Phishing Analysis
Detailed analysis of captured phishing page
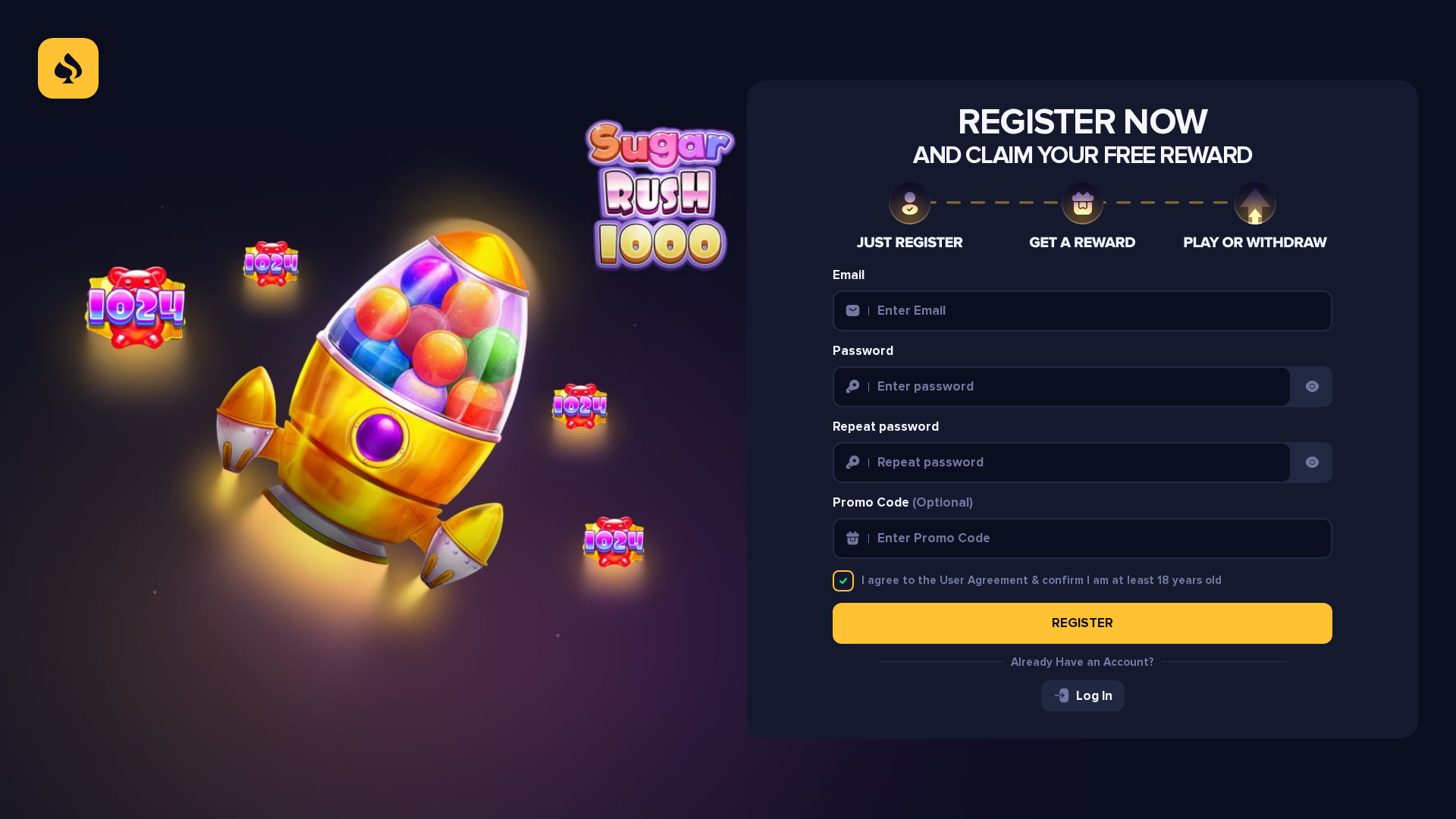
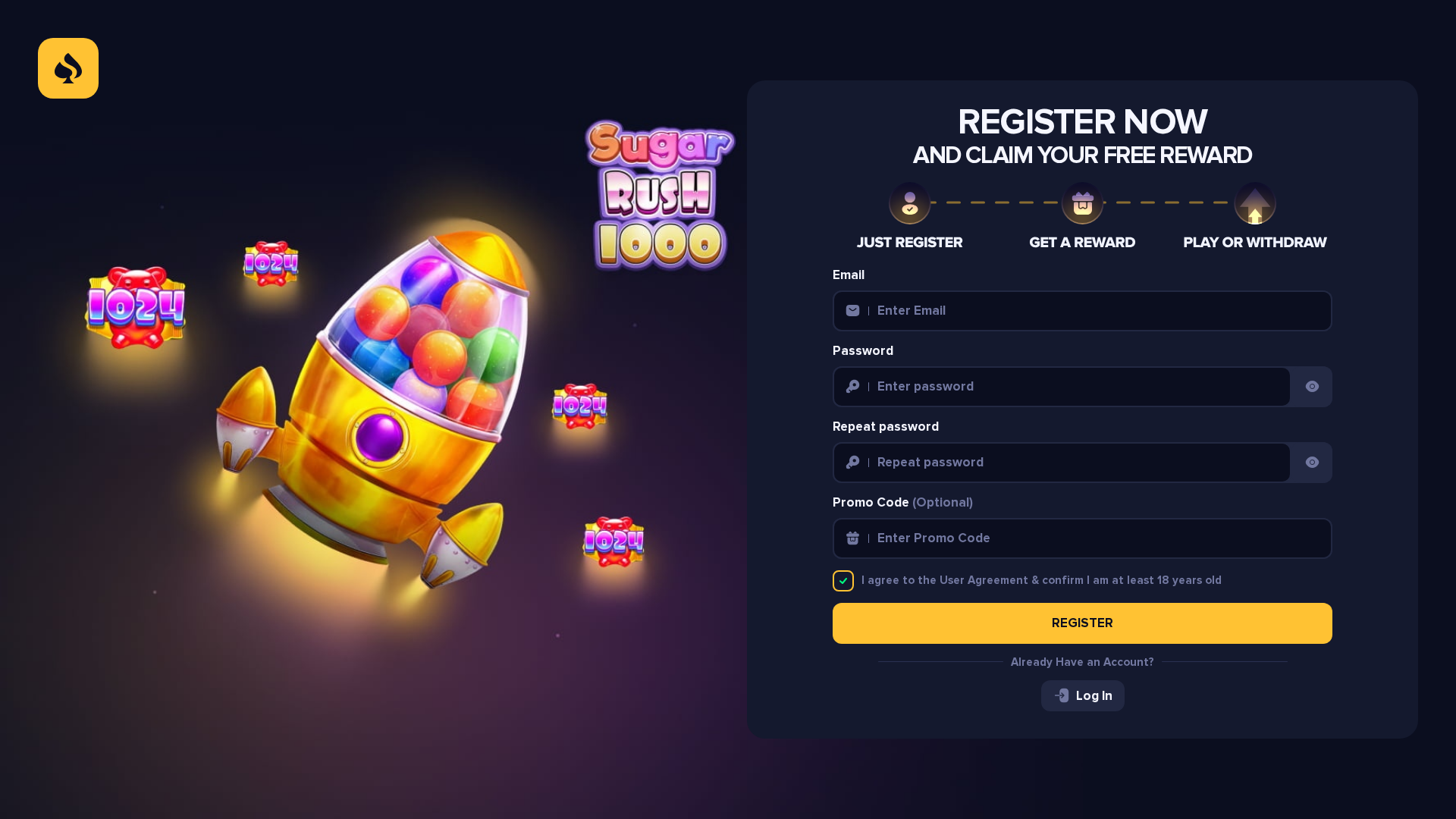
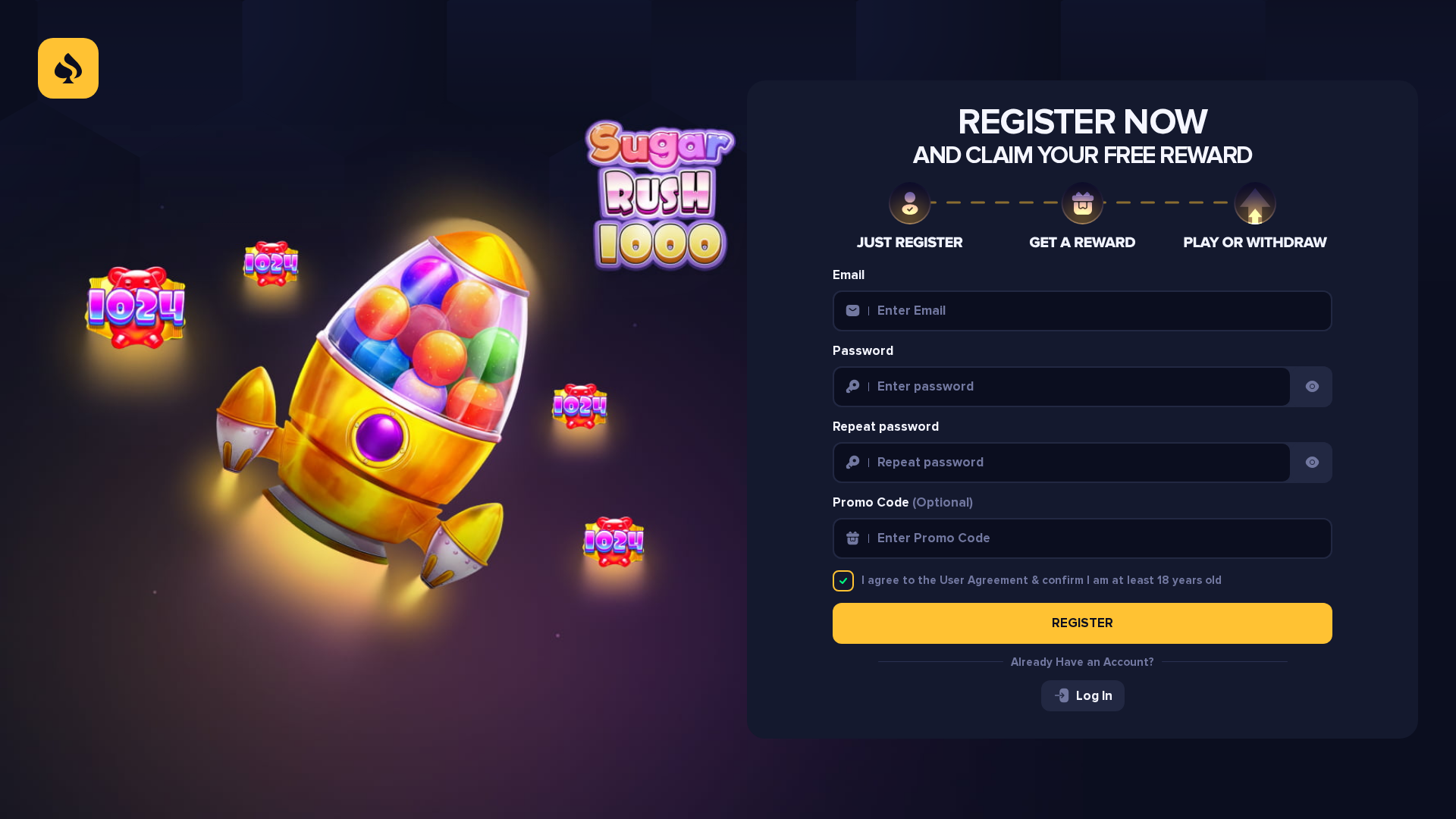
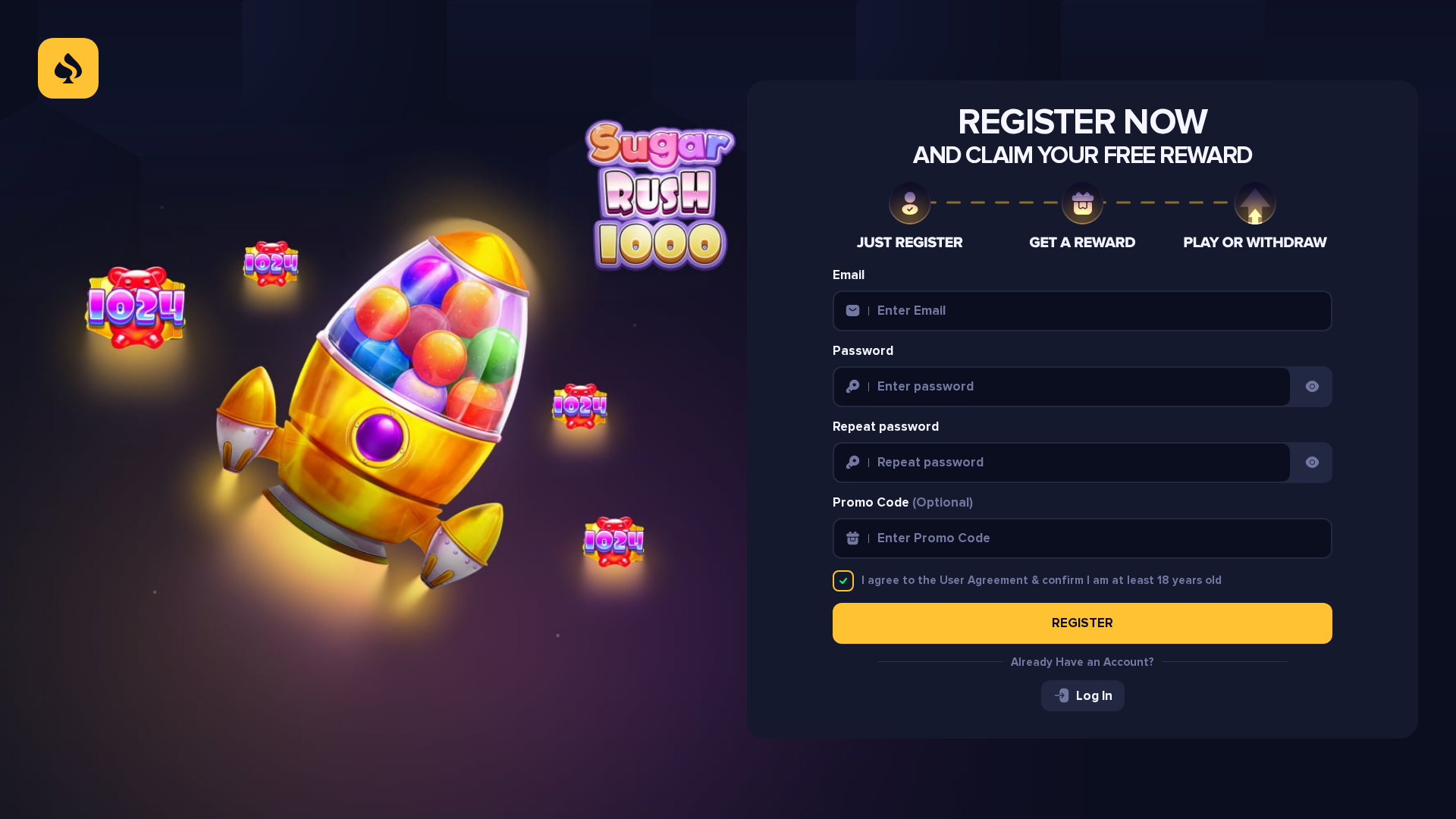
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T166E229B4A2309335B1C24BE8DA642568765FE1DCD7C695B4F388AF11B0D6CE8D9260CF |
|
CONTENT
ssdeep
|
384:4rAneu0TPRhiXkdvNTDhPhLxeAxeDWNW1Tp34PxeeJEmuW3AsQKRWCMd:4rAneuWhhPhleMeDGCSPxeeWmH7W |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c31e3cb163f34b48 |
|
VISUAL
aHash
|
801670e060766e00 |
|
VISUAL
dHash
|
0c34e6cbc3ccccc1 |
|
VISUAL
wHash
|
8016f2e070feff60 |
|
VISUAL
colorHash
|
38200448000 |
|
VISUAL
cropResistant
|
1230929aa6e2eaea,8e9ab365666a4c74,2d1cdcc7e3f8fdf9,80100c4c4c081000,0c34e6cbc3ccccc1 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Stake.us o usuarios generales de juegos de azar
• Método: Suplantación de identidad a través de un formulario de registro.
• Exfil: A través del envío del formulario, apuntando a correo electrónico y contraseña.
• Indicadores: Gráficos engañosos, dominio nuevo, envío de formulario
• Riesgo: Alto
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- http://developers.facebook.com/policy/].
- https://stakeus.space/_next/static/chunks/49080-aa8410705e183b35.js
- https://stakeus.space/_next/static/chunks/58211-d9d578b8de9e3293.js
- https://stakeus.space/_next/static/chunks/63712-08d55a4030f898f7.js
- https://qa.meldcrypto.com/
- https://stakeus.space/_next/static/chunks/app/(auth)/layout-2f72bfb00bd0ee9b.js
- https://stakeus.space/_next/static/chunks/53090-a64743b05c92b22e.js
- https://connect.facebook.net/en_US/fbevents.js
- https://stakeus.space/_next/static/chunks/58733-c5eff74fea05461f.js
- http://localhost:3001
- https://stakeus.space/_next/static/chunks/58172-2e2ad5efca352ade.js
- https://gambler-work.com/api
- https://gambler-work.com/payser
- https://react.dev/errors/
- https://guarda.com/buy/
- https://www.facebook.com/privacy_sandbox/topics/registration/
- https://www.facebook.com/tr/
- https://ramp.network/buy
- https://exchange.mercuryo.io/
- https://changelly.com/buy-crypto
- https://openocean.banxa.com/
- https://www.moonpay.com/buy/btc
- https://nextjs.org/docs/messages/react-hydration-error
- https://stakeus.space/_next/static/chunks/53331-ed5951db58e70abe.js
- https://stakeus.space/_next/static/chunks/main-app-fef4a8898ec7782a.js
- https://stakeus.space/_next/static/chunks/34230-e87c8d35c9fa1ab6.js
- https://changenow.io/buy/bitcoin
- https://global.transak.com/
- https://stakeus.space/_next/static/chunks/4bd1b696-ad7506e6ce5b48e8.js
- https://stakeus.space/_next/static/chunks/31684-5738d0dfaad74be8.js
📡 API Calls Detected
- GET
- POST
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 151 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The site uses a registration form to collect user credentials (email and password). The form likely submits data to a server controlled by the attacker.
Secondary Method: Malware Injection (potential)
Obfuscated Javascript on the page suggests the possibility of additional malicious activity like redirecting to a phishing site or injecting malware.
🌐 Indicadores de Compromiso de Infraestructura
🦠 Malicious Files
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Moderate
- : Moderate
- : Moderate
- : None
- : Light
- : Light
- : Light
- : Light
- : Light
- : Light
- : None
- : Light
- : Light
- : Light
- : Light
- : Light
- : Light
- : Light
- : Light
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
fbevents.jsSimilar Websites
Pages with identical visual appearance (based on perceptual hash)