
Phishing Analysis
Detailed analysis of captured phishing page
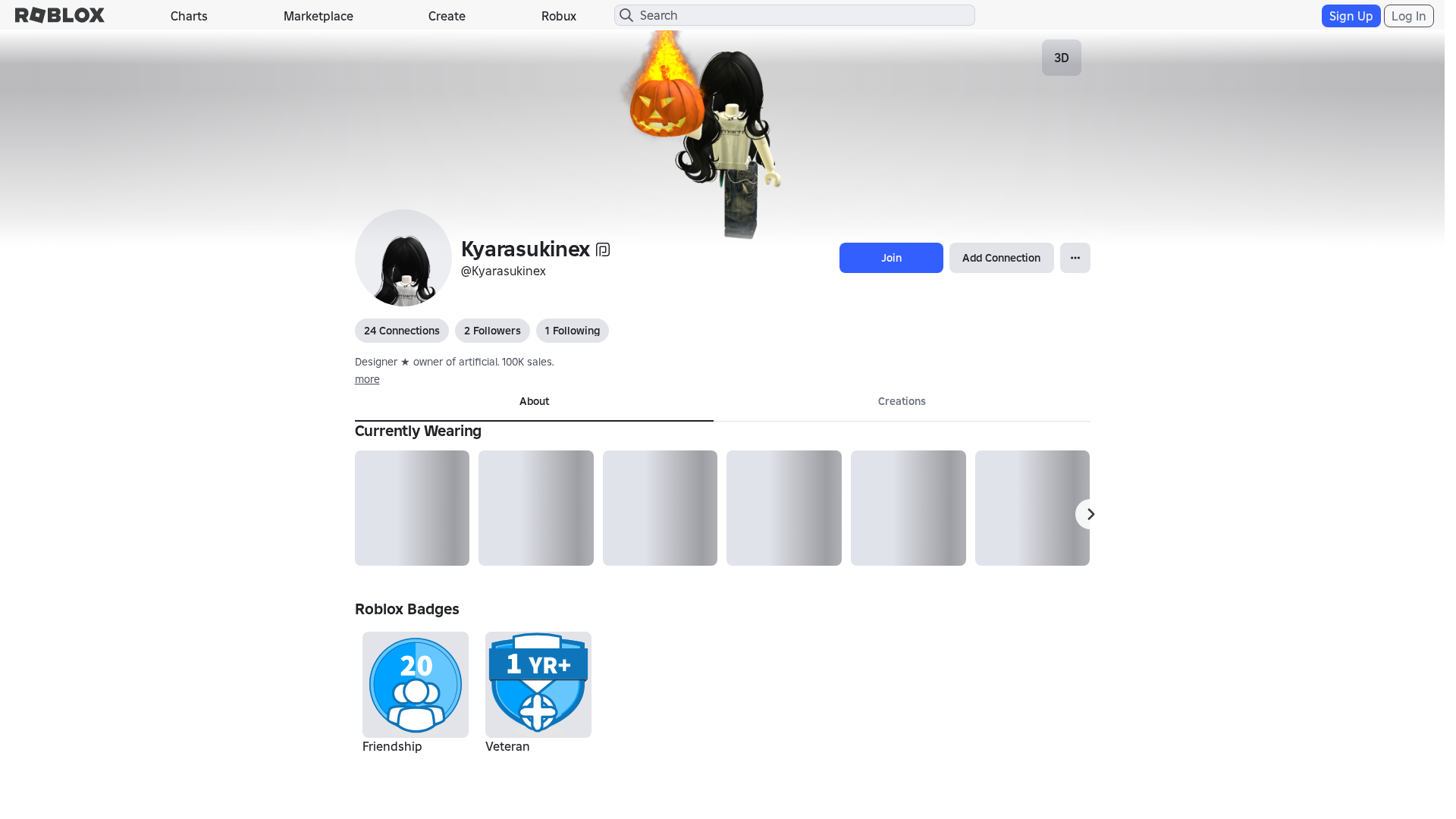
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T11B73747291502437617B79D9F164B71AA2D3C74FCA8246E1A2FC939A0FDACE1F81740E |
|
CONTENT
ssdeep
|
1536:3uZWbiXWn0OYp4J+tx8jN1LMzcrqKanJb+R8DMtjetK3YuO8eN9rnZEHFHcHwHDF:lmXWAxZFwXIuO/Cl8QjvqqqqqqqUy+4q |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b0471363c798ecbc |
|
VISUAL
aHash
|
0000d3ffc3c3dfff |
|
VISUAL
dHash
|
c8c8b63096963032 |
|
VISUAL
wHash
|
0000c3dfc3c3cfdf |
|
VISUAL
colorHash
|
07001008180 |
|
VISUAL
cropResistant
|
c8c8b63096963032 |
Análisis de Código
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /catalog/13693325067
- https://www.roblox.com/catalog/86499716/null
- https://www.roblox.com/catalog/15093053680/null
- /catalog/86499716
- https://www.roblox.com/catalog/104249641306144/null
- https://www.roblox.com/catalog/86499666/null
- /catalog
- /catalog/11573370910
- https://www.robiox.com.ps/info/blog?locale=en_us
- /login?returnUrl=6398207532123858
- https://www.roblox.com/catalog/619537468/null
- https://www.roblox.com/catalog/124604403583635/null
- /catalog/139607718
- https://www.roblox.com/catalog/13693325067/null
- https://www.roblox.com/catalog/15229649423/null
- https://www.roblox.com/catalog/86499698/null
- https://www.roblox.com/catalog/17022271708/null
- https://www.roblox.com/catalog/100969892154368/null
- /catalog/619537468
- https://www.roblox.com/catalog/619536621/null
- https://www.roblox.com/catalog/11573370910/null
- /catalog/86499666
- https://www.roblox.com/catalog/15113993645/null
- /catalog/86499698
- /catalog/619536621
- https://www.roblox.com/catalog/139607718/null
- https://www.roblox.com/catalog/139862873308551/null
- https://www.robiox.com.ps/catalog?CatalogContext=1&Keyword=
- https://www.roblox.com/catalog/14399925877/null
📡 API Calls Detected
- babylonjs
- /api/shorten
- https://ro.blox.com/Ebh5?
- /api/pageview
- https://apis.
- get
- https://help.roblox.com/hc/articles/30428367965460
- GET
- https://kyxn.dev/api/shorten
- https://kyxn.dev/api/shorten/TKvzwH
- POST
- https://kyxn.dev${e.endpoint}
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 210 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 210 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for roblx.me
Found 9 other scans for this domain
