Phishing Analysis
Detailed analysis of captured phishing page
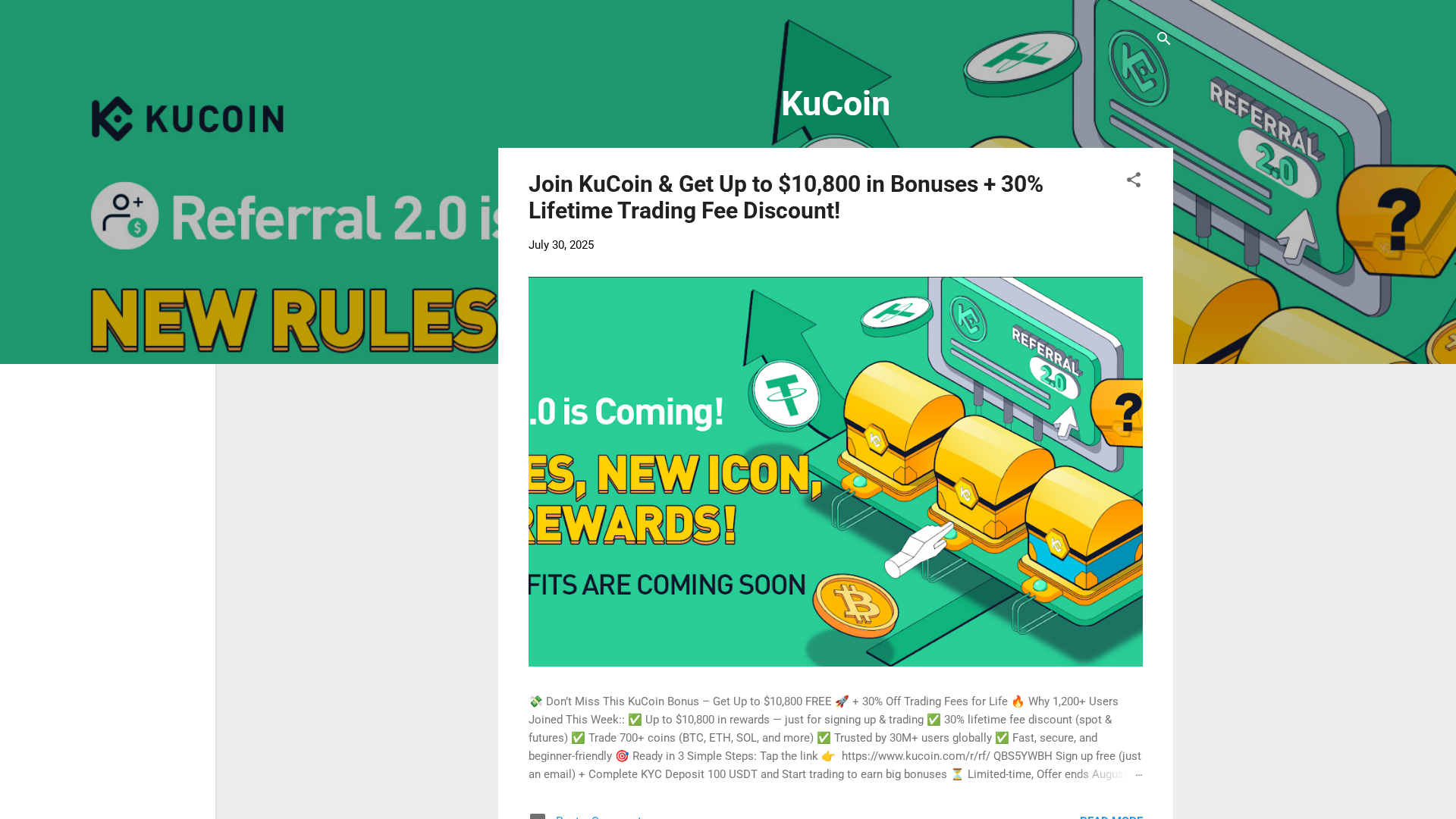
Captura Visual
Información de Detección
https://kucoinrewards.blogspot.com/?m=1
Detected Brand
KuCoin
Country
International
Confidence
100%
HTTP Status
200
Report ID
84600c0c-296…
Analyzed
2026-02-25 04:08
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13B5274A25025A92B1363C6D5B7B2F65AFB418147CE82454FD0F9D36C2BE2D71ED2A320 |
|
CONTENT
ssdeep
|
192:G3YsnFbOY2jwtkg04MZ+FXJKQM6kSZ7pm5c1ri:SFCY9kg0JZSFpAk2 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e7161c61e36d1696 |
|
VISUAL
aHash
|
00041c02e3e3fbff |
|
VISUAL
dHash
|
4e7cfc4a0f0f0334 |
|
VISUAL
wHash
|
00041c03e3e3ffff |
|
VISUAL
colorHash
|
06000008c00 |
|
VISUAL
cropResistant
|
cce2f17c5eee7231,7cbc6c0b0f0b0334,26ad5b74bcbc6c6c,48cc0c8682907169 |
Análisis de Código
Risk Score
74/100
Threat Level
MEDIO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de KuCoin
• Método: Impersonación a través de Blogspot
• Exfil: Potencialmente el correo electrónico recopilado del registro.
• Indicadores: Ofertas de bonos/descuentos en blogspot
• Riesgo: Medio
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- eval
- hex_escape
- unicode_escape
🎯 Kit Endpoints
- https://www.blogger.com/share-post.g?blogID=778339269166981657&postID=3196719827301352010&target=twitter
- https://www.blogger.com/share-post.g?blogID=778339269166981657&postID=3196719827301352010&target=pinterest
- https://kucoinrewards.blogspot.com/search
- https://www.blogger.com
- https://www.blogger.com/share-post.g?blogID=778339269166981657&postID=3196719827301352010&target=email
- https://www.blogger.com/feeds/778339269166981657/posts/default
- https://kucoinrewards.blogspot.com/feeds/posts/default
- https://kucoinrewards.blogspot.com/2025/07/join-kucoin-get-up-to-10800-in-bonuses.html?m=1
- https://www.blogger.com/share-post.g?blogID=778339269166981657&postID=3196719827301352010&target=facebook
- https://blogger.googleusercontent.com/img/a/AVvXsEhX6Iwp6ECa8dPzBdt3BVlNuahA-dZIvq0D11NoQ5RfulPOnPxrnXb4cy5XtTyJ2g3beqvv-YlAPD9LCFYjQqEuVJw1ajcT_ytGhPzuCrNnf6eRzXJZMgz97khDBgYdwcmmnSYJ8KIpvGLMDw7aBcUPoPpqbeXZXas9NTuh_c7RbNs-qkIiFzQyz-guHumb=w640-h280
- https://kucoinrewards.blogspot.com/feeds/posts/default?alt=rss
- https://www.blogger.com/share-post.g?blogID=778339269166981657&postID=3196719827301352010&target=
- https://kucoinrewards.blogspot.com/2025/07/join-kucoin-get-up-to-10800-in-bonuses.html?m=1#comments
- /responsive/sprite_v1_6.css.svg#ic_post_blogger_black_24dp
- https://kucoinrewards.blogspot.com/
📡 API Calls Detected
- post
- GET
📤 Form Action Targets
- https://kucoinrewards.blogspot.com/search
📊 Desglose de Puntuación de Riesgo
Total Risk Score
85/100
Contributing Factors
Domain Mismatch
The domain is a Blogspot subdomain and not the official KuCoin domain.
Content Red Flags
Offers of large bonuses and discounts are common phishing tactics.
Hosting Provider
Blogspot is a free hosting service known to host phishing sites.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Credential Harvesting Kit
Objetivo
KuCoin users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
HTTP POST to backend
Evaluación de Riesgo
HIGH - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Personal Info
- 12 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
KuCoin
Official Website
https://www.kucoin.com/
Fake Service
KuCoin Referral Program and/or Signup process
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker likely aims to collect email addresses or other personal information. The user is lured to register using the malicious link, exposing the user data.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
kucoinrewards.blogspot.com
Registered
Unknown
Registrar
Google
Status
Active
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for kucoinrewards.blogspot.com
Found 2 other scans for this domain

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.