Phishing Analysis
Detailed analysis of captured phishing page
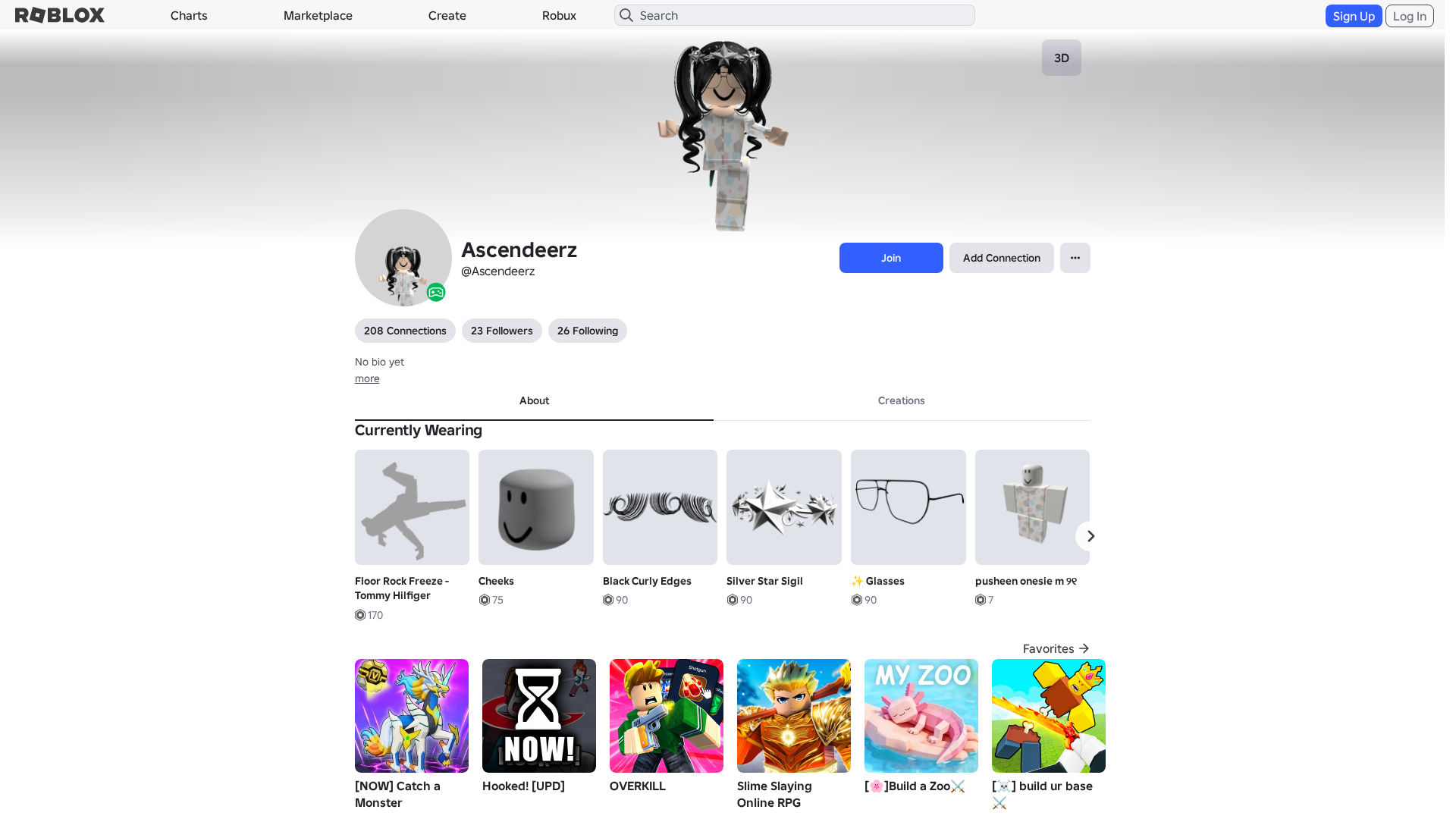
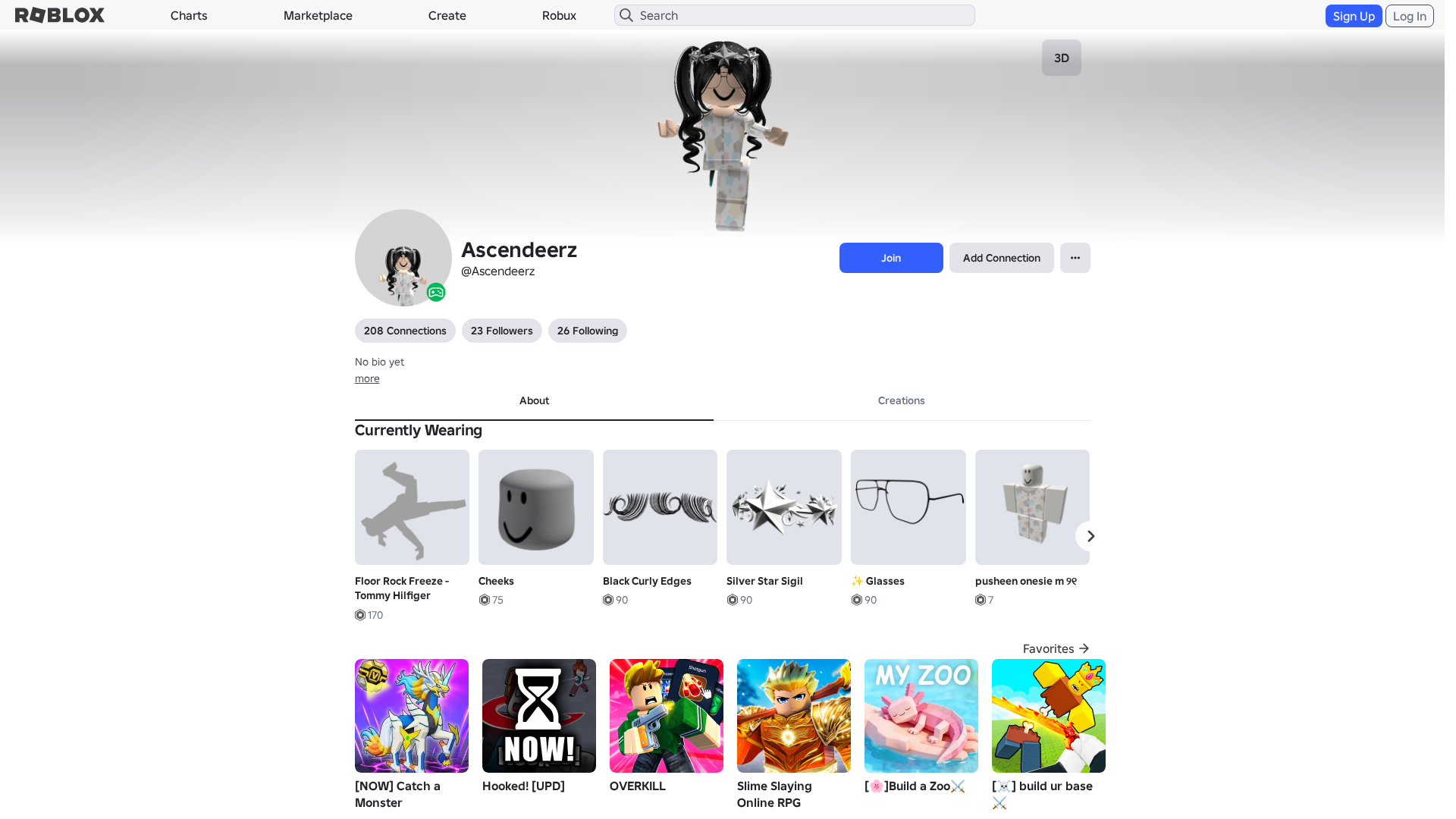
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T19183317292142837617B79DAF164671AA2D3D70FCA8347E1A2F8D39A0FD6CA1EC5340D |
|
CONTENT
ssdeep
|
1536:20xXWnmrFcG+9sgzDgmRgsOg0wgrag98gkGgxodg1DgqXgorg/ng4XgSvgrDguv6:jxXWmcXT5URZyK23ZK1zCfx61nc5YKq1 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b0467353d39ccc39 |
|
VISUAL
aHash
|
0000dfffcfdfc3c3 |
|
VISUAL
dHash
|
c8c8b6301e161f1e |
|
VISUAL
wHash
|
0000d7ffcbc7c3c3 |
|
VISUAL
colorHash
|
07001008040 |
|
VISUAL
cropResistant
|
c8c8b6301e161f1e,6969337373c9c869 |
Análisis de Código
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/86499716/Woman-Left-Arm
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- /login?returnUrl=
- https://api.injuries.lu/catalog/124480496244367/NewSide-Bangs-Fashionista-Bangs-combo-in-black
- https://api.injuries.lu/catalog/3360686498/Stadium
- https://api.injuries.lu/catalog/15958342187/Glasses
- https://api.injuries.lu/catalog/18458363449/Long-Cute-Pigtails-in-Black
- https://api.injuries.lu/catalog/15033208086/pusheen-onesie
- https://api.injuries.lu/catalog/2510230574/Rthro-Climb
- https://api.injuries.lu/catalog/2510240941/Rthro-Swim
- https://api.injuries.lu/catalog/14907734843/Silver-Star-Sigil
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/3576968026/Shrug
- https://api.injuries.lu/catalog/2510236649/Rthro-Jump
- https://api.injuries.lu/catalog/2510235063/Rthro-Idle
- https://api.injuries.lu/catalog/86499698/Woman-Right-Arm
- https://api.injuries.lu/catalog/86499666/Woman-Torso
- https://api.injuries.lu/catalog/2510242378/Rthro-Walk
- https://api.injuries.lu/catalog/13324766443/Black-Curly-Edges
- https://api.injuries.lu/catalog/10214411646/Floor-Rock-Freeze-Tommy-Hilfiger
- https://api.injuries.lu/catalog/3576823880/Point2
- https://api.injuries.lu/catalog/2510238627/Rthro-Run
- https://www.roblox.com.gl/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F108606364214%2Fprofile
- https://api.injuries.lu/catalog/15033203953/pusheen-onesie-m
- https://api.injuries.lu/catalog/2510233257/Rthro-Fall
- https://api.injuries.lu/catalog/746767604/Cheeks
- /info/blog?locale=en_us
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F108606364214%2Fprofile
- https://api.injuries.lu/catalog/139607718/Korblox-Deathspeaker-Right-Leg
📡 API Calls Detected
- POST
- https://kyxn.dev/api/shorten/TKvzwH
- get
- https://apis.
- /api/shorten
- https://kyxn.dev${e.endpoint}
- https://kyxn.dev/api/shorten
- GET
- https://help.roblox.com/hc/articles/30428367965460
- /api/pageview
- https://ro.blox.com/Ebh5?
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 209 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 209 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for kyxn.dev
Found 3 other scans for this domain