
Phishing Analysis
Detailed analysis of captured phishing page
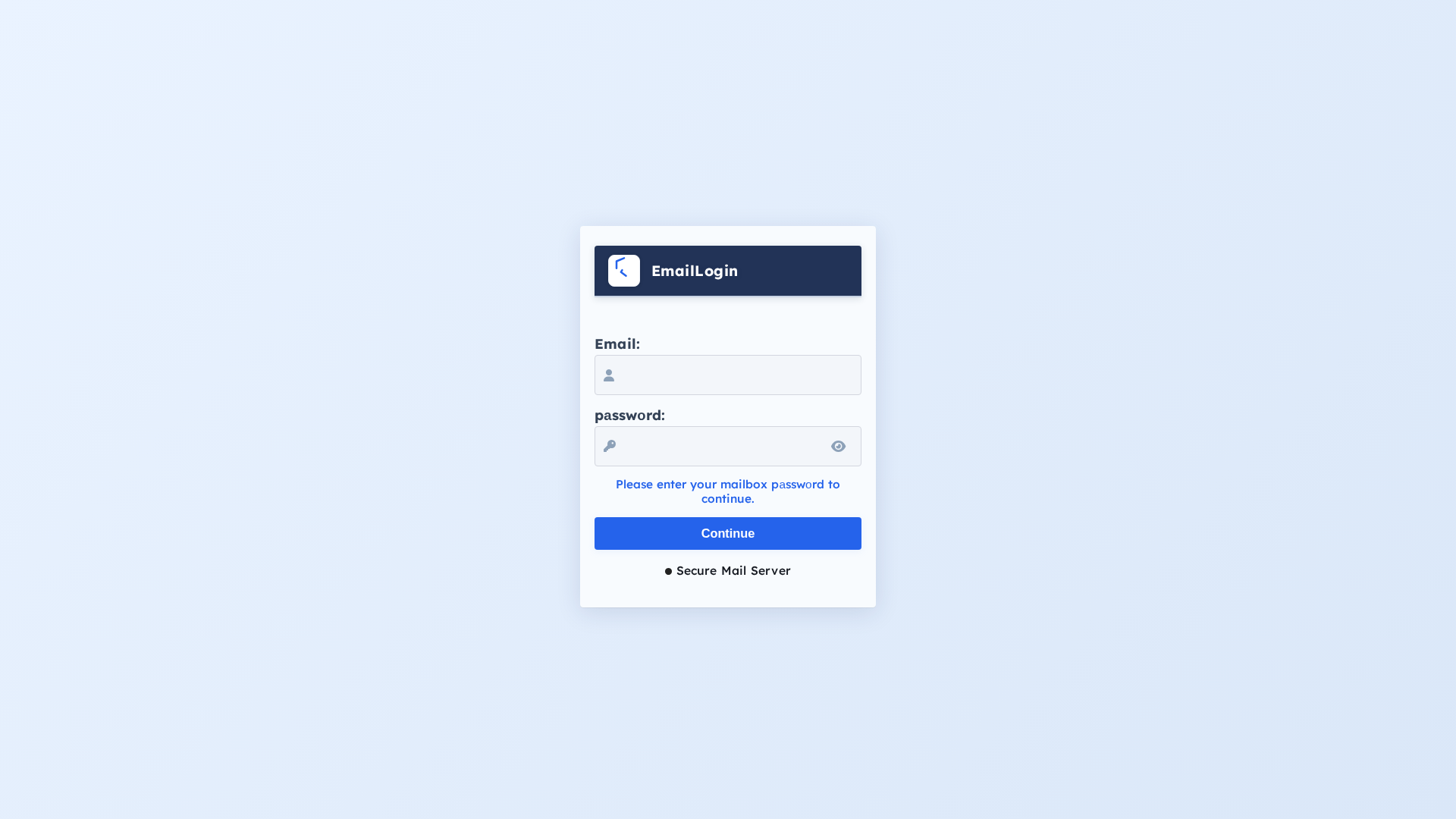
Captura Visual
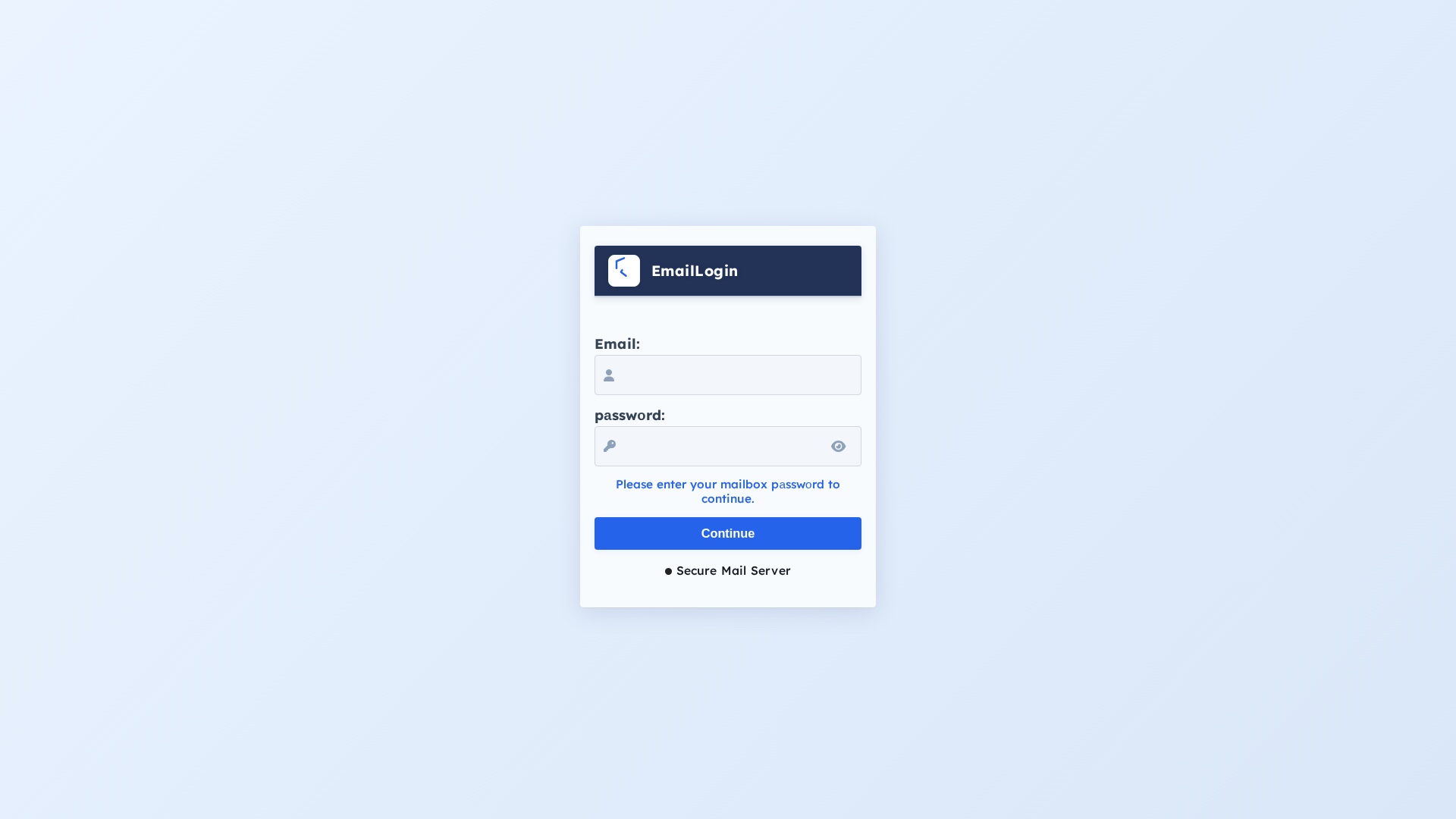
Información de Detección
https://ipfs.orbitor.dev/ipfs/bafkreietmq2owe4mmr4olp44ogax3zu5zxvomkq5cawnxu5vivaa7tzabq/
Detected Brand
Unknown
Country
International
Confidence
95%
HTTP Status
200
Report ID
91915fad-09d…
Analyzed
2026-02-27 06:20
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12F412270A018A8675292C6D876E42B1F35D68309CF526B0163FC93996BFAD49ED29094 |
|
CONTENT
ssdeep
|
24:nKCCcASZcmDGguDfEaQybnKn/9P6uCzRQ60oFHLNHziXKHVJFg4uB/eDzLwkxHib:nKWhcqGgC9bKVPTiFrBOK13DHHWN |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f6a6989999266666 |
|
VISUAL
aHash
|
ffffe6feece4f8f0 |
|
VISUAL
dHash
|
00304c10084c3000 |
|
VISUAL
wHash
|
fcf8e0f8f8e0e0c0 |
|
VISUAL
colorHash
|
070060000c0 |
|
VISUAL
cropResistant
|
00304c10084c3000,00202804242428c0 |
Análisis de Código
Risk Score
53/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Amenaza: Phishing de credenciales
• Objetivo: Usuarios de correo electrónico
• Método: Imitación de una página de inicio de sesión.
• Exfil: Desconocido (contraseña). Posiblemente extrae credenciales a través de Javascript ofuscado.
• Indicadores: Dominio inusual, formulario genérico, envío de formulario Javascript y ofuscación atob.
• Riesgo: Alto
🔒 Obfuscation Detected
- atob
📡 API Calls Detected
- POST
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Suspicious Domain
The domain is not associated with any known legitimate login pages.
Generic Login Form
The form lacks specific branding and appears generic.
JavaScript Form Submission
Form submission is handled by JavaScript, a technique often used in phishing.
Obfuscation Detected
Obfuscation can be used to hide malicious code that could compromise user credentials.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Credential Harvesting Kit
Objetivo
General public
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 4 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
EmailLogin (generic, not a real brand)
Fake Service
Email Login
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attackers are attempting to steal email credentials by presenting a fake login form on a suspicious domain. User will enter username and password.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
ipfs.orbitor.dev
Registered
Unknown
Registrar
Unknown
Status
Unknown
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
No screenshot
Unknown
https://bafkreietmq2owe4mmr4olp44ogax3zu5zxvomkq5cawnxu5viva...
Feb 27, 2026
Unknown
https://ipfs.io/ipfs/bafkreietmq2owe4mmr4olp44ogax3zu5zxvomk...
Feb 27, 2026
Unknown
https://latam.orbitor.dev/ipfs/bafkreietmq2owe4mmr4olp44ogax...
Feb 27, 2026
Unknown
https://eu.orbitor.dev/ipfs/bafkreietmq2owe4mmr4olp44ogax3zu...
Feb 27, 2026
Unknown
https://apac.orbitor.dev/ipfs/bafkreietmq2owe4mmr4olp44ogax3...
Feb 27, 2026
Scan History for ipfs.orbitor.dev
Found 7 other scans for this domain
-
http://ipfs.orbitor.dev/ipfs/bafkreihxkhc3zqivf7yc...
https://ipfs.orbitor.dev/ipfs/bafkreihujo3bmunbeph...
https://ipfs.orbitor.dev/ipfs/bafkreihxkhc3zqivf7y...
https://ipfs.orbitor.dev/ipfs/bafybeib3akl4qjotpnz...
https://ipfs.orbitor.dev/ipfs/bafkreiawyallprtg2yz...
https://ipfs.orbitor.dev/ipfs/bafkreiczdadxptbewxs...
https://ipfs.orbitor.dev/ipfs/bafkreiczdadxptbewxs...

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.