
Phishing Analysis
Detailed analysis of captured phishing page
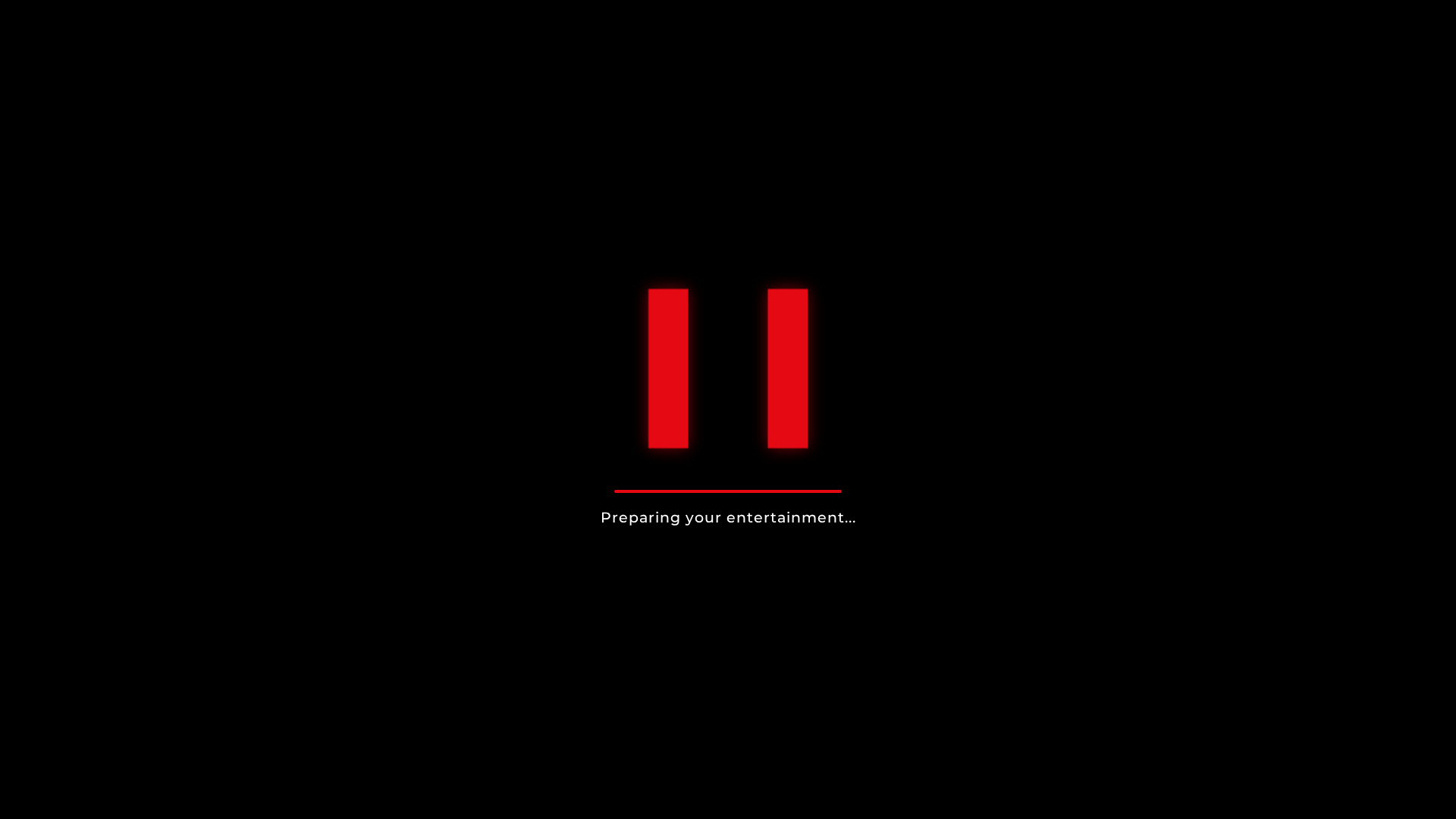
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1E2A264A05105993741A393D27273475B32F1C209DB07066852FD93ADDBEECB4ED2FAA2 |
|
CONTENT
ssdeep
|
192:8IDUR+B488HRT26lOq+KBaIYqk961b8AtOkGHzwc9dGRbOj/:8IDUR+4HRTdlOqHaIYq91/7GTwc9dDz |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc99336699996666 |
|
VISUAL
aHash
|
0000181818180000 |
|
VISUAL
dHash
|
0000303030300000 |
|
VISUAL
wHash
|
00003c3c18180000 |
|
VISUAL
colorHash
|
38000000007 |
|
VISUAL
cropResistant
|
0000303030300000 |
Análisis de Código
🔒 Obfuscation Detected
- fromCharCode
📡 API Calls Detected
- https://www.youtube.com/results?search_query=Narcos%20trailer
- https://www.youtube.com/results?search_query=Wednesday%20trailer
- https://www.youtube.com/results?search_query=Stranger%20Things%20trailer
- https://www.youtube.com/results?search_query=Money%20Heist%20trailer
- https://www.youtube.com/results?search_query=Lucifer%20trailer
- https://www.youtube.com/results?search_query=Dark%20trailer
- https://www.youtube.com/results?search_query=The%20Crown%20trailer
- https://www.youtube.com/results?search_query=${encodeURIComponent(movie.title +
- https://www.youtube.com/results?search_query=The%20Witcher%20trailer
- https://www.youtube.com/results?search_query=Black%20Mirror%20trailer
- https://www.youtube.com/results?search_query=Breaking%20Bad%20trailer
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: OTP Stealer, Personal Info
- 1 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 1 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)


Scan History for bansalpratham.github.io
Found 1 other scan for this domain
