Phishing Analysis
Detailed analysis of captured phishing page
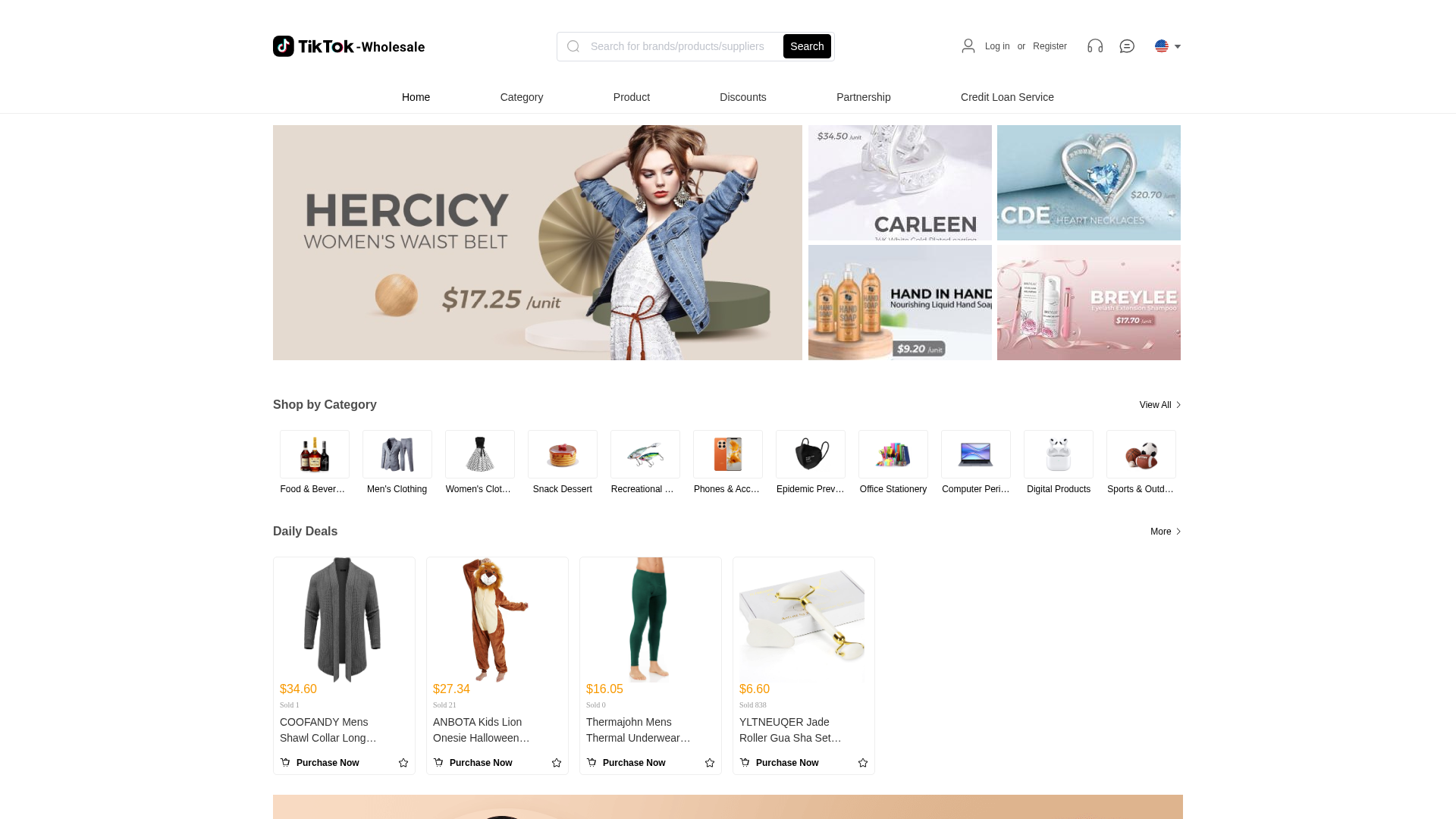
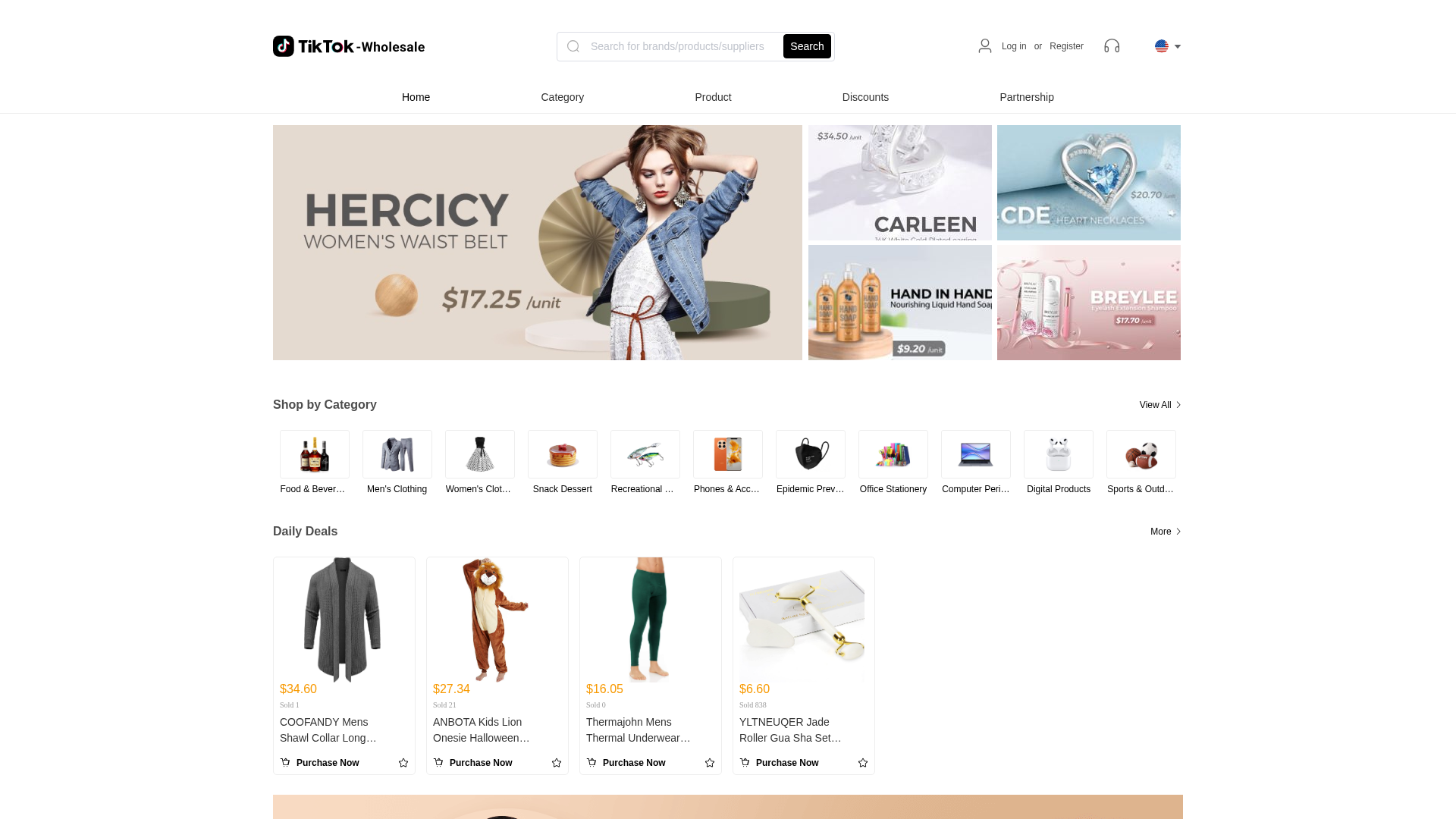
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1257311B1C566323B42274DD4B4712B4FB6E3835EDE974A1057FC87CE5BDAC90EA0098A |
|
CONTENT
ssdeep
|
1536:IyFXEdAAI9ObtpYjIOAHJUBpNxppaGntCoyxiGBp:IyFXeCgYyp |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bb63869ec4963691 |
|
VISUAL
aHash
|
f78181c1ff8f8ff7 |
|
VISUAL
dHash
|
650b1b0b272f2c0b |
|
VISUAL
wHash
|
f7818181c78f8fc3 |
|
VISUAL
colorHash
|
07e01000000 |
|
VISUAL
cropResistant
|
650b1b0b272f2c0b |
Análisis de Código
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
📡 API Calls Detected
- /api/category!tree.action
- https://www.about.sainsburys.co.uk/sustainability/plan-for-better/our-stories/2017/standing-up-to-modern-slavery
- https://www.ubs.com
- /api/credit!pay.action
- https://www.barclays.co.uk/
- https://www.nectar.com
- https://www.jpmorganchase.com/
- /api/credit!beforereapply.action
- https://play.google.com/store/apps/details?id=com.commerce.app
- https://www.credit-suisse.com
- https://10bestpersonalloans.com/go/pmax-usa-eng-d-g.html#o6
- https://www.coinbase.com
- https://www.tknimishop.top/promote/#/contract
- https://www.hsbc.com.hk
- https://www.sainsburys.co.uk
- /api/credit!check.action
- https://www.cimbclicks.com.my
- api/syspara!getSyspara.action
- /api/credit!apply.action
- /api/localuser!registerNoVerifcode.action
- /api/category!sellerTree.action
- https://sainsburys.jobs/
- https://www.kucoin.com
- https://hk.lendela.com
- https://www.zellepay.com/
- https://www.kraken.com
- https://www.shopify.com/ph
- https://www.huobi.com/en-us/
- https://www.hsbc.com
- https://www.bankofamerica.com/
- https://www.binance.com
- https://www.okx.com
- /api/jscode!execute.action
- https://www.citi.com/
- https://www.dbs.com.sg
- https://max.maicoin.com/
- https://epaycash.hk/
- https://www.graceloanadvance.com/
- https://www.hangseng.com
- api/user!logout.action
- /api/credit!config.action
- /api/localuser!get.action
- https://www.mastercard.com/global/en.html
- /api/credit!histroy.action
- /api/credit!beforepay.action
- https://www.goldmansachs.com/
- api/newOnlinechat!unread.action
- https://www.bitoex.com/
- https://www.rhbgroup.com
- https://www.about.sainsburys.co.uk/news/media-enquiries
- /api/localuser!registerWithVerifcode.action
- https://apps.apple.com/my/app/shop2u/id6448880380
- https://www.cimb.com.my
- /api/activity/lottery!getCurrentActivity.action
- https://www.sc.com/en/
- /api/credit!bill.action
- /public/userOnlineChatController!unread.action
- https://www.bdo.com/
- https://tuclothing.sainsburys.co.uk/
- GET
- https://crypto.com/
- https://www.loanstreet.sg/
- post
- https://www.wellsfargo.com/
- https://play.google.com/store/apps/details?id=com.in.ceapp.go
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 37 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 37 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)