Phishing Analysis
Detailed analysis of captured phishing page
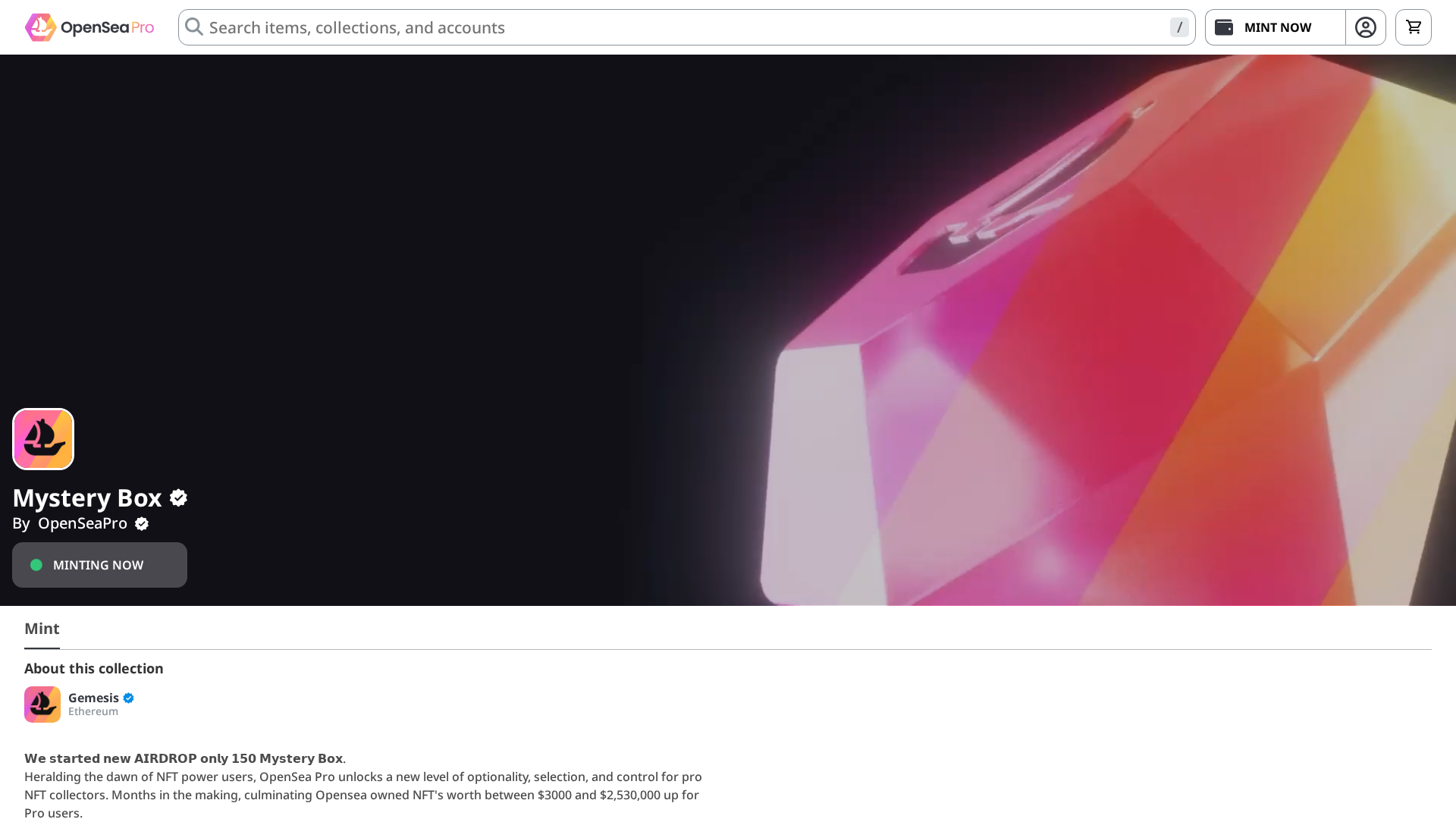
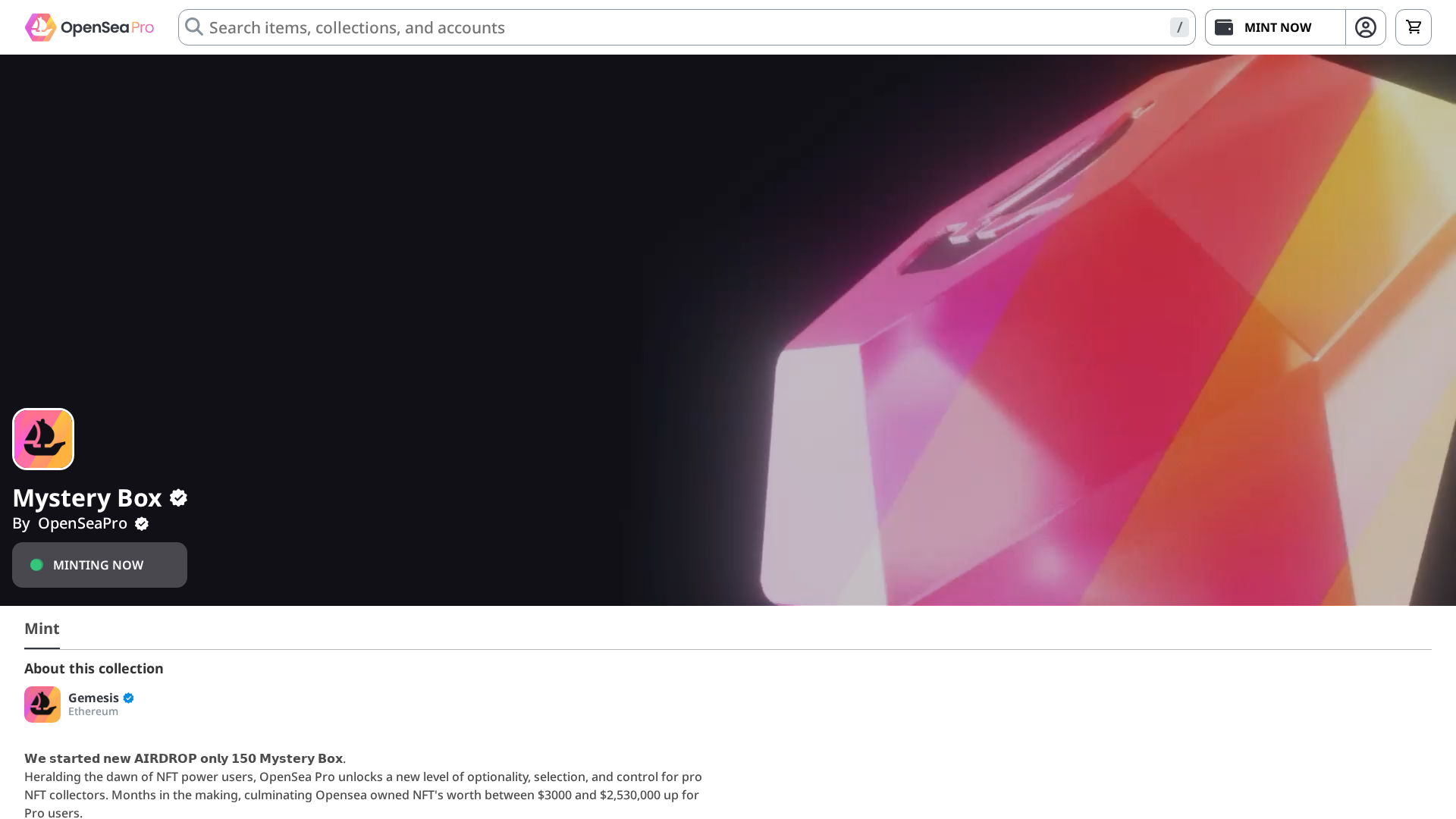
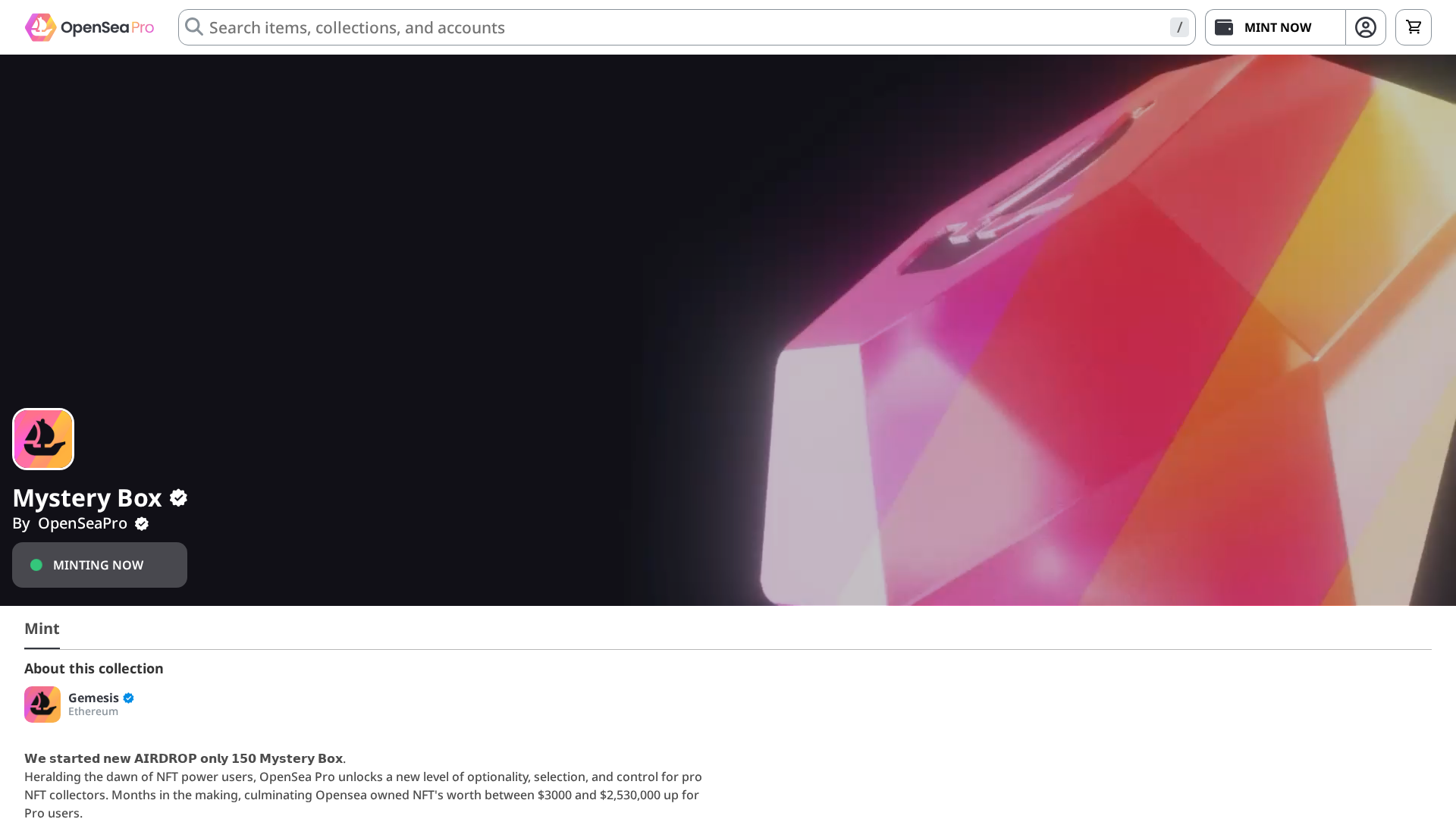
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T18E33F9F993A8E6F5E501D3E8DB214575736B11FAAE82C720C3F8DF9C69A584DCC58880 |
|
CONTENT
ssdeep
|
768:BhXTRlXND9bVOvuOdIP3hyCBE8hXTRlXND9bVN:7RFVUuO2P3bRFVN |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bb26c4d9dbc092c6 |
|
VISUAL
aHash
|
ff0101090d0fffff |
|
VISUAL
dHash
|
b60f9d5b5919d2f8 |
|
VISUAL
wHash
|
7f0101010d0dffff |
|
VISUAL
colorHash
|
132000c0002 |
|
VISUAL
cropResistant
|
02b5014e0e071717,172d9b59191980d9,fcfdfbf2ccd840a0,170f2d1b5b591919 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de OpenSea Pro
• Método: Suplantación de identidad a través de una página de destino falsa
• Exfil: Desconocido (probablemente información de billetera o frase semilla)
• Indicadores: Hosting gratuito, logotipo de la marca en un dominio sospechoso, código ofuscado
• Riesgo: Alto
🔒 Obfuscation Detected
- eval
- fromCharCode
- unicode_escape
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 2777 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Impersonation
The attackers are trying to impersonate OpenSea Pro by using their branding on a fake website hosted on Vercel. They likely intend to trick users into connecting their wallets or entering sensitive information.
Secondary Method: Social Engineering
The 'AIRDROP' text is likely used to entice users into interacting with the fake website.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)