Phishing Analysis
Detailed analysis of captured phishing page
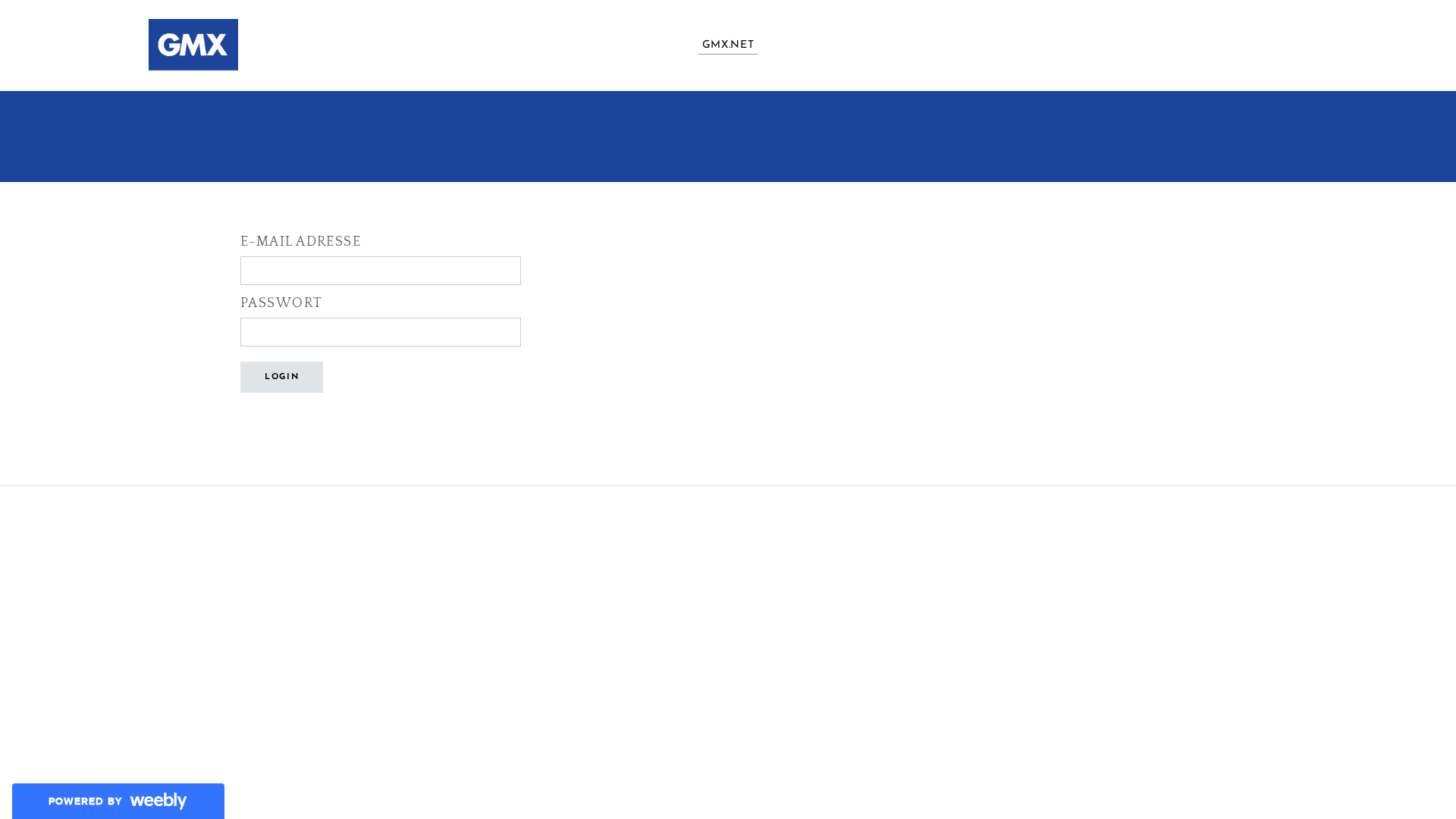
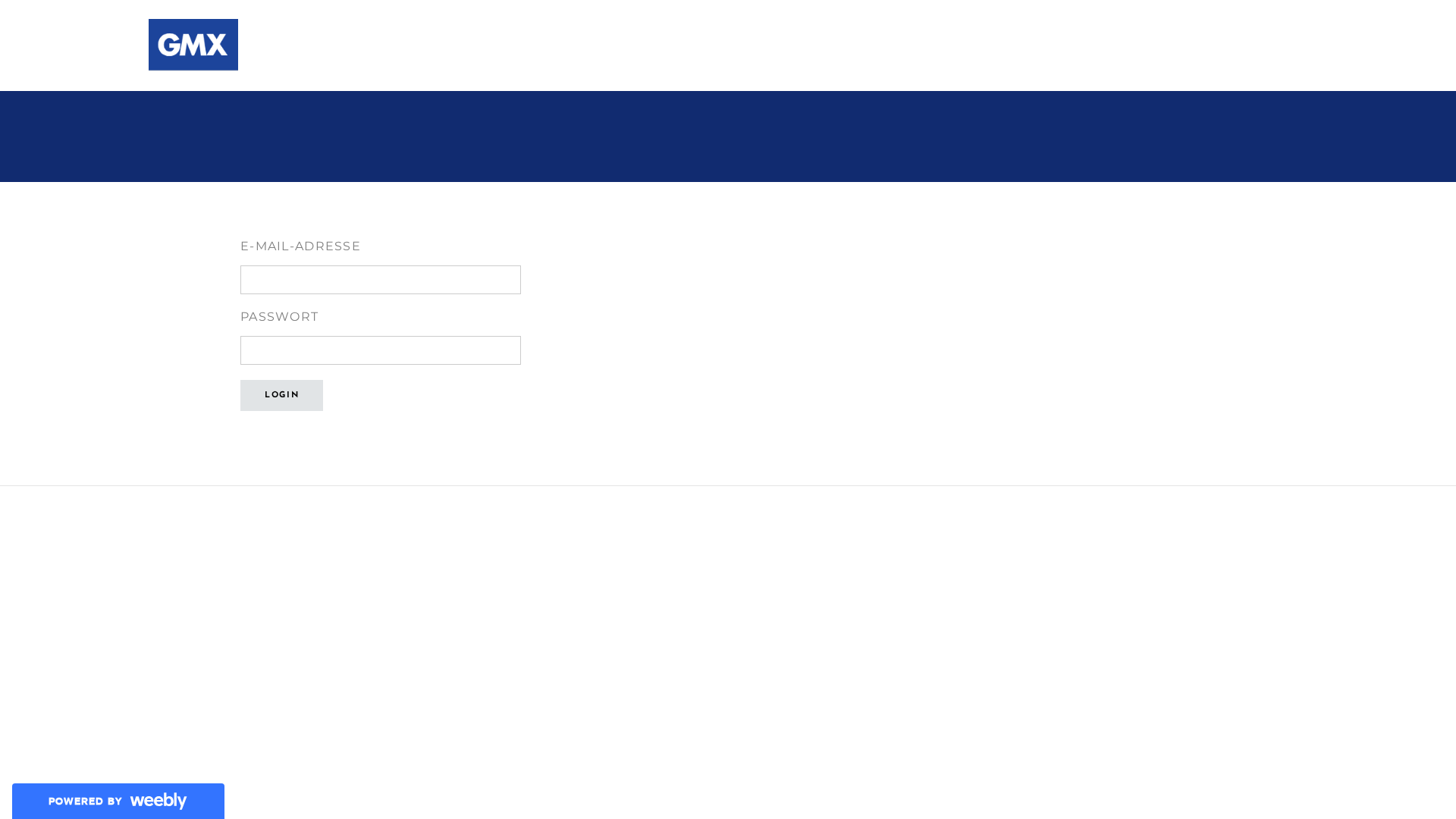
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T148F173E1E054DD330B5281C6B7B67B2FB9F2C355CB020A9452F843AE5BCFD61CA12599 |
|
CONTENT
ssdeep
|
96:TkptzYtqOSTE/bN8v67Mhd7n2NFRaXyHFRKklXD5X/M5ST5+AT431:QptzYtkg58iID7n2n5B5XkoP8F |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
833f017f83fe80f0 |
|
VISUAL
aHash
|
0000ffffffffff7f |
|
VISUAL
dHash
|
50000060608000d0 |
|
VISUAL
wHash
|
00009f9f00fff030 |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
0050505050504080,2020604000c000d0,0000000000000000 |
Análisis de Código
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
📡 API Calls Detected
- POST
- GET
📤 Form Action Targets
- https://e-mail-adresse9190.weebly.com/ajax/apps/formSubmitAjax.php
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 60 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 60 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for e-mail-adresse9190.weebly.com
Found 2 other scans for this domain