
Phishing Analysis
Detailed analysis of captured phishing page
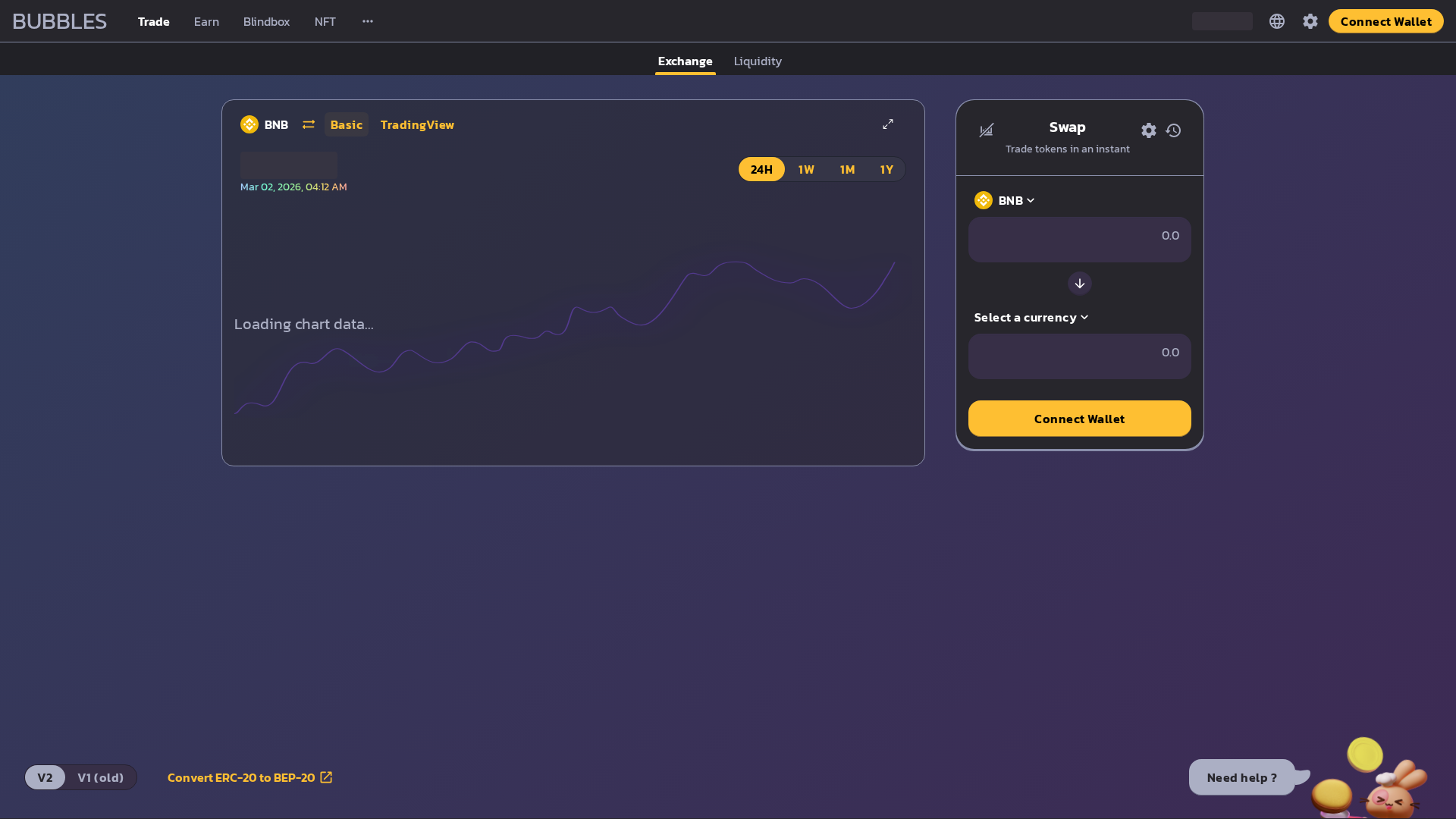
Captura Visual
Información de Detección
https://crackaf-bubbles-frontend.vercel.app/swap
Detected Brand
Binance or similar DeFi platform
Country
International
Confidence
100%
HTTP Status
200
Report ID
4938cb96-70d…
Analyzed
2026-03-02 03:12
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1BC2397F2828079AF43675BD1D312A6BF31AB303EDFDF2A51A2F487F46346DA09845485 |
|
CONTENT
ssdeep
|
384:PVLORUZRfDt+dfx/xnl+YZLXVVUTo1DvsA8dmeB2w/znBEuoiCsmsxyQdqqm:PVLo2+Bn0YZLXVVUTiiIevLBnCsmsAEm |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
be7a2952b64a2b16 |
|
VISUAL
aHash
|
01c8818686f8f4fb |
|
VISUAL
dHash
|
13131b0c0c030403 |
|
VISUAL
wHash
|
01c9818686fcfcfb |
|
VISUAL
colorHash
|
02001c00000 |
|
VISUAL
cropResistant
|
820578a696966986,13131b0c0c030403 |
Análisis de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de criptomonedas
• Método: Suplantación de identidad de una plataforma DeFi para robar información de la billetera.
• Exfil: Desconocido (probablemente apunta a las credenciales de la billetera y posiblemente a otra información personal).
• Indicadores: Alojamiento gratuito, logotipo de la marca en un dominio sospechoso.
• Riesgo: ALTO
🔒 Obfuscation Detected
- atob
- fromCharCode
- unicode_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- /nfts/collections
📡 API Calls Detected
- stats
- POST
- account
- proxy
- https://www.google.com/ccm/geo
- logs
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Free Hosting
The use of a free hosting provider (vercel.app) is a strong indicator of phishing.
Impersonation
The site attempts to impersonate a legitimate cryptocurrency exchange platform or its services.
Connect Wallet
The presence of a 'Connect Wallet' button on a suspicious domain strongly suggests credential theft.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Binance or similar DeFi platform users (International)
Método de Ataque
Brand impersonation + obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 224 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Likely Binance or another cryptocurrency trading platform
Official Website
null
Fake Service
Cryptocurrency Exchange / Wallet Connection
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The site uses a look-alike interface to lure users into connecting their cryptocurrency wallets, thereby allowing the attackers to steal the user's login details.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
crackaf-bubbles-frontend.vercel.app
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
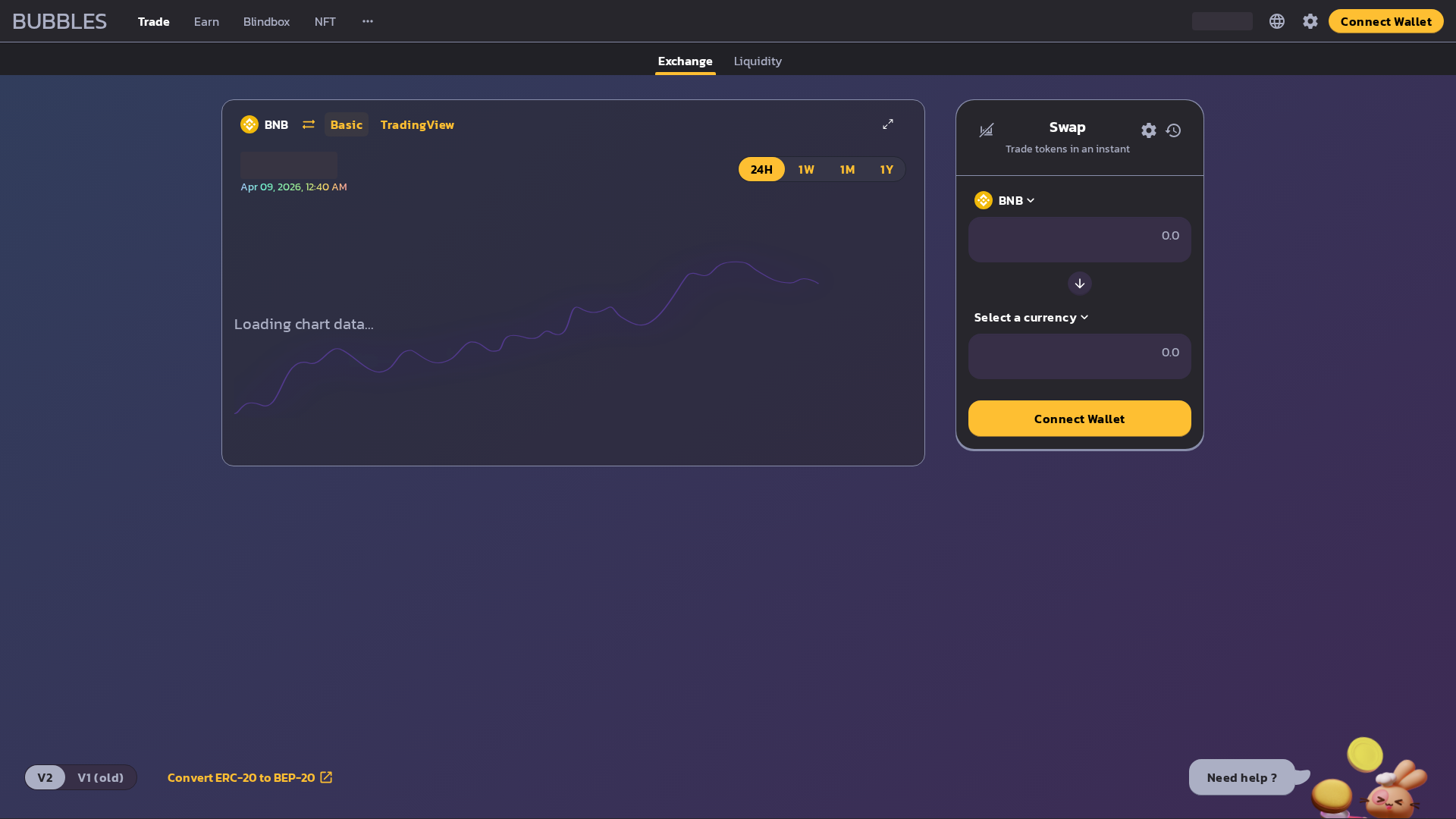
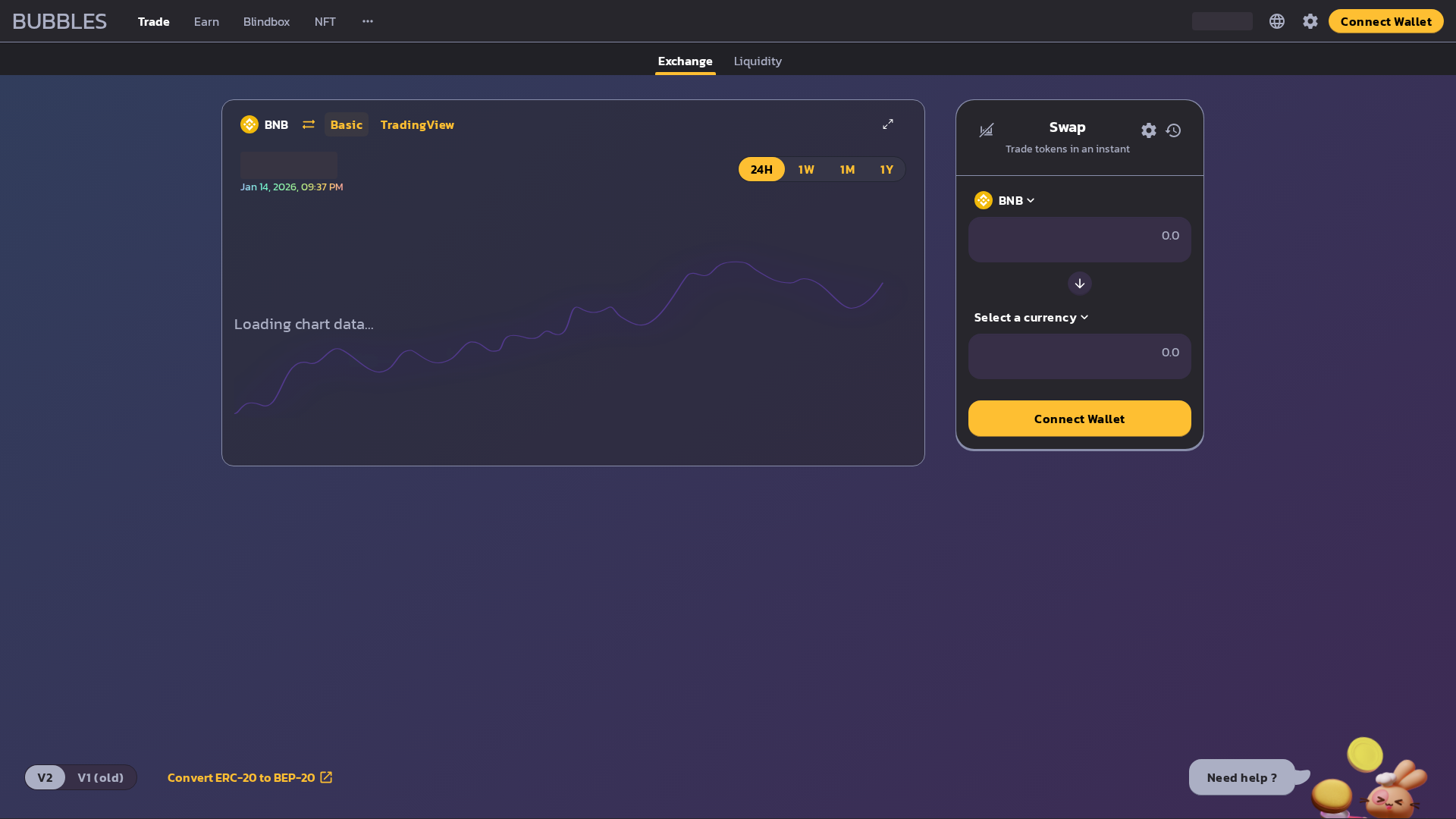
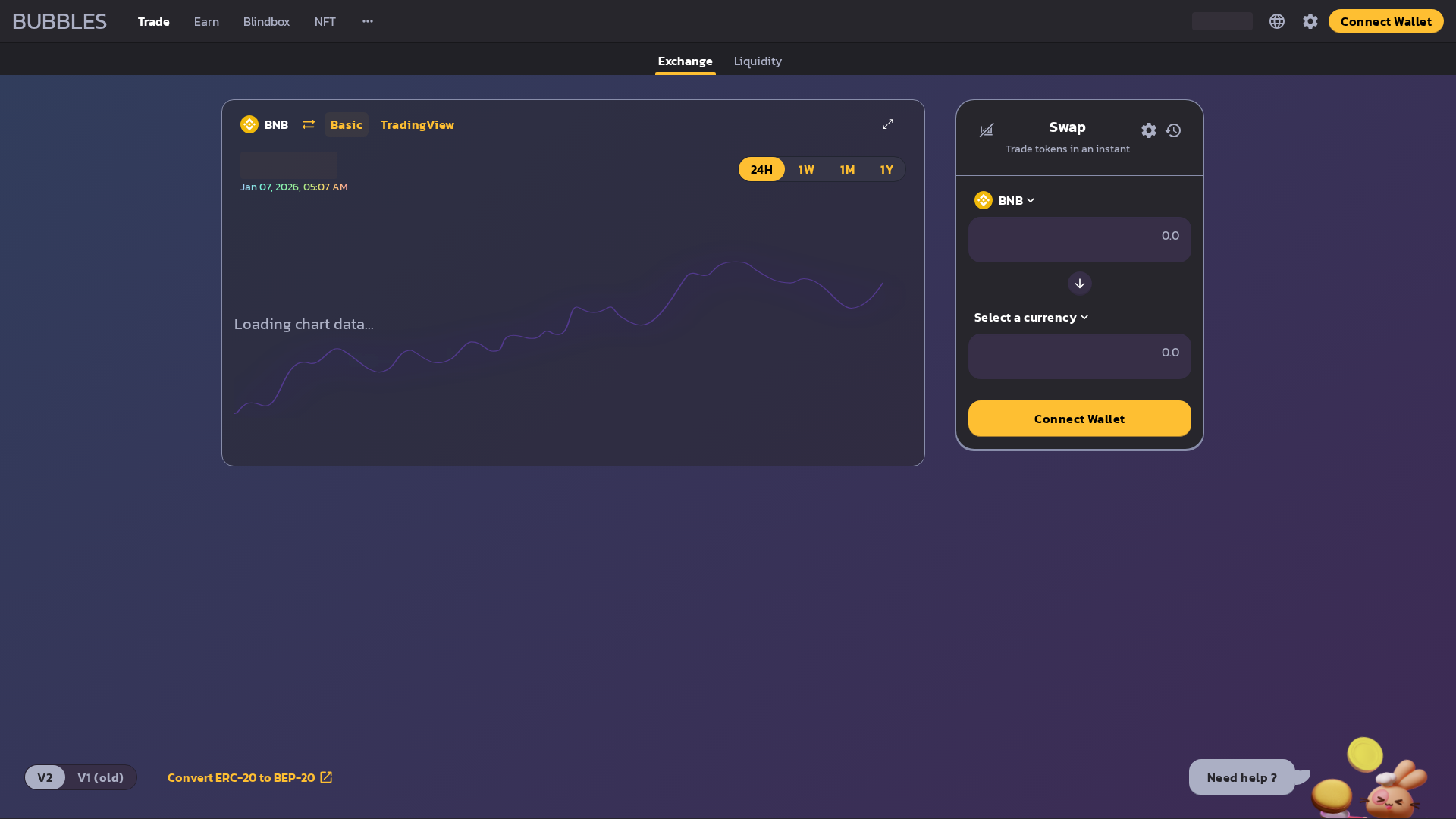
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
https://www.crackaf-bubbles-frontend.vercel.app/swap
Abr 08, 2026
BNB
http://crackaf-bubbles-frontend.vercel.app/swap
Ene 14, 2026
BNB
https://crackaf-bubbles-frontend.vercel.app/swap
Ene 07, 2026
No screenshot
Bubbles
http://crackaf-bubbles-frontend.vercel.app/swap
Dic 31, 2025
No screenshot
Bubbles
http://crackaf-bubbles-frontend.vercel.app/swap
Dic 21, 2025
Scan History for crackaf-bubbles-frontend.vercel.app
Found 10 other scans for this domain
-
https://www.crackaf-bubbles-frontend.vercel.app
https://www.crackaf-bubbles-frontend.vercel.app/sw...
https://www.crackaf-bubbles-frontend.vercel.app
https://www.crackaf-bubbles-frontend.vercel.app/
http://crackaf-bubbles-frontend.vercel.app/swap
http://crackaf-bubbles-frontend.vercel.app/
https://crackaf-bubbles-frontend.vercel.app/swap
http://crackaf-bubbles-frontend.vercel.app/swap
http://crackaf-bubbles-frontend.vercel.app/swap
https://crackaf-bubbles-frontend.vercel.app/

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.