
Phishing Analysis
Detailed analysis of captured phishing page
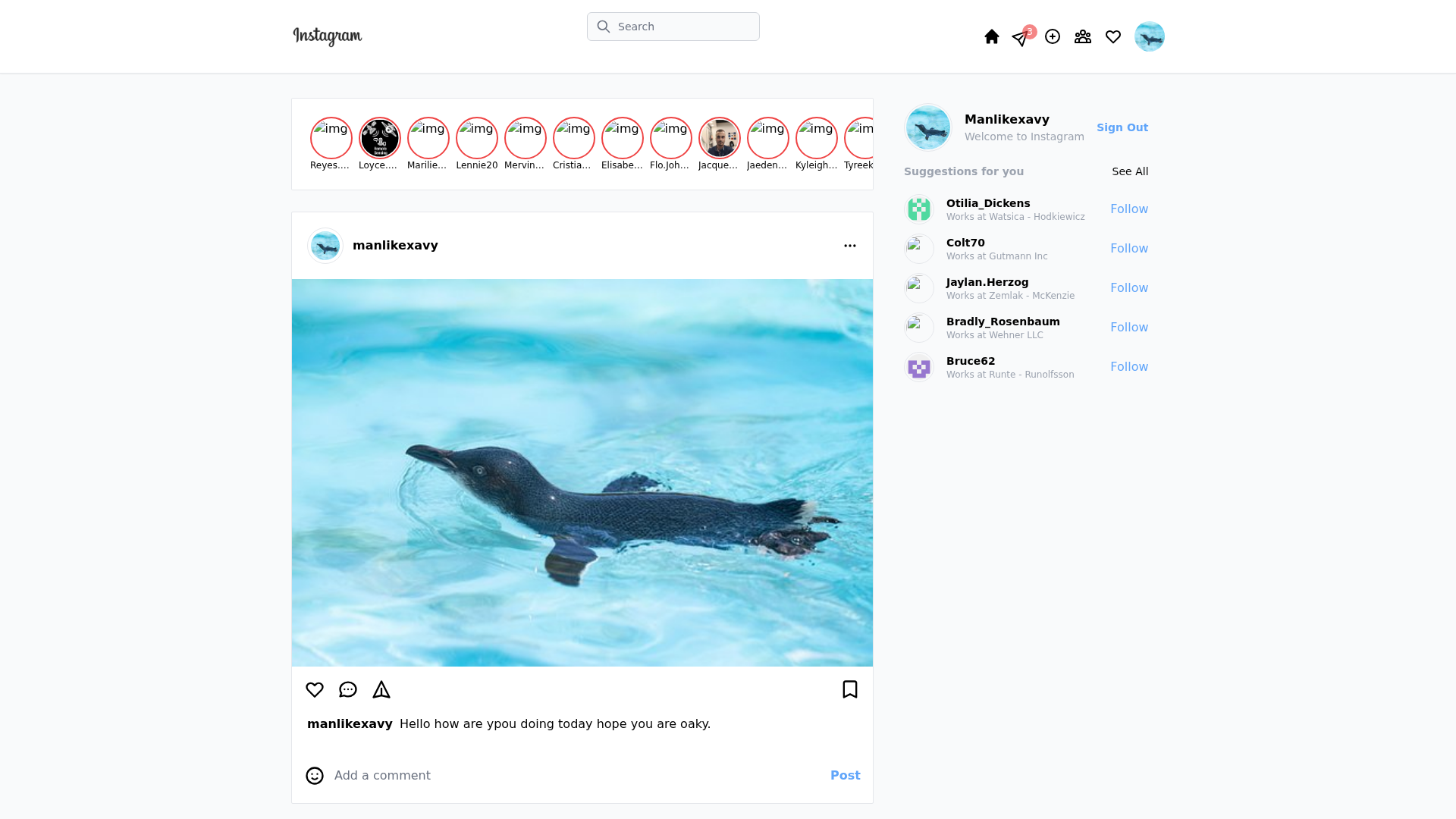
Captura Visual
Información de Detección
https://instagram-2-0-4p6f5s6nd-chibokaxavier.vercel.app/
Detected Brand
Instagram
Country
International
Confidence
100%
HTTP Status
200
Report ID
6878e0a7-201…
Analyzed
2026-02-01 12:27
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T158535CE43640AD3AA87786D6E09A3619337D630BB80C45B0F27CD9D236A0C59F467FD8 |
|
CONTENT
ssdeep
|
768:0LD1pxv7TT8kNBpHzrLkowiym+b+TeTDUV7W+dIFHgrKdrKdrKdrKtJGrTP+Q4c2:sMqcnde//dQ2 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b0cdcd3239cc33c9 |
|
VISUAL
aHash
|
ffffdf87c787d7ff |
|
VISUAL
dHash
|
2b26362f1d0d2430 |
|
VISUAL
wHash
|
fb8181838787879f |
|
VISUAL
colorHash
|
06007000000 |
|
VISUAL
cropResistant
|
2b26362f1d0d2430,636c2e2705489891 |
Análisis de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Instagram
• Método: Suplantación de identidad utilizando alojamiento gratuito
• Exfil: Desconocido
• Indicadores: Alojamiento gratuito, logotipo de la marca, ofuscación
• Riesgo: Alto
🔒 Obfuscation Detected
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://instagram-2-0-4p6f5s6nd-chibokaxavier.vercel.app/api/submit
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Free Hosting + Brand Logo
Presence of a brand logo on free hosting is a major red flag.
Obfuscation Detected
Presence of code obfuscation can make further analysis harder.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Instagram users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- Kit signatures: fisherman
- 6641 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Instagram
Official Website
https://www.instagram.com/
Fake Service
Instagram Feed
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker likely aims to steal Instagram login credentials through a fake login page. The user is tricked into entering their username and password, which the attacker then captures.
🌐 Indicadores de Compromiso de Infraestructura
🦠 Malicious Files
Main File
_next/static/chunks/pages/index-8c9b756d0b1a4a46.js
File Size
Functions: submitForm, sendData
📊 Diagrama de Flujo de Ataque
User fills <input name='username'> and <input name='password'> → submitForm() → fetch('/api/submit') → credentials sent to endpoint
🔬 JavaScript Deep Analysis
Operator Language
English (1%)
Sophistication Level
Basic
Total Code Size
3,0 MB
🔗 API Endpoints Detected
Other
22
🔐 Obfuscation Detected
- : Moderate
- : None
- : Heavy
- : Light
- : None
- : Moderate
- : Light
- : Light
- : Light
- : Light
- : Light
- : Moderate
- : None
- : None
- : None
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name='username'> and <input name='password'> → submitForm() → fetch('/api/submit') → credentials sent to endpoint
🎯 Malicious Files Identified
Main Drainer
_next/static/chunks/pages/index-8c9b756d0b1a4a46.jsFile Size
45KB
Malicious Functions
submitFormsendData
Scan History for instagram-2-0-4p6f5s6nd-chibokaxavier.vercel.app
Found 1 other scan for this domain

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.