
Phishing Analysis
Detailed analysis of captured phishing page
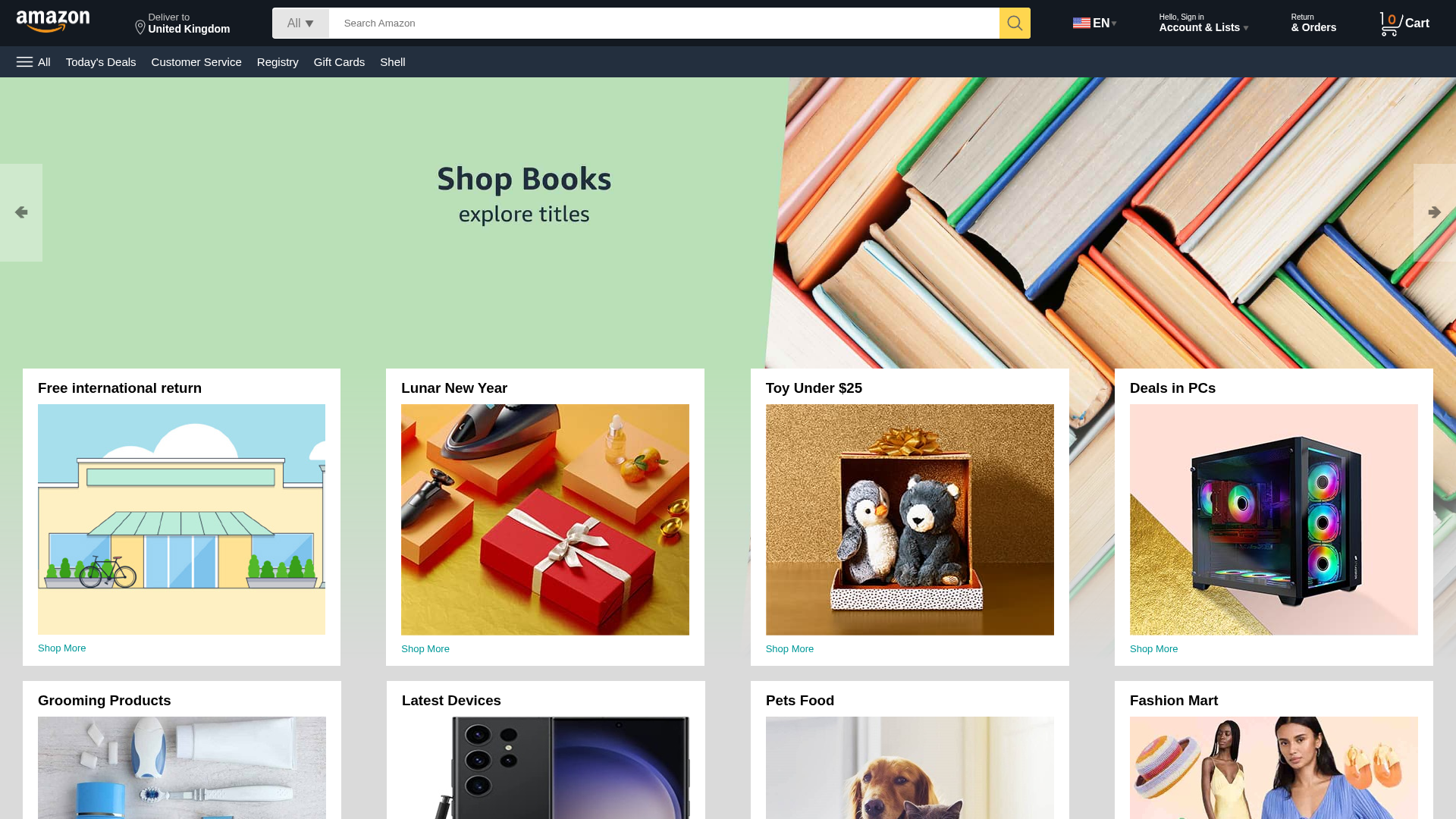
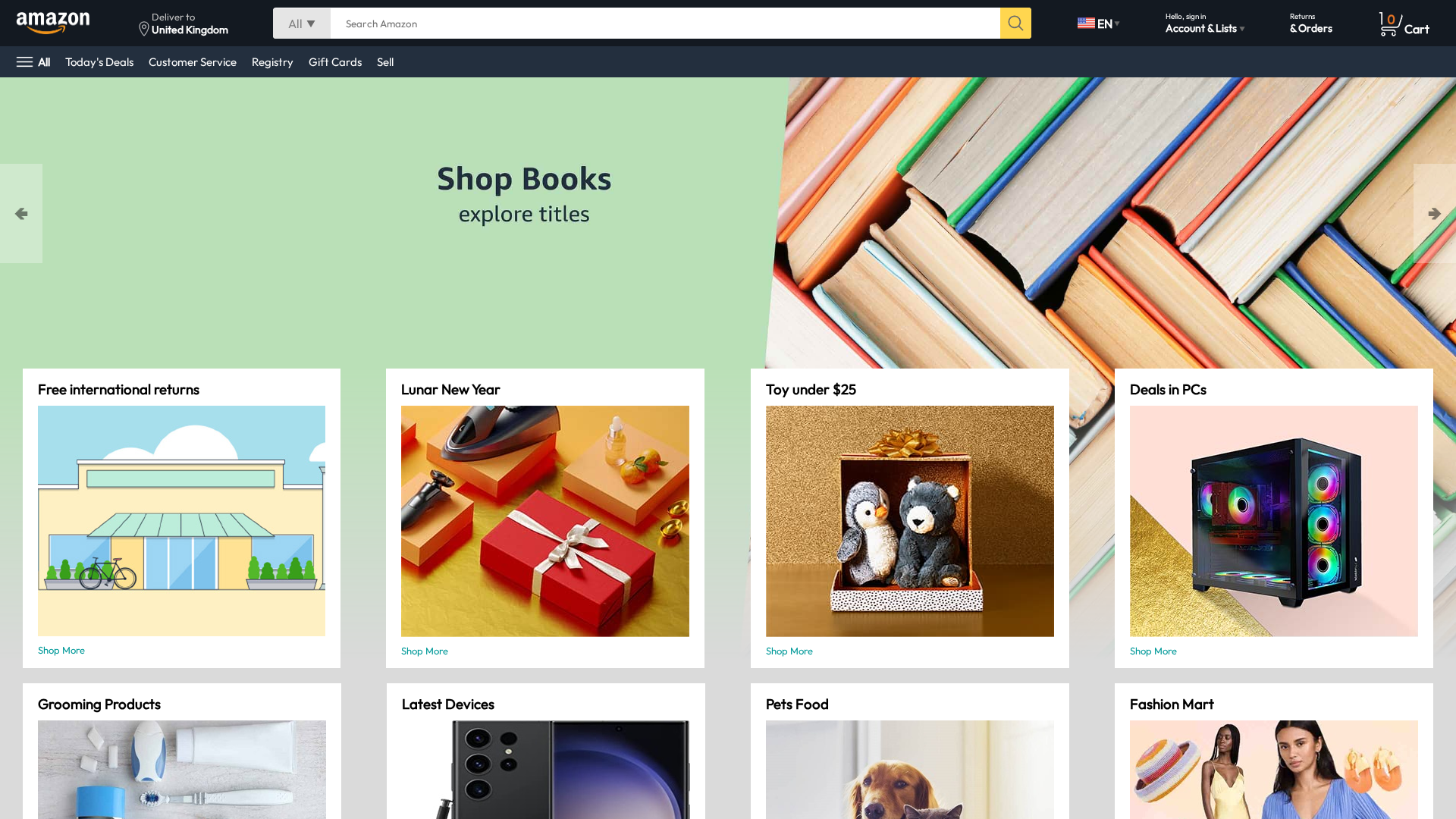
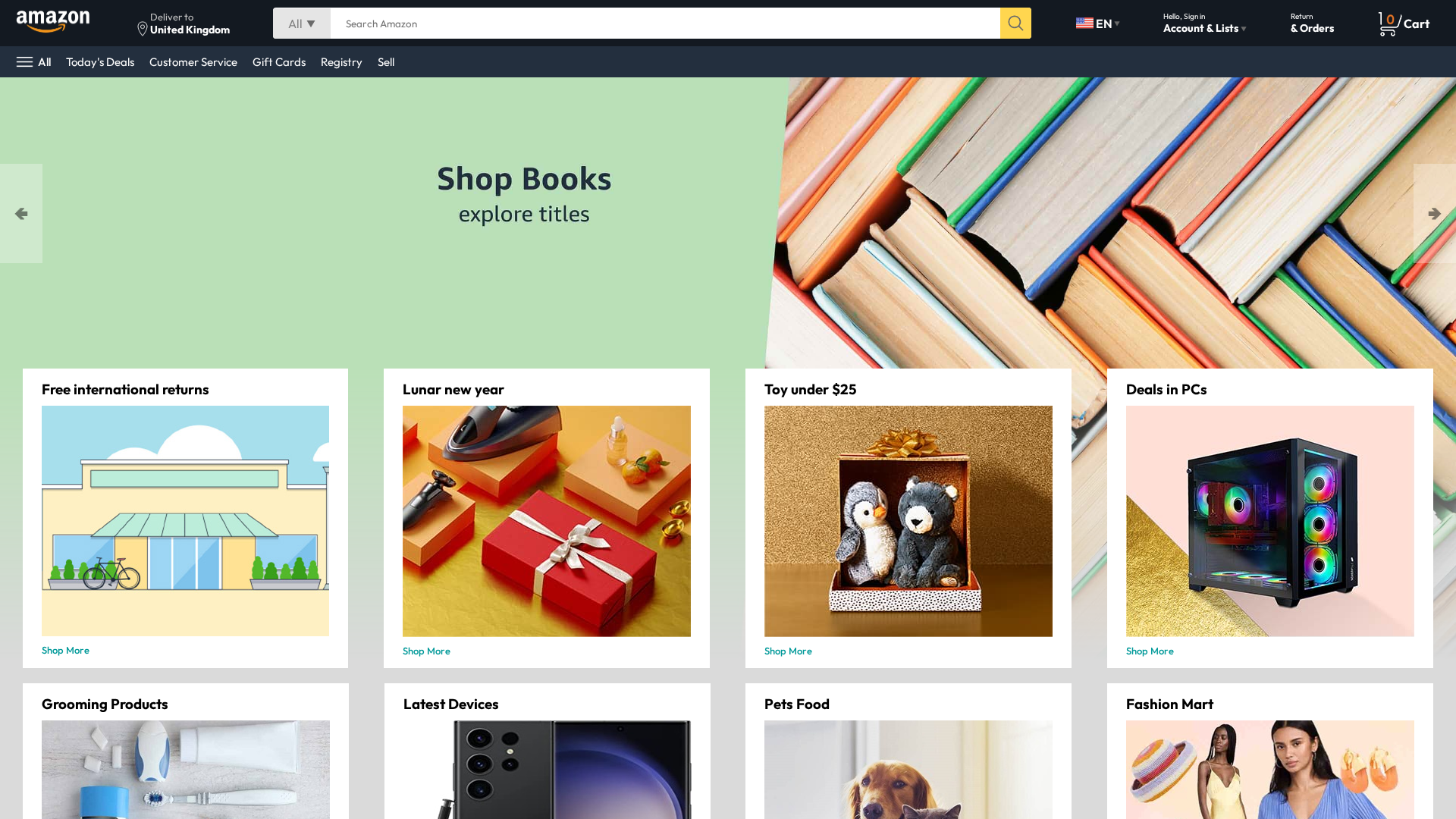
Captura Visual
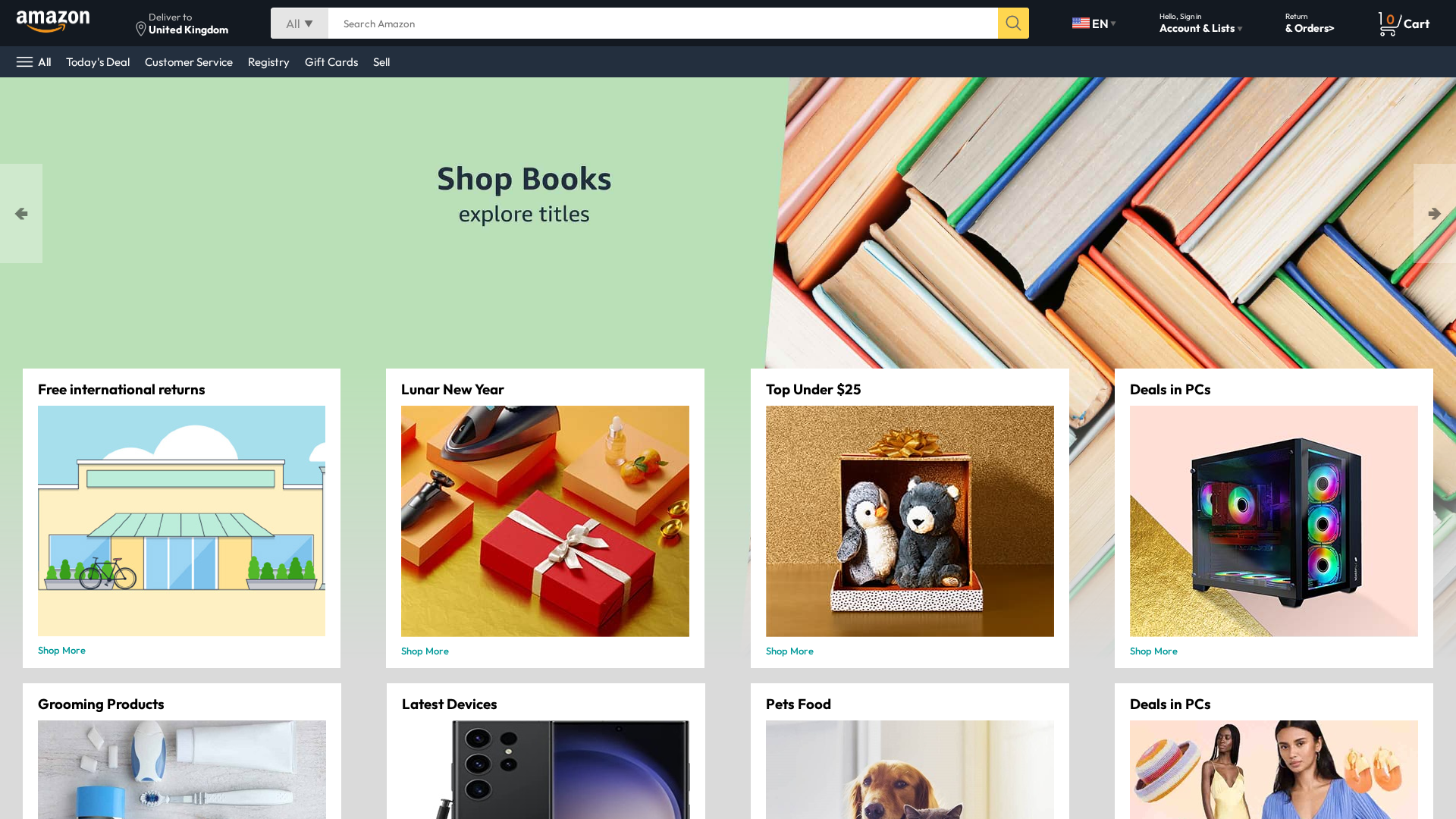
Información de Detección
https://pankajkumar-7255.github.io/Amazon-Project
Detected Brand
Amazon
Country
International
Confidence
95%
HTTP Status
200
Report ID
613efcb3-df0…
Analyzed
2026-01-12 12:56
Final URL (after redirects)
https://pankajkumar-7255.github.io/Amazon-Project/
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F2023AE0C876C673149771F4D3751FD63EC08342C6525E0493F49B99BEAAD89DE22A38 |
|
CONTENT
ssdeep
|
96:n2JO+oUAGc16263QXz5OGUI9y/0puLdoX6z5OGOKm:6P7A0I9y/0puLdoiuKm |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f84f134a13875b4e |
|
VISUAL
aHash
|
00fbf8ffc0c0ffcf |
|
VISUAL
dHash
|
c11702b295959b9d |
|
VISUAL
wHash
|
00d1f0ffc0c0ff4e |
|
VISUAL
colorHash
|
07401010000 |
|
VISUAL
cropResistant
|
808082c2c2c28080,9313629695979b9d,e9c1036397176222,1c3d4cc6799d8523,981f3ba1c5c5b909,070e4c4e0606c667,41694d6c5e5e7e3e |
Análisis de Código
Threat Level
ALTO
⚠️ Phishing Confirmed
🔬 Threat Analysis Report
• Amenaza: Sitio de phishing que suplanta a Amazon
• Objetivo: Usuarios de Amazon en todo el mundo
• Método: Sitio web falso de Amazon alojado en hosting gratuito
• Exfil: No hay formulario visible para la exfiltración de datos
• Indicadores: Hosting gratuito, dominio no coincidente, sin SSL
• Riesgo: ALTO - Potencial de robo de credenciales si hubiera formularios
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
https://cdn.gosafemode.com/screenshots/a66a089b3cde.png
Abr 06, 2026
Amazon
https://nikhil7897.github.io/Amazon-clone-webpage
Mar 12, 2026
Amazon
http://amazon-ui-clone-pi.vercel.app/
Ene 17, 2026
Amazon
http://www.amazon-ui-clone-pi.vercel.app/
Ene 17, 2026
Amazon
http://zaffar9702.github.io/amazon-clone
Ene 10, 2026

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.