
Phishing Analysis
Detailed analysis of captured phishing page
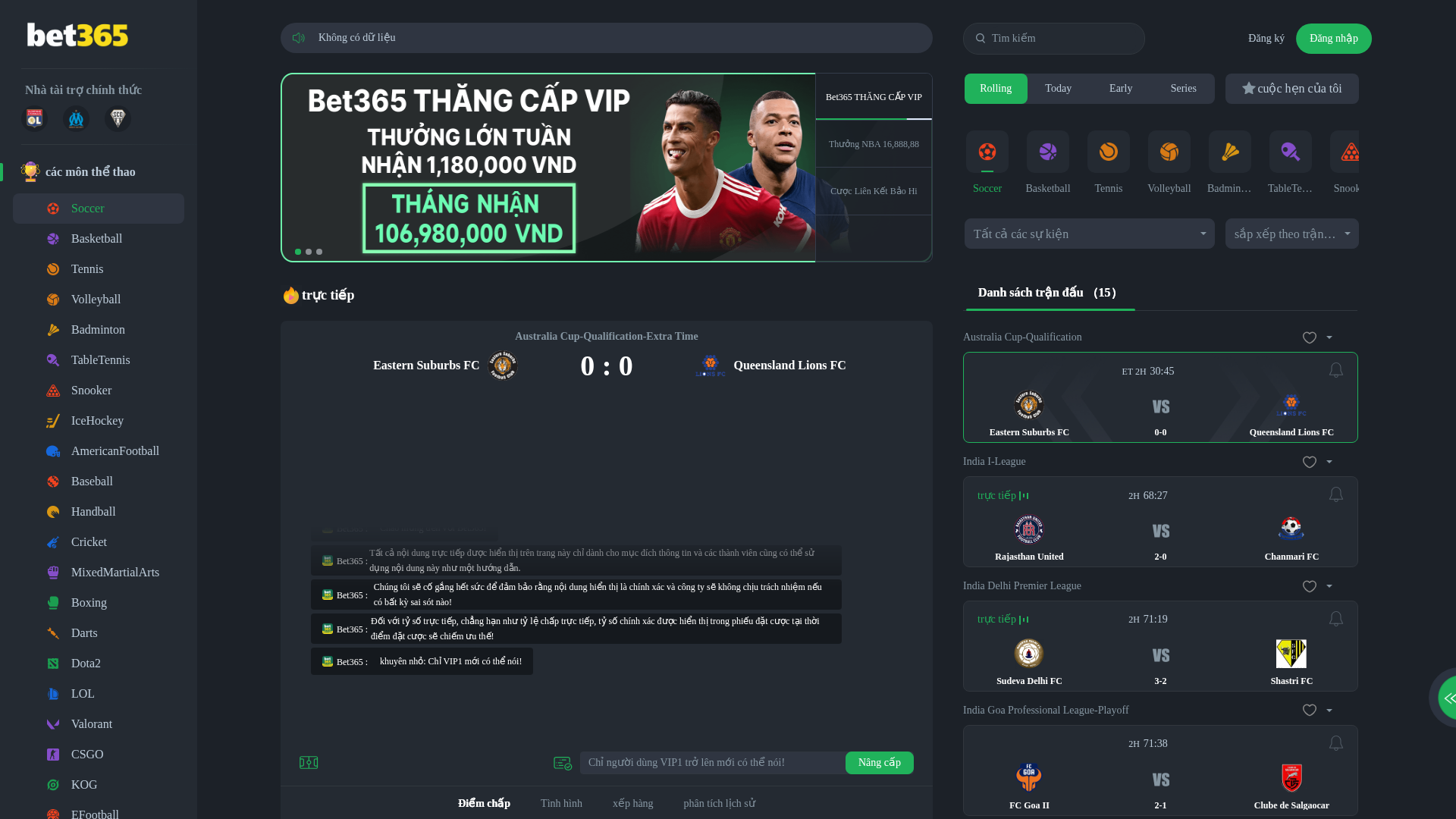
Captura Visual
Información de Detección
https://ydnaz.ksa9noa1-sdoqd.com/
Detected Brand
Bet365
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
8e094f02-39a…
Analyzed
2026-04-01 10:01
Final URL (after redirects)
https://ydnaz.ksa9noa1-sdoqd.com/home
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T141A32E247642103B6977D6C0ED64BF1A61D3F30FC9994844AAFC43A41FDBE7278AA874 |
|
CONTENT
ssdeep
|
1536:wfOKzkFMgpNLqnF+Z0V50NMdmk5o/p1wtMsaICVj41gpoMJfDPwDcvUEW:wRWLqF5rqYmk2hm6PX5mMhkDcvY |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c7c7cf383838323a |
|
VISUAL
aHash
|
bdf8b0808080041c |
|
VISUAL
dHash
|
4542446444444c7a |
|
VISUAL
wHash
|
fdf8b4b880a485ba |
|
VISUAL
colorHash
|
07210000200 |
|
VISUAL
cropResistant
|
4542446444444c7a |
Análisis de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAADgAAAA4CAYAAACohjseAAAACXBIWXMAABYlAAAWJQFJUiTwAAAAAXNSR0IArs4c6QAAAARnQU1BAACxjwv8YQUAAAriSURBVHgB7VpdjFVXFV5rn3NnmF9mCgx0gN6hImil0Bqi2KSCShM1aKzxhRAg6kP7IPRBY/0ptE0fTGumFSlpo6YNptGnRmttxIRG2wRKYqtg1DbSUpgihQLOXGaGmXvvOXu51tr7nHsurZ07c+dOA2EnZ/bP+dn7299a315730EiCuAKTgau8HQV4OWeQpiJ9MObtgKVt0AO9sL9//wlzGCaGQaDWK61gOUn4IGlb8AjK/MwQ2mGAEZ5CCPi3JWLQ69D/+IdMANpZgCa8loIY4ScMMlApYzlnbB7QT80OGHD18E967ugcPQcGMsMWgZICIaBGilbUYGfwB3nvwMNSo1ncPSNLzNj4C+EsEyVOpusKd0FT87eDg1KjQdoSjsVTE7AiYlaVH8UcCnI4g54ekFDhKexAHct2s7q2acgRGBCfwWxAynqGgrguBvK5xoiOo3zwSeW5WFk8GXuoTv1N7lMcik4AmSAPAIyRHjN8nnwuVeHYBpT/Qz++IZV72oTcKNDzzNDXRn/S0zSmWcuJmUyx1McArcZsBcHtsnrVC7Cmfs25U9///bNUGeqD+CPlvRDNPJwVZuAu3iewUVsmsxUjgHlFBR5s8z4IpI1hhkMwAZcQVorn4iH3kEbD32LgvGfnb7/Cw9CHWlqJrrnk11w4e3n+e2VzEABvn1yrrY/tmAb2PK9bH5dvByIrxGbI6ZmmZhogECIkjNgw+ZppC5AB836c/MKj23Ol4YLfyBjF6OR78DhWV19Gzq/+YsCTDJNLRYdPsUMMbhABz8bHp2/g0GtA4w/raIRJL6ll/gbeWBITBgYB8rVpeza+OrCl5bno2jp3dhqexlcrOungRUle/QZ7nkdTDJNnsGH8g+DibalzGic6Rdxx1RmIRdg4EECkZqjAiIFxGWLDiQGWqexU/n+8Qudd6ACY+EJQHKQMtPx+JyNByeltpMD+Mh129kE+6uikVQJPSD2pKRM3I4iIIzLogPngHG3XCefe9BAUSuMvr1omGciQgdO+rAeIE8CxSxI93VvePnntQ65doAiHoXCK9yR8y9UVawCVGFVZ9+Zo/obgwoFDFe0zfsdl5k5kjwqt2JxsEdoLjDnZQbDVsEXPy5sEpeNY7PQ2bP4Frjx9xdqGXbtPjhS2MkD76qIhVfCinh4oMIopuxgaJRBZcybZcYHldmo3Anl0U7AFst4bMxrYiRgZG0U5owzT/6ssAltw2PH7+kA+G4tw66NQSf9rwsrKVPKUuzBkVdKAgbGOaq/kUnAOKZkScBA7wlAtNTMzHWAtU36riz4jPAM62lEyiDIxPEnGZhQIWaLCpqKUcdnu2/+68mJhl4bg8X/unjSsYWqiuKH6EVGgMmKmrKDmCm7PGDAbKrWzMKYckC2GSwwsCZmzUTglwP5TlEYs8atIGzoYqWayP0R2rEpHP8q13460dBrAxjwfs4kcq8segalrSL9UdAOMc5iEM16qTrqpJADiaKWAKlomLKCUnAoADHiL1npMolAkDw4XSgTpFyO7ddrATixiT45dy3Ysf2peYpJqmoSKVMMLg7boZibA7Fp9YD4vWILwKlFnM8CmHsecOF/mC1hKgEoPsXMp6NGYWeczeJ0Asit/iRJOgKXO8giPxZaNnas/tuh9xt+DQwW16bmqb7n1iT1obCJccxngC3gxKDs2eIBHOvjvWCbG/rpXqDBOYB9A4DXvgOeFLW2tALKXVE8DHTxdMAccOWYQP8IUlSIBktruFAnwFDMUwGKqqUyb3MMruNasGEARrZCqdk5gPFQt47NDYX/lJuA/vExsOfnAl7/JkBLMQNOHhJuaNxJrgIWgsEBdnWN79J39LkbJhz+RA/weUqXBM0uVnTCYXMhlubM17eNggeHRHt3NodRMyQI0MF0OAYWA5ydB/ChY2y2pyBDp3ASKa2E3g6VZTVTd9/7oX+HtXXFRMOfGGCOrnMhlguvbMjgeuYChZmenBm5KwHDjL1X0gGWGfzhm4HO9gAu/TezOSavFFkd9RGiBFQiLJ45SmwCwN+bDfUCZHnvplT6A4g6O7gtB6k6OHPyBWdNapLKYFJJ0KGrJ3r45hKg0wsAlr0G0PvWWDJ6ifAIHEaFaqXi3nUtHjZNC8DArWVinrkcxS3t6Gc6GbUXi2yb8QxWTLbyQT/opD7Mz73CWnGqt5mW/6sEraMWdfmTJR0zJpqoKqQqWpmpOgBCGBxncH0aL7Z1oFvRK95VpYJ+ljX3Joo6AVSN8b36GVjaAmd7m3D9M2ddBI6pQJEGs/p93iFTaqb83Qn3hxMCZJUsQBqNsBKm7GX8jbJ1qALojStjqVlWqfINAZTjZSYWh8/cpoS0hHb0viiloP5QDXPhYV4BV1EQggaEiZBU5LoCiip+qEKS/Q5USVIVNG3rHSjC6heGxd9S07s0iiH/motIeXmCt6BegKyaR4ihsbCQ27QlQwSoKkM1cIyaKs/4+dZReVSp9zSVCFb/aZgWHiu559E5dWYCxRn1VWf+qrLyJIfhr0K9AHPNbS8Uo4vcb+jFBd+1QCejFlHw+lbNYFY5s2nZ4TG48dAY5MYtWMiwhh6Qb0gZRL+O+Pth8wGoFyCsOX4ED/UO8Uasi7ehKUDvNZXxa3xWiafw/6yDmtoLQLc8Z6Hn5EUnHGicn16y/mXBJlh9G78w0PbFA9MAkJPN5XbxVuFeYZAyapmNJd1kZxi+xAeTKaEVHDre9CIH7aULvOUwkC4J4BjCdFEHShiDrEh57DEehBpSTeei5bYP7yZxQcuPW7+hSXNfjn099vV5vHsQPxQmJZ/FZv75pwBW72d/Ll3kZ4jfQWLV5MEiWhd7ujZ0u2L3Pa3LHlC2/3Jf+ohy1zxUy9hrAtjxkf1DFIa7tJKCef+cPrWPQY24o42P/gXoK48DzD8hAx7HyJTJqmk6YFo2JgGnYGIPSIUtaZPNrpxcmF93femPA7WMveZDp+HX1neZM2eOUsl0p4t5GihfoqqZALoqt1hkUOO+ax4suUDAiWNFOV0Ik/lWGm+Lr5+IW7s21Aqw5qN7YZFPxh5wJmj8dSl74E0UvAlX3S/yUVJRD0Jjz5AckCpLcpbh2OH3jfp6bIw3S2ZV7snOWnAHD9YKTqdmsge/I/s+3s8zf1c1i1nWkvaMwpJsZE1Jn7EJ3f5+EkiDD1MlI9dGAKng6H1j9sze+NL3YBJpSr9NjOxbtR/KZl1FNZMRVExVYZKeSbBZUpROQrLlSRdtv9xU1BgNVYNzE4DPtm8+uBEmmab06xL1zfsax6e/TcxQ49PYaE5xUuexx2aMIj4hZvPidhERo6bmRUVExsg+TBVUzdaI+SqrVg7tjDNNwmdtz6I7YQqprh9AR37ziR1k7U5w8WHFPC2UWSdkd05YCQzQzWbKJCQBtNqkExtMI4jE9A3u7thy4G6YYqr7F97hp9dshdjew8UlbIq8uqmvWRmswcygJVG6s/BbhBRgEq1mnx8sBU13ztn6599BHWlafsIef+62fPnC8A8Y4EZ3HiYnX74DcDvytEbZvpMgNsMY0RD/CLFnuPv6Rxfevrfun7On9Tf6wq9uywd2dBOb7SZmKw+qIugstXovR3oUmMaYqjuDTPmeQsjAtuydtt/pG/ZPCCNPfeZWiKOVTN+tzGCemVnC3c32KnqC+y2wxBxhRo9A0Pz39m/sfxEakBr/n04fcLr6D7GXe7oK8HJPVzzA/wFrJ9TAksrY/gAAAABJRU5ErkJggg==
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAACgAAAAoCAYAAACM/rhtAAAACXBIWXMAABYlAAAWJQFJUiTwAAAAAXNSR0IArs4c6QAAAARnQU1BAACxjwv8YQUAAALpSURBVHgB7VhRbtNAEH3j1AhRIcwJyA1qTkB6AsIJmnyiqqIIEvGXzQ9CKigNbeGz7QkaTtDcoLlBzQ3yA0JN7WHW67SJu3YqhYQK/KJk17PPs2+9O7MbAwX+cVBe4zv1tYwl4IN6GWS1ZQpstvY7DGxjKaCjnfZm3dpiM26rjueyey5VD0vCKo0eK/V6mLav2Mgu7lUB9kR9cEGldSwQLodnUng/oxU9Wwq3ESjiNuJfov5uzvr4E2iqvS4ztaSv57AIdNKGODAYFV13gS4WjAtc7iZV/63aq6TbbwgMOWrpUqZ38F5tDrBg7Op1R+jHfUaoYpZAmdhK/Eu08Kd3jeg4Log2lAToZMuUwDdqT4+grOslOH0sCSOEPSl0BHs/4gCFXWBJ1kFS7eclT71Om62Dk6YZUC70umq09k8b6sDP4uhpJsK3+CKK/EyBPM57RAFyEOGyxuAqg2qYAWLnlRQV6Xgm1yhyHk1dTl5IuAfGKft5PpidNVPBM8wEl+OCaC2XBTyJaYi+I0vgCpV6CdnPmj6zP/O4zZMtMXM7lGmt4XrZVGxpxPgUe5LaIpiItgqM1x2REcl0mHQw5Sjk8HTSJoPp2EQ21ZcqOOpM2sjiU/NCxokh0NFHtdWfuiftWO/D99g94ySaRYJEFw2EWB7b9BYoaeiFjOIQV0/I8JK62MgbcyPiuiPirn0iMN9pniPbajo4b+RBHVFMUXtiDNpB5cq5JFXtaEeS+IhG69J5d5JnvqZTGUD3Aa0+1U9F38OE48RpeYqHOO+2bZnDepppqM81sKOfzkAEtB05OGj7CK51b9brcoRLf8zTWMXDnlL14UyuiXJfprcugz5K8zMOC1cYflJbvRmc8YEzwC2Q5jbU/oZeyFlwcMdRCJwXhcB5UQicF4XAeVEInBd3XmDuYUGOOt6i33CF8slDrkB99JcT9Dn+IqxTLP/WAiwZBBra7RlQ6tAb4tdSXr95uD+0HW4L/Bf4DQgaGpUgZNDaAAAAAElFTkSuQmCC
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAEIAAABCCAMAAADUivDaAAACQFBMVEX///8AAAD/////////////////////////////////////////////2P9dL/j/u/9IIvbglf/SiP+da/jakP9NJffGef/tpP+icfmYZ/jXjP9QJ/jmnv/QhP+NW/liM/lkNve7bf/poP/Nf/9sOfndlP9NJ+DLfP9oN/lWLOD60f+WYfqJVPnvp//yqv/BdP+fb/qRX/pWK/f/t/9UKvf/3f/jmv78tf/0rf+XZfupefmmdflXLPg2CvZjNd/3sP/km/98SPpdMOH3zP/m3v1FId92Qfn/yv/0yv/hmP9EHPf+0v6rffm/cf9wPfqEUfmBTfn18P/2x//Puf1EA7C3aP+wYP9EFPZdHru0Zf/t5/5jQPj1wfY9D/ZlN+ZNC7P/4v+ES/iBTuxOJ+psQN9XFrj/8//10v+wgPlNIPdQGPcvAvV0RuN7TeH59v//6v//wv/ywP/wt//pnf/Hc/+6lvucgvqlb/ieZ/h1VPj3yfdbNvfxtvbtqfZuPua+av/mqv76wv3TwfyumvugWvush/qVe/qpdPm3j/hoL/iKVPFmNu9wPu5cMO5WLOg8HN3i1f3Zzf3Iqvzg0fu/sPtcIfglAPWocu+SXeyHV+R1QMU6AKr44//nlf/Xhf/pxv3mtP3go/ySTvzEpfvZnvioY/jXyO+2ce55R+ukgNqRVdRsMspiI77di//GuPy1bvvOjPmIavl9XfhtTPfLlvWWW/XixPHBhfCeZu/RsO61due3kuJkN9OJdPigYduHRNRch596AAAADHRSTlPyAPXoccfAmIKAHxjBIb2VAAAGZUlEQVRYw6TT20sicRTA8Wm71/yQMlCj5kGI2JlRFJm0hC5r7BgGbToPEoIWXnrQNEMUUcggcnuSfGjVloqitgvLPrTtdmH3X9ujpuPPtmTX74tP58MZjj+iBerp7mgl/rnWju6eFqhItL0h/7M3bWWik2yiziLRRjZVWwvRSzZZL9HVLNFFtJMNW8vYTiLpSCSyt5VZJOtrJ1obAdmIlGKp7wyjiMVi8tWTDInXSjQ46NL28jKrVSikUo1cLjcajdFoOosftgFhe/9xQatlxqvGxPx8NHqyiBHEC8NBl8tLfmU1E+wMxYzXGqvz0e1ZshrxAuFFFosF+fbMQdehfEa7CwgYgIAByM5OpiGBLAiBwnEIBYM5p/1KW2cYZxsQLhBoGpXz3noEZ0ADhqLGmF96lfCCYDKhSuSd03lFUQxmRNOvEshCr1uRGPlQ8AQCu1qmYhQPE7O9QnBWaxgEMZf3svDo9sM/rMbYmVh8iTi75dePrBwSo3mOzl+tnm6eatia48b2/kpkH/LXp6nNqsDBN8XjcYdFYuD5EC/RUIrqYYywRj1xdpH3CIV7viLASem4w5FKSSS6UEgC8ccLjGjEbBgBQN4pOD3CpQQEcd4B4zpJpZAuFxAPI93GiVmP4LHbndfHapMLAEQ7EokEDOPx+4858cVIZzHiQrDb7R7nuZ52cYh3JJJJg16vhw1w4sYdoKoGY3tOCL+nLBxdnFcbpiB9vRIyBPy7DMOUDSaCEXeCBz5jE8UTSaVSpVarDRCu6OCX/+legdfPlF6MYmJNJKBfQkH4wSfHxjZkMplKVVaedoGK8yGeDt5MBigtILAHtIQRqfPLe/VQ39CQUqmUPVd0KZ6GuEM/rAFIaQ8mixG+z2pVX9/Y9PQQhCvAWOliKMihT5MrFFU2FNQWRiwODoz0QSUF2wUK+0wQDY/YlX7nZ5+McdaGEeTx8MDAyJMyhisqg9lUDAjuyO1eYUsI84w4HB0cHKgoc6BUvwha95nNJit9QFtQbvILWza0y3XEwXD/ICQqc6KiDPvMYJitJprbf+v/sFA2cAIaGe3vBwUQqGYXQDZkZshnMq+HJd8m3TMLZWN5q47404r9vaYNRXEAfxh7C5IOVJi4arWJQq3Fhj4ZVyUGGjCtFA0qEVoHozqErSKIoFCtzNofOLTtw1pGoawvXdeWsb3sf9u5ibfN1XYduC9J3s6Hc3LzcvKlZAcDK9DLtNaL9nYX37+F8lmf1fra9y50saz3sdYdIj6zrJ1A8ERwRotTH3xTm9pXN38Mk6wgY3lGwASOveRy2R9RliYWBmc0/9P7JgzE8szKq/gQ8fvslGVdoEA0BWJQ8Pcyu1AL7YYRIs5RJNE6lO0Wi0VXiGbIk7b61r21MDLcH0miwUumGAsGVgB5ULEu1iJZMQxxrxLElipxdNPlBwErmCHPaHP+yBsK7YpiWAynjUSxqnI2Kcz6IVgZnWh6acq6dBSJZDWiPUcZiXLBZrPRJqc/FrtXWF3ByMTmyfevxzUGBESI/U9GQpAUIMx0s+R0OmPAEAowL6ZPXlp+rYcYxhuCdGRRbItxI9EqmM1gSGEgtBDN2C8vXVfHNW+U8UYikVAo25FlWexvUwYiHlDNyKAnE85EglRcp6eW8/Usg+ohUO92yxBPWzASPZ4262nWU6nEneJn7ezVj4tIFOq9SMh2PG49cr9MYUKfg9YNaa2eTKEgpcTGznegfVSPhL2Ow+32DIz2pEAQFZ6GIMKRSKKknLFSognt4/r9PYfD44ELojWR36YIIsMjAQyaPqsDUK+f7+zuRw+iDMNo9aZJiANlYPTlOEEUq0DohmQ+Syaba1nmAOpRclAPANxGw5FfpUa7wH1Ipr3ofX3AhKM1go18mRoiKgVaDxjwiEaRkMtxgWAwiAG4seHOV6hhonGIBYTYbDkIxwWDYATAGCC4D0/ekR4hitU7AwhA9HAB3SCGAcEkUCSBIlQPCzyKqkjgYITjuAA5DBiKAwsEAbNUMpBqgFb4QoFXpQ3cB0cYkwG1kqYIYniZiAvdb43yTYbmgTFrBjGMgs/i6X1E6JVvbTyvbMAkd4ZNVW661DDxt8Uq3WtlJGCkDRRFVUzXW9RInj213nUb17dVGMaUqbR6aeqBPP+XJTMuCEK6+PiSOf6qO/7CPf7a/39+Poz/C+QPrzFqv+6wvhMAAAAASUVORK5CYII=
📡 API Calls Detected
- POST
- GET
📊 Desglose de Puntuación de Riesgo
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Code Obfuscation
JavaScript code obfuscated using 1357 technique(s) to evade detection
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Bet365 users
Método de Ataque
obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 1357 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Bet365
Official Website
N/A
Fake Service
Banking/payment service
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 1357 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
ydnaz.ksa9noa1-sdoqd.com
Registered
2026-03-24 14:30:35+00:00
Registrar
GoDaddy.com, LLC
Status
Recently registered (7 days old)
Hosting Information
Provider
GoDaddy
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for ydnaz.ksa9noa1-sdoqd.com
Found 1 other scan for this domain

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.