
Phishing Analysis
Detailed analysis of captured phishing page
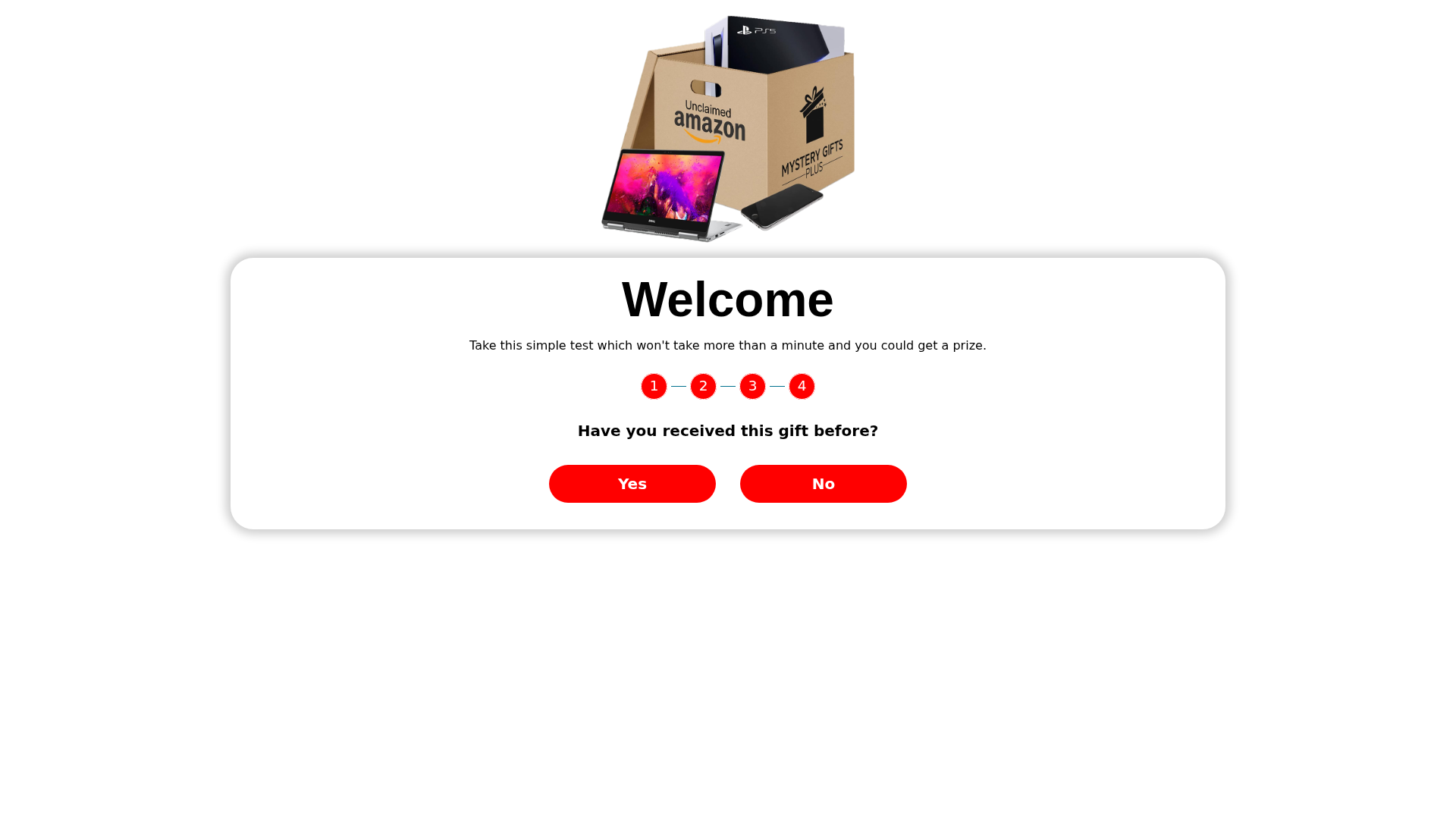
Captura Visual
Información de Detección
http://im.nbpublic.com/loading_page/snack_box/snack_box_cf_3
Detected Brand
Amazon
Country
USA
Confidence
95%
HTTP Status
200
Report ID
2c5a2dde-910…
Analyzed
2026-03-16 23:51
Final URL (after redirects)
http://im.nbpublic.com/loading_page/snack_box/snack_box_cf_3/
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T176618A715449D8BF82C3C2E086783B5E36C1CA86EE2B1A9886F4D30D1FEBD90ED07155 |
|
CONTENT
ssdeep
|
48:llMLEY0OW2IbSAwwy6qj4OQHj4OQgj4OQtj4OQ8pt8BjH5c7BjHY3BjHM/9MBjH3:LTaw9ycAzuozscqK0 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e666c666cccc9833 |
|
VISUAL
aHash
|
e7e7e7e7e7e7ffff |
|
VISUAL
dHash
|
2d4d0f0d4d0d0008 |
|
VISUAL
wHash
|
27278080a581ffff |
|
VISUAL
colorHash
|
07400018000 |
|
VISUAL
cropResistant
|
2d4d0f0d4d0d0008 |
Análisis de Código
Risk Score
3/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Clientes de Amazon
• Método: Incentivo de regalo para obtener información del usuario
• Exfil: Desconocido (es probable que los clics del usuario conduzcan a la recopilación de datos)
• Indicadores: Oferta de regalo, marca Amazon, encuesta corta
• Riesgo: Alto
🔒 Obfuscation Detected
- unescape
📡 API Calls Detected
- POST
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Mismatched Domain
The domain is not related to Amazon.
Impersonation of Brand
The website attempts to impersonate Amazon with branding and a gift offer.
Suspicious Content
The offering of 'mystery gifts' and a test for a prize is a red flag.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Amazon Phishing Landing Page
Objetivo
Amazon users (USA)
Método de Ataque
Brand impersonation + obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
LOW - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- 2 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Amazon
Official Website
https://www.amazon.com
Fake Service
Gift offers or surveys
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Brand Impersonation
The attacker uses the Amazon brand to lure victims. The site creates an initial hook with a welcoming message and a simple prompt to engage.
Secondary Method: Social Engineering
The attacker uses an incentive, a prize or gift, to entice the user to interact with the page.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
im.nbpublic.com
Registered
2022-09-14
Registrar
Namecheap
Status
ACTIVE
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Amazon
https://im.nbpublic.com/loading_page/amazon/AmazonGiftCard_5...
Mar 07, 2026
Amazon
https://im.nbpublic.com/loading_page/snack_box/snack_box_cf_...
Dic 31, 2025
Amazon
http://im.nbpublic.com/loading_page/snack_box/snack_box_cf_3...
Dic 31, 2025
No screenshot
Amazon
http://im.nbpublic.com/loading_page/snack_box/snack_box_cf_3
Dic 22, 2025
Scan History for im.nbpublic.com
Found 10 other scans for this domain
-
https://im.nbpublic.com/loading_page/paypal/paypal...
https://im.nbpublic.com/loading_page/amazon/Amazon...
https://||im.nbpublic.com/loading_page_cpl/amazon/...
https://||im.nbpublic.com/loading_page/amazon/amaz...
http://im.nbpublic.com/loading_page/amazon/AmazonG...
https://im.nbpublic.com/loading_page/paypal/paypal...
https://im.nbpublic.com/loading_page/amazon/Amazon...
https://im.nbpublic.com/loading_page/snack_box/sna...
http://im.nbpublic.com/loading_page/snack_box/snac...
http://im.nbpublic.com/loading_page/snack_box/snac...

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.