
Phishing Analysis
Detailed analysis of captured phishing page
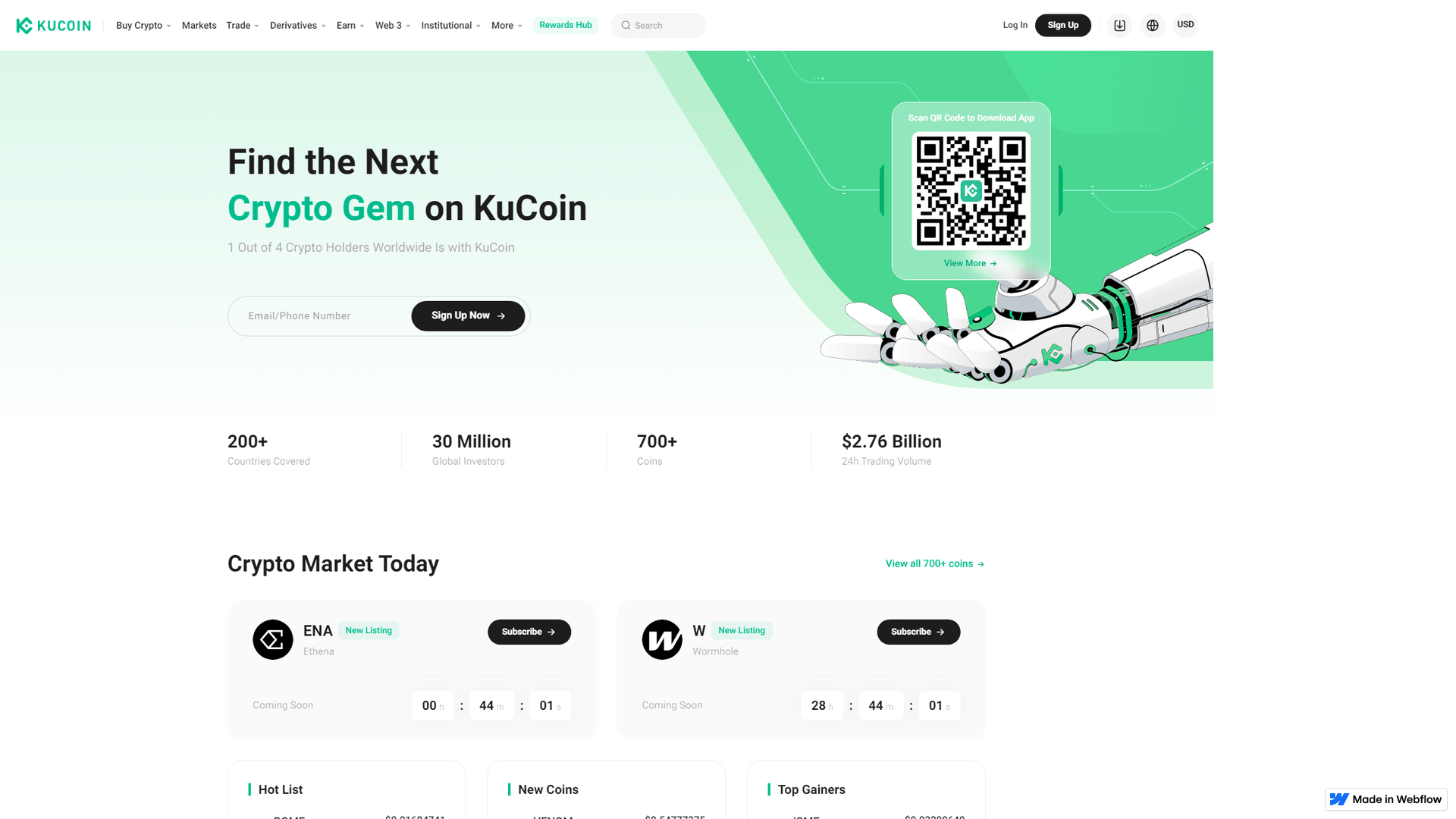
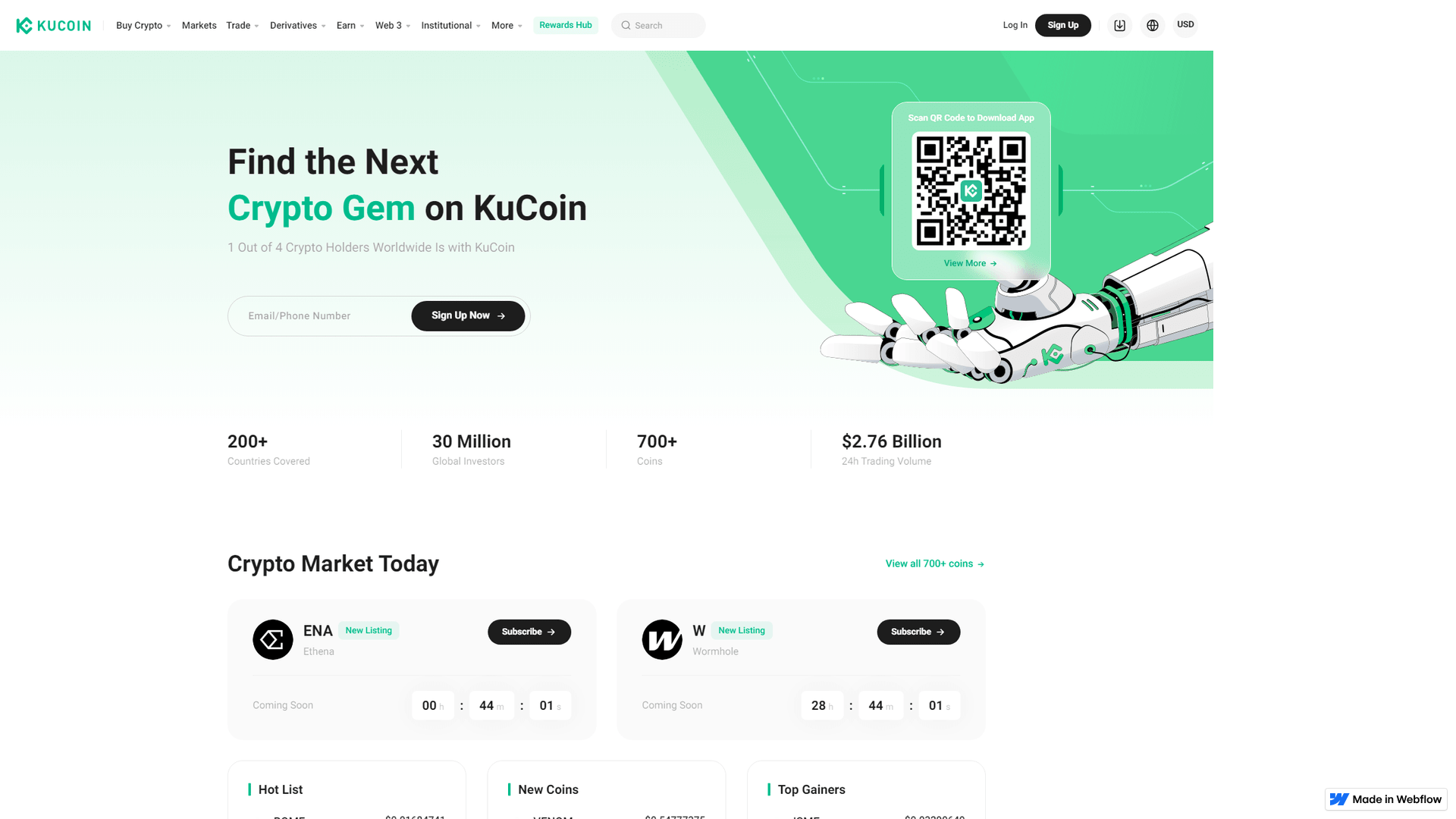
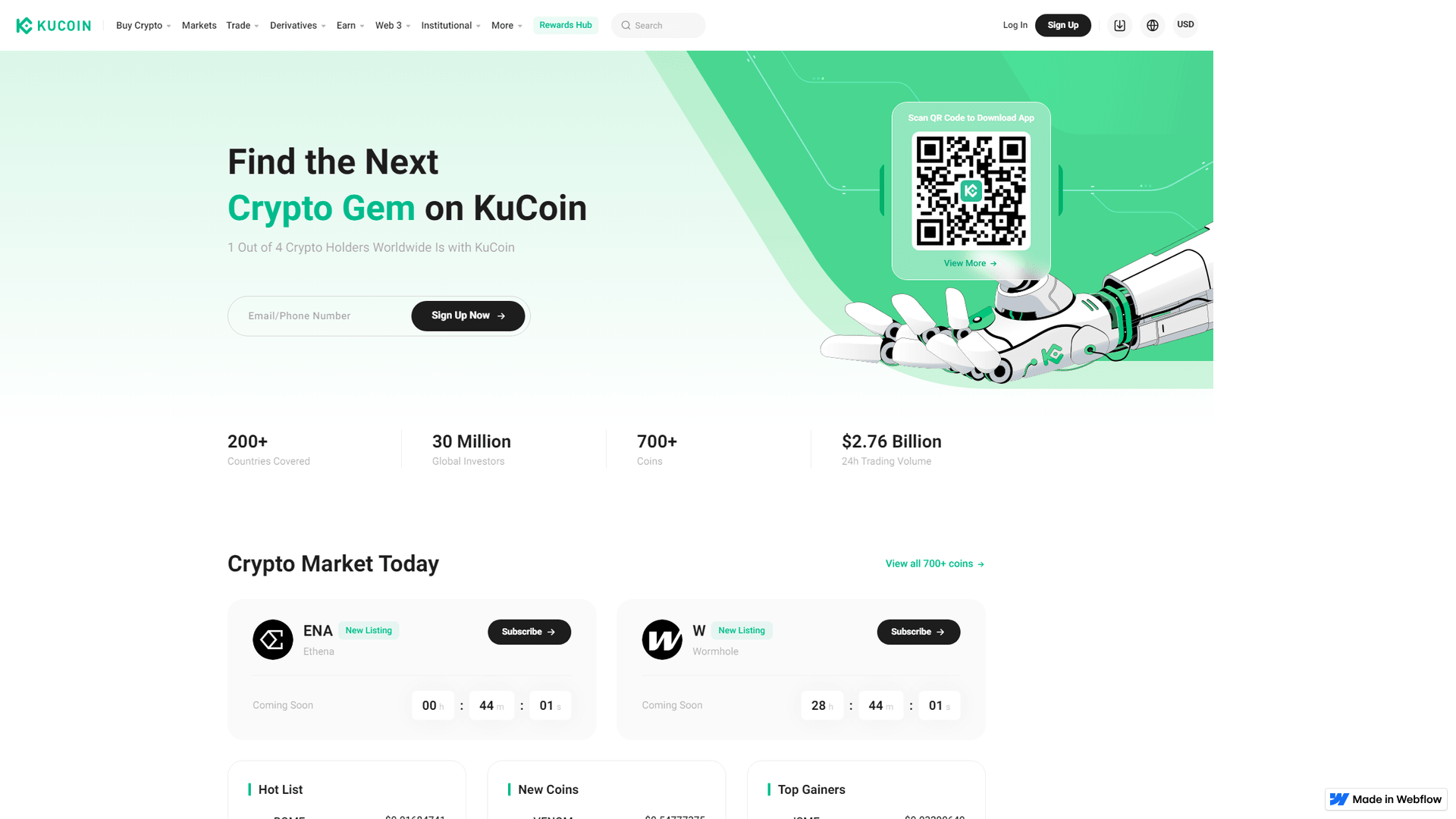
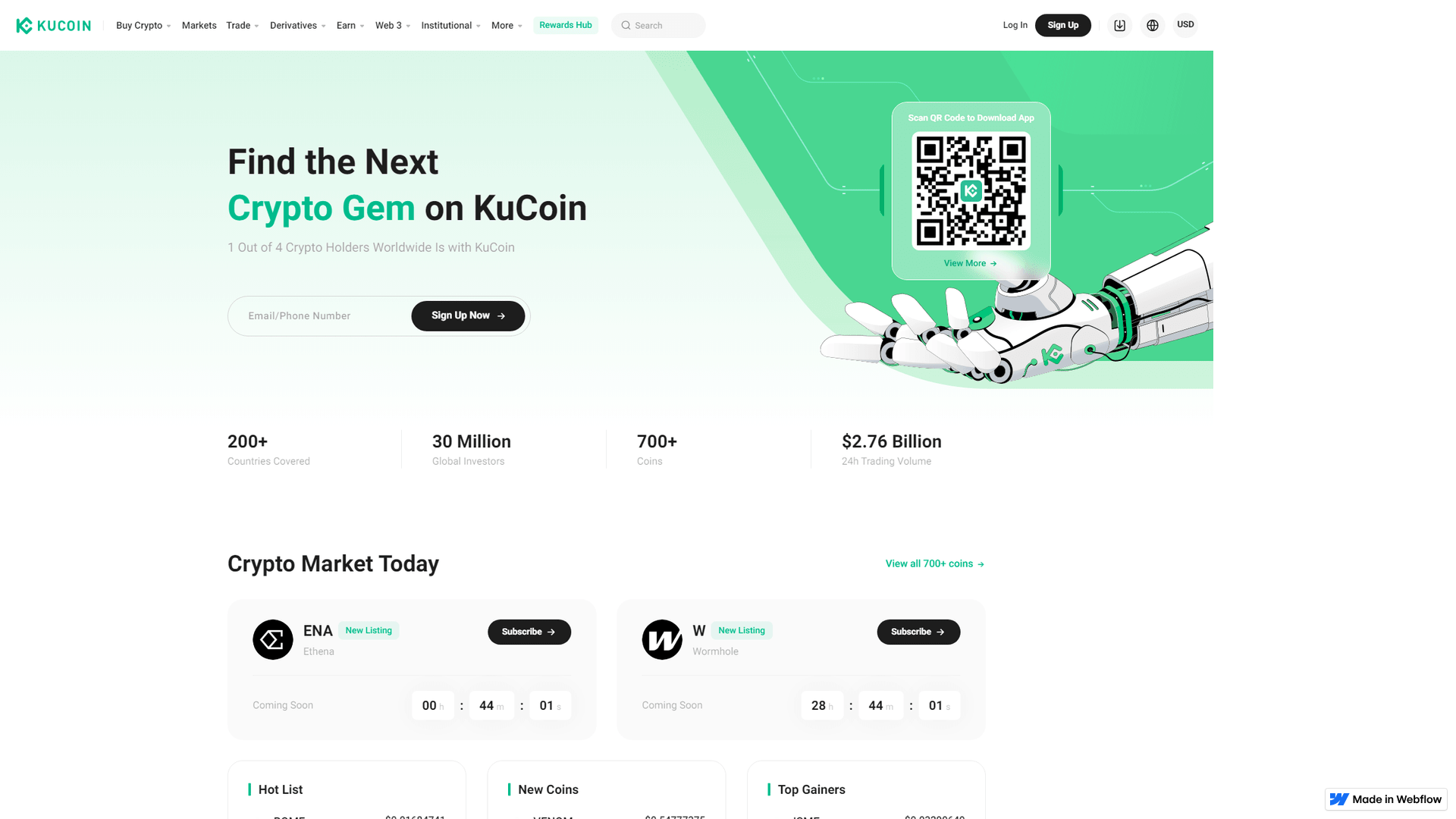
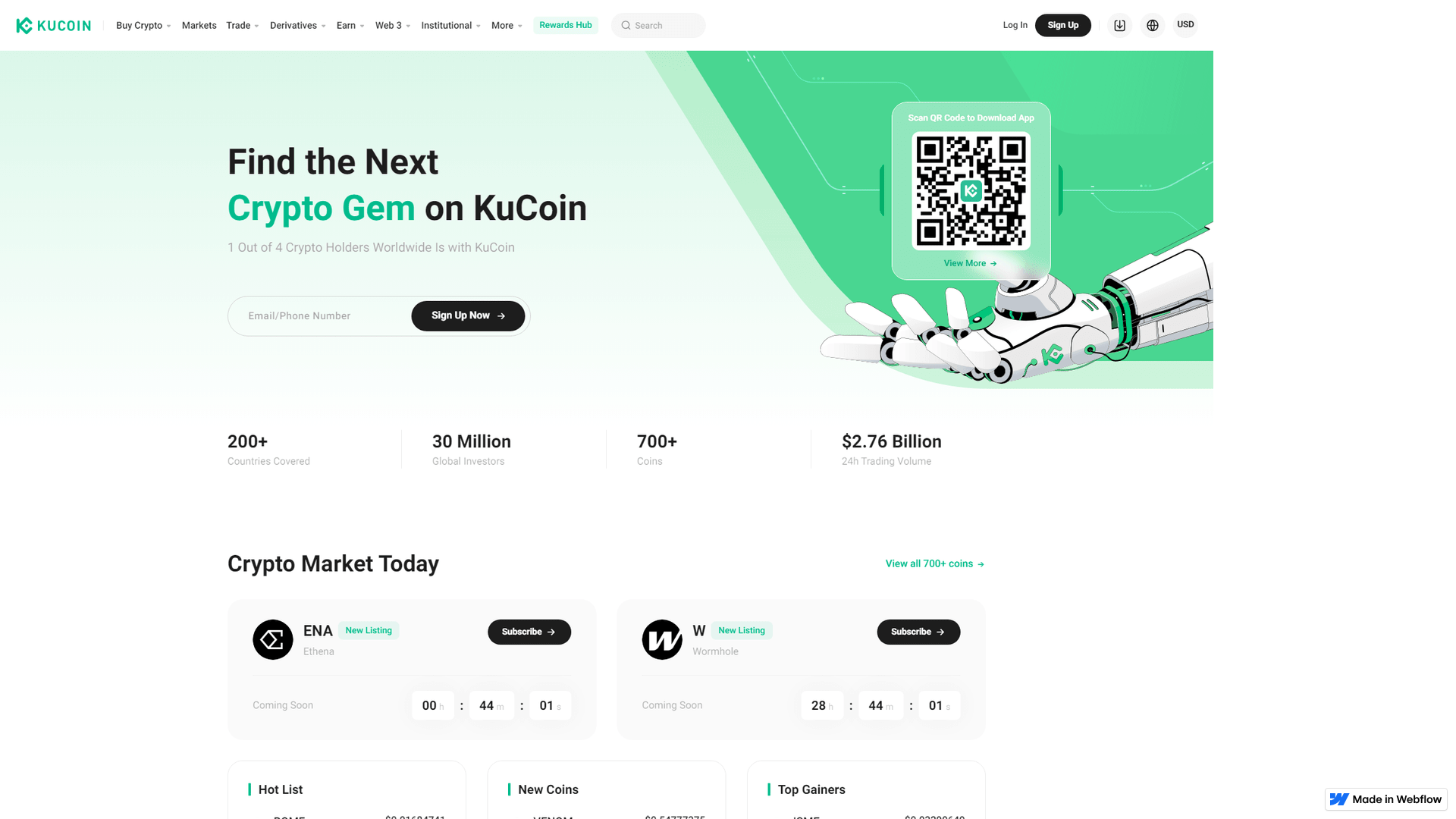
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T19981737795A8E815D320C3F86DA5229CE247918FC6C0D99776D2802E23FCA1D442BE65 |
|
CONTENT
ssdeep
|
96:tXv4a9TPSw/eARlHAttADAfAR11luuKo74ATON1r:9l9TPSwmsstE8XGON1r |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ec68669793999991 |
|
VISUAL
aHash
|
e18191d9ffff8fff |
|
VISUAL
dHash
|
e32733b34436562c |
|
VISUAL
wHash
|
010101d1ff9f83ff |
|
VISUAL
colorHash
|
07038000000 |
|
VISUAL
cropResistant
|
e32733b34436562c |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de KuCoin
• Método: Suplantación de identidad a través de un sitio web similar alojado en hosting gratuito.
• Exfil: Potencialmente robo de credenciales (correo electrónico/teléfono y contraseña)
• Indicadores: Hosting gratuito, logo de la marca, formularios
• Riesgo: Alto
🔒 Obfuscation Detected
- fromCharCode
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 2 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker is attempting to steal user's KuCoin account credentials by creating a fake login page that mimics the legitimate website's design. Users are tricked into entering their information into the malicious form.
Secondary Method: Social Engineering
The attacker may use various social engineering techniques to direct users to the fake site. This could include phishing emails, social media posts, or search engine optimization.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
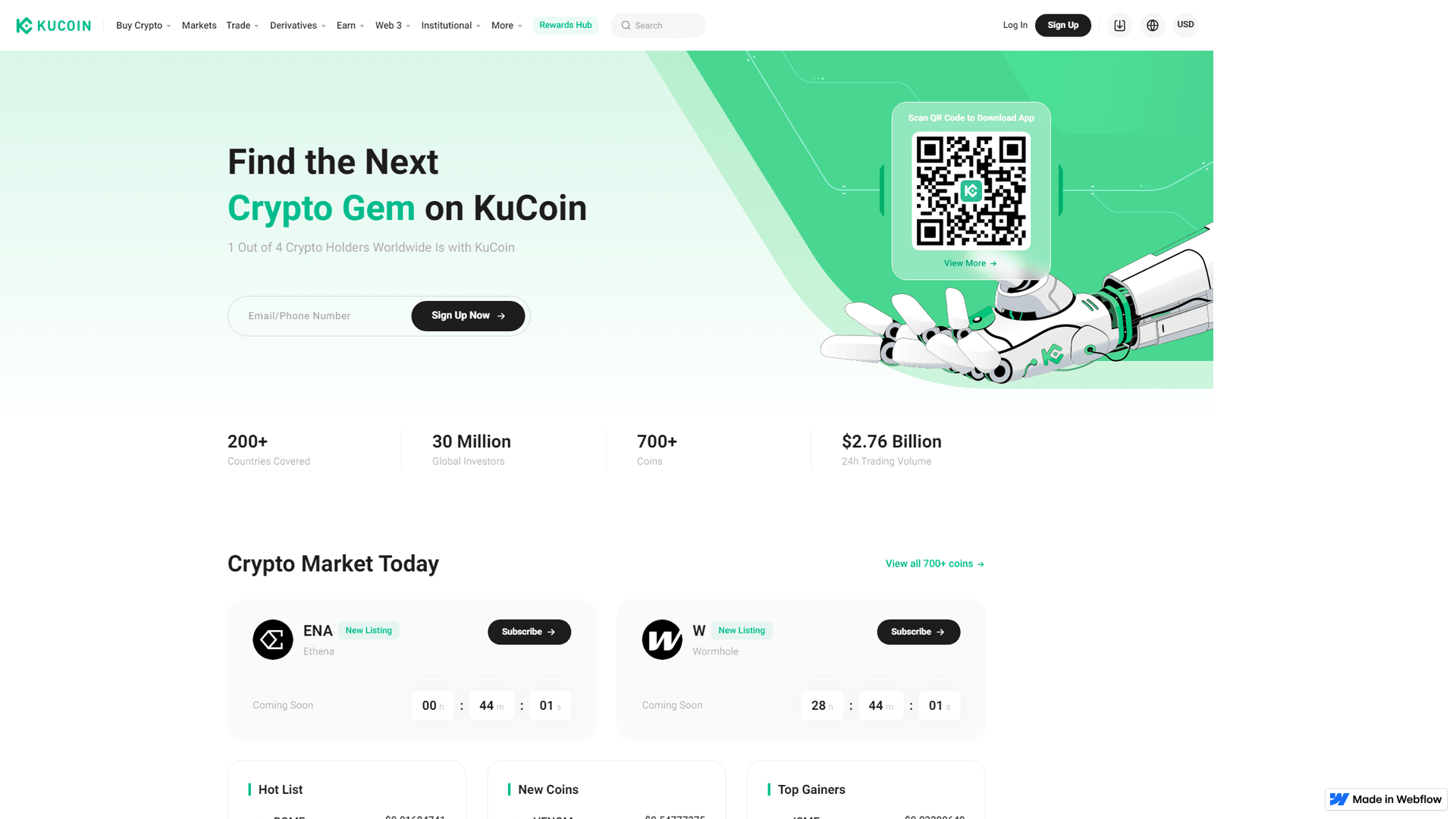
Scan History for oauth---en--sso----kucoin.webflow.io
Found 1 other scan for this domain
