
Phishing Analysis
Detailed analysis of captured phishing page
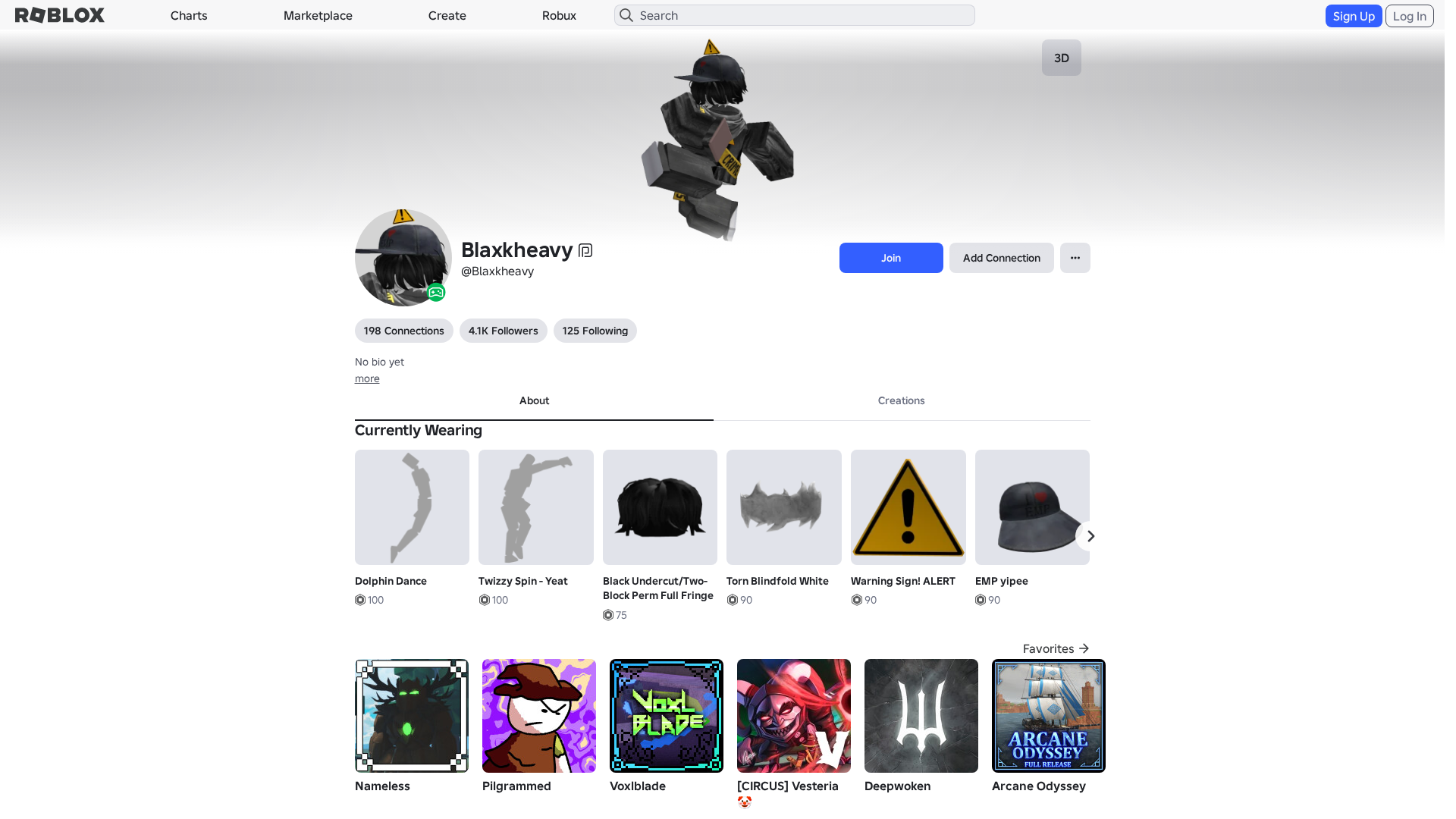
Captura Visual
Información de Detección
http://www.roblx.me/s/hWilGa
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
3c866c50-3e1…
Analyzed
2026-04-04 21:09
Final URL (after redirects)
https://www.robiox.com.py/users/346425773633/profile
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F1D310729121283754BB75DAB124A75EA6D7C74FCAC343E1A2FCC39A4FDAC91EC12409 |
|
CONTENT
ssdeep
|
3072:EtXW0SnEmgJTD43YFY2/xy47pgt90bXHBONL69RAUIG:cXjSnEmgJTD43YFY2/xy47pgt+bXHBOe |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b4966343d99ccc3c |
|
VISUAL
aHash
|
2024dfffe3e3c3c3 |
|
VISUAL
dHash
|
c8c836300e068e8e |
|
VISUAL
wHash
|
0000dfffc3e3c3c3 |
|
VISUAL
colorHash
|
07000208040 |
|
VISUAL
cropResistant
|
c8c836300e068e8e,8c0e2d33116c3f0d,63bcece8dc716717,f97176f3f3353e3e,6149696169717131,9d13071b67255d53 |
Análisis de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/100416618991324/Best-All-Might-Victory-Pose-R6
- https://api.injuries.lu/catalog/126354114956642/adidas-Community-Animation-Pack
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F346425773633%2Fprofile
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/88224135185704/EMP-yipee
- https://api.injuries.lu/catalog/135545153917736/Miku-Beam-Emote
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F346425773633%2Fprofile
- https://api.injuries.lu/catalog/84235260043475/Twizzy-Spin-Yeat
- https://api.injuries.lu/catalog/123283221135727/heavyblack-jeans
- https://api.injuries.lu/catalog/11573370910/Anime-Mood
- https://api.injuries.lu/catalog/122902903651413/Long-Grey-Scarf
- https://api.injuries.lu/catalog/7168548591/Black-Undercut-Two-Block-Perm-Full-Fringe
- https://api.injuries.lu/catalog/12545323293/Warning-Sign-ALERT
- https://api.injuries.lu/catalog/15093053680/Headless-Head
- https://api.injuries.lu/catalog/5938365243/Dolphin-Dance
- https://api.injuries.lu/catalog/113307296054375/Hands-Behind-Back
- https://api.injuries.lu/catalog/70888470847518/Silly-Animals-Dance
- /login?returnUrl=
- https://api.injuries.lu/catalog/78606930759163/leatherjacket2
- https://api.injuries.lu/catalog/121289788791960/Crime-Scene-Do-Not-Cross-Scarf-1-0
- https://api.injuries.lu/catalog/112540347880956/Feeling-Cute
- https://api.injuries.lu/catalog/11703495178/Torn-Blindfold-White
- https://api.injuries.lu/catalog/619522386/Robot-Run
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/106537098239253/Caution-pin
- /info/blog?locale=en_us
📡 API Calls Detected
- https://kyxn.dev${e.endpoint}
- https://www.google.com/ccm/geo
- https://apis.
- https://help.roblox.com/hc/articles/30428367965460
- POST
- /api/shorten
- https://ro.blox.com/Ebh5?
- get
- GET
- https://kyxn.dev/api/shorten/TKvzwH
- /api/pageview
- https://kyxn.dev/api/shorten
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 226 technique(s) to evade detection
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Roblox users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
HTTP POST to backend
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 226 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 226 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
www.roblx.me
Registered
2026-03-28 03:56:41+00:00
Registrar
NAMECHEAP INC
Status
Recently registered (7 days old)
Hosting Information
Provider
Namecheap
ASN
🤖 AI-Extracted Threat Intelligence

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.