Phishing Analysis
Detailed analysis of captured phishing page
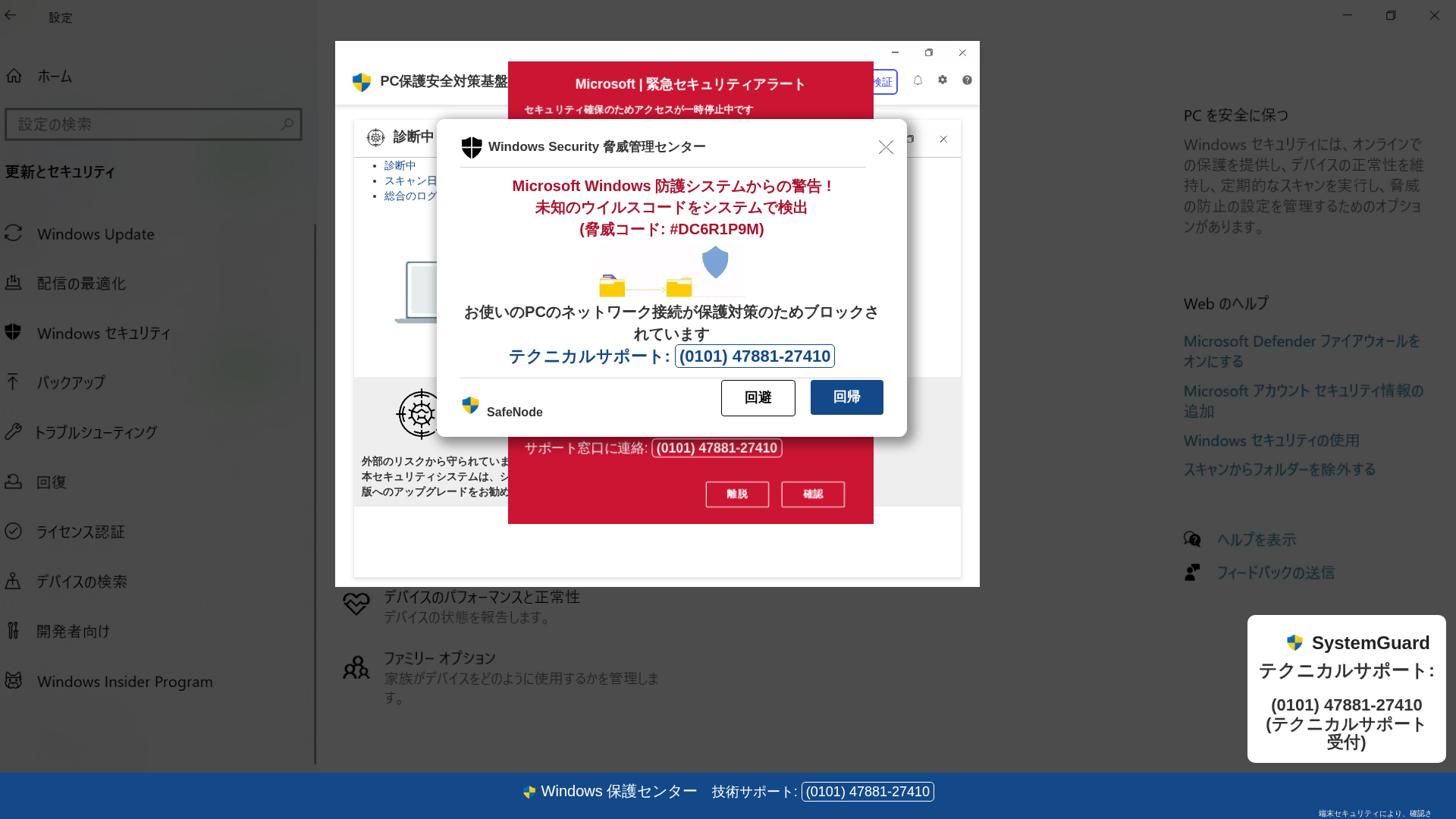
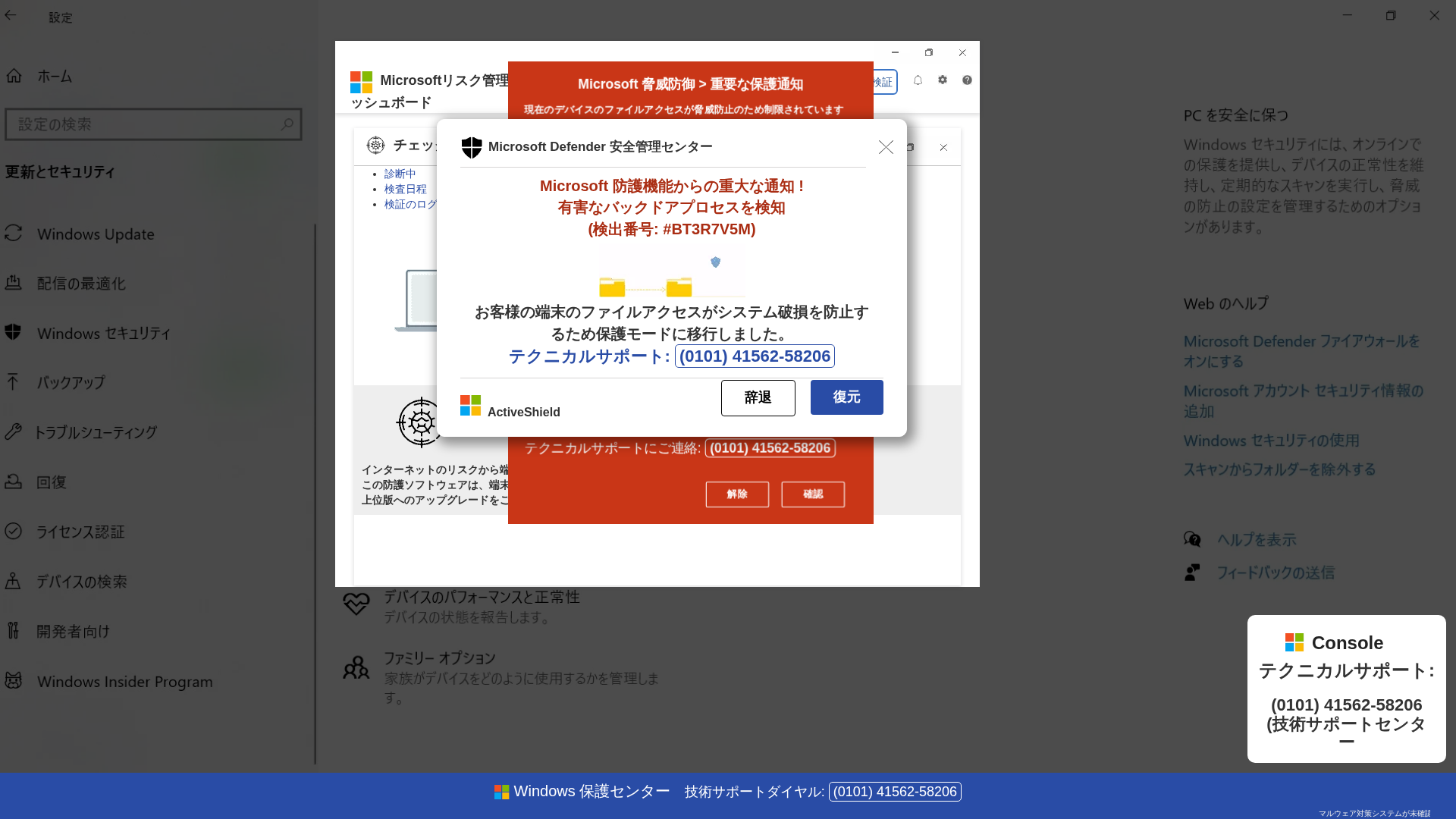
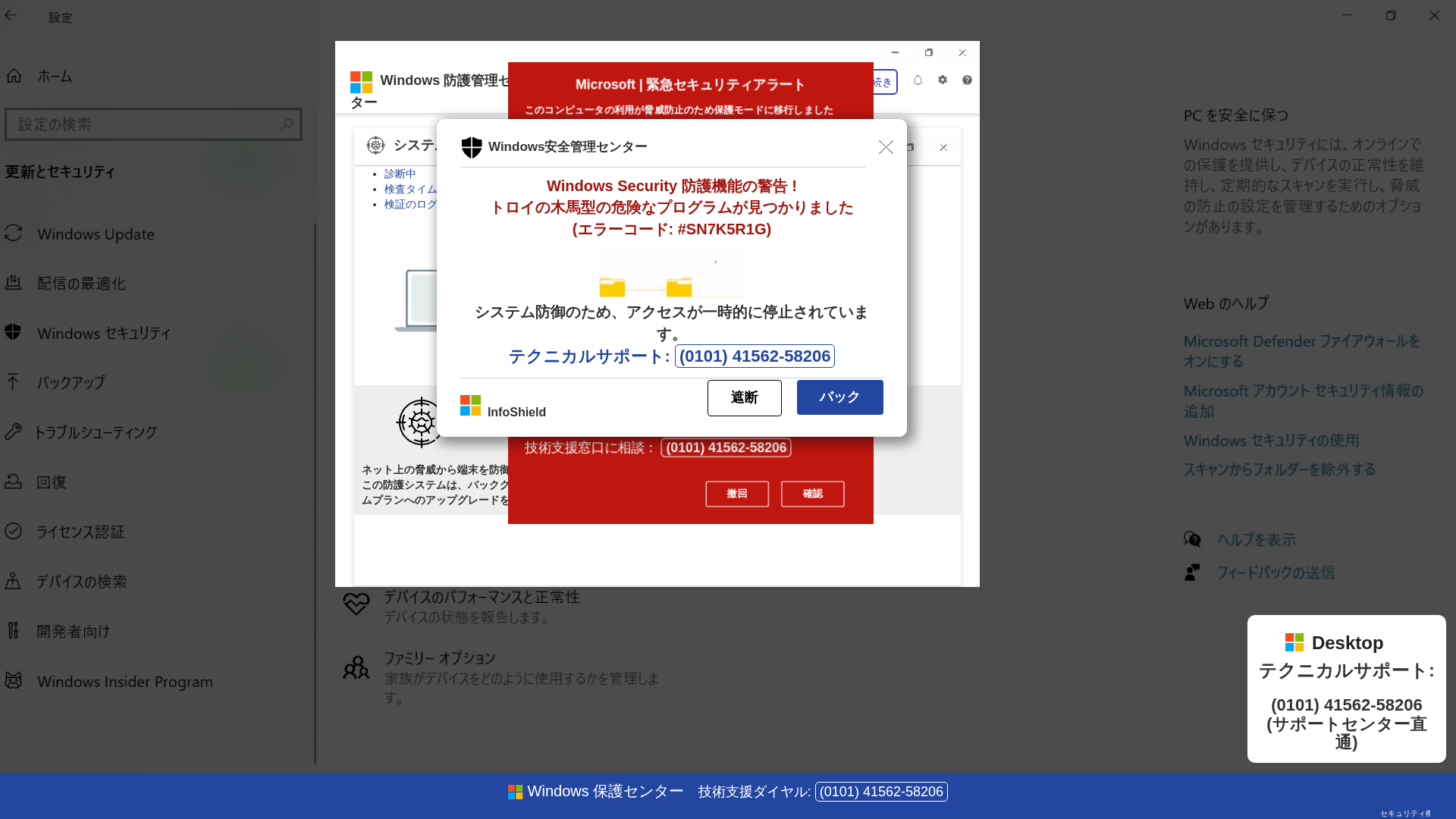
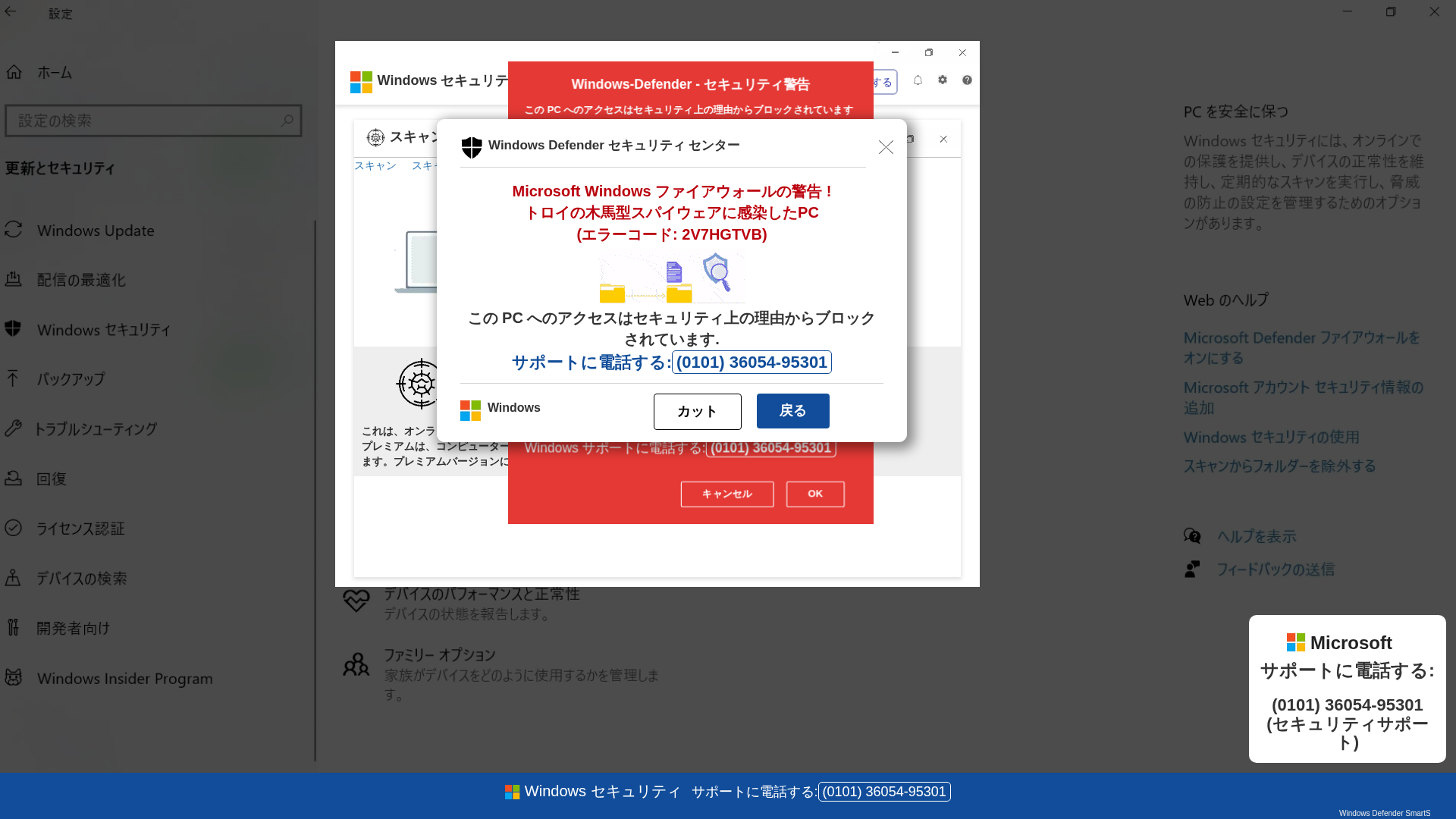
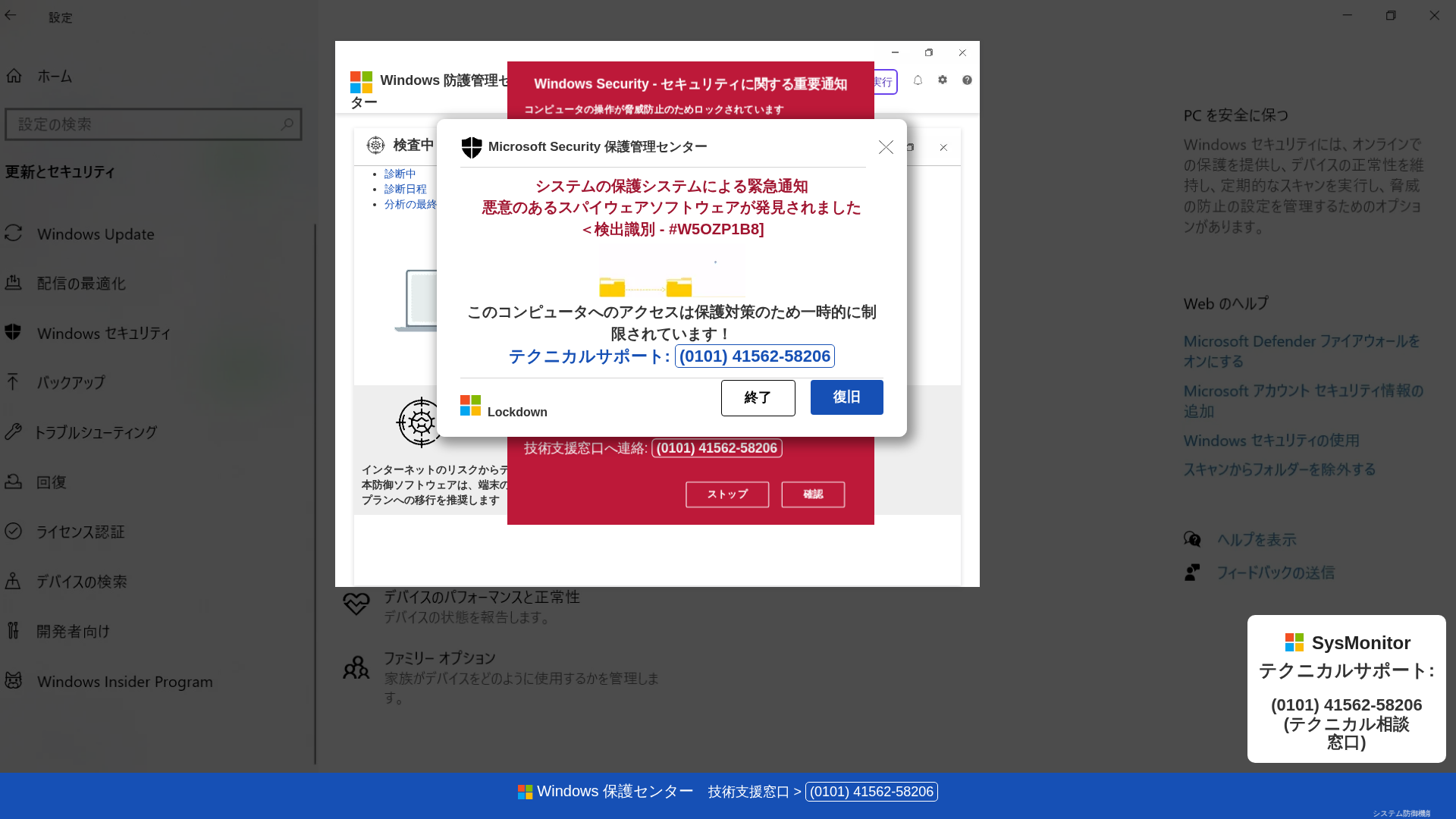
Captura Visual
Información de Detección
https://sapafugesu.z38.web.core.windows.net/
Detected Brand
Microsoft Windows
Country
International
Confidence
100%
HTTP Status
200
Report ID
3d44a351-8e3…
Analyzed
2026-03-14 02:39
Final URL (after redirects)
https://sapafugesu.z38.web.core.windows.net/j8qb90gdp3cm.html
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1CA73C039B2407E36010A43C5EFA28B6B7356C748DE561F48026CC77AADEFD68EC5259C |
|
CONTENT
ssdeep
|
1536:qpHmQjIE+8xY13QnN04Fmadph7XiE/XRL+fmHxdgRJ2YedsV2:qpHmQjIDcw3aN08dnDgRJcsE |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cbd33c33762c5522 |
|
VISUAL
aHash
|
283c3c3c3c3c0101 |
|
VISUAL
dHash
|
c9c9e9e1c9c9b3fb |
|
VISUAL
wHash
|
3c7c7c7c7c7c0301 |
|
VISUAL
colorHash
|
07000000183 |
|
VISUAL
cropResistant
|
939bc6ccc3139b93,a0aa8696aaa28acc,c9c9e9e1c9c9b3fb,815e8e86314ec0e0,b9b947981a1a180a |
Análisis de Código
Risk Score
85/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Estafa de phishing.
• Objetivo: Usuarios de Windows.
• Método: Mostrar una alerta de seguridad falsa e instar a la víctima a llamar a un número de soporte falso.
• Exfil: Número de teléfono para posible ingeniería social y robo de credenciales.
• Indicadores: Discordancia de dominio, alertas urgentes, número de teléfono, Javascript ofuscado.
• Riesgo: Crítico.
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
📊 Desglose de Puntuación de Riesgo
Total Risk Score
95/100
Contributing Factors
Domain Mismatch
The domain 'sapafugesu.z38.web.core.windows.net' is unrelated to the brand.
Impersonation
The site mimics Windows Security to create a sense of urgency.
Phishing Indicators
Presence of urgent warnings, a phone number and instructions.
Obfuscation
Obfuscation of javascript can be used to hide malicious code
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Microsoft Windows users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Personal Info
- 30 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Microsoft Windows
Official Website
https://www.microsoft.com/en-us/windows
Fake Service
Windows Security
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Tech Support Scam
The site displays a fake security alert designed to impersonate Microsoft and scare users into calling a provided phone number.
Secondary Method: Social Engineering
The attackers likely attempt to trick victims into providing personal information, granting remote access, or paying for fraudulent services.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
sapafugesu.z38.web.core.windows.net
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.