
Phishing Analysis
Detailed analysis of captured phishing page
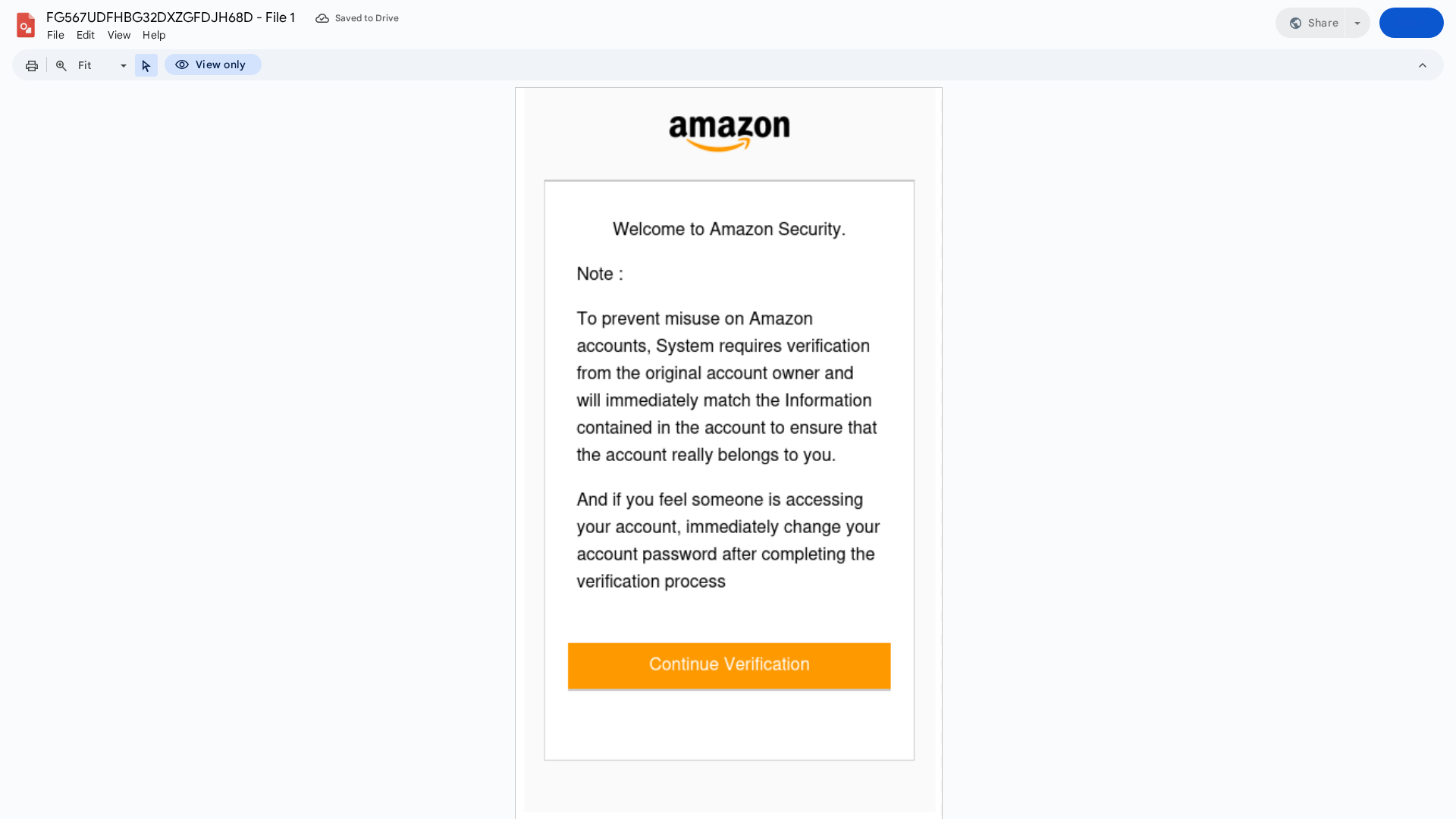
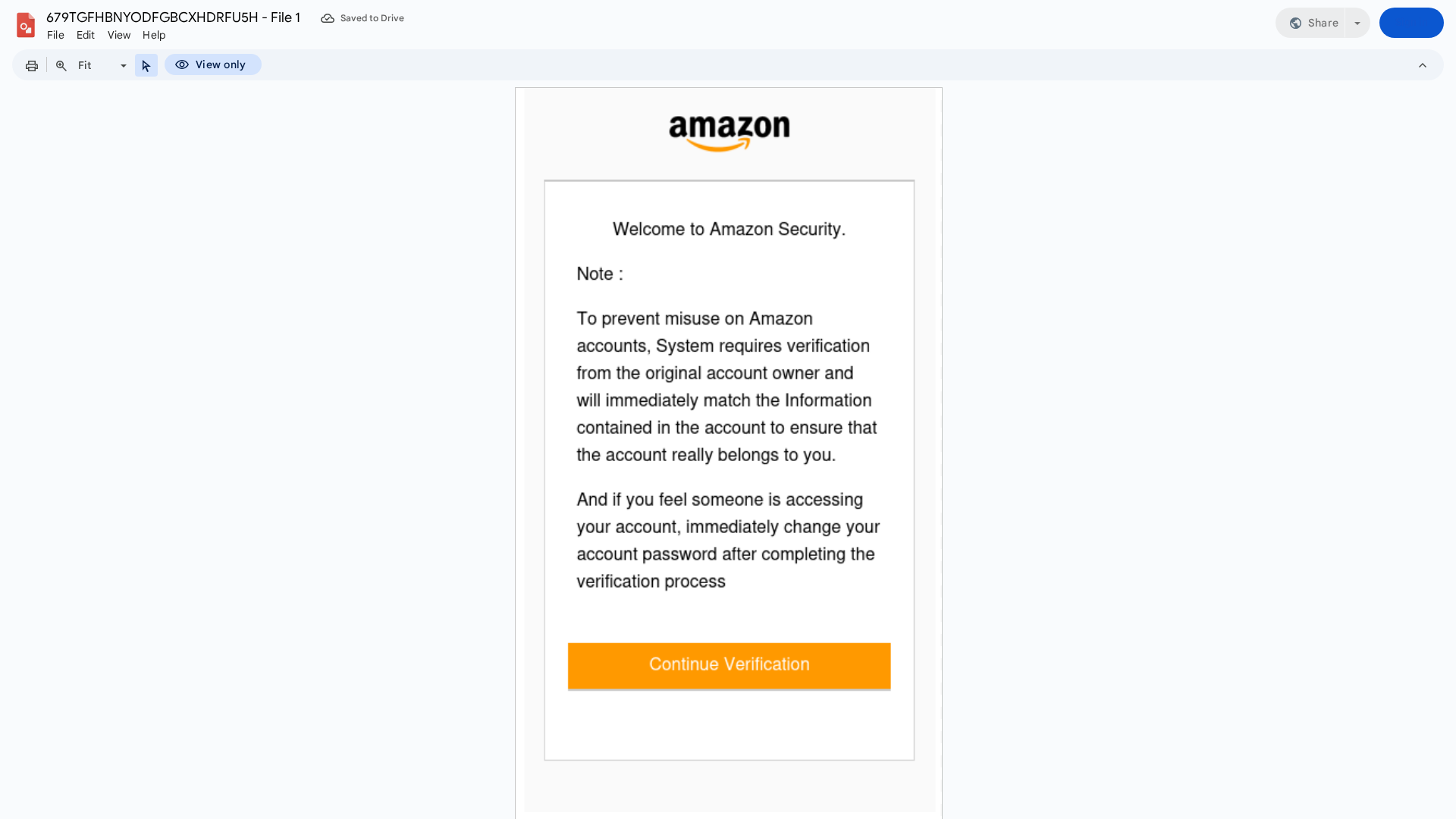
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C1130233C0132132525B52E5F8A0775A2293C32EDF4708851B7CDB913BEBDAA7987A5D |
|
CONTENT
ssdeep
|
768:4XRd/CNiaL13/9DJ6a+co6v+c6o4IE/Irb5dEoGEqOzVWsPk6TRC1mX6nwCTT:kRdaNhL13/tJ6fco6Gc6o4L/Irb5dEoI |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b7155d1515159d55 |
|
VISUAL
aHash
|
26e7ffe7e7e7e7ff |
|
VISUAL
dHash
|
ca0d484c4c4c4c04 |
|
VISUAL
wHash
|
00e3c3c3c3c3c3fb |
|
VISUAL
colorHash
|
07000030000 |
|
VISUAL
cropResistant
|
ca0d484c4c4c4c04 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Clientes de Amazon
• Método: Suplantación de identidad a través de Google Docs
• Exfil: Desconocido (potencialmente credenciales)
• Indicadores: Dominio no coincidente, suplantación de identidad, urgencia
• Riesgo: Alto
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- base64_strings
📡 API Calls Detected
- td
- kbd
- h2
- hr
- ol
- a
- p
- GoogleDocs
- footer
- POST
- /debug/fetchmediafromfilestorage?mediaId=
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 970 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Brand Impersonation
The attacker creates a document on a legitimate hosting platform (Google Docs) and mimics the branding and messaging of Amazon to trick users into providing their credentials or clicking a malicious link.
Secondary Method: Spear Phishing
The attacker may have targeted the user specifically, making the communication look more authentic.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for docs.google.com
Found 10 other scans for this domain
-
https://docs.google.com/drawings/d/1sj4whBVnBiYbBM...
https://docs.google.com/drawings/d/1yLlUaHnTsx9QSl...
https://docs.google.com/drawings/d/1HkX3Q8Vmr0bSej...
https://docs.google.com/drawings/d/1RCgegAUJGIZOBP...
https://docs.google.com/drawings/d/18Q2Qo6ik56ER5d...
https://docs.google.com/drawings/d/1LyvbqGTLtDzf81...
https://docs.google.com/drawings/d/1QKtwKh3JuUaEHs...
https://docs.google.com/drawings/d/1fL_fne4OgKiCLk...
https://docs.google.com/drawings/d/16f_LOTLDkqMT1D...
https://docs.google.com/drawings/d/11hOe-NpeBFsnAL...
