Phishing Analysis
Detailed analysis of captured phishing page
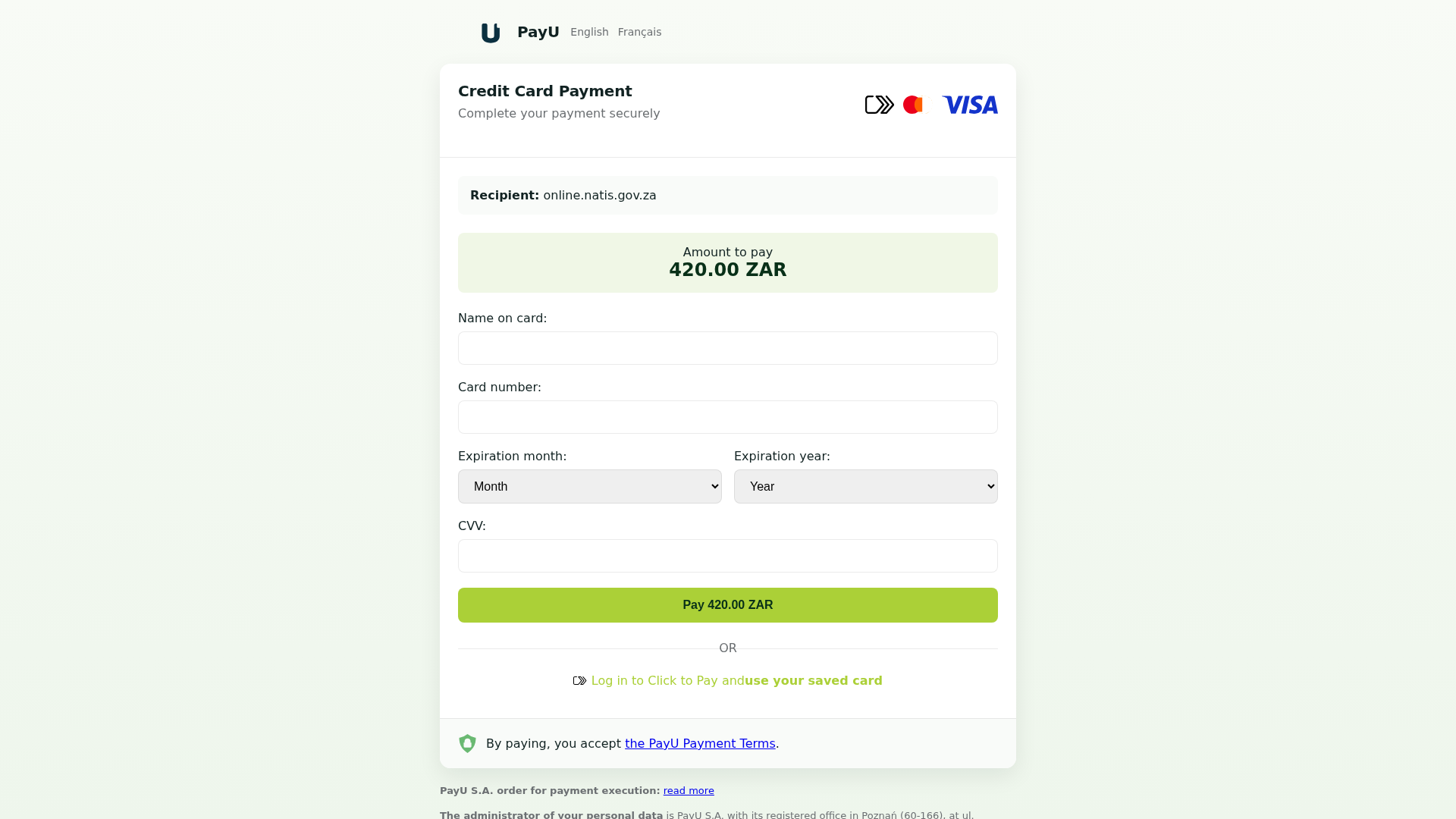
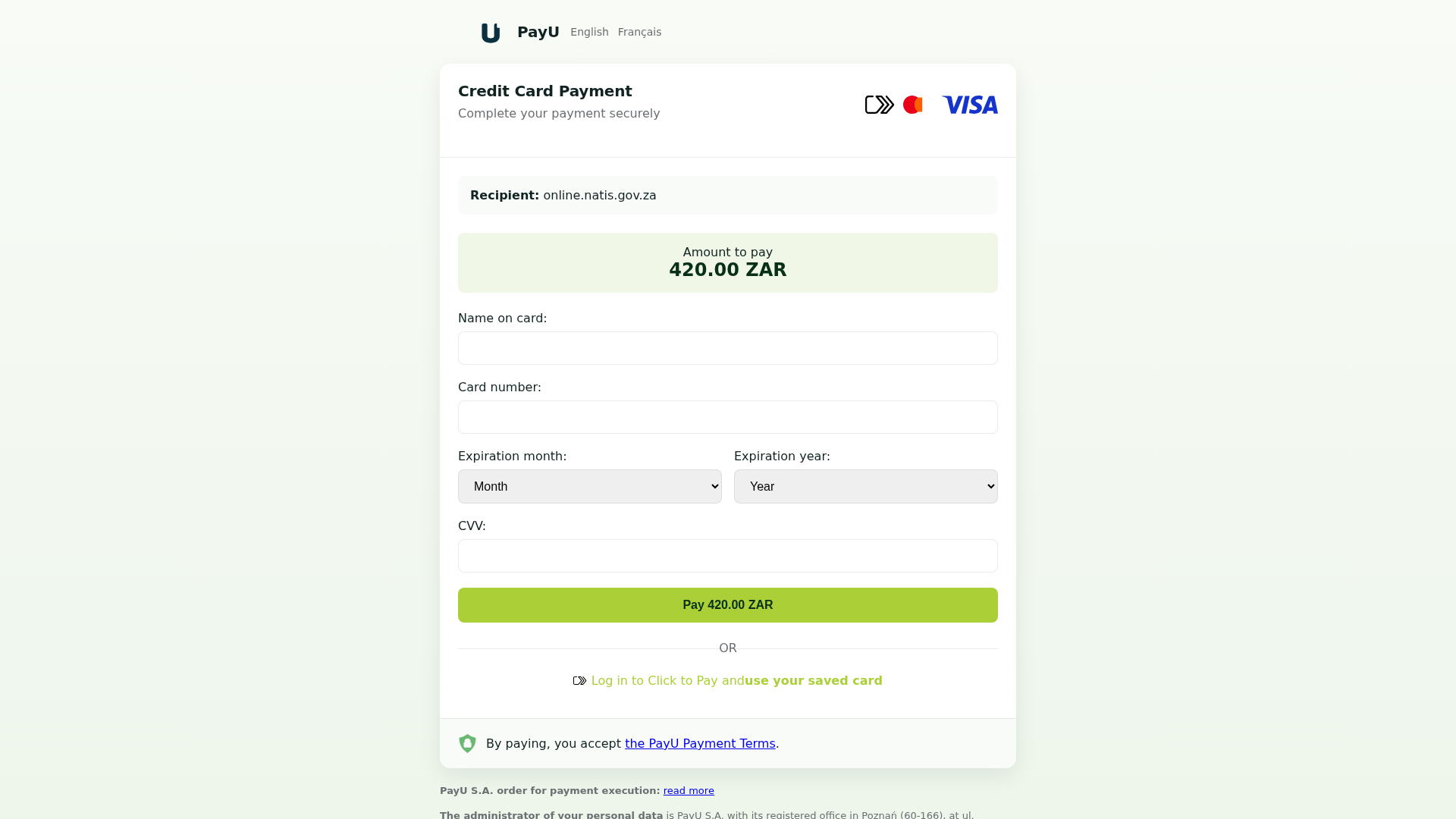
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1B93299E16758D868248F5AD4DF7B095D232AD2B9B782004CF5EDC7E48693CA9CE33D84 |
|
CONTENT
ssdeep
|
192:sESC0ak3PEPgv4+aGl5gnLpnC63PDZpak3PEP16XVZjBaDuG:feQoSFC633QAXVKDuG |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b1d9316c98e6339a |
|
VISUAL
aHash
|
cbdfe7ff3d000000 |
|
VISUAL
dHash
|
96128839310e4c19 |
|
VISUAL
wHash
|
cfdfe7df14003c00 |
|
VISUAL
colorHash
|
07000006000 |
|
VISUAL
cropResistant
|
96128839310e4c19 |
Análisis de Código
🔐 Credential Harvesting Forms
🎯 Kit Endpoints
- #/clicktopay/login
📡 API Calls Detected
- GET
📤 Form Action Targets
- ../system/Processing.php
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Card Stealer
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Payment Card Theft
Victim enters credit/debit card details including CVV and expiration. Card data is captured and can be used for fraudulent transactions or sold on dark web markets.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)