
Phishing Analysis
Detailed analysis of captured phishing page
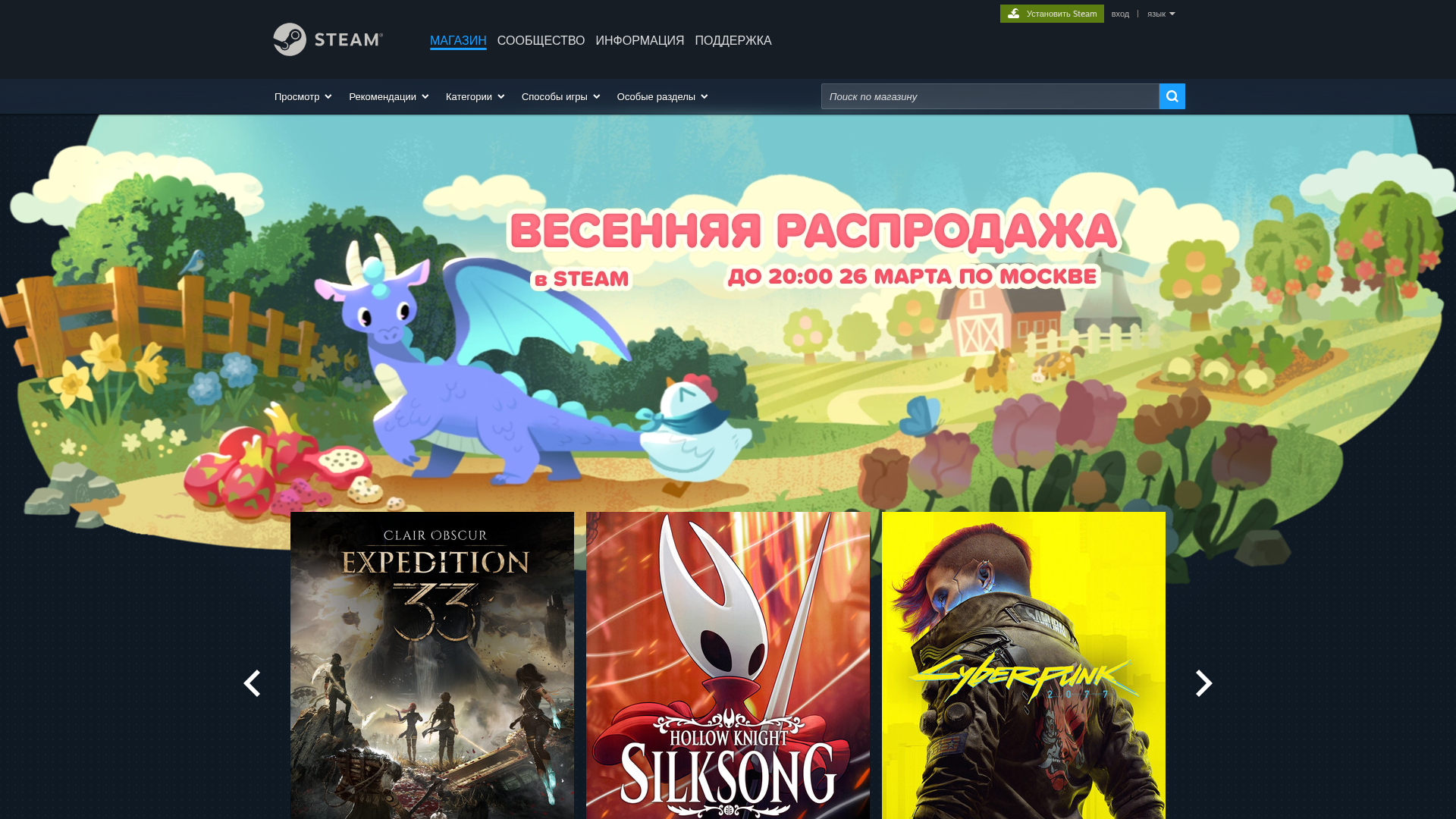
Captura Visual
Información de Detección
https://vovchik14888.github.io/steam/
Detected Brand
Steam
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
933e716d-3b1…
Analyzed
2026-04-04 21:09
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1B4547271905494378A4BFAF0F921571E3697936FCA474792E2FC8BA81BC6CE1FD22508 |
|
CONTENT
ssdeep
|
6144:EnUTHrZFaRavYnOpcMOSJrMT2wRWUFYFdkPBE2iwPu2gObHxs0dFAELl3DJqF4n4:zNFHpcMOSJrMT2wRWUFYFdkPBiwPu2gn |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
95ae62706b171cc7 |
|
VISUAL
aHash
|
00ffffbffe1e0c00 |
|
VISUAL
dHash
|
84ae7078b0b4d4d0 |
|
VISUAL
wHash
|
00ffbfbffc0e0800 |
|
VISUAL
colorHash
|
11242008000 |
|
VISUAL
cropResistant
|
9674785ab0b4d0d2,c4a48967aab4e0fe,84ae7078b0b4d4d0,20222c2c61e46464,63377324348c4c29,8e3747635b3f2d53 |
Análisis de Código
Risk Score
85/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://store.steampowered.com/app/1086940/Baldurs_Gate_3/?snr=1_4_seasonalsale__629
- https://store.steampowered.com/login/?redir=%3Fl%3Drussian&redir_ssl=1&snr=1_4_seasonalsale__global-header
📡 API Calls Detected
- get
📤 Form Action Targets
- https://store.steampowered.com/search
📊 Desglose de Puntuación de Riesgo
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 16 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 802 technique(s) to evade detection
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Steam users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
HTTP POST to backend
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 802 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Steam
Official Website
N/A
Fake Service
Banking/payment service
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 802 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
vovchik14888.github.io
Registered
Unknown
Registrar
Unknown
Status
Hosting platform (subdomain)
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.