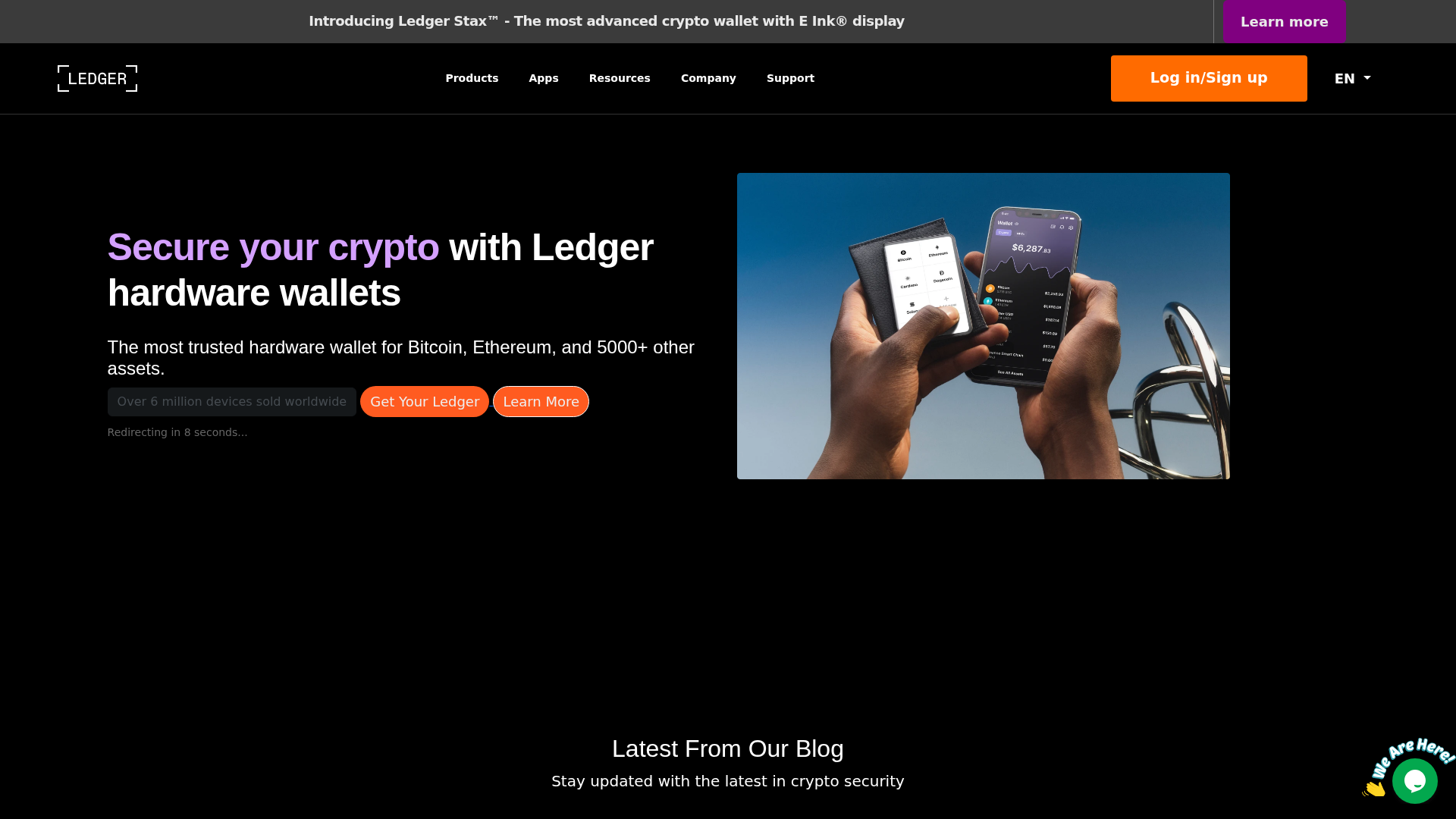
Brand Impersonation
The website attempts to mimic the appearance of Ledger.
Obfuscation
Javascript obfuscation is detected, often used to hide malicious functionality.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Ledger users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 16 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Ledger
Official Website
https://www.ledger.com/
Fake Service
Ledger hardware wallet
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The phishing site is designed to steal user credentials. It likely redirects to a login page or uses a form to collect email addresses and passwords.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
login-ledgger-load-io-frame.vercel.app
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Ledger
http://www.login-ledgger-load-io-gateway.vercel.app/
Abr 03, 2026
Ledger
https://start-ledger-com-encryption.vercel.app/
Mar 20, 2026
Ledger
http://start-ledger-com-encryption.vercel.app
Mar 19, 2026
Ledger
https://www.login-ledgger-load-io-gateway.vercel.app/
Mar 19, 2026
Ledger
https://login-ledgger-load-io-gateway.vercel.app/
Mar 18, 2026

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.