Phishing Analysis
Detailed analysis of captured phishing page
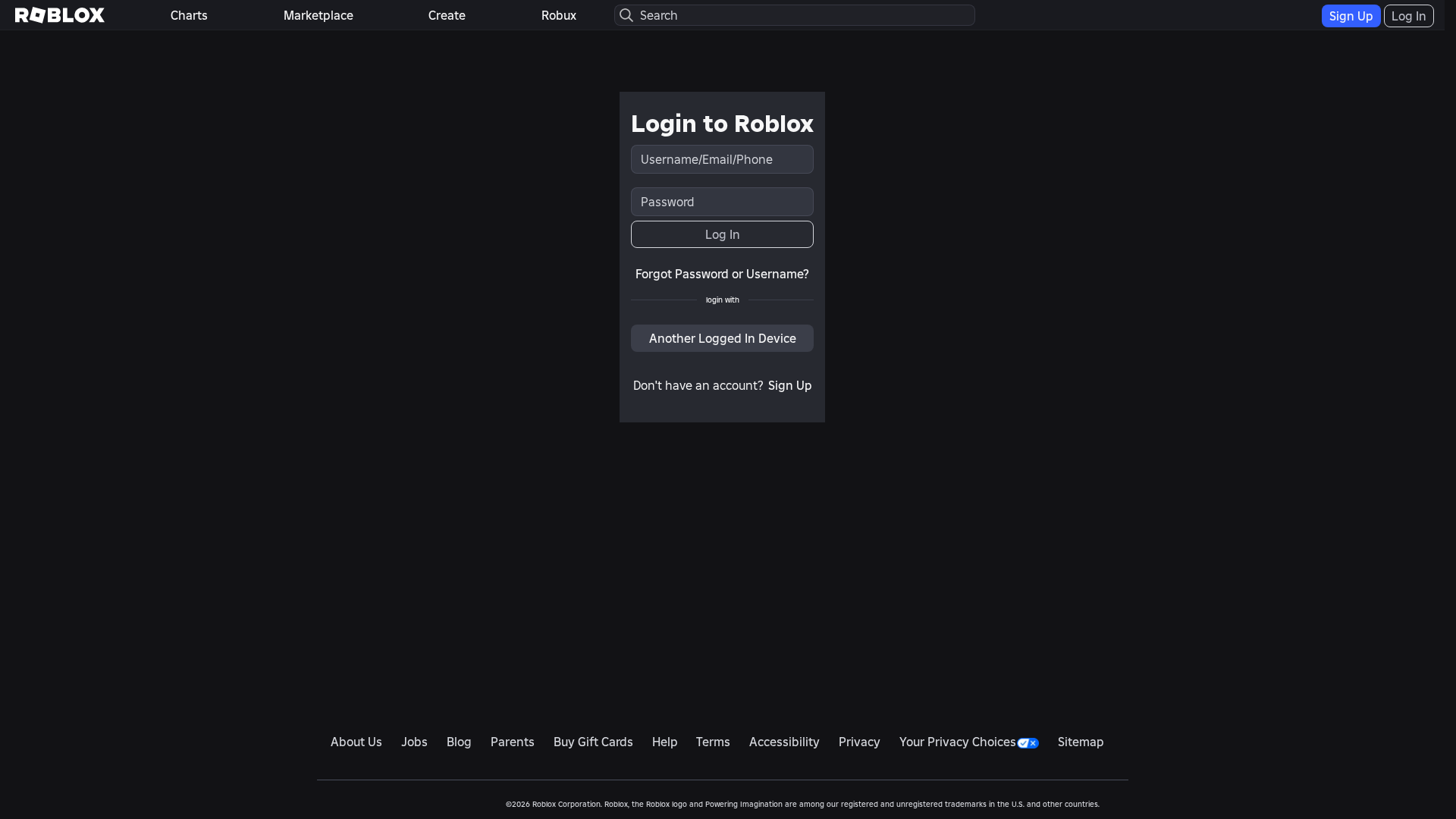
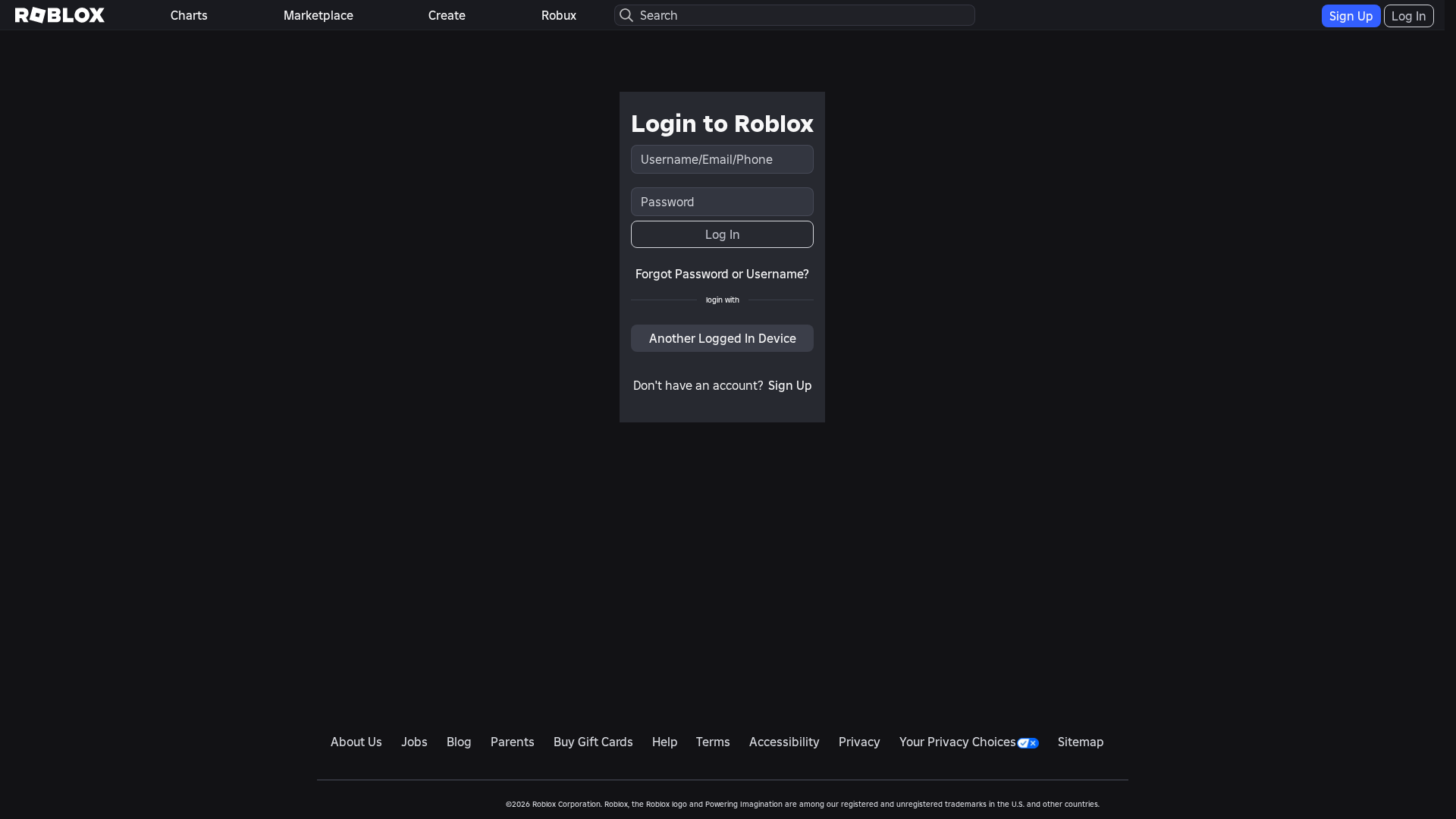
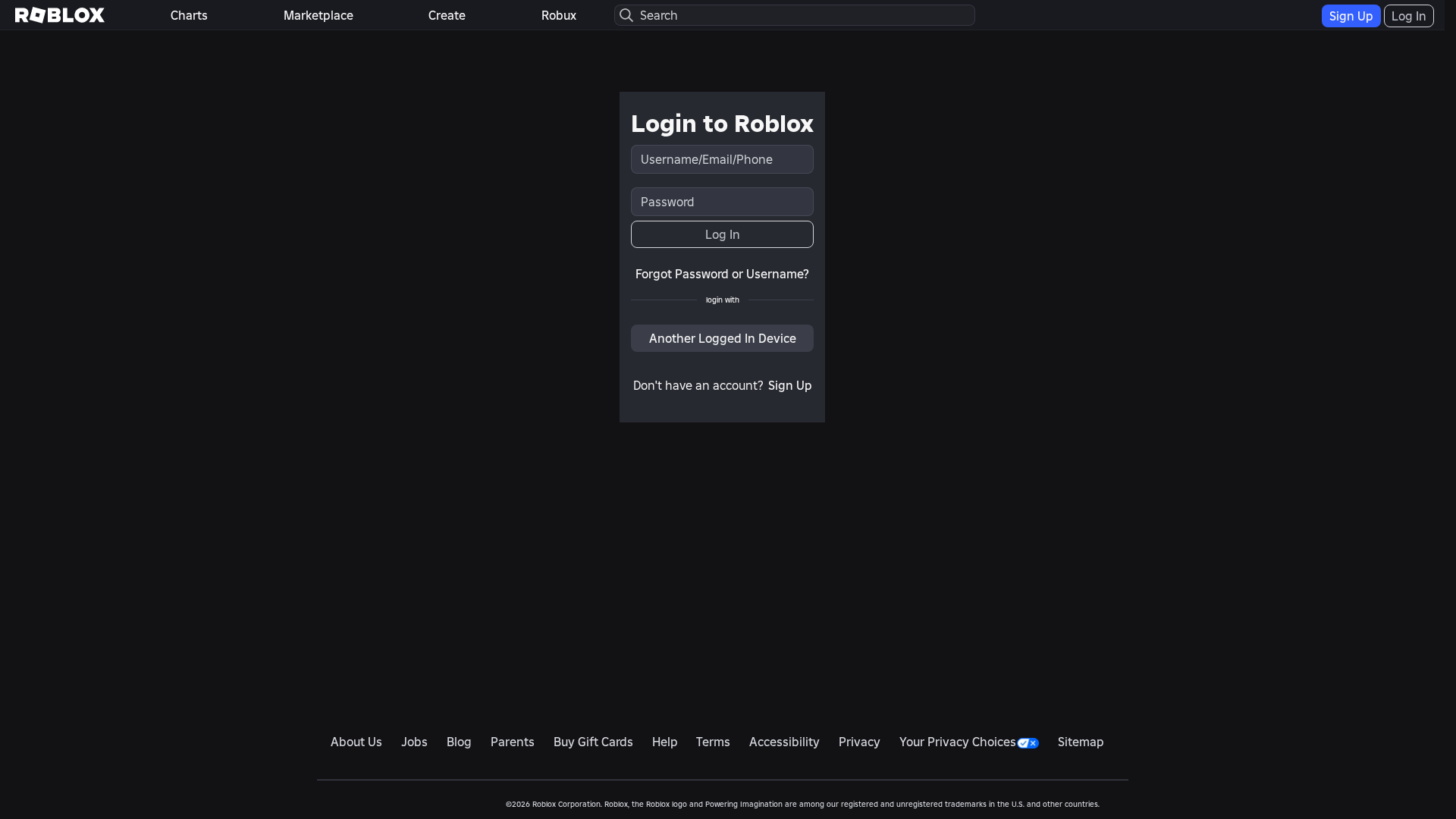
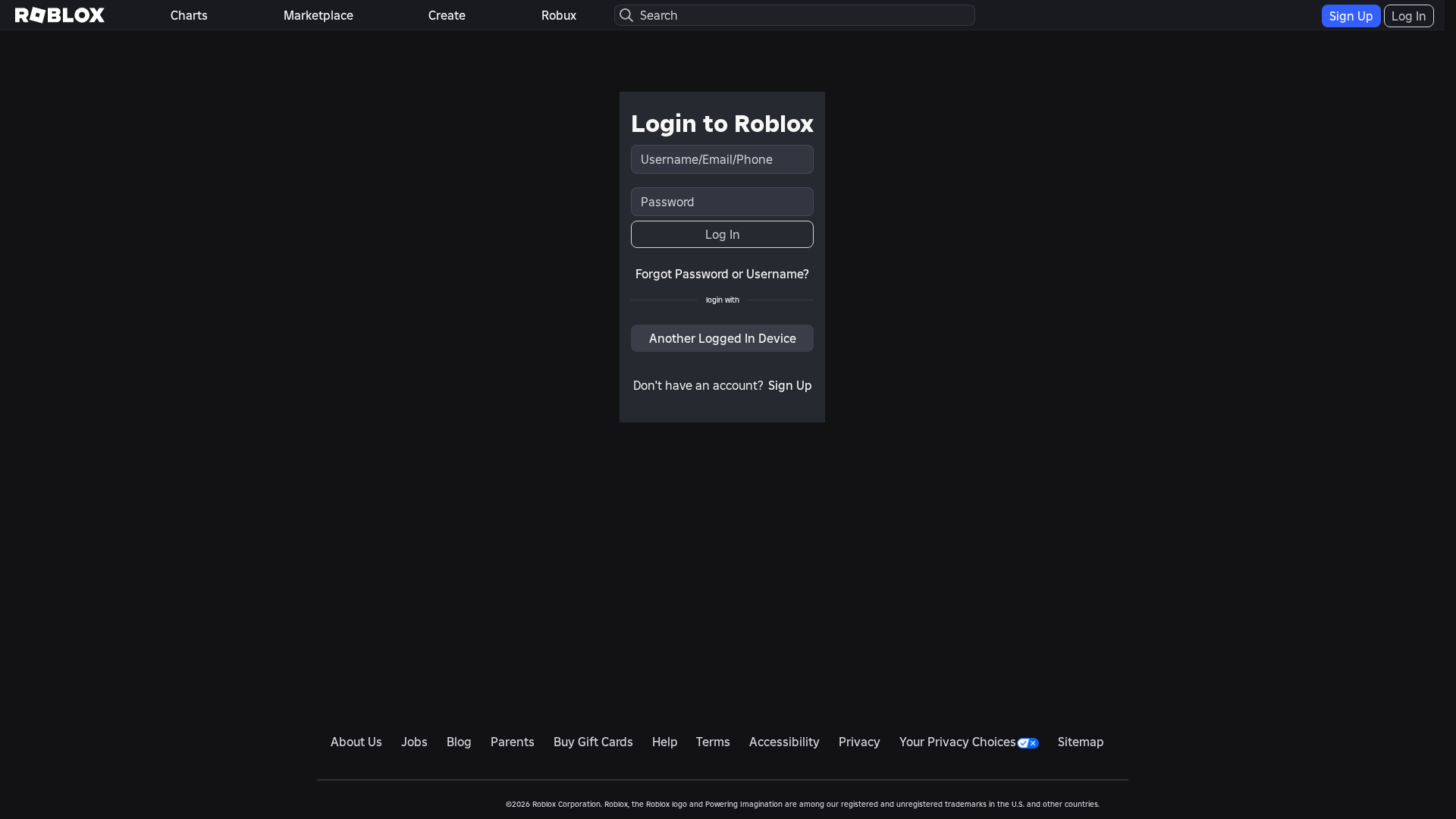
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T158C27572A0701836A26F73DAF514B7149093EB1FCF869BF291A8637619CDD22BD0741E |
|
CONTENT
ssdeep
|
384:ueoXW/D4N98TJp6pr4i+LK4xHAnDzmkwtkUiEl6g:boXW/bbL4PmpiEAg |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cccca263a2eba2e3 |
|
VISUAL
aHash
|
f91818180000003c |
|
VISUAL
dHash
|
33b2323230084068 |
|
VISUAL
wHash
|
ff3c3c3c1800407e |
|
VISUAL
colorHash
|
380000001c0 |
|
VISUAL
cropResistant
|
33b2323230084068 |
Análisis de Código
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://www.roblox.com/de/login
- https://www.roblox.com/pt/login
- https://cerulean-entremet-a1aeb4.netlify.app/login?returnUrl=https%3A%2F%2Fcerulean-entremet-a1aeb4.netlify.app%2F
- https://www.roblox.com/it/login
- https://cerulean-entremet-a1aeb4.netlify.app/info/blog?locale=en_us
- https://www.roblox.com/tr/login
- https://www.roblox.com/login/forgot-password-or-username
- https://www.roblox.com/pl/login
- https://www.roblox.com/th/login
- https://www.roblox.com/fr/login
- https://www.roblox.com/ko/login
- https://www.roblox.com/vi/login
- https://www.roblox.com/login
- https://www.roblox.com/id/login
- https://www.roblox.com/es/login
- /catalog
- https://cerulean-entremet-a1aeb4.netlify.app/catalog?CatalogContext=1&Keyword=
- https://www.roblox.com/ja/login
- https://www.roblox.com/ar/login
📡 API Calls Detected
- get
- https://help.roblox.com/hc/articles/30428367965460
- https://ro.blox.com/Ebh5?
- https://api.ipify.org?format=json
- https://apis.
- POST
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- 1 Discord webhook(s)
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 183 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 183 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for cerulean-entremet-a1aeb4.netlify.app
Found 1 other scan for this domain