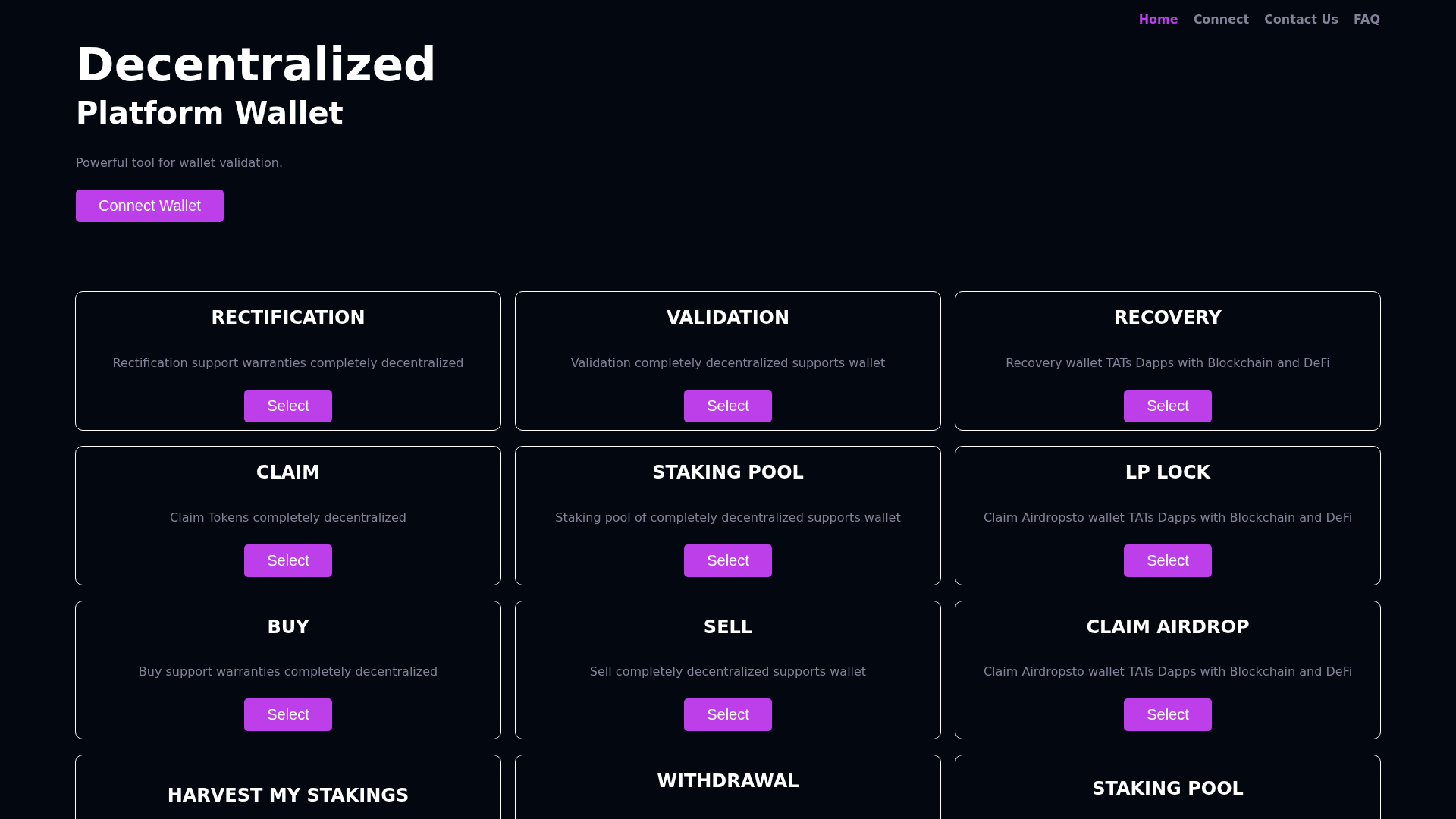
Phishing Analysis
Detailed analysis of captured phishing page
Captura Visual
Información de Detección
http://gadyahjd.pages.dev
Detected Brand
Unknown
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
8ae2a36a-e59…
Analyzed
2026-04-06 17:27
Final URL (after redirects)
https://gadyahjd.pages.dev/
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T190E1456246C5B23A022A29C4E22187AD70DE027DDEC76D7167FDA8BF4BC9D50531E18F |
|
CONTENT
ssdeep
|
192:1t3raj3Ea3F3Q4Z3t+3l3tF3S3s3W31Z3j3oX3nO3bX3l3Oz3V3W7+3Z8:HraTEkxQ4F+Rtxcqw1FToHnoLRODhA4y |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f07ae2e1c187071f |
|
VISUAL
aHash
|
e0c0805a5a5a5a5a |
|
VISUAL
dHash
|
9289369696969696 |
|
VISUAL
wHash
|
e0c0c05a7e7e5a7a |
|
VISUAL
colorHash
|
38000000038 |
|
VISUAL
cropResistant
|
9289369696969696 |
Análisis de Código
Threat Level
ALTO
⚠️ Phishing Confirmed
📊 Desglose de Puntuación de Riesgo
Total Risk Score
0/100
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Unknown Threat
Objetivo
General public
Método de Ataque
Phishing webpage
Canal de Exfiltración
Unknown
Evaluación de Riesgo
LOW - Automated credential harvesting with Unknown
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Generic Phishing
Official Website
N/A
Fake Service
Credential harvesting service
⚔️ Metodología de Ataque
Primary Method: Phishing Webpage
Generic phishing page with unclear attack methodology. May use social engineering, brand impersonation, or other tactics to deceive victims.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
gadyahjd.pages.dev
Registered
Unknown
Registrar
Unknown
Status
Hosting platform (subdomain)
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.