Phishing Analysis
Detailed analysis of captured phishing page
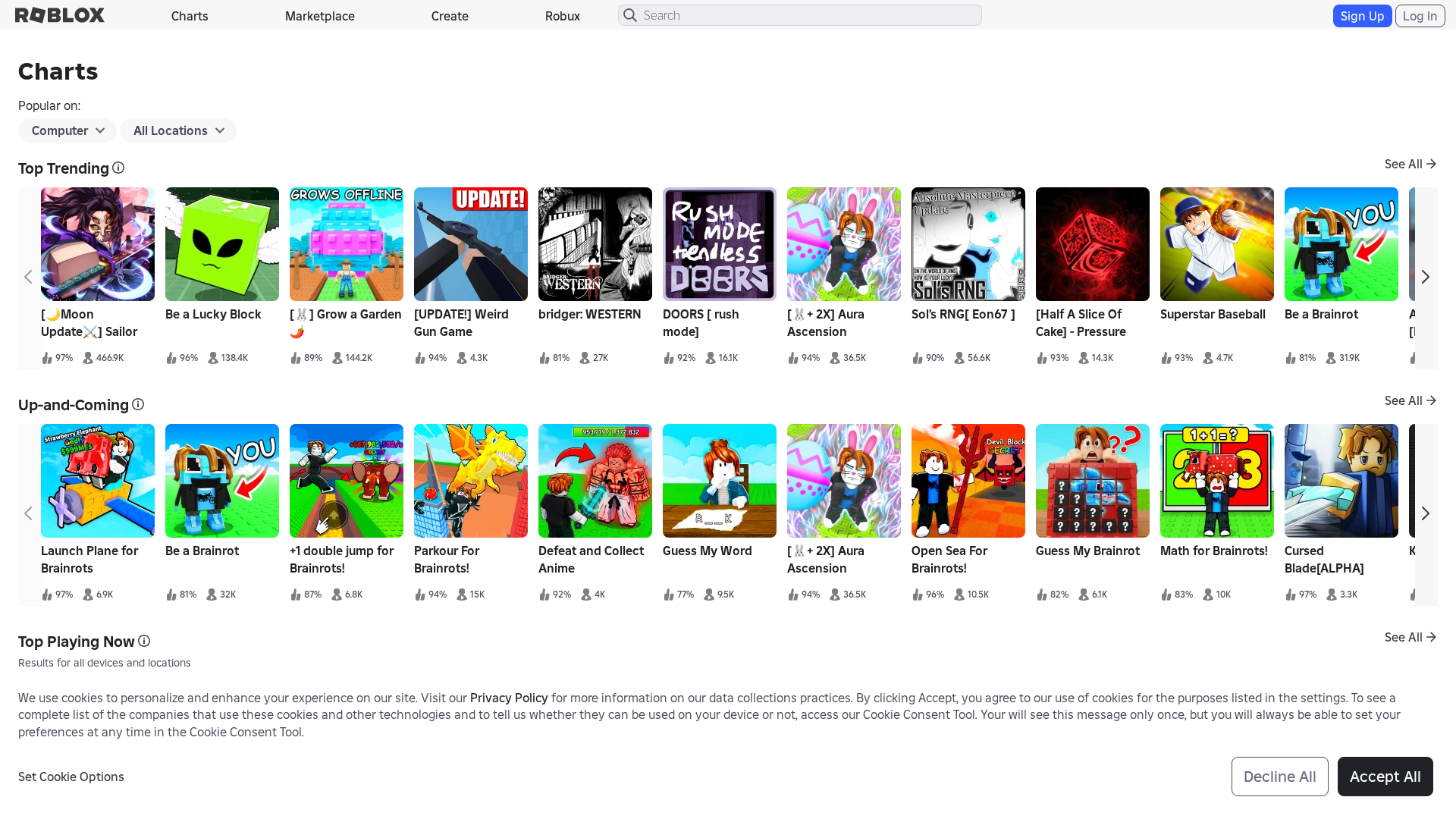
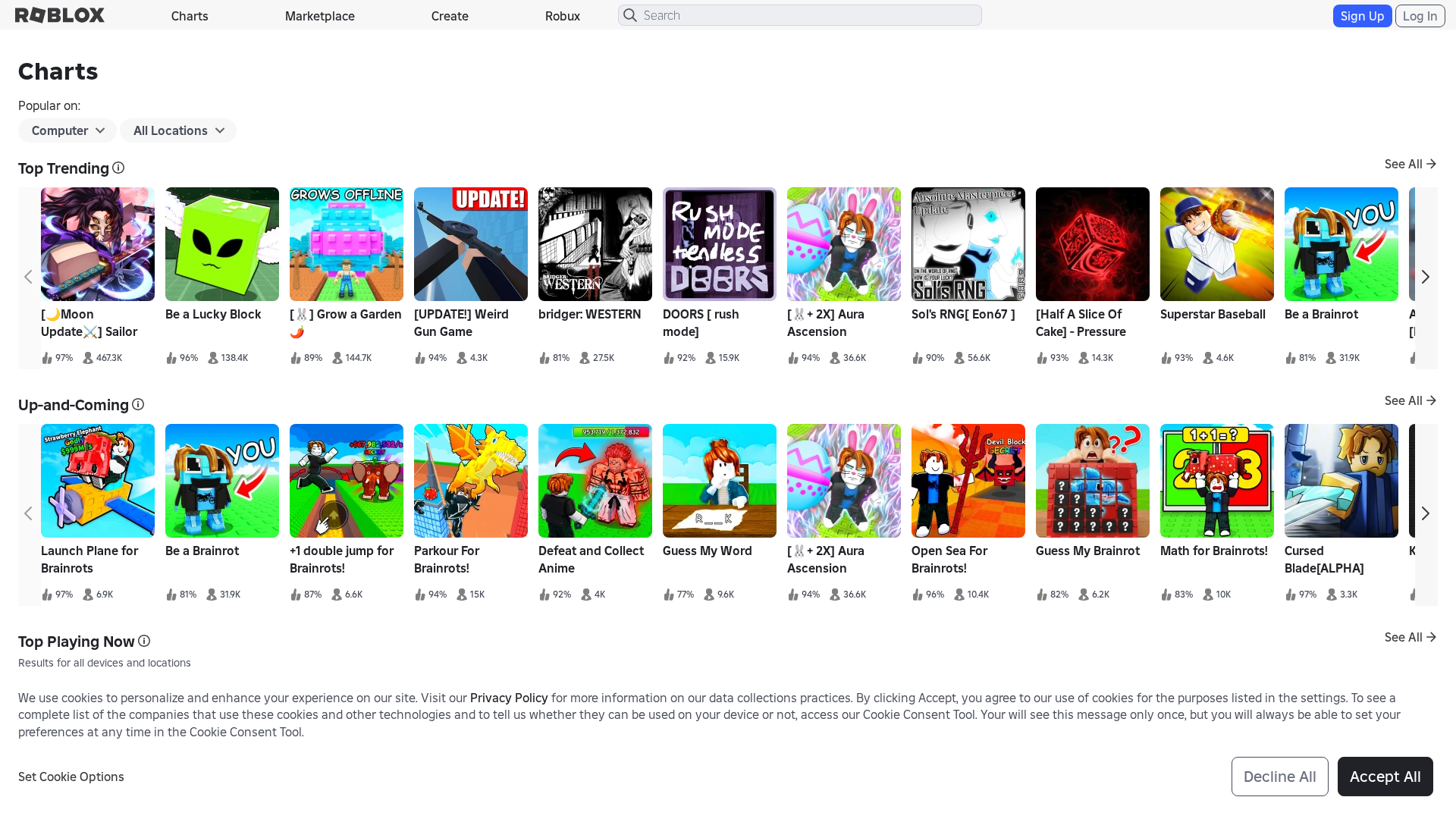
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F6A40C613617003B503792D9B08DF7D56AE2E36FE4C3A689B1EC9381CFCBC6274459A9 |
|
CONTENT
ssdeep
|
6144:TX0g7KhTo8tDa63GzZ5KhT2DQSr4wifN1PF7KhTdJCx:TXjX8tD93GzZbkN1PcJCx |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
db2bd48cd4a0792b |
|
VISUAL
aHash
|
ffff00ff0080fffe |
|
VISUAL
dHash
|
a4cb9bb97313c0d0 |
|
VISUAL
wHash
|
7f2900ff00007ffe |
|
VISUAL
colorHash
|
06001009040 |
|
VISUAL
cropResistant
|
a4cb9bb97313c0d0,17575393ce87c74f,5191797979b59396,5a5a595d5e5e5e5b,1761797d30090e4f,c7668ab239697e59 |
Análisis de Código
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://roblox.net.pk/login?returnUrl=https%3A%2F%2Froblox.net.pk%2Fcharts
- https://roblox.net.pk/catalog?CatalogContext=1&Keyword=
- https://roblox.net.pk/games/8884433153/Collect-All-Pets?appliedFilters=device%253Dcomputer%252Cage%253Dall%252Ccountry%253Dall&discoverPageSessionInfo=7f648471-684e-46a1-8b44-7fc42ac8c005&gameSetTargetId=237&gameSetTypeId=23&isAd=false&nativeAdData=&numberOfLoadedTiles=74&page=gamesPage&placeId=8884433153&playContext=gamesPage&position=32&sortPos=5&universeId=3359505957
- https://roblox.net.pk/games/130313702827830/Defeat-and-Collect-Anime?appliedFilters=device%253Dcomputer%252Cage%253Dall%252Ccountry%253Dall&discoverPageSessionInfo=7f648471-684e-46a1-8b44-7fc42ac8c005&gameSetTargetId=238&gameSetTypeId=23&isAd=false&nativeAdData=&numberOfLoadedTiles=91&page=gamesPage&placeId=130313702827830&playContext=gamesPage&position=57&sortPos=1&universeId=9553855481
- https://roblox.net.pk/games/76285745979410/Anime-Card-Collection?discoverPageSessionInfo=7f648471-684e-46a1-8b44-7fc42ac8c005&gameSetTargetId=671&gameSetTypeId=23&isAd=false&nativeAdData=&numberOfLoadedTiles=91&page=gamesPage&placeId=76285745979410&playContext=gamesPage&position=62&sortPos=3&universeId=9362896961
- https://roblox.net.pk/games/8884433153/Collect-All-Pets?appliedFilters=device%253Dcomputer%252Cage%253Dall%252Ccountry%253Dall&discoverPageSessionInfo=7f648471-684e-46a1-8b44-7fc42ac8c005&gameSetTargetId=222&gameSetTypeId=23&isAd=false&nativeAdData=&numberOfLoadedTiles=64&page=gamesPage&placeId=8884433153&playContext=gamesPage&position=0&sortPos=4&universeId=3359505957
- https://roblox.net.pk/games/132169393925482/Collect-Dinos?appliedFilters=device%253Dcomputer%252Cage%253Dall%252Ccountry%253Dall&discoverPageSessionInfo=7f648471-684e-46a1-8b44-7fc42ac8c005&gameSetTargetId=239&gameSetTypeId=23&isAd=false&nativeAdData=&numberOfLoadedTiles=41&page=gamesPage&placeId=132169393925482&playContext=gamesPage&position=37&sortPos=2&universeId=9784883402
- https://roblox.net.pk/games/7041939546/Catalog-Avatar-Creator?appliedFilters=device%253Dcomputer%252Cage%253Dall%252Ccountry%253Dall&discoverPageSessionInfo=7f648471-684e-46a1-8b44-7fc42ac8c005&gameSetTargetId=222&gameSetTypeId=23&isAd=false&nativeAdData=&numberOfLoadedTiles=64&page=gamesPage&placeId=7041939546&playContext=gamesPage&position=40&sortPos=4&universeId=2711375305
- https://roblox.net.pk/games/130313702827830/Defeat-and-Collect-Anime?appliedFilters=device%253Dcomputer%252Cage%253Dall%252Ccountry%253Dall&discoverPageSessionInfo=7f648471-684e-46a1-8b44-7fc42ac8c005&gameSetTargetId=239&gameSetTypeId=23&isAd=false&nativeAdData=&numberOfLoadedTiles=41&page=gamesPage&placeId=130313702827830&playContext=gamesPage&position=4&sortPos=2&universeId=9553855481
- /info/blog?locale=en_us
- https://roblox.net.pk/games/7041939546/Catalog-Avatar-Creator?discoverPageSessionInfo=7f648471-684e-46a1-8b44-7fc42ac8c005&gameSetTargetId=671&gameSetTypeId=23&isAd=false&nativeAdData=&numberOfLoadedTiles=91&page=gamesPage&placeId=7041939546&playContext=gamesPage&position=14&sortPos=3&universeId=2711375305
- /catalog
📡 API Calls Detected
- https://en.help.roblox.com/hc/articles/7997207259156
- POST
- https://ro.blox.com/Ebh5?pid=experiencestart_mobileweb&is_retargeting=false&af_dp=
- get
- GET
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 137 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 137 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for roblox.net.pk
Found 9 other scans for this domain
-
https://roblox.net.pk/upgrades/robux?ctx=navpopove...
https://roblox.net.pk/games/2146627/aaa?privateSer...
https://roblox.net.pk/games/920587237/Adopt-Me?pri...
https://roblox.net.pk/games/920587237/3H-Adopt-Me?...
http://roblox.net.pk/users/7929089379/profile
http://roblox.net.pk/games/16732694052/Fisch?priva...
http://roblox.net.pk/games/17625359962/RIVALS?priv...
https://roblox.net.pk/games/109983668079237/Steal-...
http://roblox.net.pk/games/6872265039/BedWars-Hype...