Phishing Analysis
Detailed analysis of captured phishing page
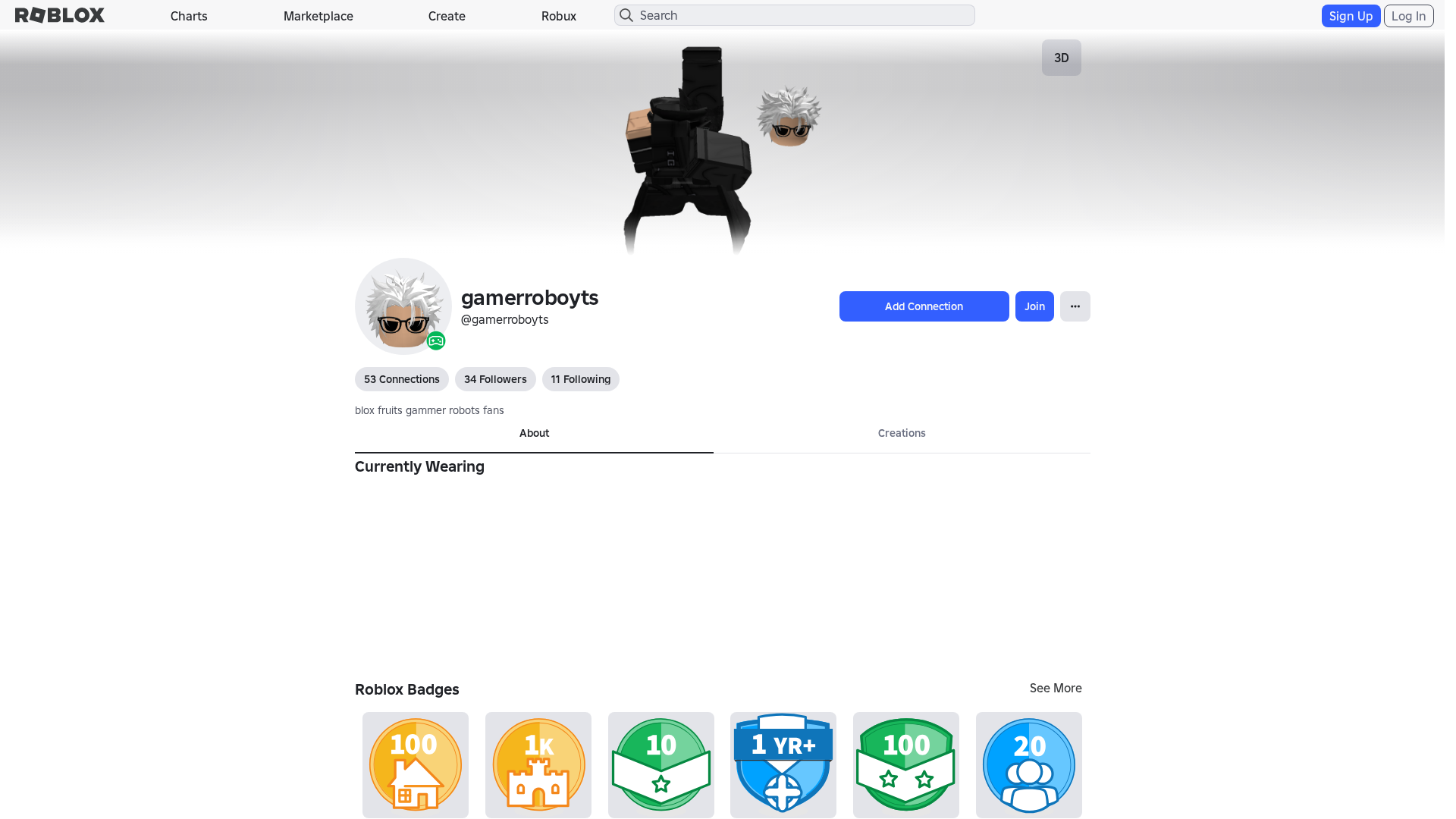
Captura Visual
No screenshot available
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T19593B8B29251243320BFB1D5F1297709A2D3D74EC68287D1E2FCA36B1ED6CA1F817856 |
|
CONTENT
ssdeep
|
1536:u8QXWnSravouOssorJBPmzzXXMd6MiucCOK:1QXWdvouOOTmzzXXMd6M1cCOK |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b31363936ccccc9c |
|
VISUAL
aHash
|
0000e3dbffffffc3 |
|
VISUAL
dHash
|
c8c80e3638002606 |
|
VISUAL
wHash
|
000042c3dfffdfc3 |
|
VISUAL
colorHash
|
07200008280 |
|
VISUAL
cropResistant
|
c8c80e3638002606,46c6073f5d2d33f1 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: No detectada.
• Objetivo: N/A
• Método: N/A
• Exfil: N/A
• Indicadores: El dominio es robloxc.com.es que no es roblox.com
• Riesgo: BAJO - Potencialmente un intento de recolección de datos, pero no hay evidencia clara de actividad maliciosa en la captura de pantalla.
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- /catalog
- /login?returnUrl=
- /login?returlUrl=316088579
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://www.roblox.com/info/blog?locale=en_us
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- get
- POST
- https://apis.
- https://help.roblox.com/hc/articles/30428367965460
- GET
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 862 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The phishing kit employs a credential harvester to capture Roblox usernames and passwords in real-time. Submitted credentials are likely exfiltrated to a remote server controlled by the attacker for immediate account takeover.
Secondary Method: OTP and Payment Data Theft
The kit includes modules for intercepting one-time passwords (OTP) and stealing payment card details. This enables attackers to bypass multi-factor authentication and conduct unauthorized transactions.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🦠 Malicious Files
Large JavaScript payload containing credential harvesting, OTP interception, and payment card stealing functionality.
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : None
- : Heavy
- : Light
- : Heavy
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for robloxc.com.es
Found 10 other scans for this domain
-
https://www.robloxc.com.es/users/7048358411/profil...
https://robloxc.com.es/users/241551989/profile
https://robloxc.com.es/users/1539346212/profile
https://www.robloxc.com.es/discovers/?Keyword=
https://robloxc.com.es/users/1958949928/profile
https://robloxc.com.es/users/2069911119/profile
https://robloxc.com.es/users/518931499/profile
https://robloxc.com.es/charts
https://robloxc.com.es/users/704835841/profile/
https://robloxc.com.es/users/2123049659/profile