
Phishing Analysis
Detailed analysis of captured phishing page
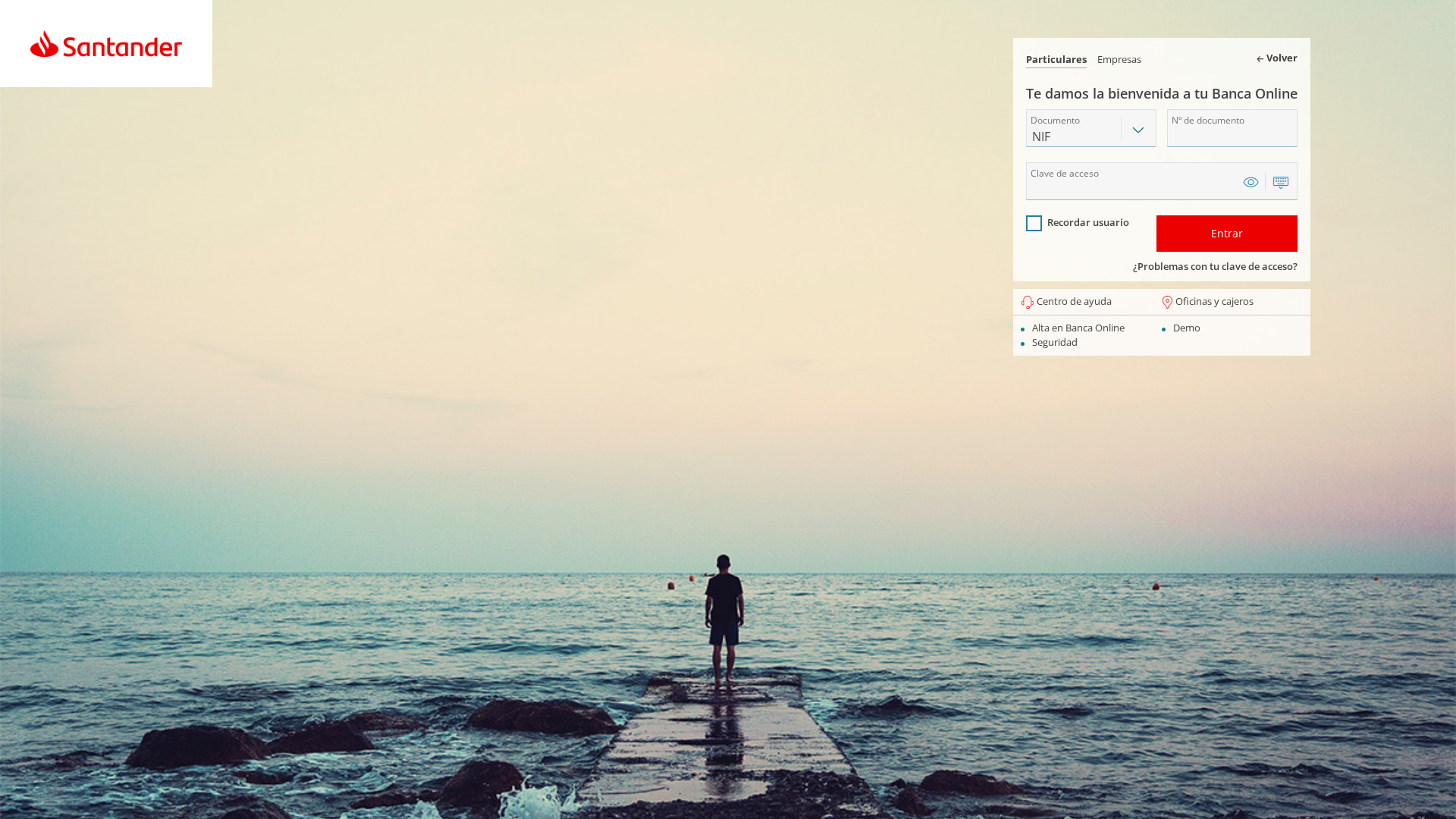
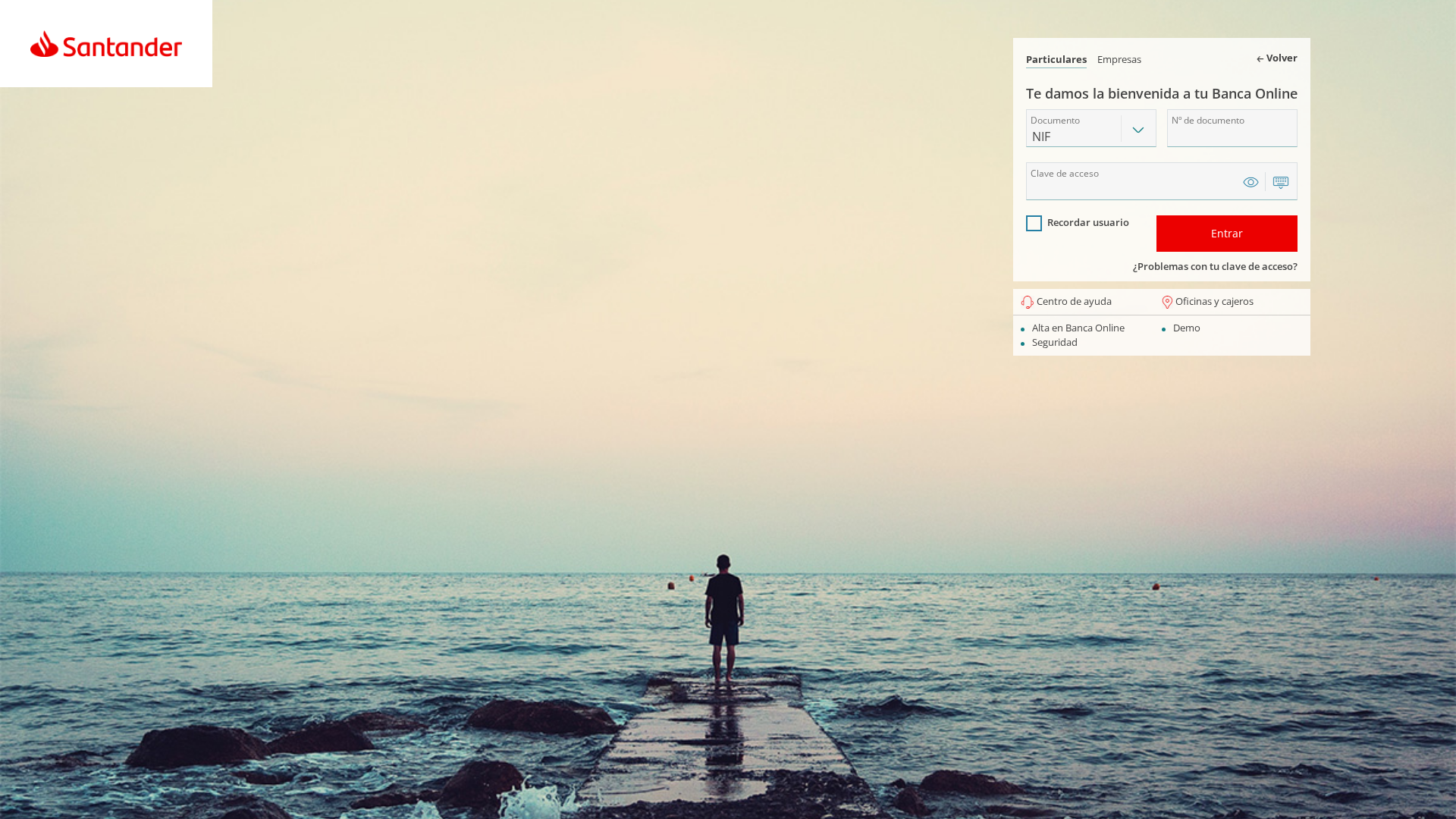
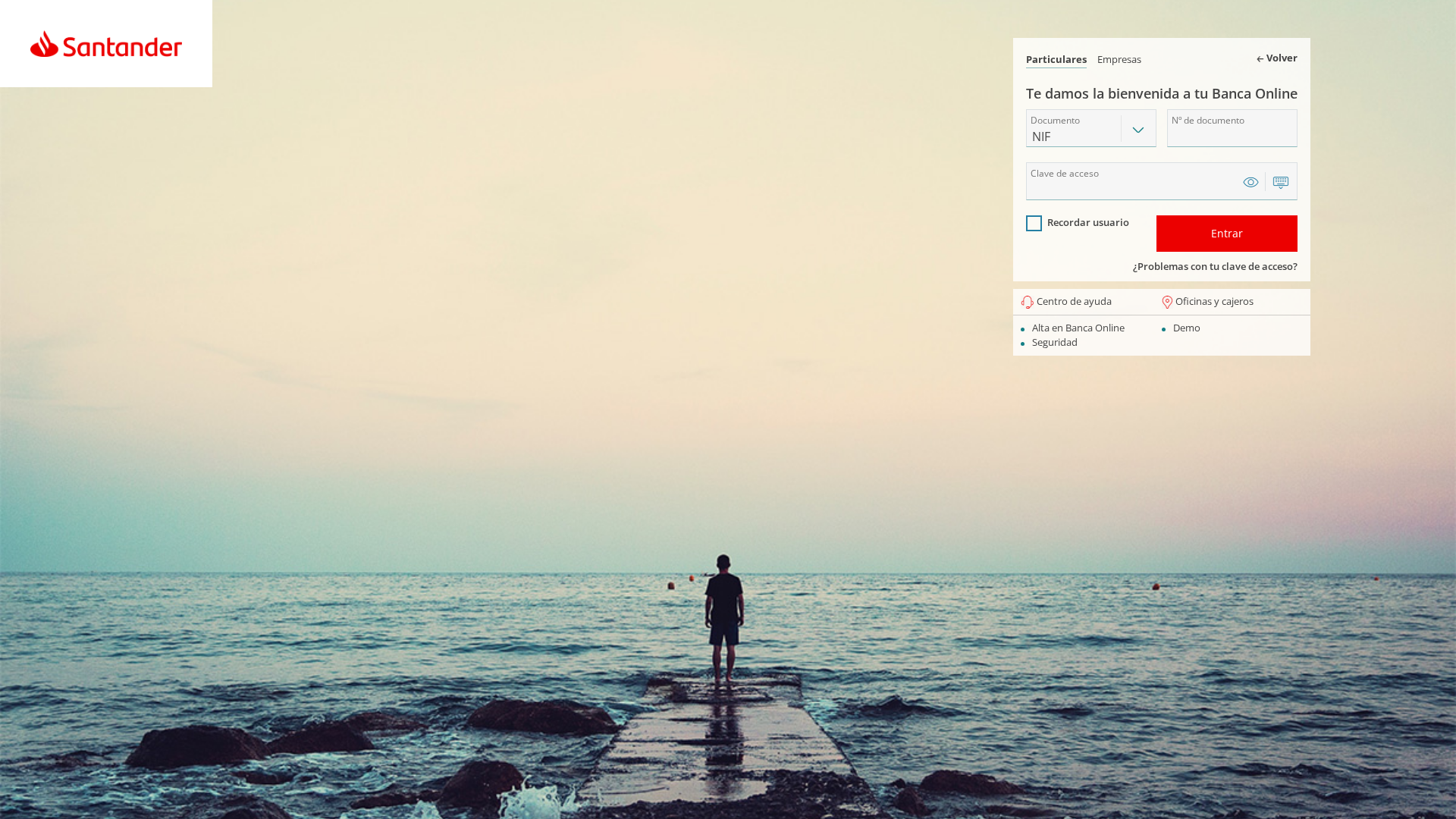
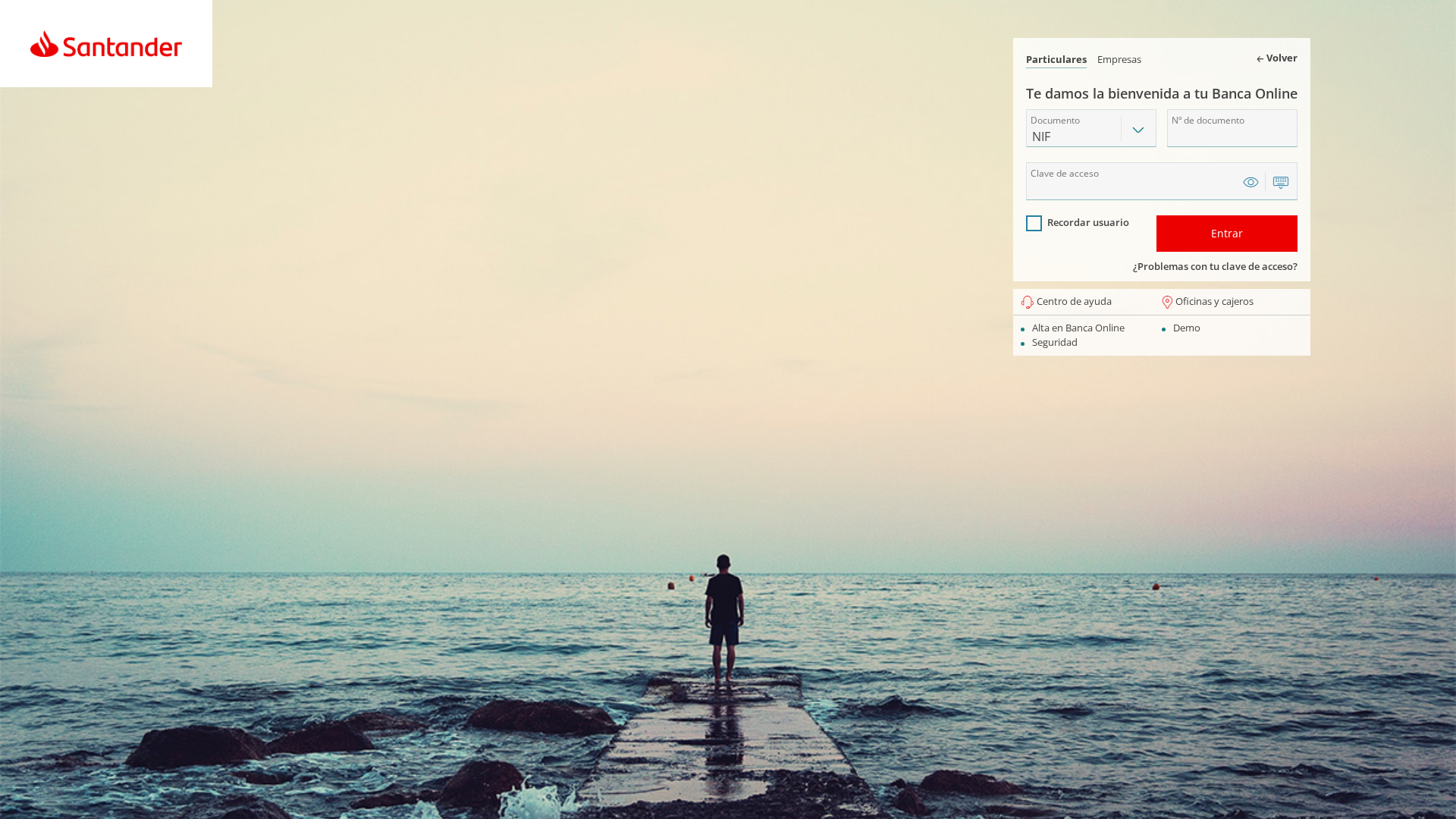
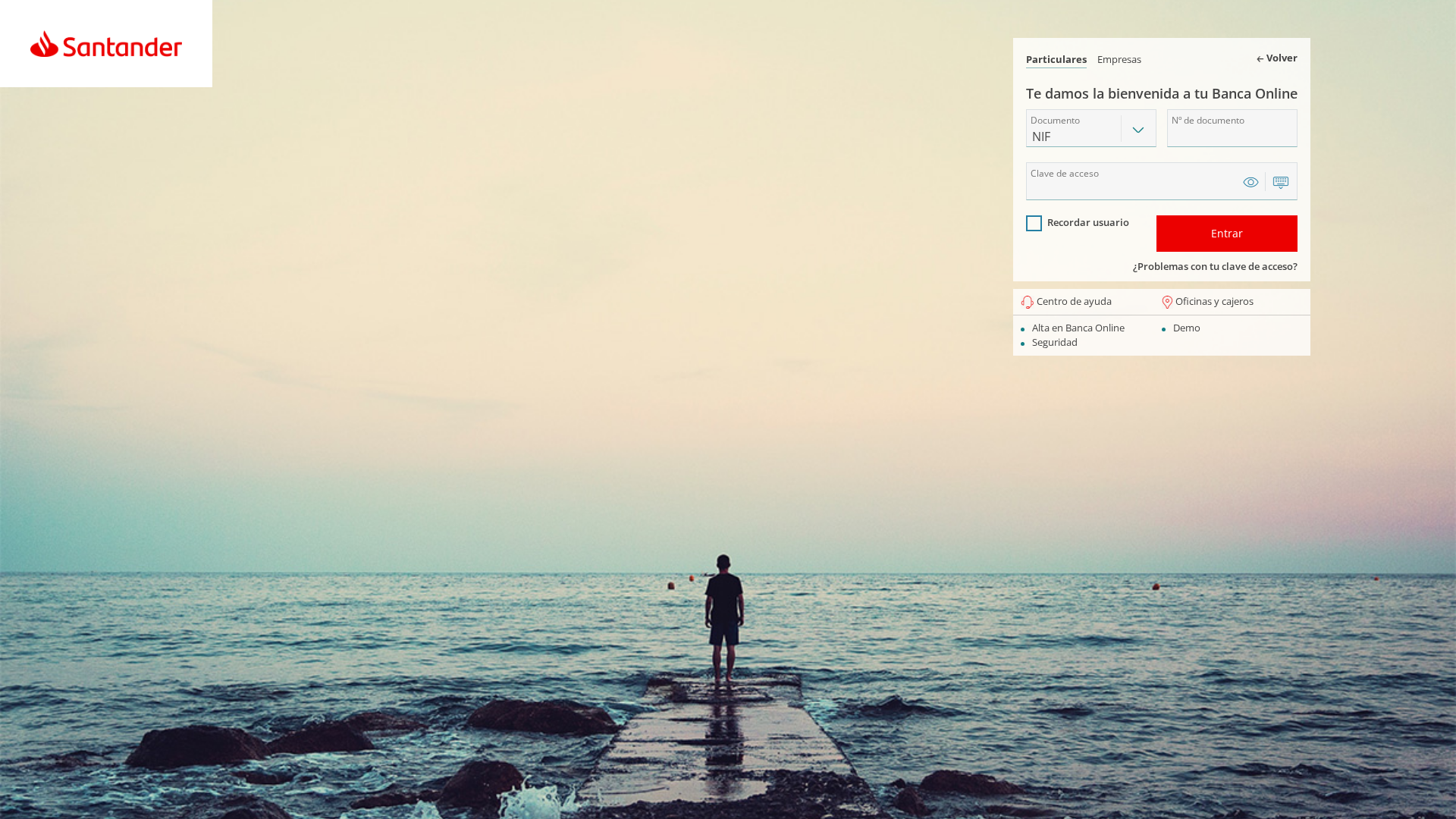
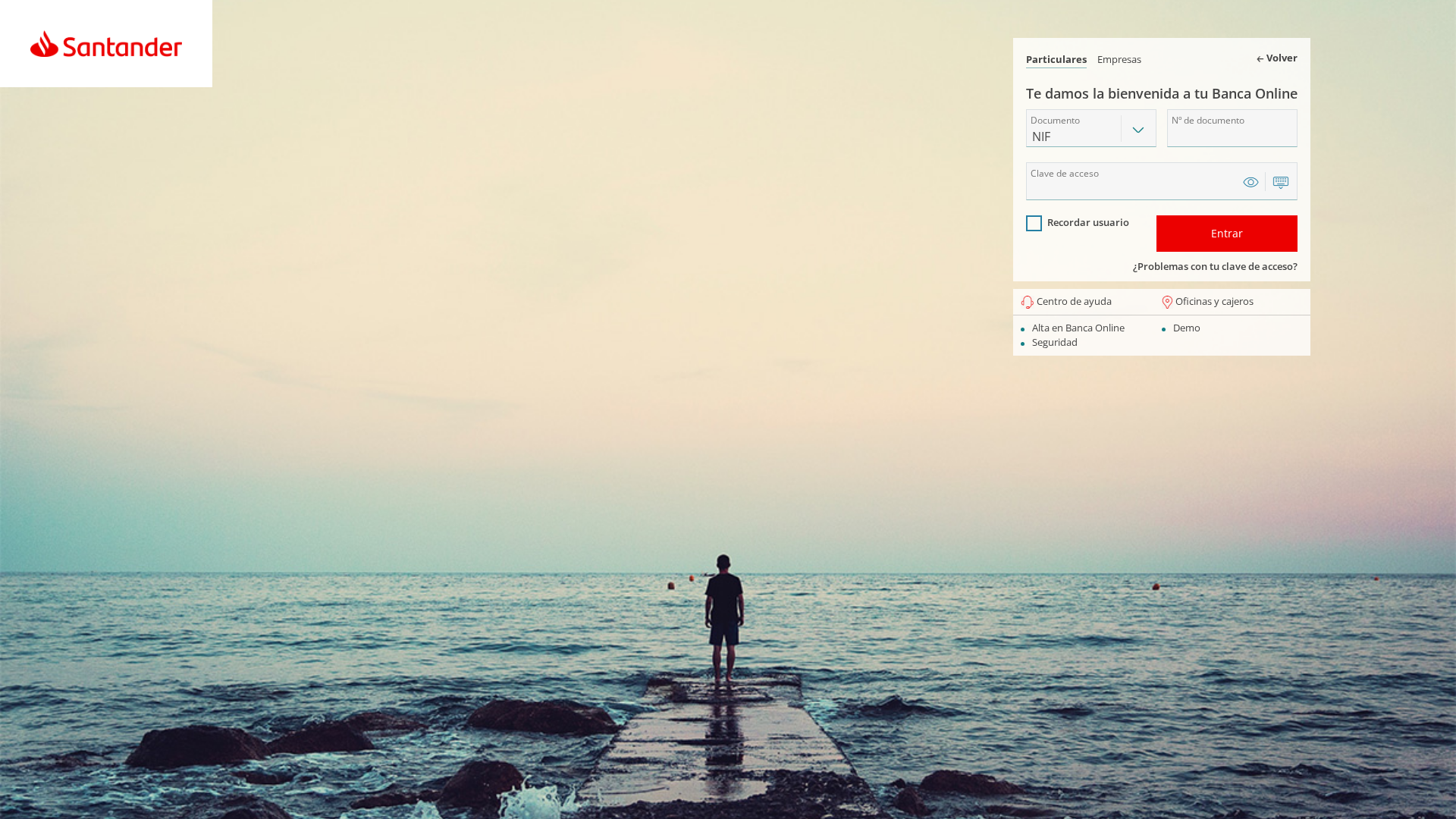
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17651CF205189BD2F048392C48FB55B8E67D58321CF530B4512EDC39E9EC6D98DD2B845 |
|
CONTENT
ssdeep
|
48:dJoPDCSEGquo/vGjnYQZV1wpuM6e1e30DUH9Ab0GAkxo9orVClWTbK:rUuSM0YcTwpu54NDCjGAkxworVClYK |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
d4e83dc12df14a5a |
|
VISUAL
aHash
|
ffffffffff200000 |
|
VISUAL
dHash
|
26c4d5e6f0e88874 |
|
VISUAL
wHash
|
fffffdff08000000 |
|
VISUAL
colorHash
|
07006000000 |
|
VISUAL
cropResistant
|
26c6d5e6f0e8c85c,c8e8c88c1478f426 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Clientes de Santander
• Método: Suplantación de la página de inicio de sesión de Santander
• Exfil: ./Assets/php/config/func.php (Probable)
• Indicadores: Discordancia de dominio, formulario en un sitio web no relacionado, logotipo de Santander.
• Riesgo: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- base64_strings
📡 API Calls Detected
- http://localhost/ES/santander/panel/api.php
- ./status/update_status.php
📤 Form Action Targets
- ./Assets/php/config/func.php
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 6 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attackers are using a fake login form to steal the victim's Santander login credentials. The user is tricked into entering their username and password on a site that looks like Santander, but isn't. The stolen credentials can then be used to access the victim's account.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🔬 JavaScript Deep Analysis
🔐 Obfuscation Detected
- : None
- : None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for encausticcementtiles.co.uk
Found 8 other scans for this domain
-
https://encausticcementtiles.co.uk/santaticket.enc...
https://spotifycaseid.encausticcementtiles.co.uk/
https://spotifycaseid.encausticcementtiles.co.uk/p...
https://www.spotifycaseid.encausticcementtiles.co....
https://www.spotifycaseid.encausticcementtiles.co....
https://encausticcementtiles.co.uk/account/pages/l...
https://encausticcementtiles.co.uk/.well-known/pki...
https://encausticcementtiles.co.uk/.well-known/pki...
