Phishing Analysis
Detailed analysis of captured phishing page
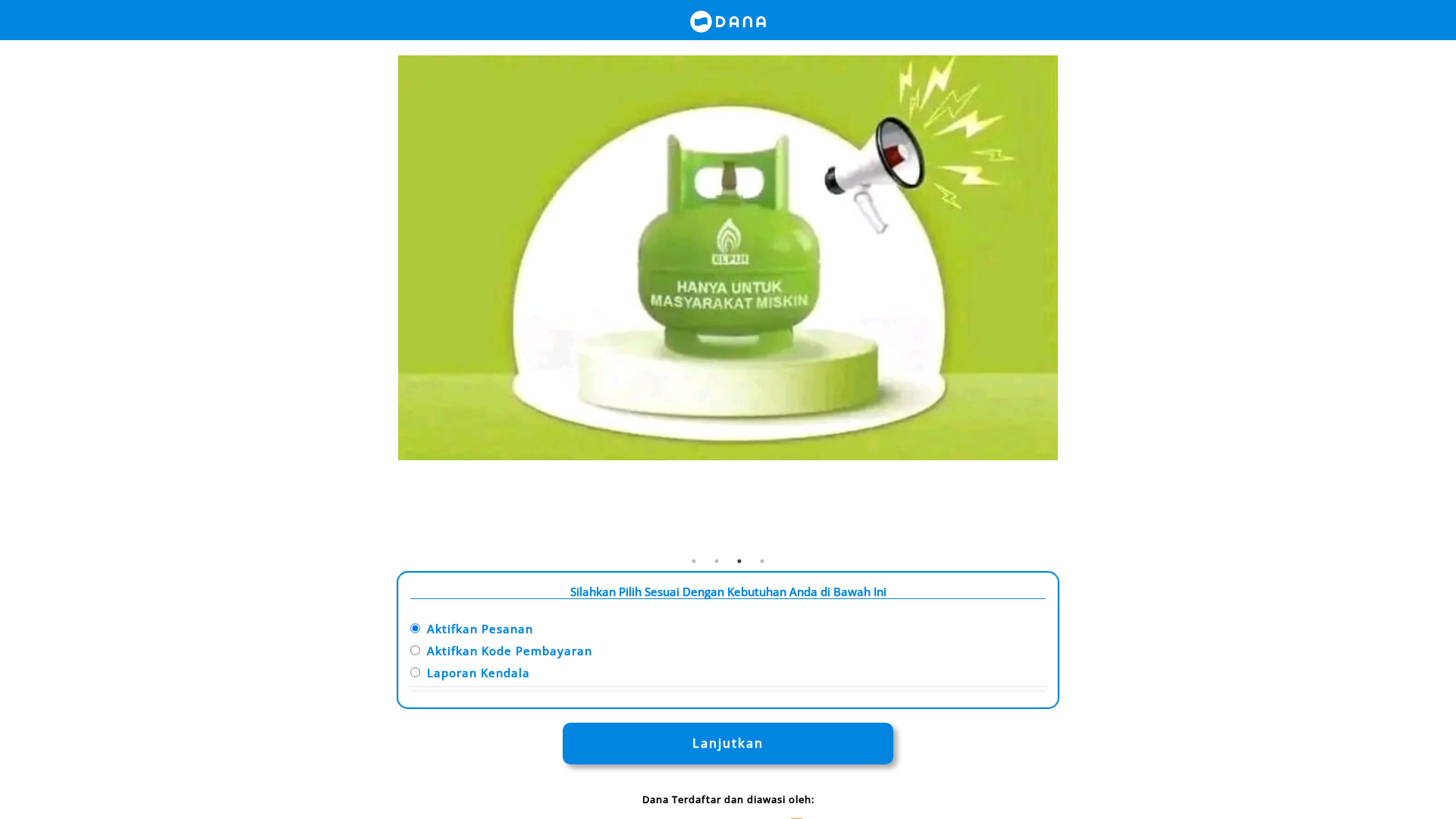
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12A0274B28404542B121281C97667FB4E60839346CF761851A7D543AFBAEEAF0DCBB397 |
|
CONTENT
ssdeep
|
192:BSiS7oiwQcYIhFB+unhnzgJ3OUz3NXTX2a:BSiS7oiwQ8f9UOU3NXTXB |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f46d1319665e5313 |
|
VISUAL
aHash
|
00c3c3c3d3ffffe7 |
|
VISUAL
dHash
|
1616aaae16080e4d |
|
VISUAL
wHash
|
00c3c3c3c3c7cbe7 |
|
VISUAL
colorHash
|
06040006080 |
|
VISUAL
cropResistant
|
9616aaa616080e4d,0000343430303410 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de DANA
• Método: Suplantación de identidad a través de una página similar.
• Exfil: login.php (acción de formulario)
• Indicadores: Desajuste de dominio, ofuscación de JavaScript, formularios detectados.
• Riesgo: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
🎯 Kit Endpoints
- login.php
📡 API Calls Detected
- POST
📤 Form Action Targets
- login.php
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 2 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker likely aims to steal user credentials by creating a fake login page that mimics DANA. Users are tricked into entering their information which is then captured by the attacker via the login.php form action
Secondary Method: Malware distribution
The site may be distributing malware through malicious Javascript code.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for exe.senx.biz.id
Found 3 other scans for this domain