
Phishing Analysis
Detailed analysis of captured phishing page
Captura Visual
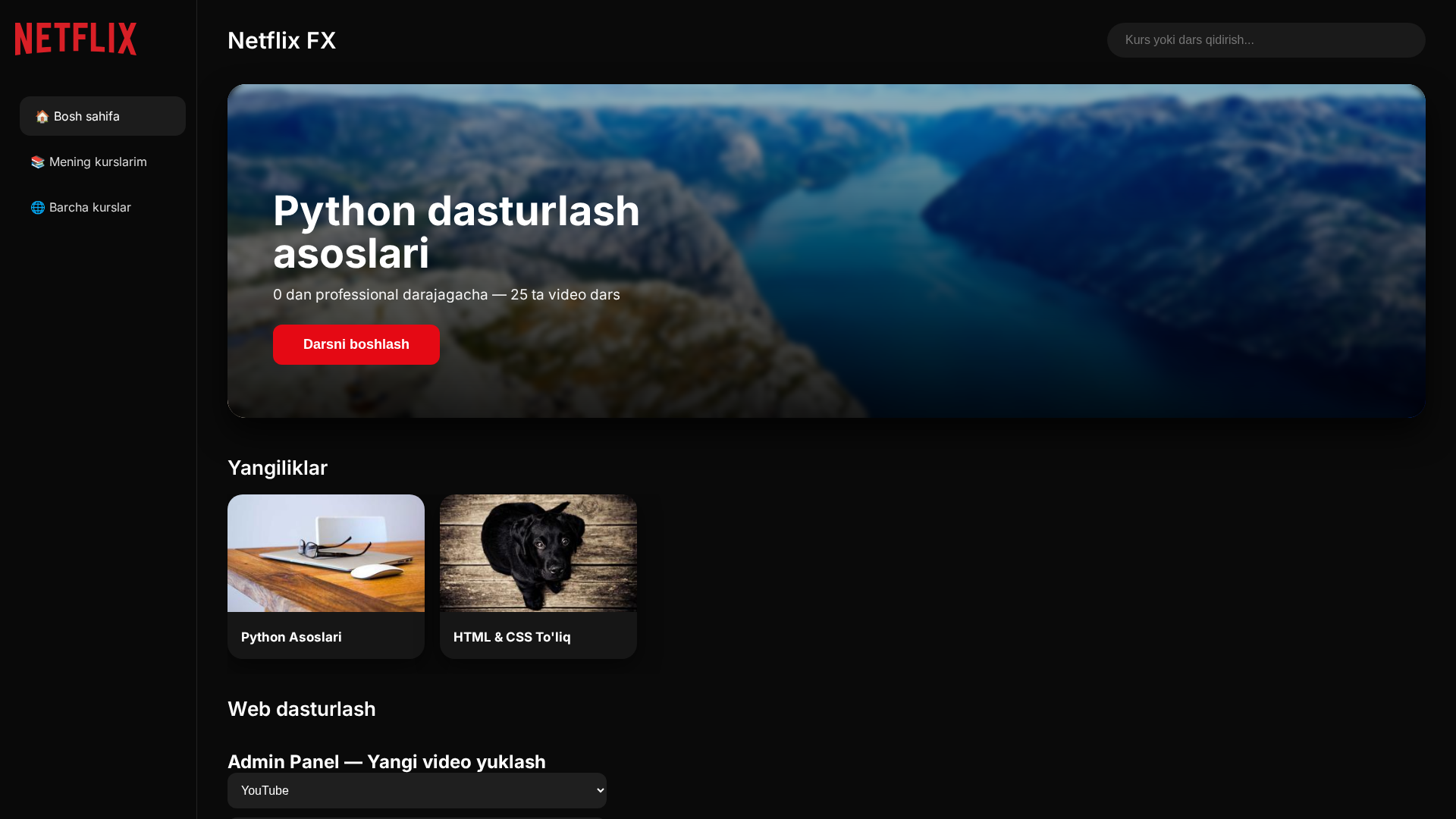
Información de Detección
http://lutsifermorningstar.github.io/netflix-fx
Detected Brand
Netflix
Country
Unknown
Confidence
95%
HTTP Status
200
Report ID
78867f1c-7a0…
Analyzed
2026-04-07 13:22
Final URL (after redirects)
https://lutsifermorningstar.github.io/netflix-fx/
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A161F13064588D774283E2E8FAE06F1E2199C351C6130B0417F983AD8FD2E5DCD766A1 |
|
CONTENT
ssdeep
|
48:Ab4KX4tKkyCQ+i5uUx3IoIA6fZBaXHQIdeHu+/:AvoJQ+i8Ux4VTfLagIR+/ |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c19fbe603c3ce138 |
|
VISUAL
aHash
|
3f7f796060700000 |
|
VISUAL
dHash
|
f6e8c3d0c2c088c8 |
|
VISUAL
wHash
|
7f7f7d7860704060 |
|
VISUAL
colorHash
|
380030000c0 |
|
VISUAL
cropResistant
|
6372f2d0d8d89898,a0c0ec844eac392c,f6e8c3d0c2c088c8 |
Análisis de Código
Risk Score
50/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
📡 API Calls Detected
- https://raw.githubusercontent.com/LutsiferMorningStar/netflix-fx/main/courses.json
📊 Desglose de Puntuación de Riesgo
Total Risk Score
70/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Credential Harvesting Kit
Objetivo
Netflix users
Método de Ataque
Phishing webpage
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Netflix
Official Website
https://www.netflix.com
Fake Service
Credential harvesting service
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
lutsifermorningstar.github.io
Registered
Unknown
Registrar
Unknown
Status
Hosting platform (subdomain)
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for lutsifermorningstar.github.io
Found 1 other scan for this domain

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.