Phishing Analysis
Detailed analysis of captured phishing page
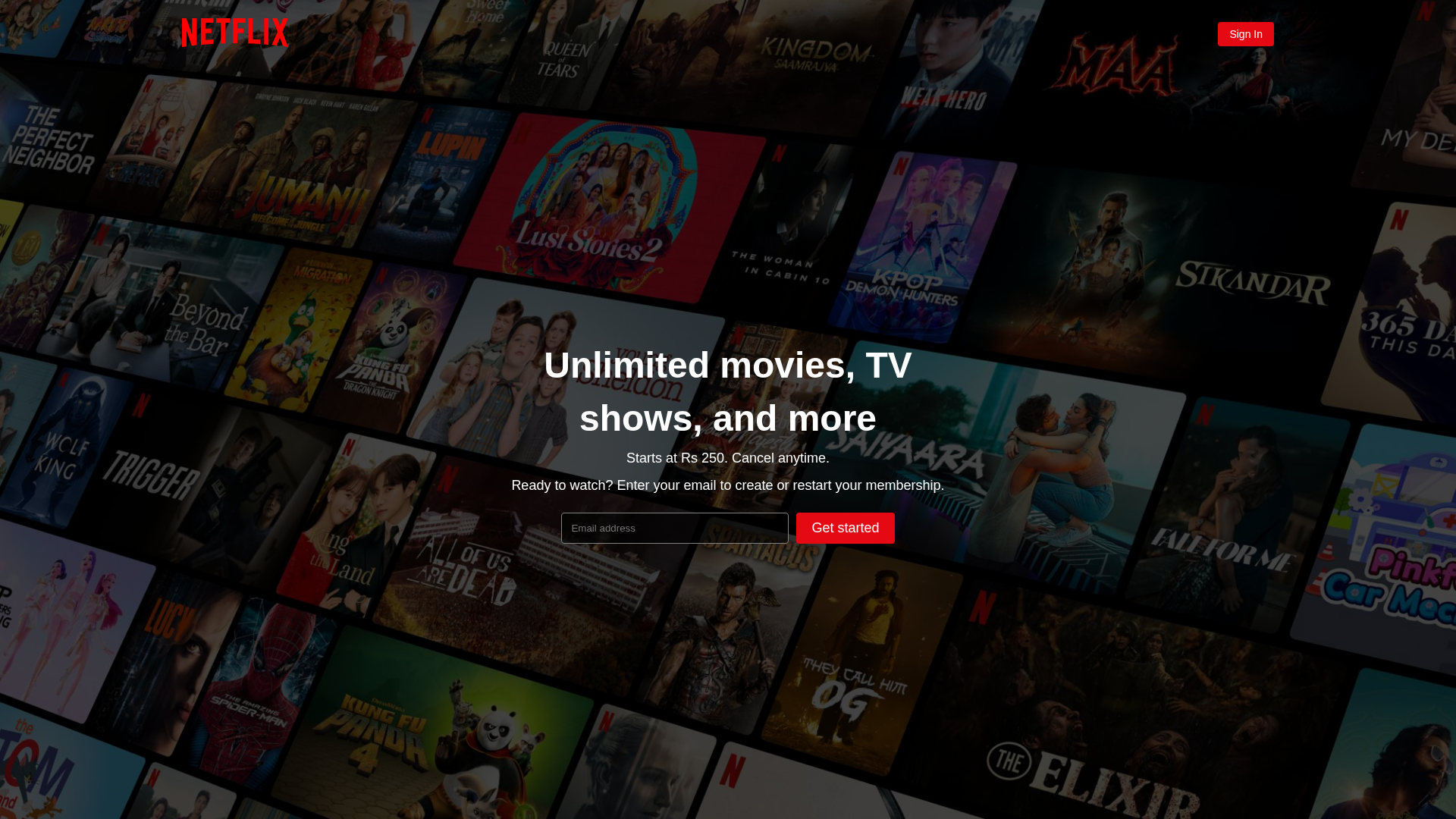
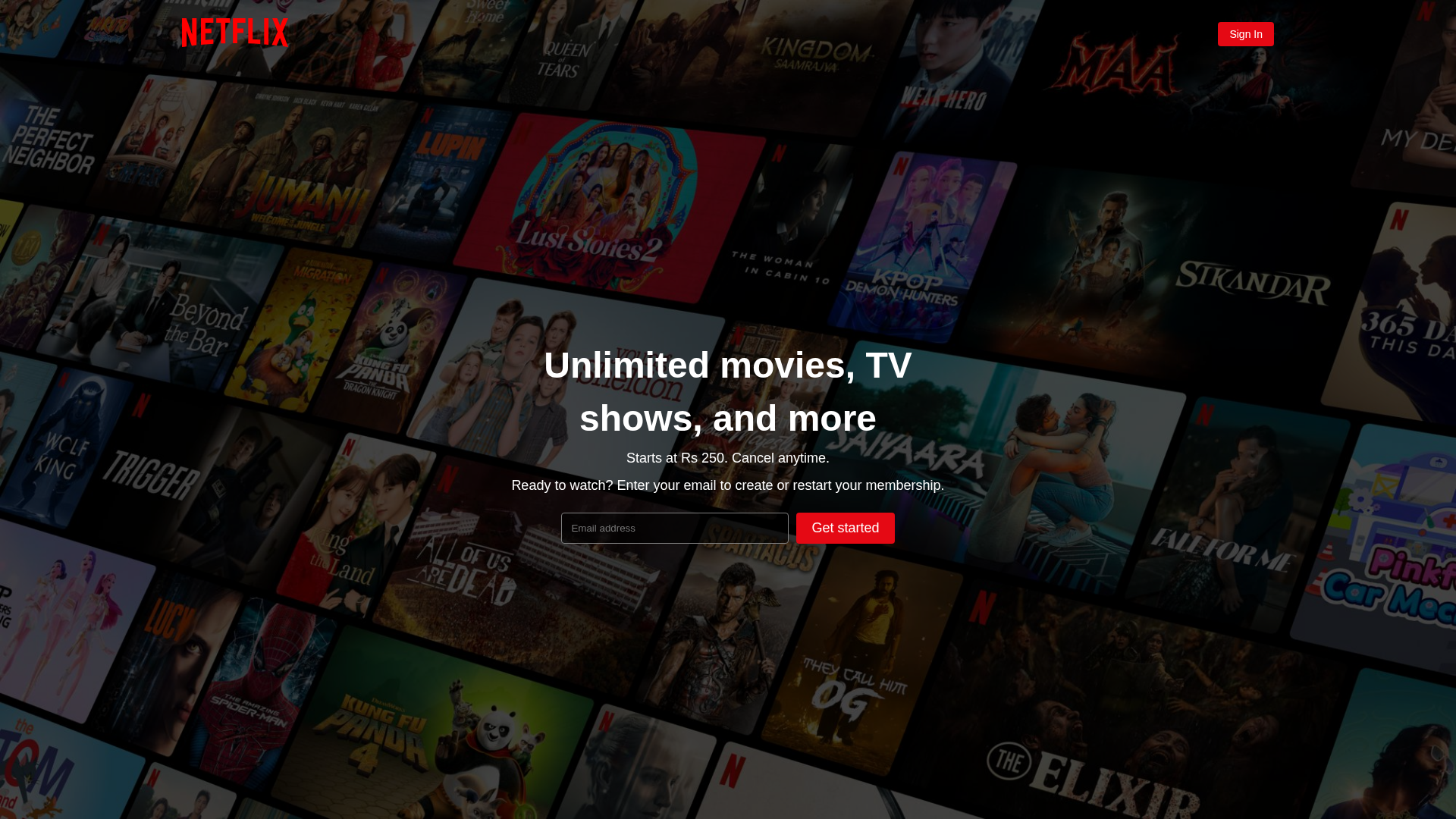
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T160B1AEF06052AB2B4293C2E11733ABAF33E6D68DCAD6171256FC539A0BE7C52FC15095 |
|
CONTENT
ssdeep
|
96:noYzDnfAeHnWnWn7ETnenynin/4nG6nMnnrwqEGnfAe+lBpk:oYPnf0e6FGnf6fpk |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ce4071398ce7b336 |
|
VISUAL
aHash
|
4010a07c3f89a0b8 |
|
VISUAL
dHash
|
88a129e1755b4371 |
|
VISUAL
wHash
|
60d0b0fc3fb9a8b8 |
|
VISUAL
colorHash
|
39401008000 |
|
VISUAL
cropResistant
|
88a129e1755b4371 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Netflix
• Método: Suplantación de identidad a través de un sitio web similar en alojamiento gratuito.
• Exfil: Direcciones de correo electrónico
• Indicadores: Alojamiento gratuito, logotipo de la marca, formulario.
• Riesgo: Alto
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
🏢 Análisis de Suplantación de Marca
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker attempts to collect the user's email address under the guise of Netflix using a landing page to create a subscription or restart an existing one.
Secondary Method: Social Engineering
The website uses Netflix branding to deceive the user into providing personal information.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🔬 JavaScript Deep Analysis
🔐 Obfuscation Detected
- : None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for codestudiocore-source.github.io
Found 1 other scan for this domain