Phishing Analysis
Detailed analysis of captured phishing page
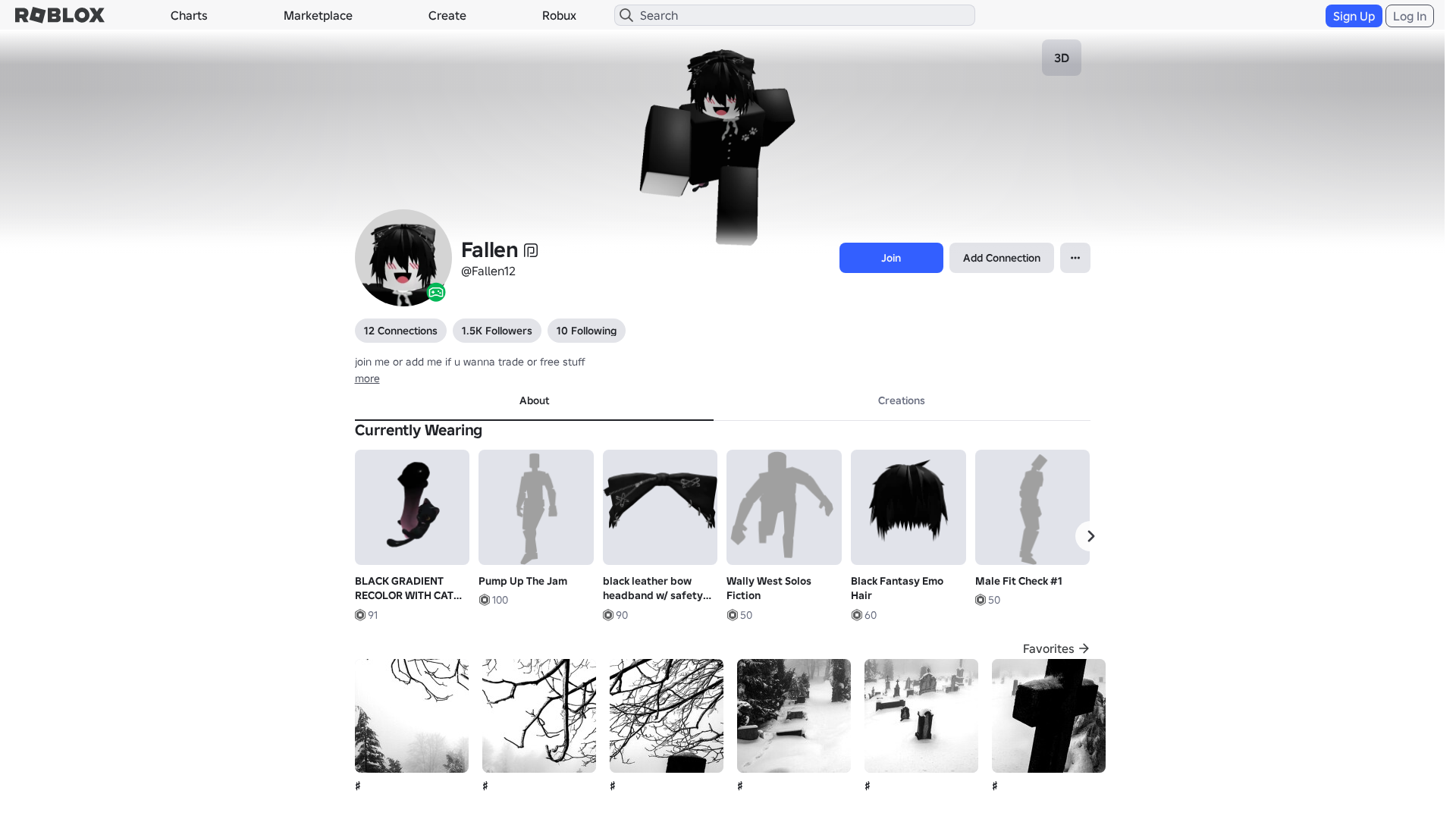
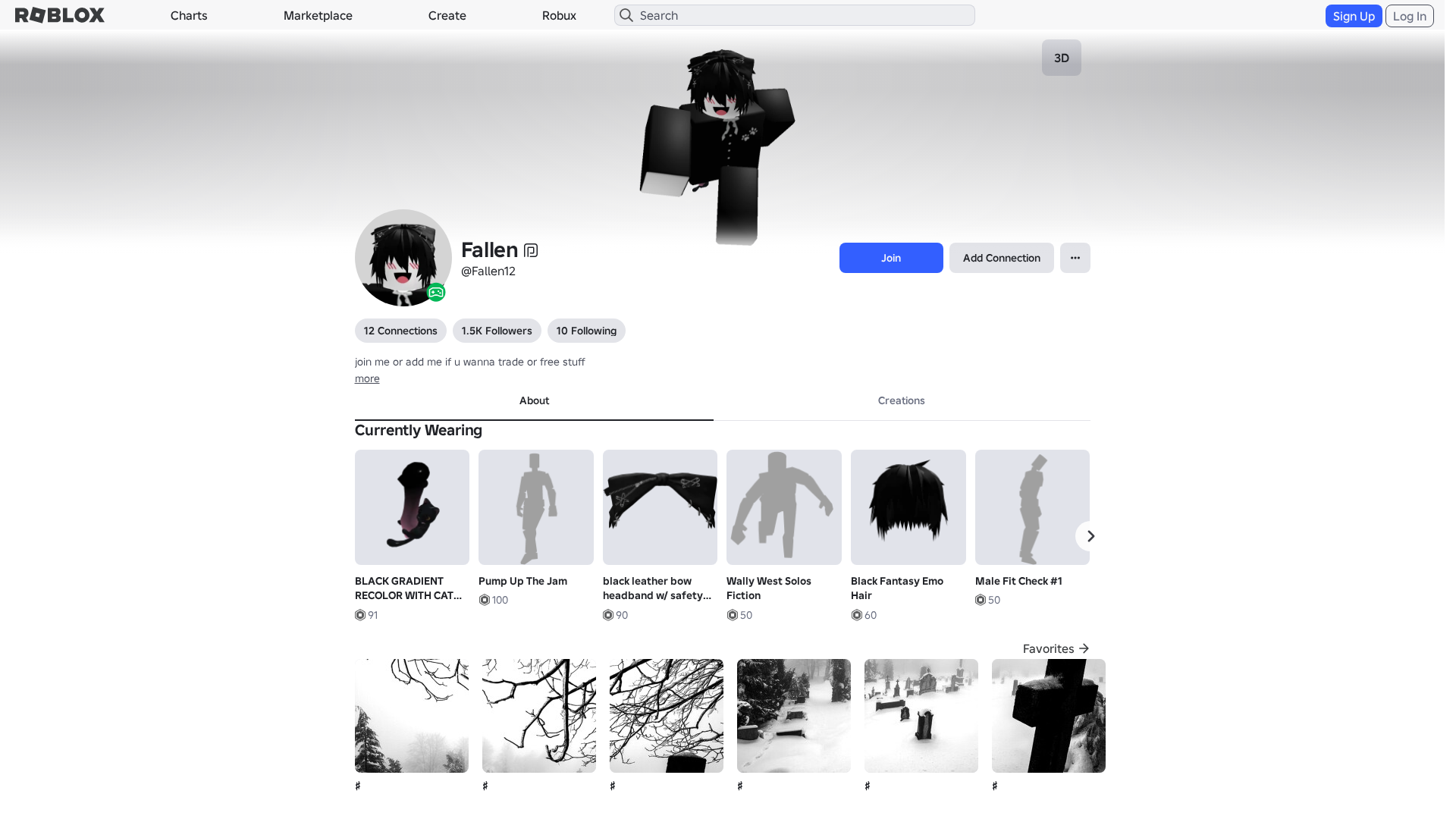
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14D73527292542837617B79DAF064672AD2D3D70FCA4346E1A2F8D39A0FD6CE1E86340D |
|
CONTENT
ssdeep
|
1536:0h2XWn4r6bWexYsgrRgVEgI6gs2g91gpGgSmgSug7agtWgHagMXgqWgdrgFng29w:G2XW1b2wKo1KaK75vg3FsjtCkwMWclZo |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e6164367d9c89c6c |
|
VISUAL
aHash
|
0024d7ffc3c3e3e3 |
|
VISUAL
dHash
|
c8c8263086360b0b |
|
VISUAL
wHash
|
0000d7ffc3c3e3cb |
|
VISUAL
colorHash
|
07000000180 |
|
VISUAL
cropResistant
|
c8c8263086360b0b,8e97115b4f962626 |
Análisis de Código
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /info/blog?locale=en_us
- /login?returnUrl=
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F219691264161%2Fprofile
- https://api.injuries.lu/catalog/119079173538697/R6-Smooth-Right-Arm
- https://api.injuries.lu/catalog/79412759833752/Wally-West-Solos-Fiction
- https://api.injuries.lu/catalog/619536621/Zombie-Run
- https://api.injuries.lu/catalog/138525477297391/Black-Fantasy-Emo-Hair
- https://api.injuries.lu/catalog/88425531063616/Stylish-Floating
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/112564481620053/black-leather-bow-headband-w-safety-pins-metals
- https://api.injuries.lu/catalog/14618207727/Default-Mood
- https://api.injuries.lu/catalog/129913805701008/R6-Smooth-Left-Arm
- https://api.injuries.lu/catalog/132971777995699/R6-Smooth-Left-Leg
- https://api.injuries.lu/catalog/82691797173391/unnamed
- https://api.injuries.lu/catalog/81609164587072/Male-Fit-Check-1
- https://api.injuries.lu/catalog/619537468/Zombie-Walk
- https://api.injuries.lu/catalog/95880344444701/BLACK-GRADIENT-RECOLOR-WITH-CAT-FOR-KORBLOX
- https://api.injuries.lu/catalog/114502615688717/Around-the-Head
- https://api.injuries.lu/catalog/5319922112/Oldschool-Idle
- https://api.injuries.lu/catalog/18755922352/No-Boundaries-by-Walmart-Fall
- https://api.injuries.lu/catalog/82534789806334/R6-Smooth-Torso
- https://api.injuries.lu/catalog/123509187015792/Wicked-Dancing-Through-Life-Animation-P-Climb
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F219691264161%2Fprofile
- https://api.injuries.lu/catalog/75548043720221/unnamed
- https://api.injuries.lu/catalog/96709439922660/Super-Super-Happy-Face-Dynamic-Head
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/104721659176603/Sonic-Adventure-Profile-Pose
- https://api.injuries.lu/catalog/139607718/Korblox-Deathspeaker-Right-Leg
- https://api.injuries.lu/catalog/1113742359/Vampire-Jump
- https://api.injuries.lu/catalog/18755938274/No-Boundaries-by-Walmart-Swim
- https://api.injuries.lu/catalog/139749659598065/Michael-Myers-Bounce-NEW-VERSION
- https://api.injuries.lu/catalog/101572357319427/Blue-Top-Rock
- https://api.injuries.lu/catalog/95323564137838/Pump-Up-The-Jam
📡 API Calls Detected
- https://apis.
- https://ro.blox.com/Ebh5?
- POST
- get
- GET
- https://help.roblox.com/hc/articles/30428367965460
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 210 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 210 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for s4w.in
Found 8 other scans for this domain
-
https://s4w.in/www-roblox-com-gl-users-21623285688...
https://s4w.in/www-roblox-com-users-13342902-profi...
https://s4w.in/https-roblox-com
https://s4w.in/roblox-com-user-293628-profile
https://s4w.in/toBsT
https://s4w.in/roblox-com-users-1029920-profile
https://s4w.in/www-roblox-com-gl-users-21623285688...
https://s4w.in/WzXCr