
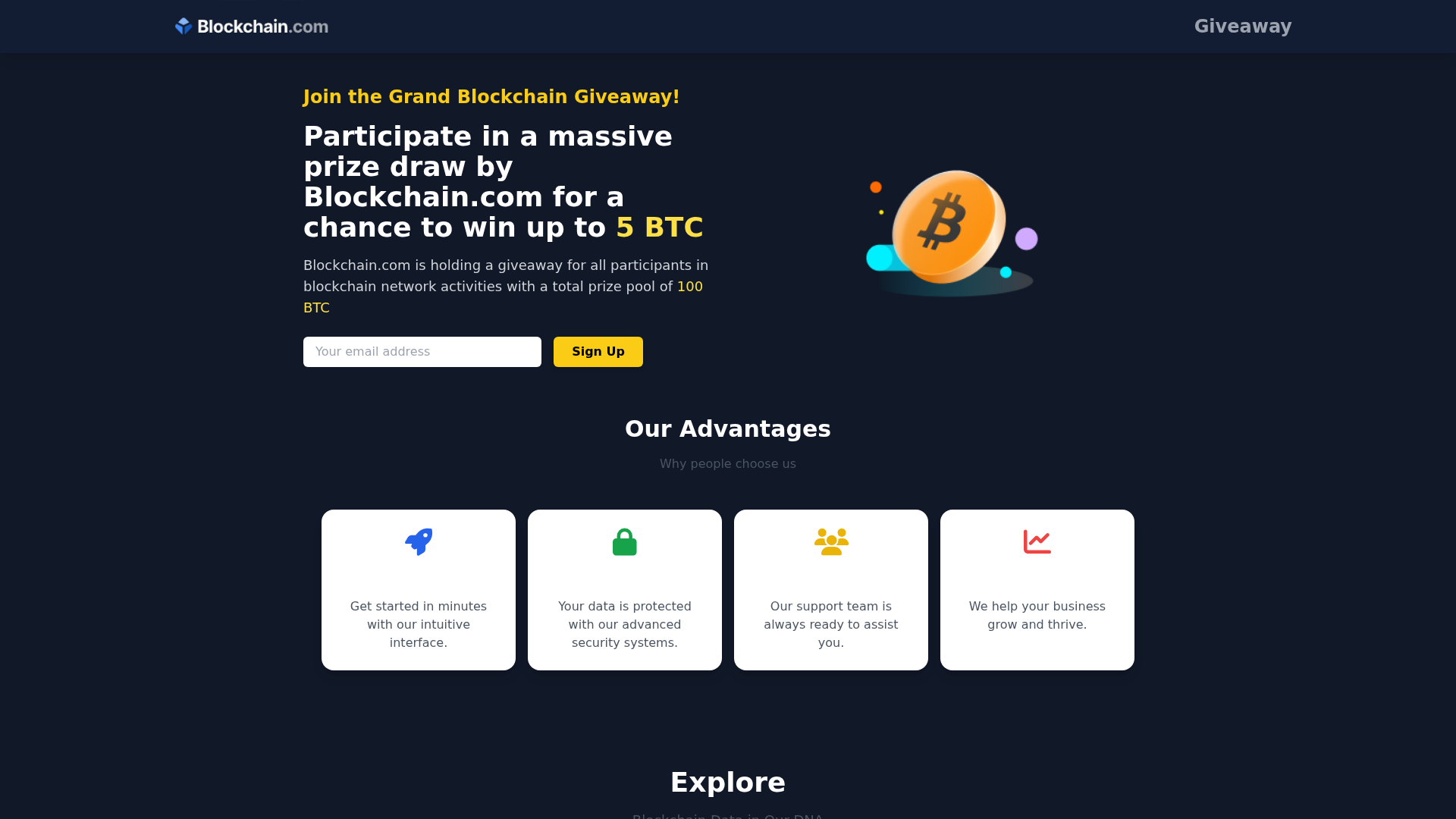
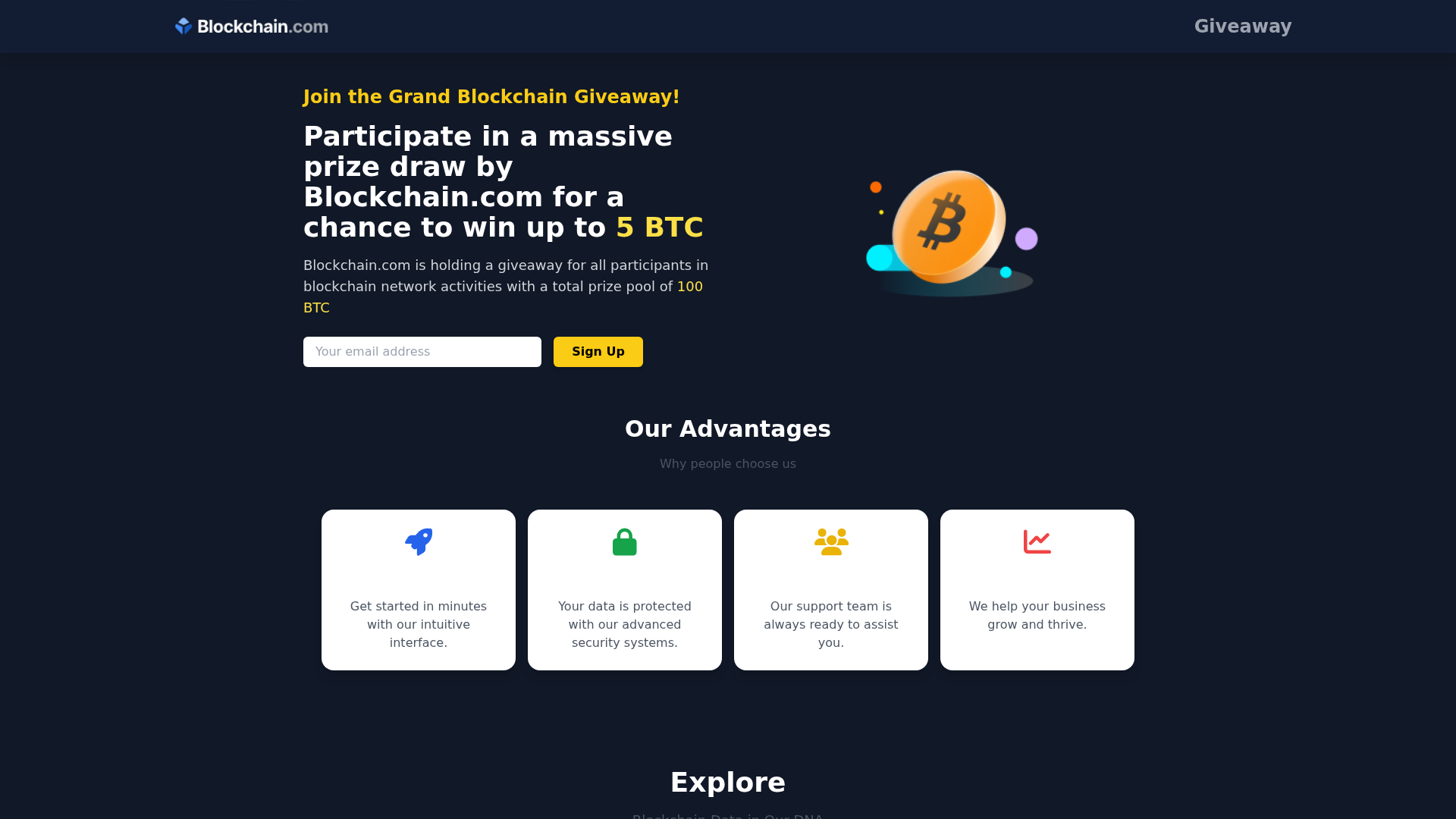
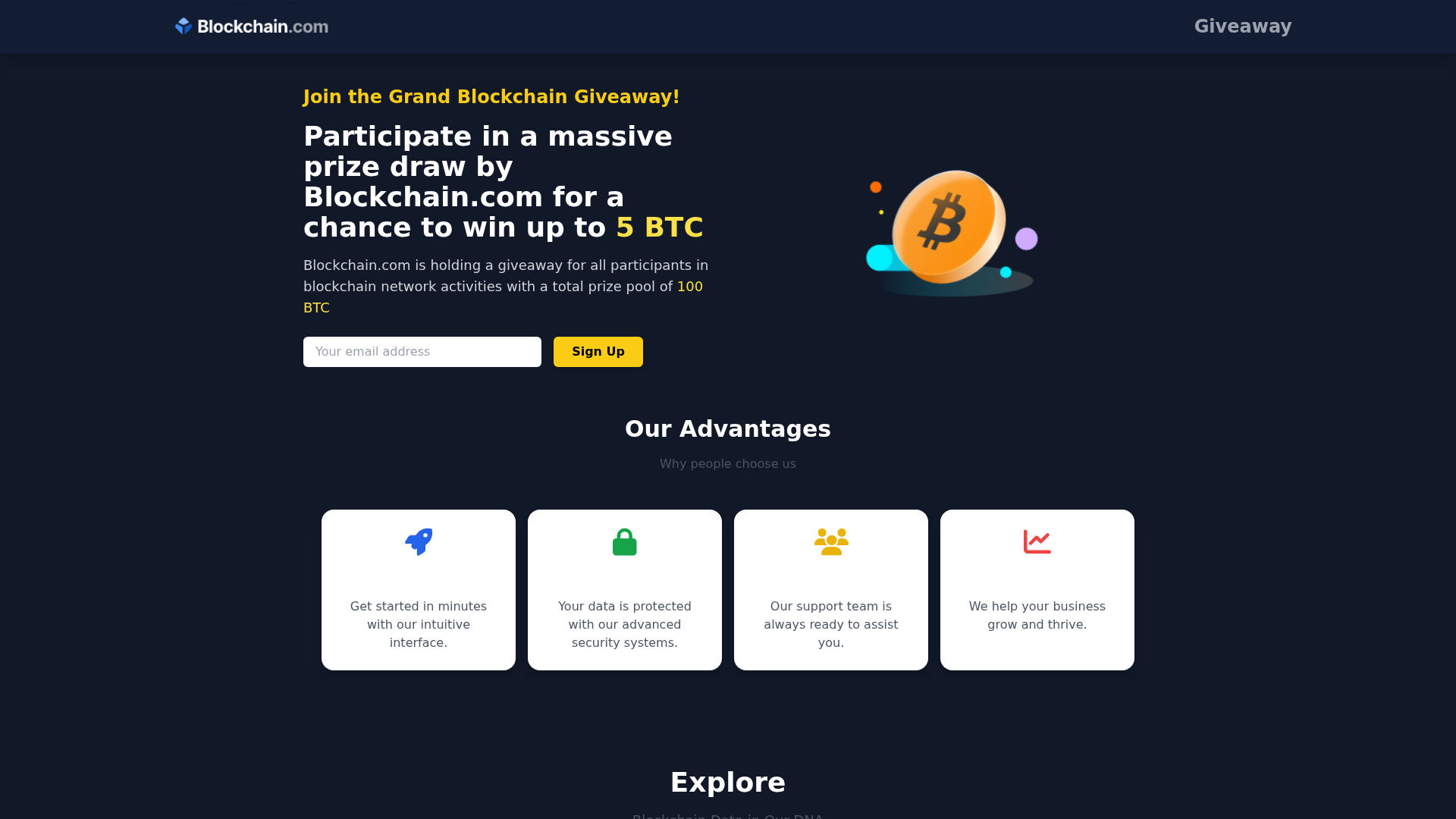
Phishing Analysis
Detailed analysis of captured phishing page
Captura Visual
Información de Detección
https://rul.godprox.cc/go/63b433/y284w2
Detected Brand
Blockchain.com
Country
International
Confidence
100%
HTTP Status
200
Report ID
362b32f3-fae…
Analyzed
2026-02-21 11:32
Final URL (after redirects)
https://122alo.borotti.cc/gives/
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F3B1123031542ABB61C799F1B3A22B2E72E8C658CA27C649B3F5C35A6BDBC15CD40364 |
|
CONTENT
ssdeep
|
96:MTLCh/am/hVRt0UTM8////LQA0nJCPD9RJ4nsB:MTLC4mpVRt0UTHHbQZQD9RJ4nI |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c3693c966dc79238 |
|
VISUAL
aHash
|
00202420007e7e00 |
|
VISUAL
dHash
|
a6c9c9c6f0e8e833 |
|
VISUAL
wHash
|
72747c70187e7e18 |
|
VISUAL
colorHash
|
31200030000 |
|
VISUAL
cropResistant
|
3866c7c7c7ce567c,8383abb1b18b0383,2b6b2b2b2b2b2b2b,a6c9c9c6f0e8e833 |
Análisis de Código
Risk Score
76/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Blockchain.com
• Método: Suplantación con sorteo
• Exfil: wheal.php (Datos del formulario)
• Indicadores: Coincidencia de dominio, sorteo, Javascript ofuscado
• Riesgo: ALTO
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
📤 Form Action Targets
- wheal.php
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain rul.godprox.cc is not affiliated with Blockchain.com.
Form Submission
Form submitting data to a suspicious php file.
Obfuscation
JavaScript is obfuscated, indicating malicious intent.
Impersonation
Attempts to impersonate Blockchain.com.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Blockchain.com users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
HTTP POST to backend
Evaluación de Riesgo
HIGH - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 6 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Blockchain.com
Official Website
blockchain.com
Fake Service
Giveaway
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The site uses a form to collect email addresses, likely with the intention of harvesting credentials for phishing or account takeover.
Secondary Method: Giveaway Scam
The offer of a giveaway is used as a lure to entice users to enter their email and potentially other data.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
rul.godprox.cc
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Blockchain.com
https://rad.godprox.cc/go/63b433/y284w2
Feb 23, 2026
Blockchain.com
https://122jip.borotti.cc/gives/
Feb 07, 2026
Blockchain.com
https://122era.nickles.cc/gives/
Feb 04, 2026
Blockchain.com
https://122gtd.proxer.cc/gives/
Feb 03, 2026
Blockchain.com
http://a.krotoz.cc/gives/
Ene 20, 2026
Scan History for rul.godprox.cc
Found 3 other scans for this domain

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.