
Phishing Analysis
Detailed analysis of captured phishing page
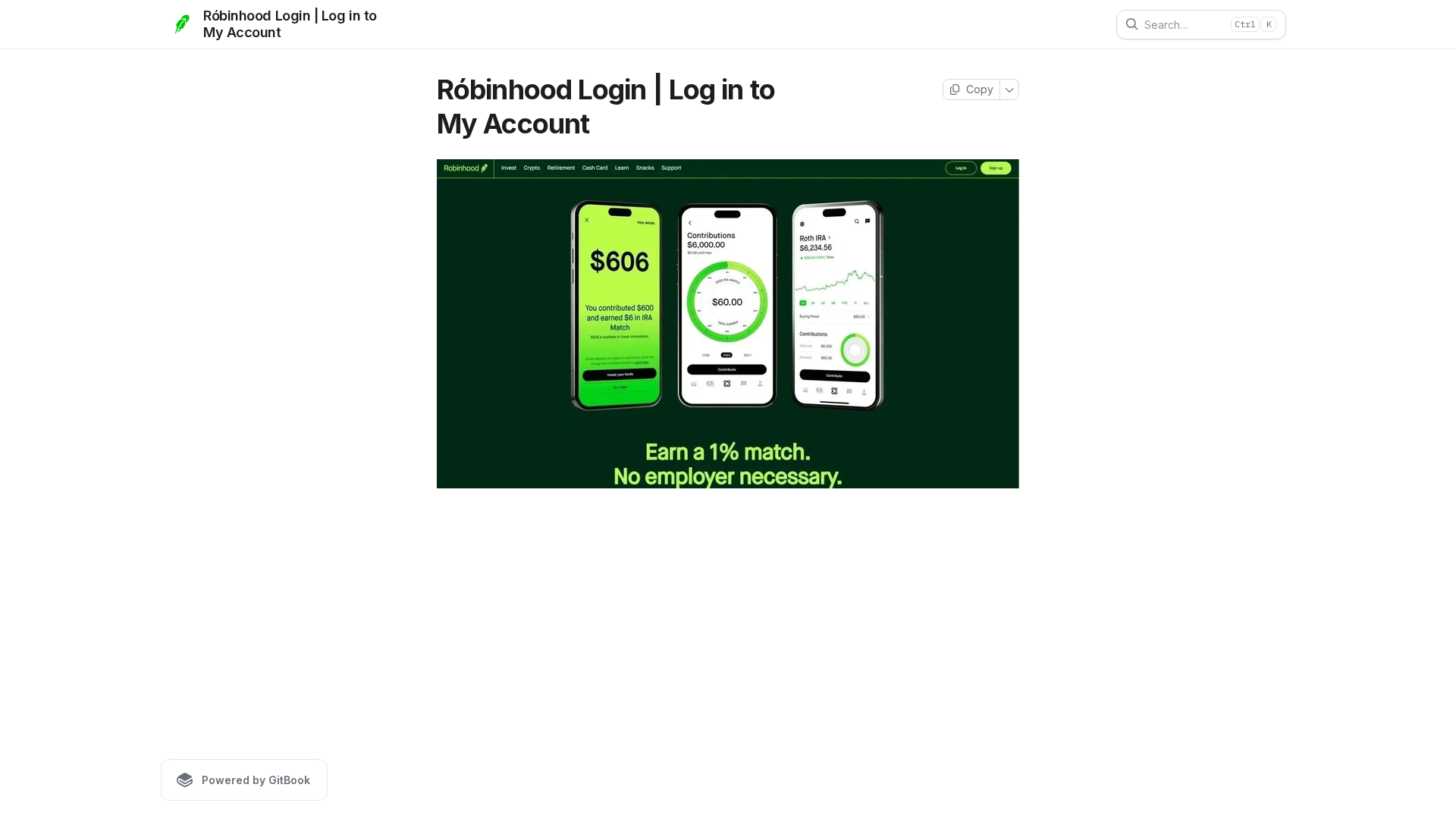
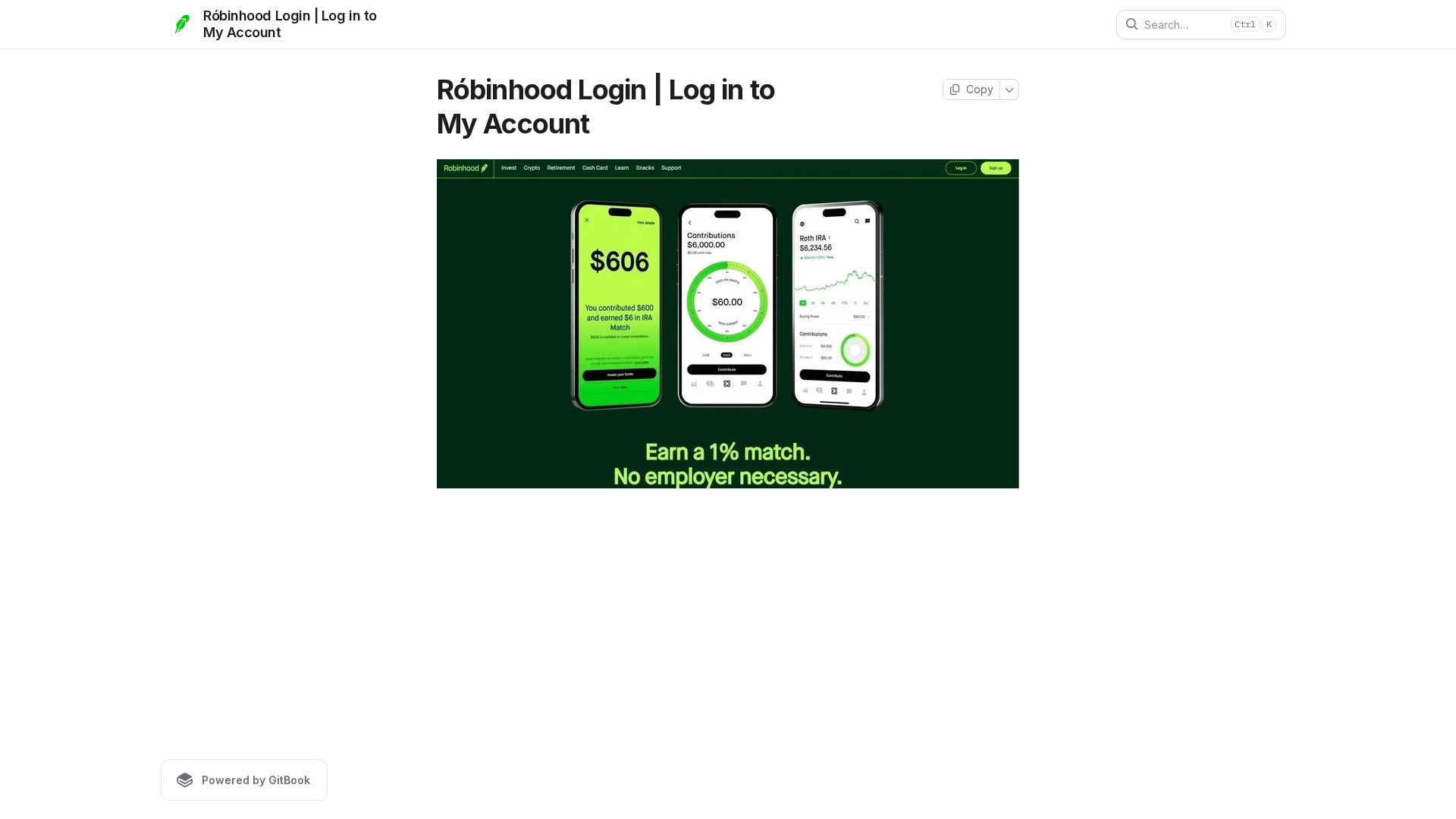
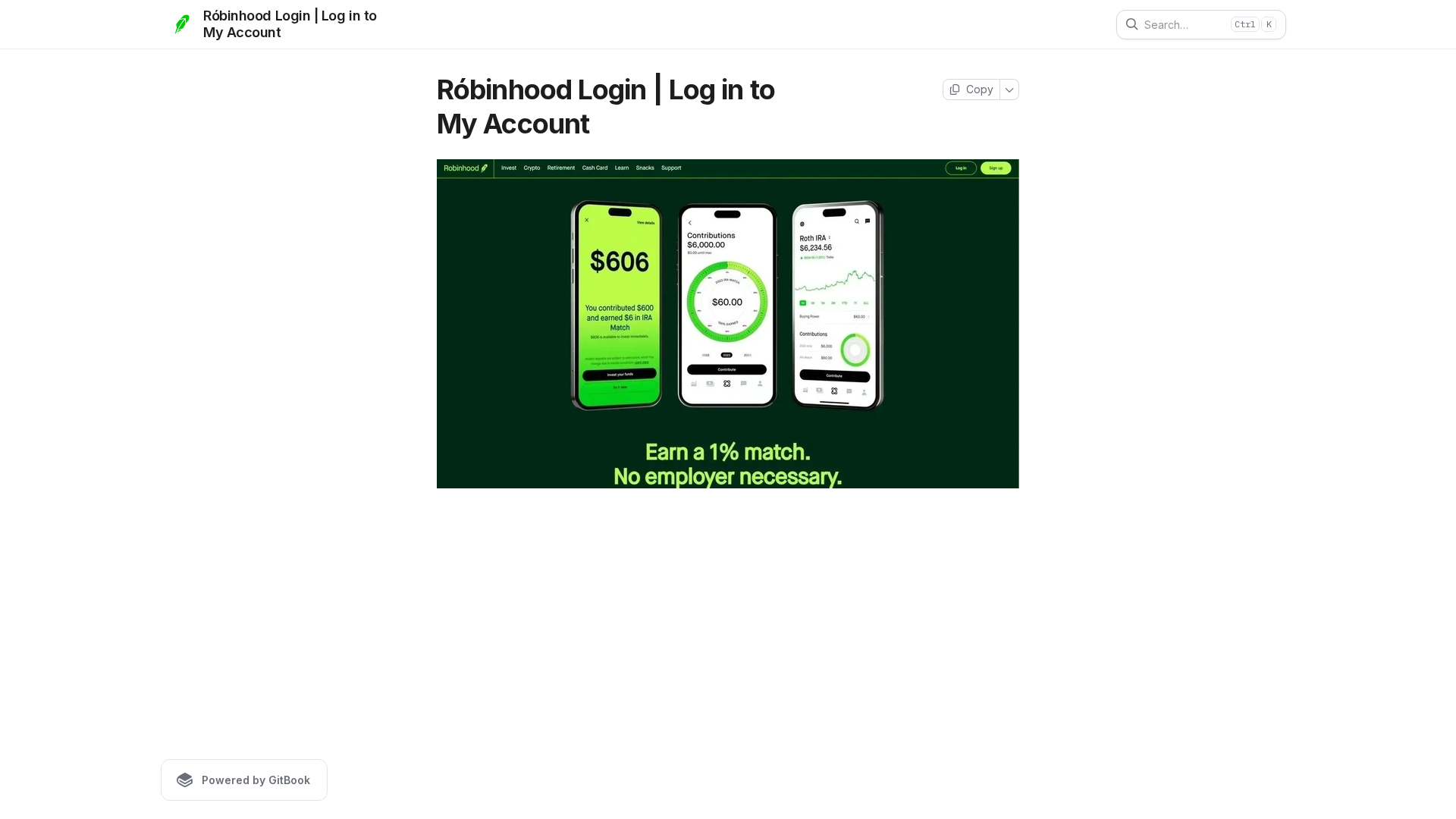
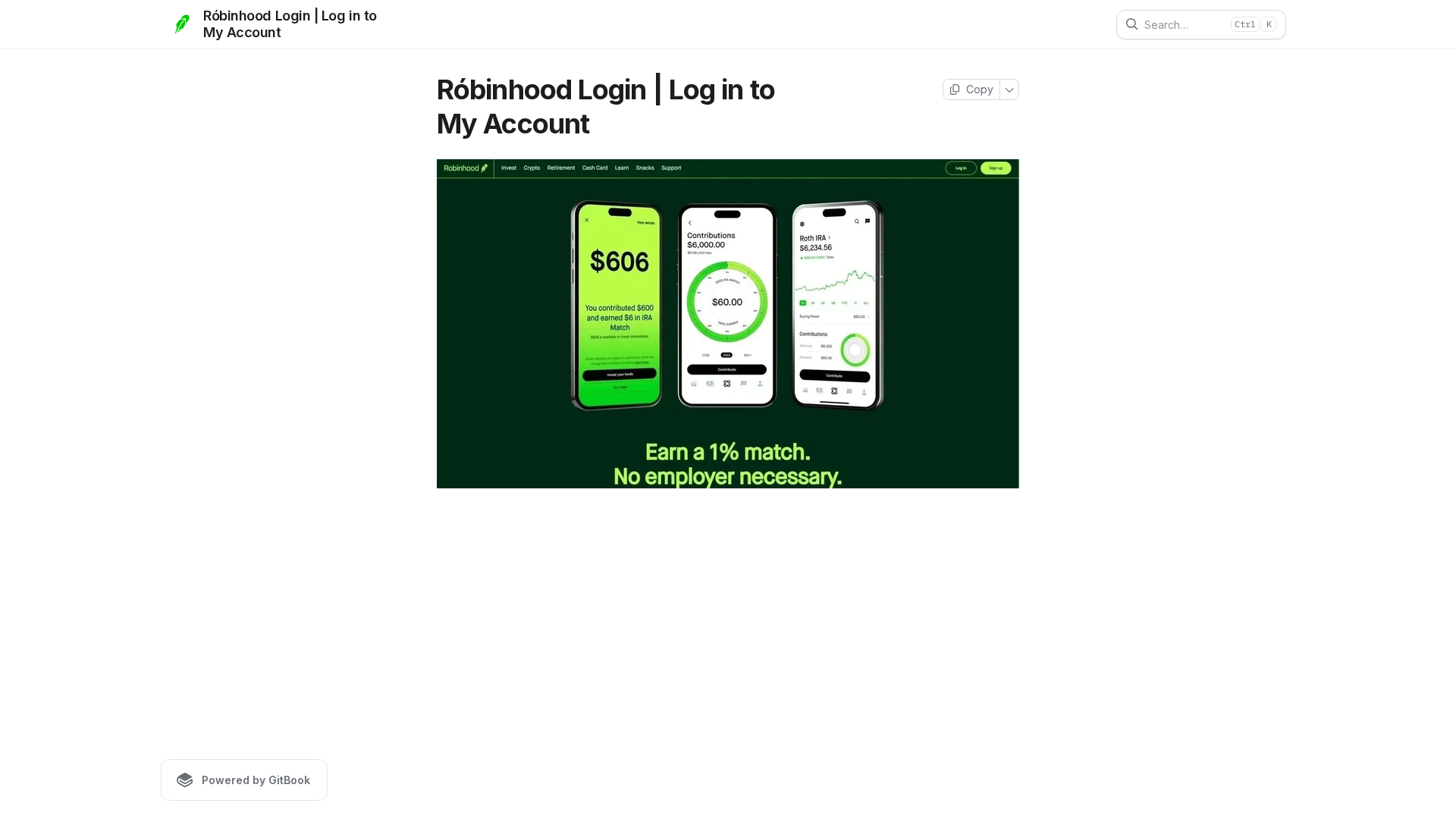
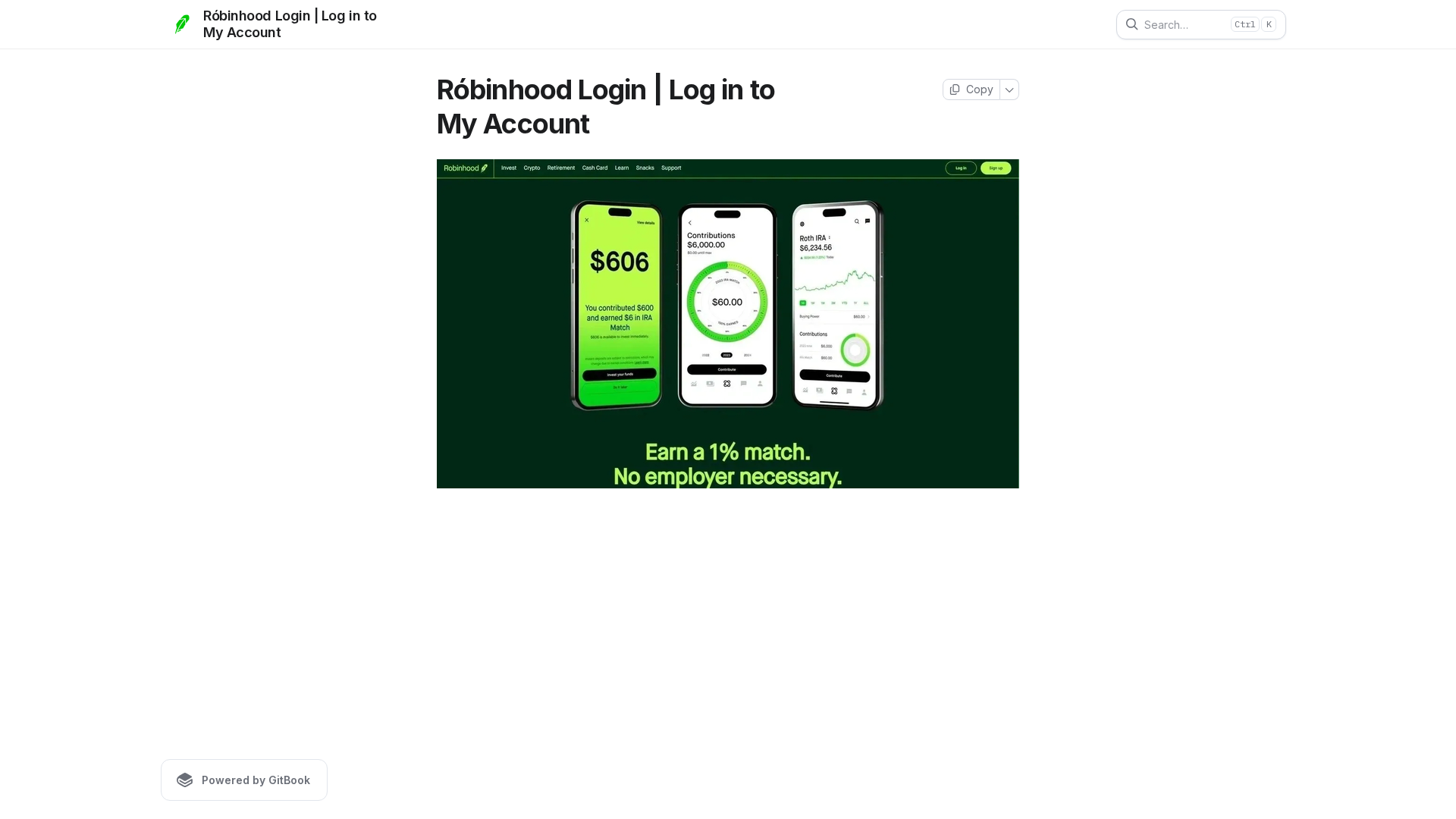
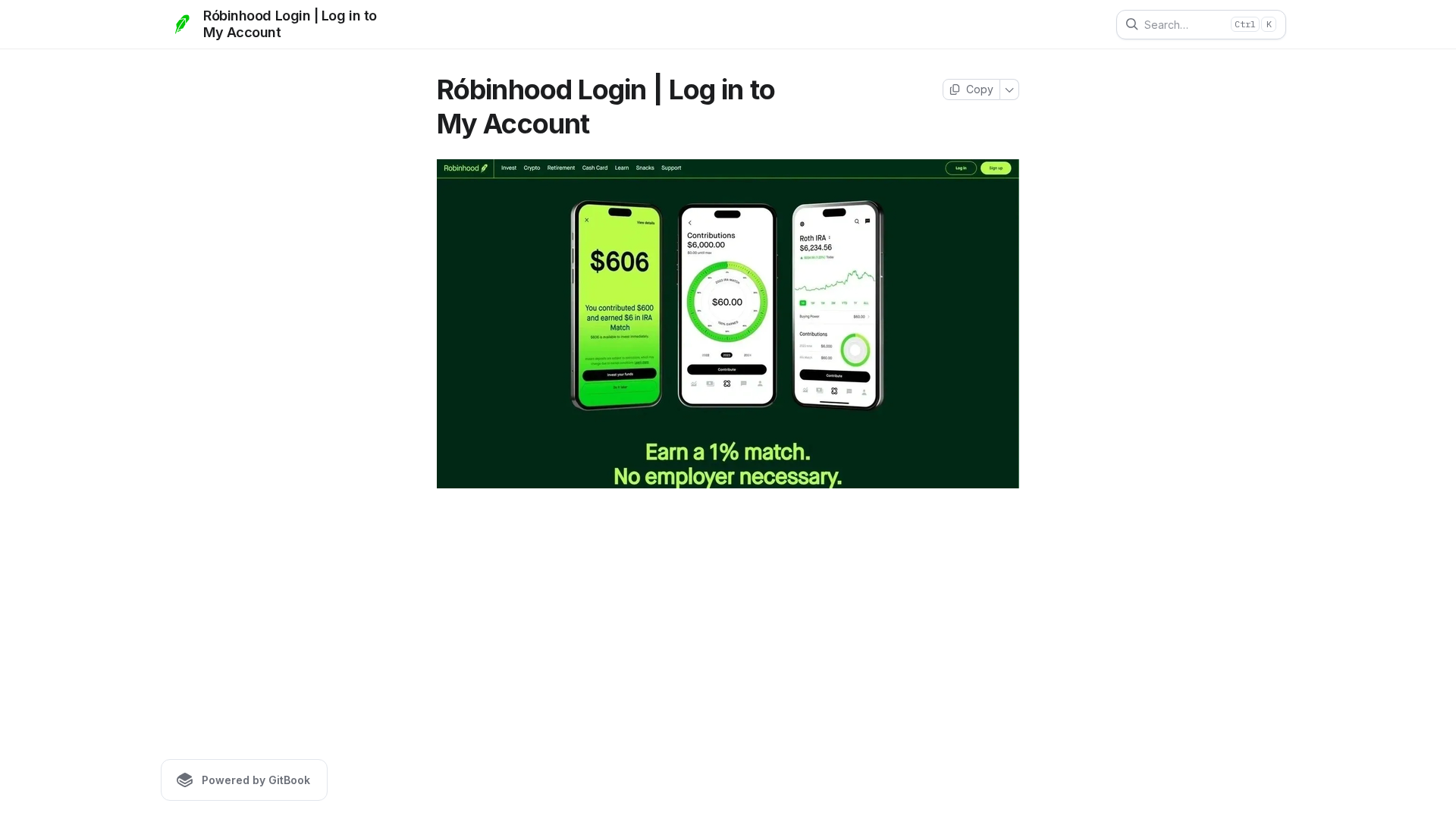
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16523E8512200769B58320F75B38B709AC0DED344FBE6A96DB2859322B4D2436C797DBE |
|
CONTENT
ssdeep
|
768:ghp9p5Y5IBZX6YPkPQnWy8RP5PXPIjPRfAPTPUL:ghp9p5Y5IBN6IZNfxL |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b1319e8635d9cd64 |
|
VISUAL
aHash
|
ffc3c3c3c3ffffff |
|
VISUAL
dHash
|
7196969696001640 |
|
VISUAL
wHash
|
00c3c3c3033fcf0f |
|
VISUAL
colorHash
|
06080003200 |
|
VISUAL
cropResistant
|
7196969696001640,ccf09a82deb29696,ccb02b2bd00d8fb1,8cb89e3adce8aa8e,0dd5d555f5f57161 |
Análisis de Código
🔒 Obfuscation Detected
- atob
- fromCharCode
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://robinhood-logne.gitbook.io/account/robinhood-login-or-log-in-to-my-account.md
- https://robinhood-logne.gitbook.io/account/~gitbook/image?url=https%3A%2F%2F2100530087-files.gitbook.io%2F%7E%2Ffiles%2Fv0%2Fb%2Fgitbook-x-prod.appspot.com%2Fo%2Fspaces%252FpEvGreYN7Uw5xPYSKEop%252Ficon%252FYX2UyOSHI5dkDXsXvuO2%252Frobinhood.png%3Falt%3Dmedia%26token%3D1e985086-611f-4a4c-9e76-958ca67b27e3&width=48&height=48&sign=9ce4b092&sv=2
- https://robinhood-logne.gitbook.io/account/~gitbook/image?url=https%3A%2F%2F2100530087-files.gitbook.io%2F%7E%2Ffiles%2Fv0%2Fb%2Fgitbook-x-prod.appspot.com%2Fo%2Fspaces%252FpEvGreYN7Uw5xPYSKEop%252Ficon%252FYX2UyOSHI5dkDXsXvuO2%252Frobinhood.png%3Falt%3Dmedia%26token%3D1e985086-611f-4a4c-9e76-958ca67b27e3&width=32&dpr=3&quality=100&sign=9ce4b092&sv=2
- https://robinhood-logne.gitbook.io/account/~gitbook/image?url=https%3A%2F%2F2100530087-files.gitbook.io%2F%7E%2Ffiles%2Fv0%2Fb%2Fgitbook-x-prod.appspot.com%2Fo%2Fspaces%252FpEvGreYN7Uw5xPYSKEop%252Ficon%252FYX2UyOSHI5dkDXsXvuO2%252Frobinhood.png%3Falt%3Dmedia%26token%3D1e985086-611f-4a4c-9e76-958ca67b27e3&width=180&height=180&sign=9ce4b092&sv=2
- https://robinhood-logne.gitbook.io/account
- https://robinhood-logne.gitbook.io/account/~gitbook/image?url=https%3A%2F%2F2100530087-files.gitbook.io%2F%7E%2Ffiles%2Fv0%2Fb%2Fgitbook-x-prod.appspot.com%2Fo%2Fspaces%252FpEvGreYN7Uw5xPYSKEop%252Fuploads%252FeSf8GcHUtw9Lp04mexaR%252Fnew%2520robbin.webp%3Falt%3Dmedia%26token%3Da647d8f2-6256-4957-9814-e21aa3a9e133&width=768&dpr=3&quality=100&sign=44a36ba8&sv=2
- https://robinhood-logne.gitbook.io/account/rss.xml
📡 API Calls Detected
- virtual
- first
- _blank
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 357 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 357 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for robinhood-logne.gitbook.io
Found 1 other scan for this domain
