
Phishing Analysis
Detailed analysis of captured phishing page
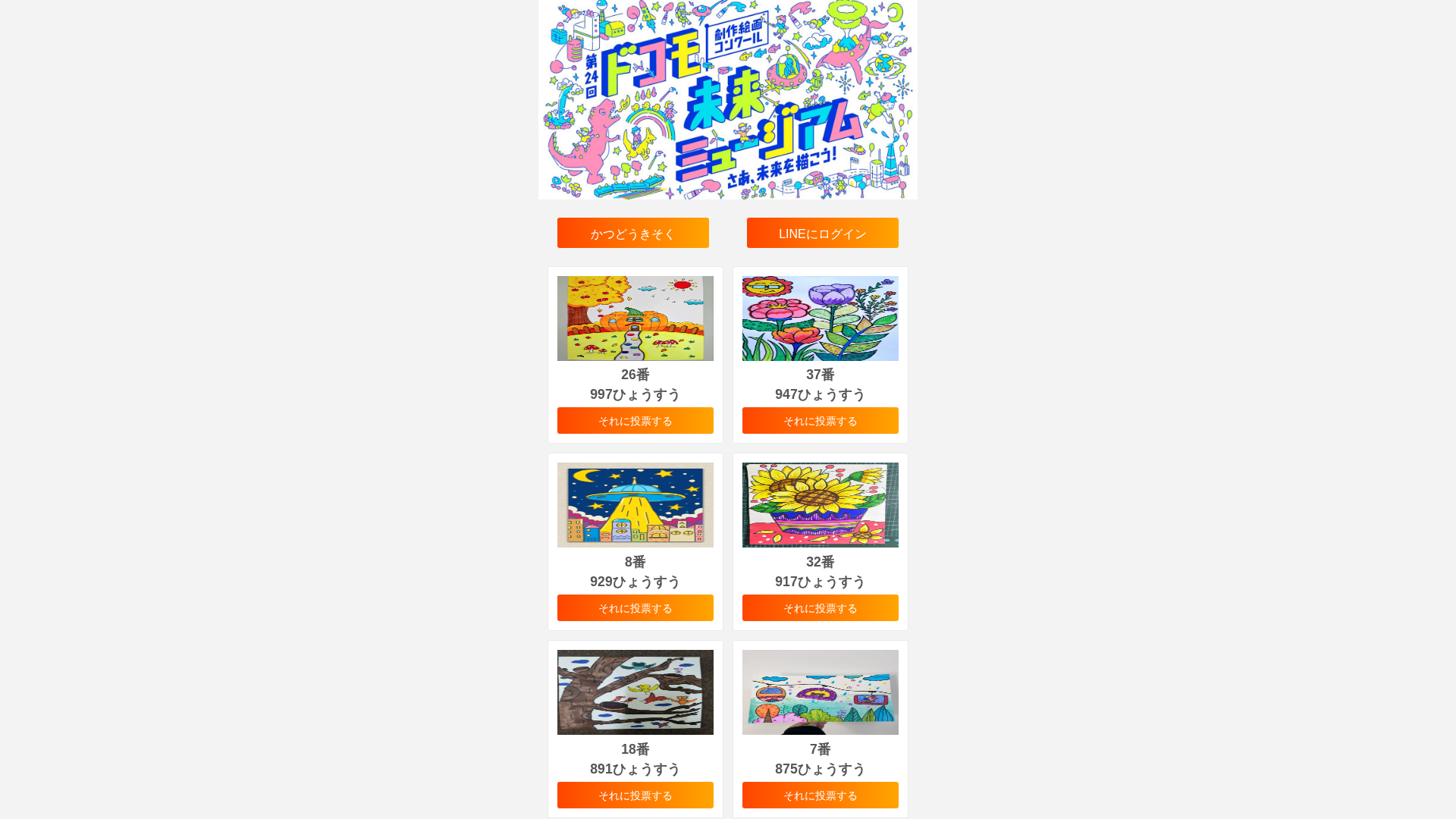
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T10182E0309402DC2320E3A1E60A755A9E2AC2EE0FDA135B991BEC97DC2BDFDD4CD11365 |
|
CONTENT
ssdeep
|
96:GoxZjEEUfEof6gC7tP04WWPTgJTLRs+od6fNYrLcnAP01j6EU6OiUr3JrltdEOMy:Goxz6GDiTD2UyYhAFKfzcEEPj7vl |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3ce33338499cc33 |
|
VISUAL
aHash
|
e7e7e7e7e7e7e7e7 |
|
VISUAL
dHash
|
4d4d4d4d4d4d4d4d |
|
VISUAL
wHash
|
2727070707070707 |
|
VISUAL
colorHash
|
07000018040 |
|
VISUAL
cropResistant
|
4d4d4d4d4d4d4d4d |
Análisis de Código
🔒 Obfuscation Detected
- unescape
📡 API Calls Detected
- POST
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- 2 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: SEO Poisoning Landing Page
Fake NTT Docomo page designed to appear in search results and trick users into visiting. May redirect to credential harvesting pages, malware downloads, or serve as a trust-building step before requesting sensitive information.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 2 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Scan History for jp.voteg6z2.baby
Found 1 other scan for this domain
