Phishing Analysis
Detailed analysis of captured phishing page
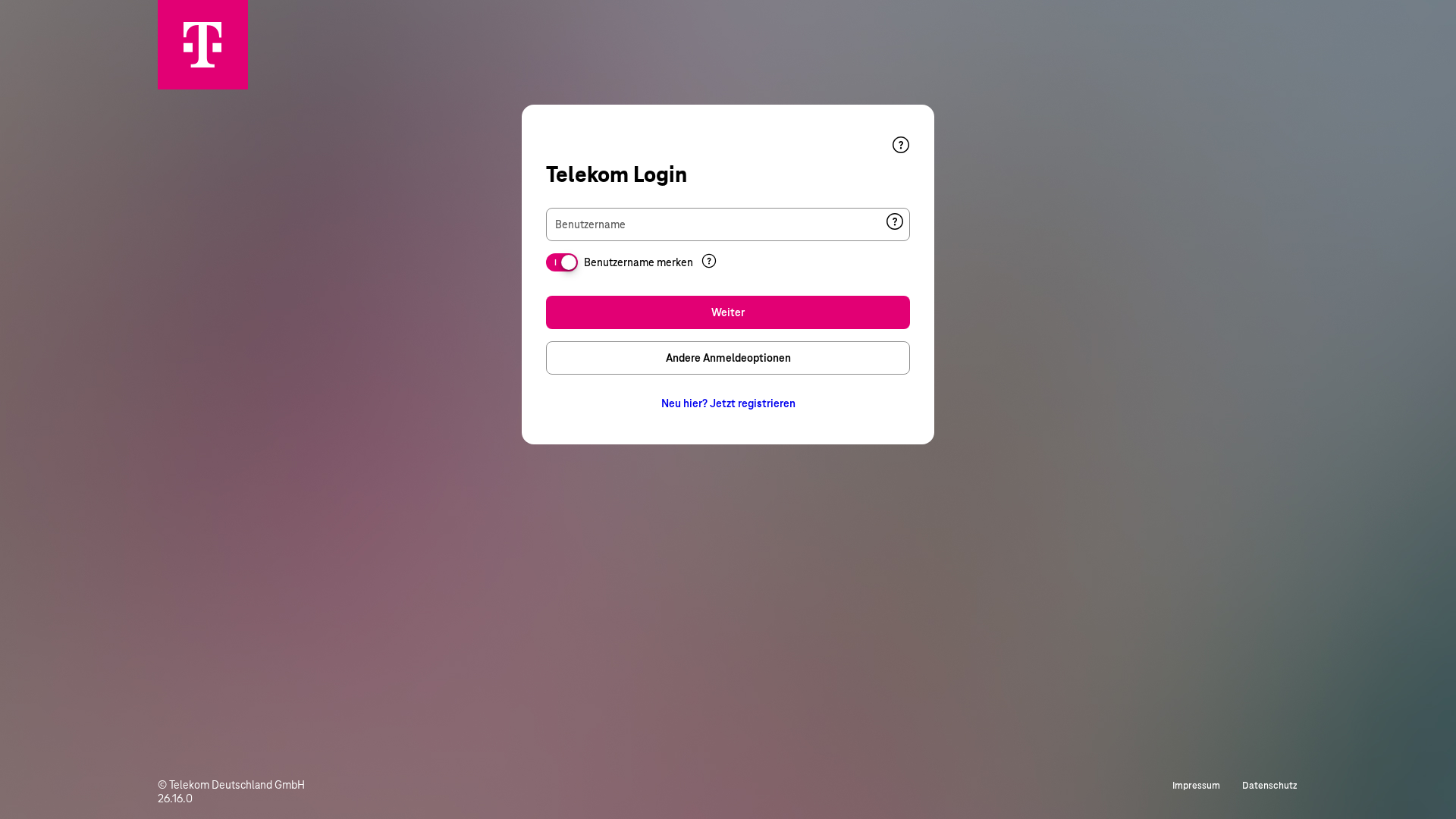
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C262C9A2C165AD3F4287C3E5A785AE43125991B4C79B1C0553FECBAE1EF2C61EC0E531 |
|
CONTENT
ssdeep
|
192:tdnVQCbGTuzzPk5ARUPVhO2uh+Bmiff6nI0FkXzVZWQmh5ycQX9EiNG9fQFkYUml:tn3GNcgSzSjy6mi5SYxEZV5M |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9d99722666666671 |
|
VISUAL
aHash
|
1c1c1c3c18000000 |
|
VISUAL
dHash
|
7232727272446080 |
|
VISUAL
wHash
|
1f3f3f3e3c1030e0 |
|
VISUAL
colorHash
|
07000000007 |
|
VISUAL
cropResistant
|
a0d8d8e073178c86,7232727272446080 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Telekom
• Método: Suplantación de identidad a través de una página de inicio de sesión falsa.
• Exfil: Probablemente roba las credenciales del usuario.
• Indicadores: Alojamiento gratuito, logotipo de la marca, formulario de inicio de sesión.
• Riesgo: Alto
🔒 Obfuscation Detected
- fromCharCode
🔑 Telegram Bot Tokens (1)
- 7903455868:AAFf...-bDTBlV0
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- 1 Telegram bot token(s)
- Kit types: Credential Harvester, OTP Stealer, Personal Info
- 4 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The phishing site impersonates the Telekom login page to trick users into entering their credentials, which are then harvested by the attackers. The captured credentials can be used to access the user's Telekom account.
Secondary Method: Data exfiltration via Telegram.
Stolen credentials are likely sent to a Telegram bot controlled by the attacker.
📡 Infraestructura de Comando y Control Telegram
💬 Message Templates (3)
| ID | Portuguese | English | Trigger |
|---|---|---|---|
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)