
Phishing Analysis
Detailed analysis of captured phishing page
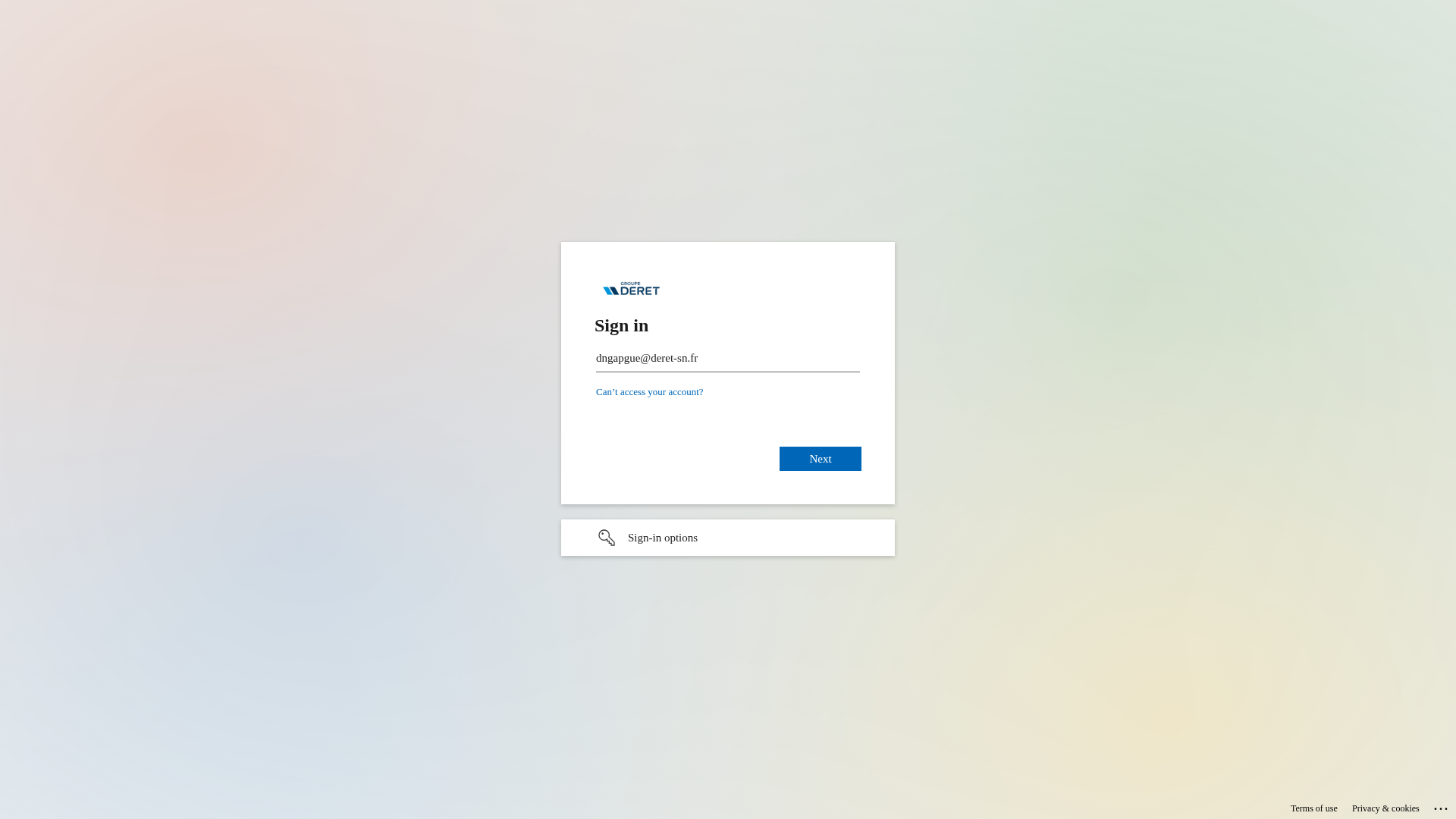
Captura Visual
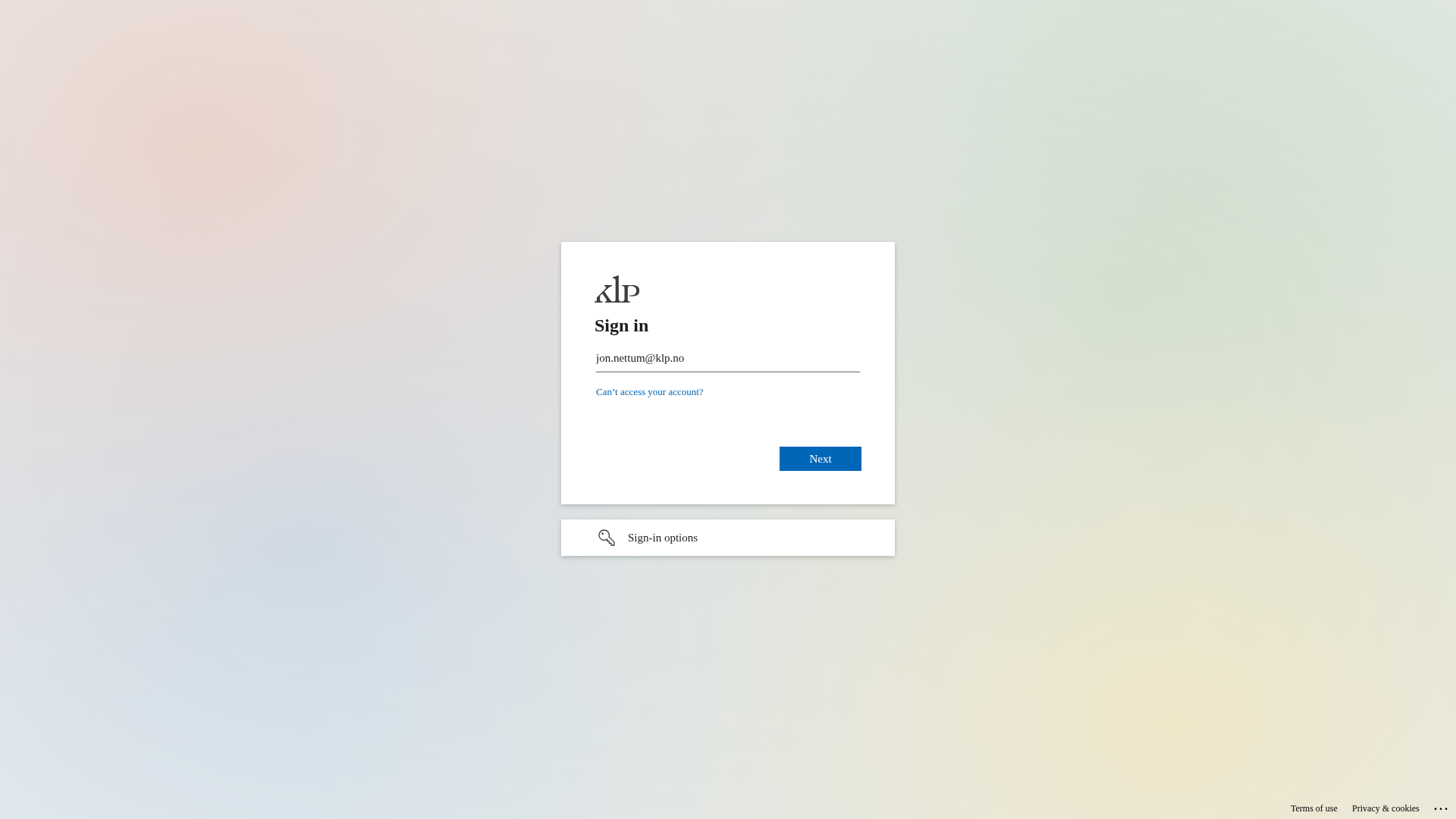
Información de Detección
https://multi-factor.link/3XaU00WDGY80ng
Detected Brand
KLP (Likely Impersonation)
Country
International
Confidence
100%
HTTP Status
200
Report ID
265defae-64b…
Analyzed
2026-03-19 10:33
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T152D1EE7060409D3B4283C7D8B3B96B9F3394C346EA97565A67F4C35C1EE3E16CC1A226 |
|
CONTENT
ssdeep
|
96:DIpkCGTHRPy9OkrwkMxs39TbJG9KjsWsjOI0U2gs0sjO5OVJQ6Q6ynQjNsjOO:ZsOk8A9TbJG9a2ZOVJQyyQjq |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9c497326cc99d966 |
|
VISUAL
aHash
|
18001818191f0f9f |
|
VISUAL
dHash
|
7161713331727d38 |
|
VISUAL
wHash
|
191818181f1f1fff |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
7161713331727d38 |
Análisis de Código
Risk Score
70/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Clientes de KLP
• Método: Recolección de credenciales
• Exfil: Desconocido, probablemente a atacantes.
• Indicadores: Dominio malicioso, formulario de inicio de sesión, suplantación.
• Riesgo: Alto
🎯 Kit Endpoints
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-416676562927&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-8024-21bc5137cc6d&protectedtoken=true&domain_hint=klp.no&nonce=899285250283.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=am9uLm5ldHR1bUBrbHAubm8#
- https://login.microsoftonline.com/common/login#
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-487191339135&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-8136-21bc5137cc6d&protectedtoken=true&domain_hint=klp.no&nonce=829204807123.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=am9uLm5ldHR1bUBrbHAubm8#
- https://passwordreset.microsoftonline.com/?ru=https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-399058842550&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-6822-21bc5137cc6d&protectedtoken=true&domain_hint=klp.no&nonce=163656193502.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=am9uLm5ldHR1bUBrbHAubm8#
📊 Desglose de Puntuación de Riesgo
Total Risk Score
95/100
Contributing Factors
Domain Mismatch
The domain 'multi-factor.link' is completely unrelated to the intended brand (KLP).
Requesting Sensitive Information
The page is requesting an email address as a login credential.
Impersonation
The page attempts to impersonate KLP's login page.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Two-Factor Authentication Stealer
Objetivo
KLP (Likely Impersonation) users (International)
Método de Ataque
Brand impersonation
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
🏢 Análisis de Suplantación de Marca
Impersonated Brand
KLP
Official Website
klp.no
Fake Service
KLP Login Portal
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker aims to steal user credentials by mimicking a legitimate login page and tricking users into entering their information.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
multi-factor.link
Registered
None
Registrar
Unknown
Status
Active
🤖 AI-Extracted Threat Intelligence
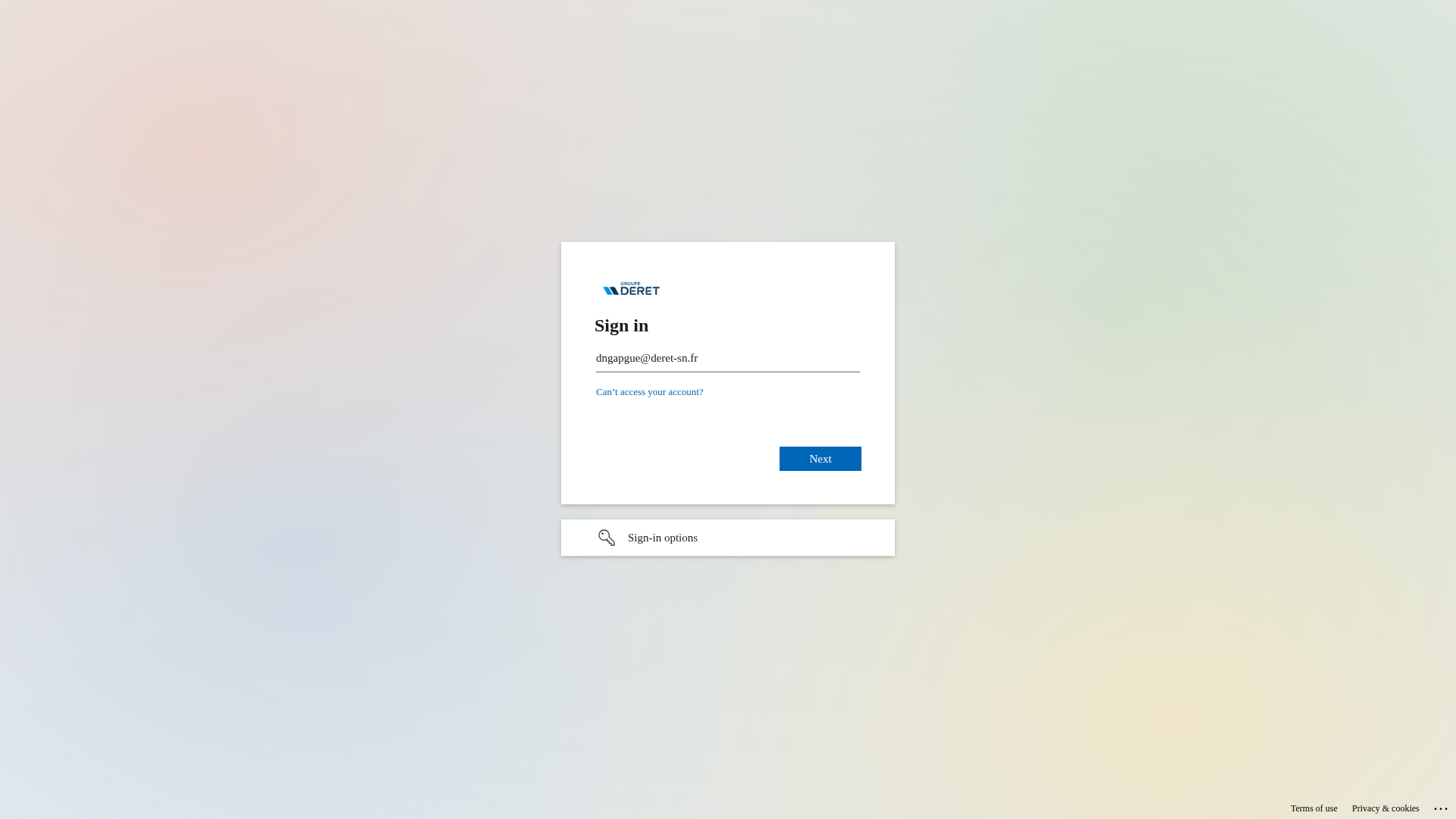
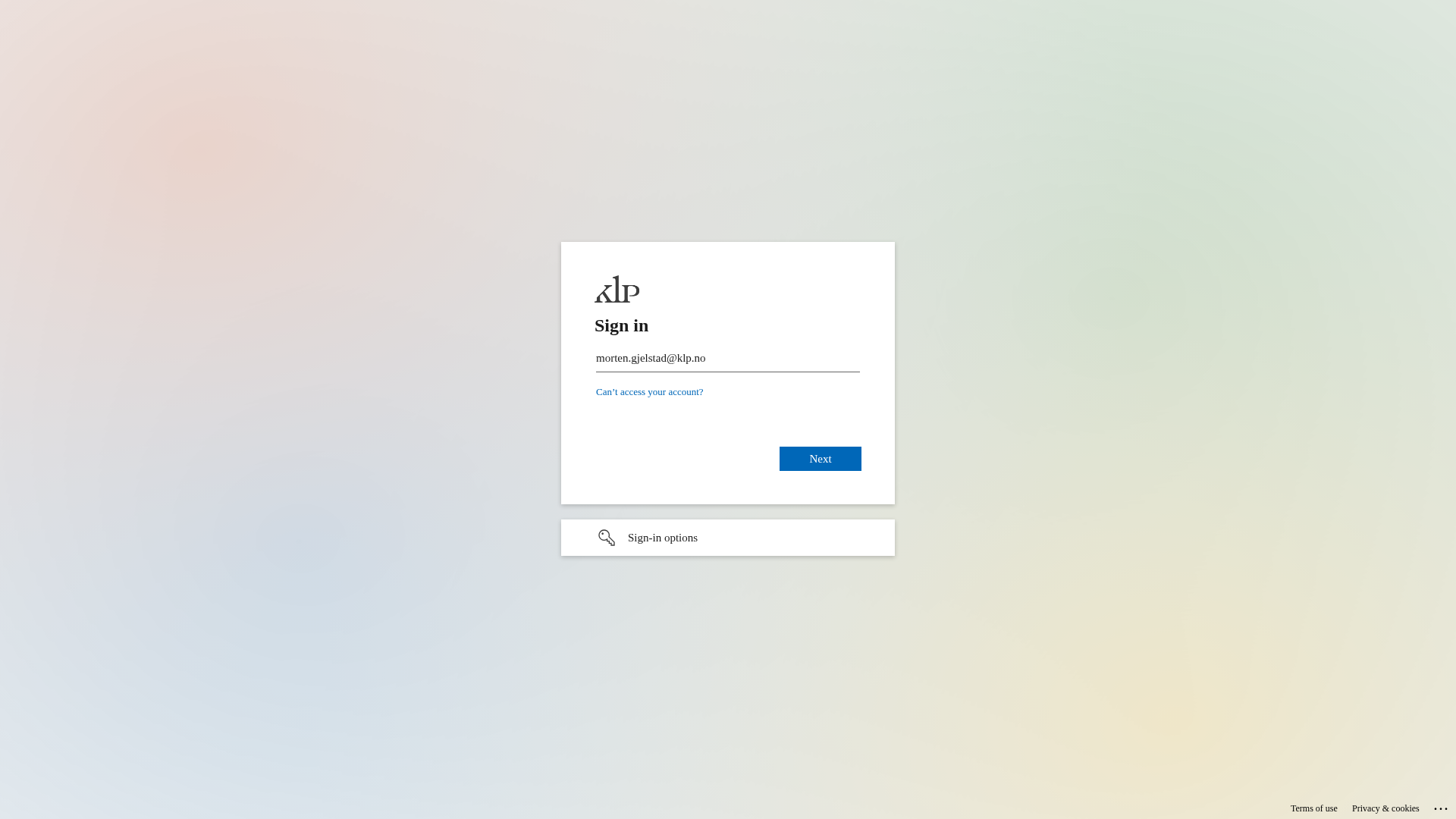
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
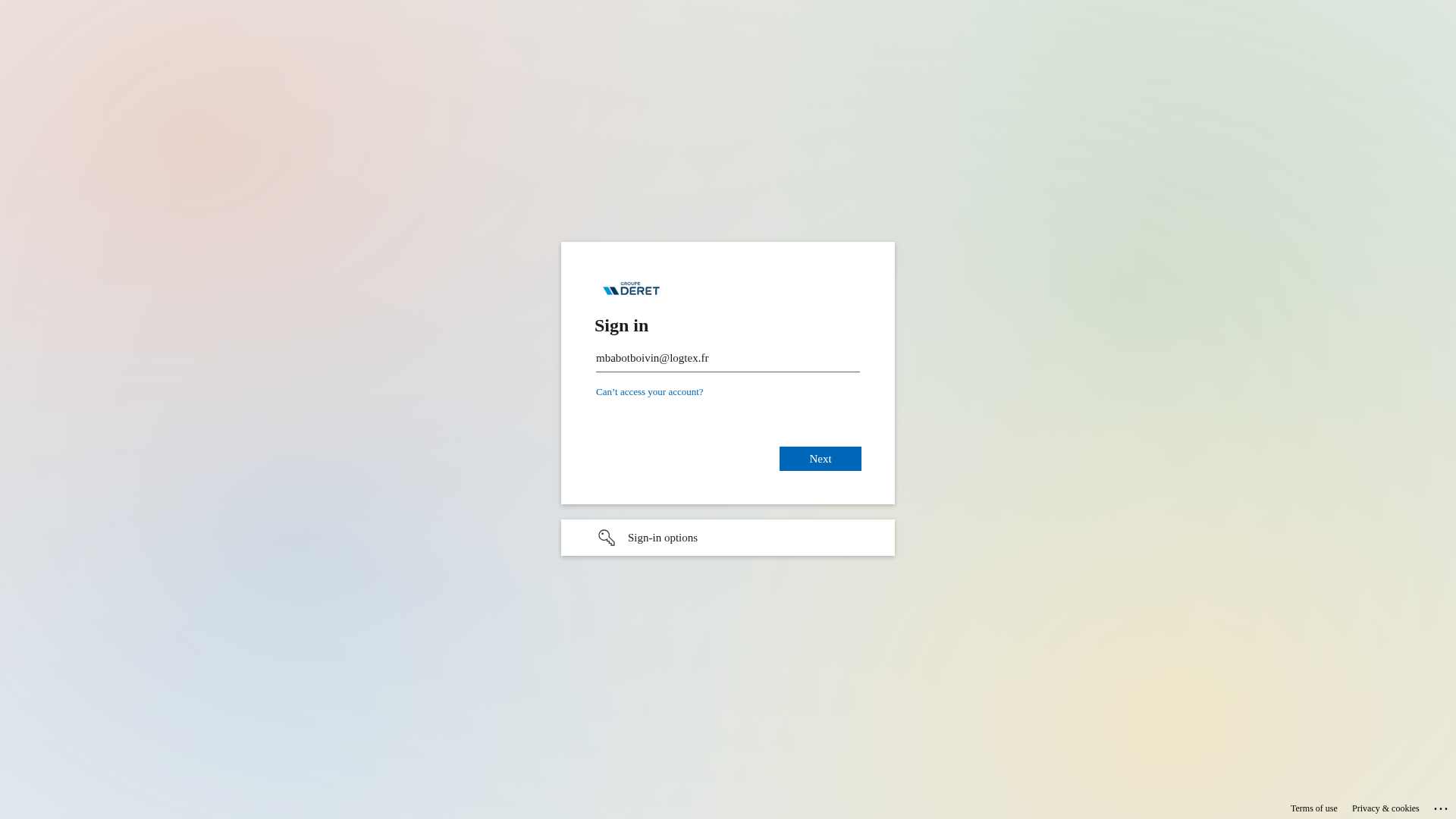
Groupe Deret
https://loginservice.cloud/MaFjX1S4Auo
Abr 05, 2026
Microsoft 365
https://authentication.ms/lr_zHa7DF9xZlA
Abr 05, 2026
Unknown
https://cdn.gosafemode.com/screenshots/49bc7805d422.png
Abr 05, 2026
Microsoft 365 (impersonated)
https://authentication.ms/lNU4Ma0tGc5AARehVw
Abr 05, 2026
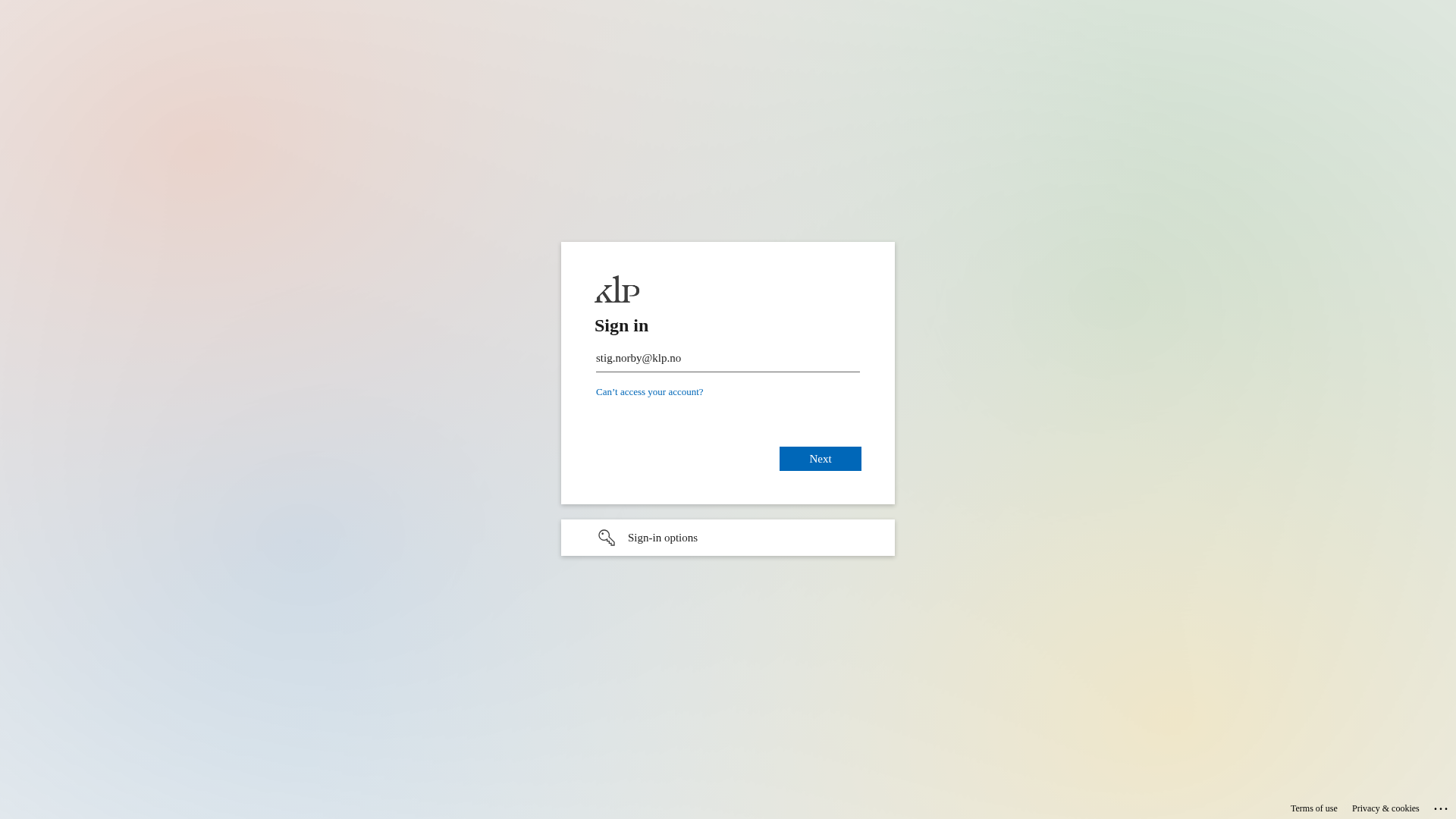
KLP
https://loginservice.cloud/stF-CMW7YaMOXKtf
Abr 05, 2026
Scan History for multi-factor.link
Found 10 other scans for this domain
-
https://multi-factor.link/X-K3CeZWToDctA
https://multi-factor.link/f-RUA_KGYl3F?/ContextID=...
https://multi-factor.link/RYkgo7bJzbDKSpTz6A
https://multi-factor.link/hyXVBzQmfrFL
https://multi-factor.link/_Sb1YAwXrHtOIg
https://multi-factor.link/ml6rxBE89to
https://multi-factor.link/Klqob1GIQic
https://multi-factor.link/q4Ikhp2EI5_YOQ
https://multi-factor.link/qewOWgJmJow
https://multi-factor.link/XLHO3q9WdoQ

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.