
Phishing Analysis
Detailed analysis of captured phishing page
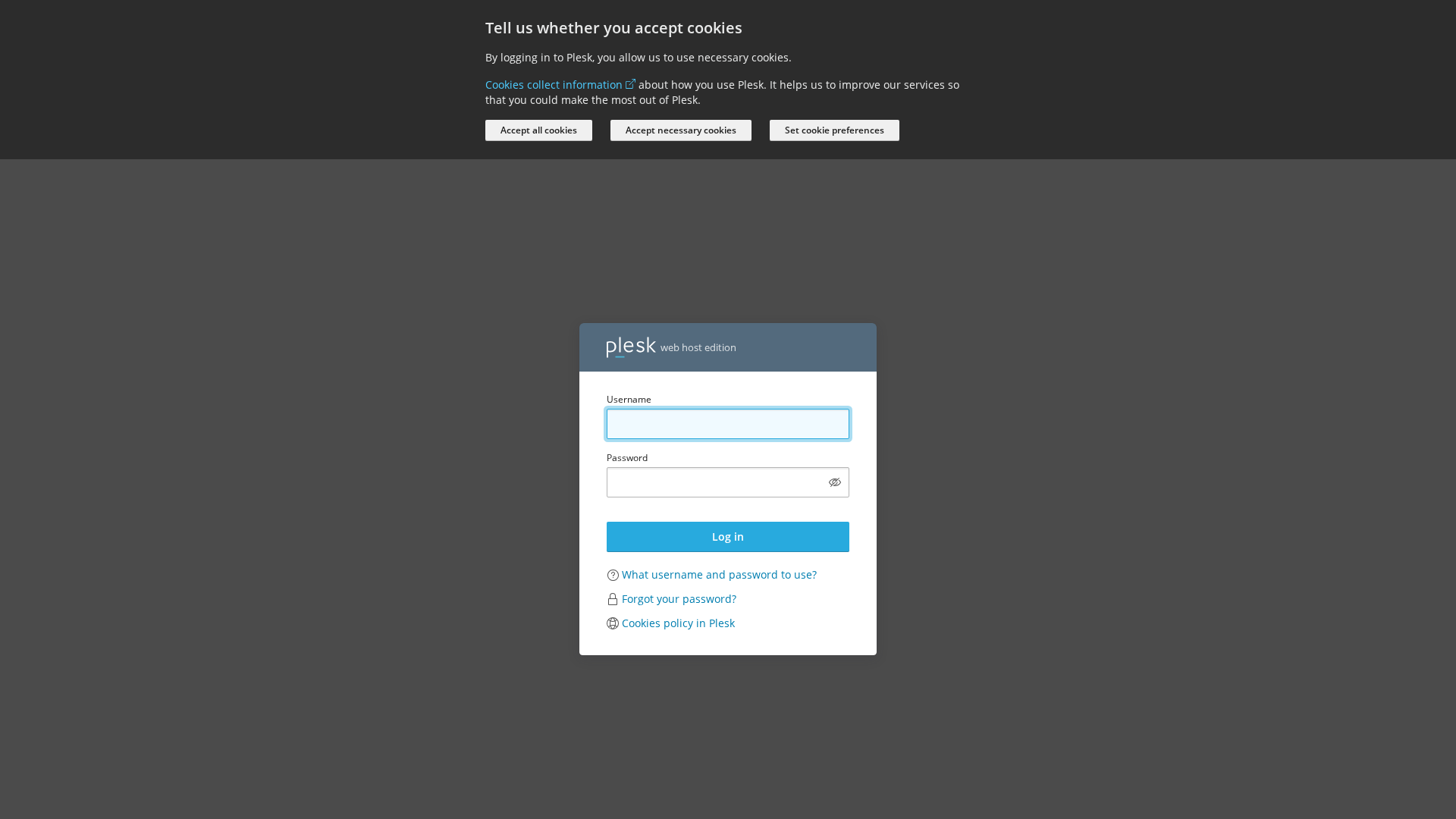
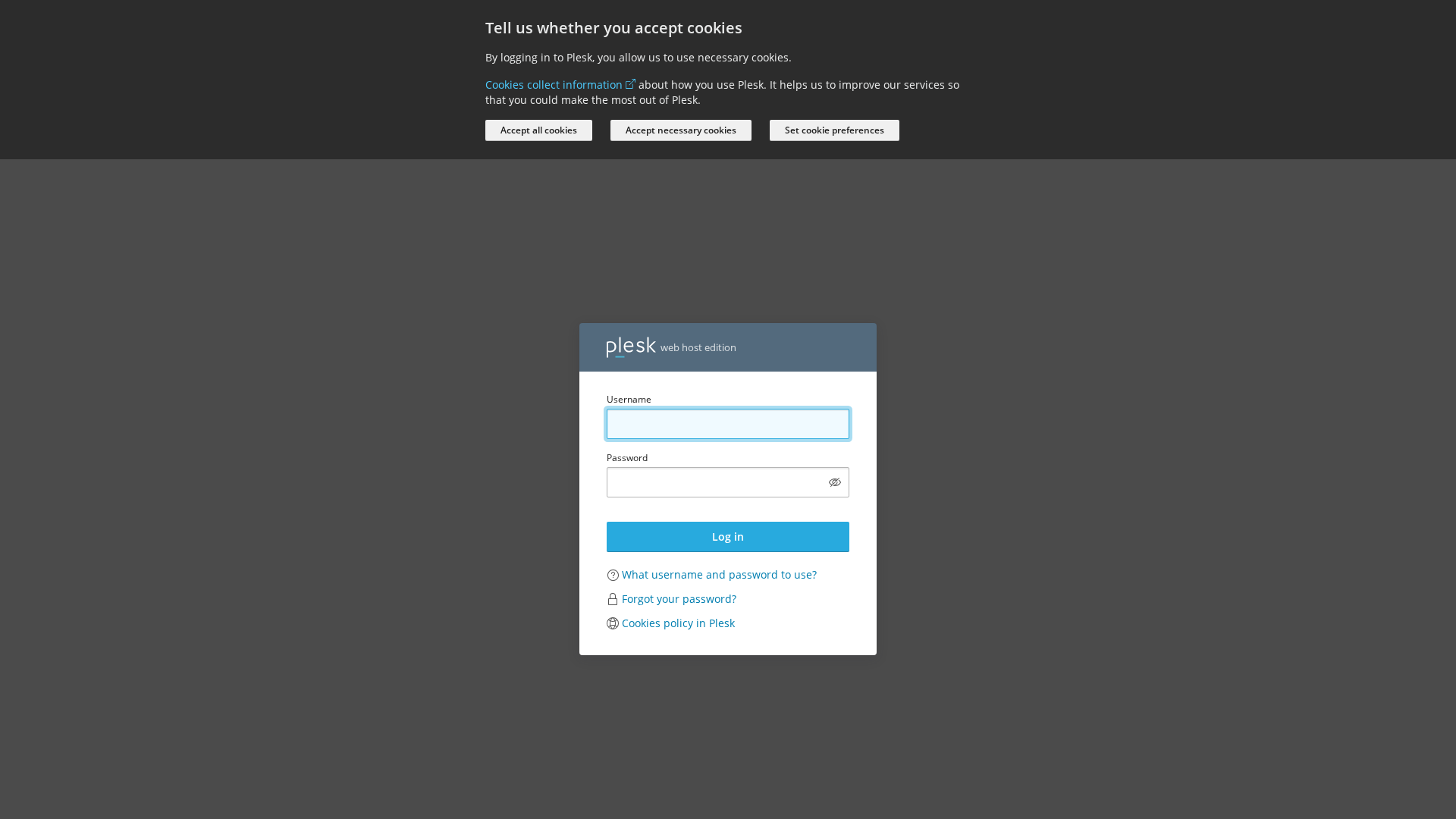
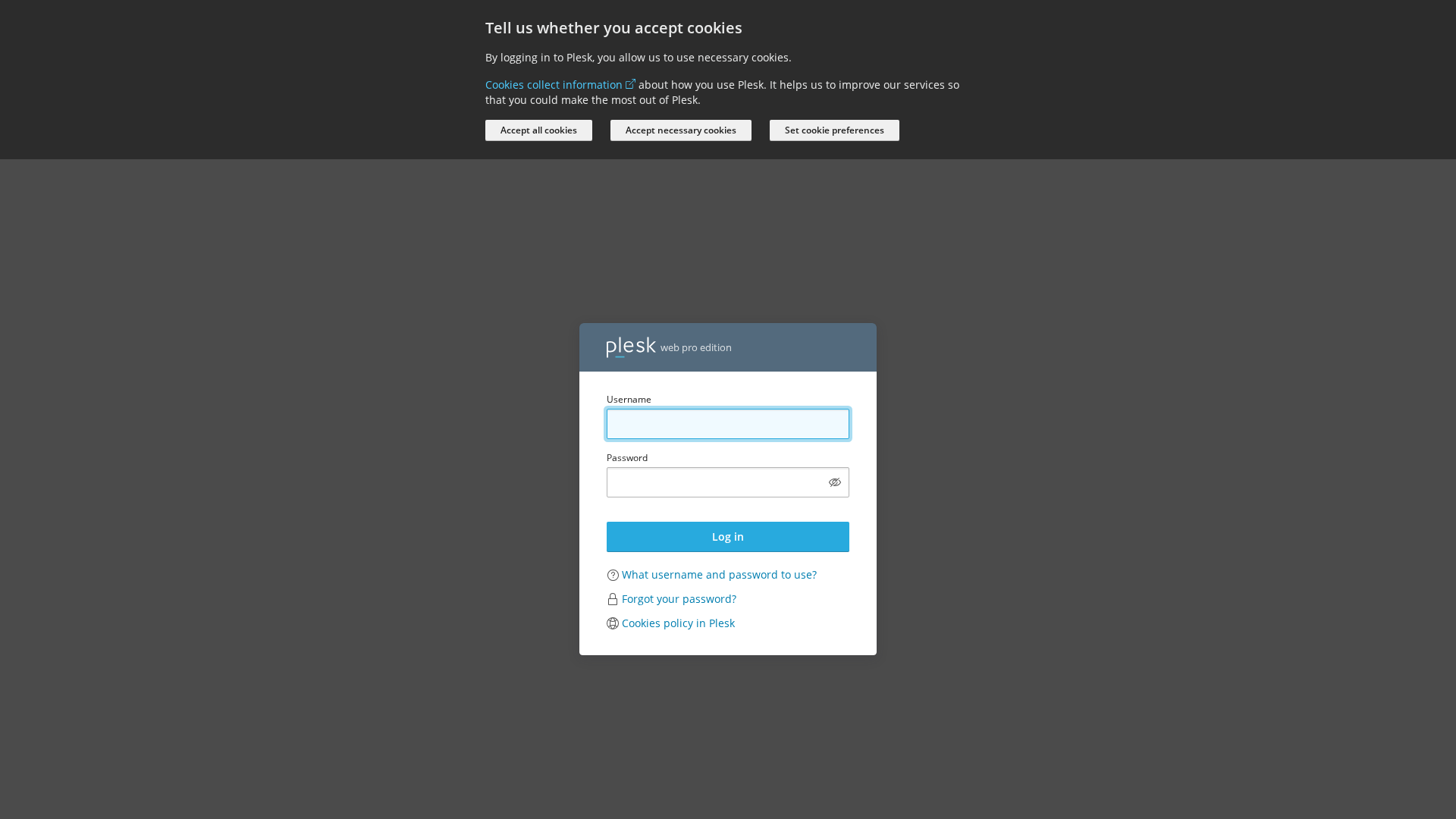
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T180F10C32644CEC3723235BD1B492B715E2D6C66ECA421610D6BC839D0FFBEE2E44665B |
|
CONTENT
ssdeep
|
192:EHVLJlkYMHSTCuCgEXCBdDxe8LTjKkrfjg1r9j3rr7dv:WVLJlkR+3jECxe8LTjKkrfjg1r9j3rr9 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc6666cc5c763233 |
|
VISUAL
aHash
|
0018001818181800 |
|
VISUAL
dHash
|
62724cb2b2b2b24c |
|
VISUAL
wHash
|
00183838fcfcfcfc |
|
VISUAL
colorHash
|
07007000080 |
|
VISUAL
cropResistant
|
e2a2e28033b2b8b8,62724cb2b2b2b24c |
Análisis de Código
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- ${(0,m.default)(`/admin/report/download/file/${encodeURIComponent(n.file)}`)}
- /login_up.php?modals[cookie-policy-preferences]=true
- https://support.plesk.com/hc/en-us/articles/12377667582743-How-to-log-in-to-Plesk-
- /logout.php
- log-in
📡 API Calls Detected
- /admin/copilot/stat
- /admin/copilot/gen-answer
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 71 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 71 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for survey-ppl-log.com
Found 1 other scan for this domain
