
Phishing Analysis
Detailed analysis of captured phishing page
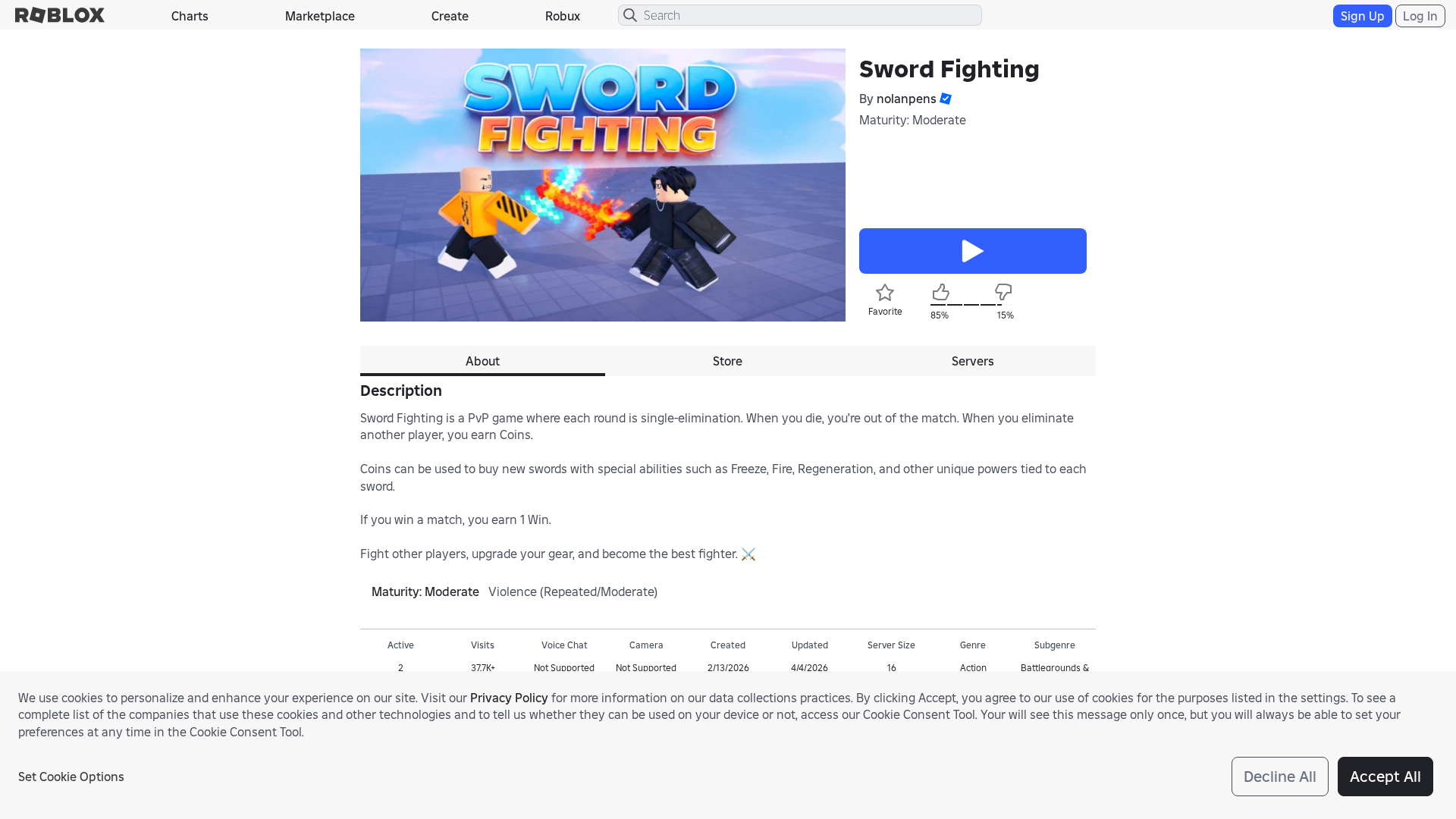
Captura Visual
Información de Detección
https://roblox.com.ge/games/107864120223329/Sword-Fighting?privateServerLinkCode=84004407555862227890023517560389
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
4b872466-250…
Analyzed
2026-04-05 02:25
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T10613EA72A1202837A1AFA3D5F515B716A1D3E70ECB8357E2A1F4637A0AD9C31FD1341A |
|
CONTENT
ssdeep
|
768:nUXB1JySQ2yu2Kby6MjVdrvrvEQ3KmOuvBRW8A1F9NpBxJ8m8:nUXB1Jyn2f2KajMS/XW9NTxJ8m8 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b03057cfcd8c746c |
|
VISUAL
aHash
|
c7c7c3cffffffffe |
|
VISUAL
dHash
|
9e0f8e1e36181bc0 |
|
VISUAL
wHash
|
42c7c3c7dfdf0104 |
|
VISUAL
colorHash
|
07007000040 |
|
VISUAL
cropResistant
|
9e0f8e1e36181bc0,a6e6e66636d6f2a4 |
Análisis de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /catalog
- /login?returnUrl=9899221085181440
- https://roblox.com.ge/catalog?CatalogContext=1&Keyword=
- https://roblox.com.ge/info/blog?locale=en_us
📡 API Calls Detected
- https://apis.
- POST
- get
- GET
- https://en.help.roblox.com/hc/articles/7997207259156
- https://ro.blox.com/Ebh5?pid=experiencestart_mobileweb&is_retargeting=false&af_dp=
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 180 technique(s) to evade detection
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Roblox users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
HTTP POST to backend
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 180 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 180 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
roblox.com.ge
Registered
2025-08-21 00:00:00+00:00
Registrar
domenebi.ge
Status
Active (227 days old)
Hosting Information
Provider
domenebi.ge
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for roblox.com.ge
Found 10 other scans for this domain
-
http://roblox.com.ge/users/5444670953/profile
https://roblox.com.ge/users/4315481918/profile/
https://roblox.com.ge/users/4055073701/profile/
https://roblox.com.ge/users/563694698/profile
https://roblox.com.ge/users/3788468315/profile
https://roblox.com.ge/users/1799479109/profile/
https://roblox.com.ge/users/8734399446/profile?clc...
https://roblox.com.ge/communities/7756774386/
https://roblox.com.ge/communities/5612844815/Great...
https://roblox.com.ge/users/7533428443/profile/

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.